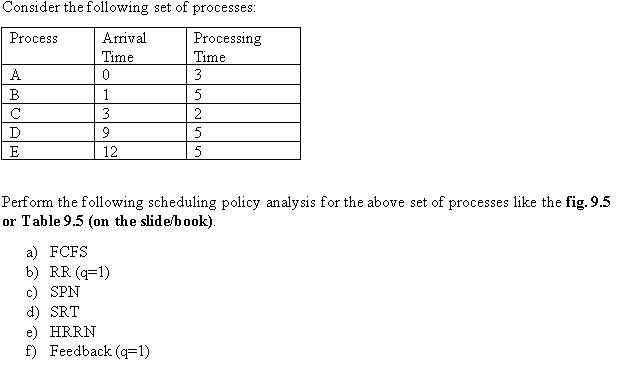
Perform the following scheduling policy analysis for the above set of processes like the fig. 9.5 or Table 9.5 (on the slide/book)
Q: Explain the concept of VLAN trunking and the protocols commonly used for it.
A: In the realm of modern networking, the need for flexibility, efficiency, and security has led to the…
Q: discuss the difference between a forensic disk image and a regular disk image specifically…
A: A disk image is a file-based representation of an entire storage volume or device. It contains an…
Q: Describe the primary functions of a firewall in a network security architecture.
A: A firewall is a crucial component of network security architecture designed to protect a network…
Q: What is VLAN tagging, and why is it important in a virtual LAN setup?
A: VLAN tagging, also known as Virtual LAN tagging, plays a role in computer networking in virtual LAN…
Q: ends in data management, such as the use of artificial intelligence and machine learning for data…
A: in the following section you will learn about the emerging trends in data management, such as the…
Q: Write a java program that takes the birth year from the user and prints her/his age. Here are…
A: The following are steps needs to be taken for the given program:Using Scanner class first we ask the…
Q: In the era of big data, how do NoSQL databases like MongoDB and Cassandra differ from traditional…
A: In the era of big data, the landscape of data management has evolved significantly, giving rise to…
Q: Discuss the concept of data modeling and its role in designing a database schema.
A: Data modeling is essential to database schema design. It involves visualizing database data…
Q: oncept of VLANs and how they enhance network segmentation
A: Let's embark on a journey to understand VLANs, a term you've probably heard or read about when…
Q: Write Java source code to take an integer n and returns the sum of all odd positive integers less…
A: The problem revolves around finding the sum of all odd positive integers up to and including a given…
Q: Explain the concept of microservices architecture in distributed systems. How does it differ from…
A: A distributed system is made up of several computers connected by a network that cooperate to…
Q: Explain the challenges of data consistency in distributed systems and the techniques used to address…
A: The maintenance of data consistency is of utmost importance in any system, since it guarantees the…
Q: Explain the key challenges in designing distributed systems, such as communication and…
A: There are several challenges arise such as synchronization and communication, when designing…
Q: specifies a physical star topology featuring a central hub and twisted-pair cable as the medium.…
A: 10BASE2, also known as "thin Ethernet," is a type of Ethernet networking standard.It uses a physical…
Q: How do distributed systems improve fault tolerance compared to centralized systems?
A: In computer systems, fault tolerance is a factor that ensures operation even in the face of hardware…
Q: In a cloud-based data management environment, what are the key factors to consider in selecting a…
A: Selecting the right data storage and processing platform in a cloud-based data management…
Q: What is the role of middleware in a distributed system architecture?
A: The distributed system architecture is a network of computers that work together to complete a task.…
Q: Describe the concept of data governance and its role in ensuring data quality and compliance.
A: Data governance is a framework of policies, processes, and controls that ensure the effective…
Q: Explain the concept of VLAN tagging (802.1Q) and how it facilitates the identification of VLAN…
A: Given,Explain the concept of VLAN tagging (802.1Q) and how it facilitates the identification of VLAN…
Q: Discuss the principles of data privacy and the implications of data protection regulations like GDPR…
A: Data privacy is the practice of protecting individual's personal information and…
Q: Explain the fundamental principles of a distributed system. What are the key challenges in building…
A: A distributed system is a computing system that consists of multiple interconnected computers or…
Q: Question p Convert the following assembly language instruction into hexadecimal machine language:…
A: In the realm of computer architecture and low-level programming, the translation of human-readable…
Q: Explain the role of indexing in database management. How does indexing impact query performance, and…
A: Indexing is an operation applied to optimize data retrieval in a database engine. A key requirement…
Q: How do data management strategies differ for structured and unstructured data?
A: When it comes to managing data, there are strategies for unstructured data due to their inherent…
Q: Discuss the challenges of data storage in the era of big data. How do technologies like distributed…
A: In today’s world of data, organizations face the challenge of managing and storing enormous amounts…
Q: In a multi-cloud or hybrid cloud environment, how can organizations effectively manage and secure…
A: Managing and securing data in a multi-cloud or hybrid cloud environment is a complex task that…
Q: What does the following program do .ORIG x3000 TRAP x20 TRAP X21 Pick one of the following below. A.…
A: Little Computer 3, or LC-3, can be defined in such a way that it is a kind of computer educational…
Q: How does data management intersect with data privacy and compliance regulations like GDPR and CCPA?…
A: To comply with data privacy and protection laws like the General Data Protection Regulation (GDPR)…
Q: a) Using a loop, write a segment of code which adds all positive integers between and including the…
A: 1. Import the Tkinter library as `tk`.2. Define the variables `intMin` and `intMax` with your…
Q: In the context of distributed systems, what are Byzantine faults, and how can Byzantine…
A: Byzantine faults are a form of distributed system problem or failure when a component may display…
Q: Explain the role of a VLAN ID (VID) and how it is used in Ethernet frames to identify VLAN…
A: The segmentation of a single physical network into numerous Virtual Local Area Networks (VLANs) is a…
Q: What are data lakes, and how do they differ from traditional data warehouses in terms of data…
A: A database system is a software program or platform that effectively stores, manages, organizes, and…
Q: Define the principles of data management. What are the key components of a well-structured data…
A: The utilization of data has become an indispensable component within the operational and…
Q: What are private VLANs (PVLANs), and how do they enhance security in a VLAN environment?
A: In environments Private VLANs (PVLANs) are used to enhance network security and control by creating…
Q: Explain the purpose of VLANs in a network, and provide examples of scenarios where VLANs can be…
A: A VLAN, or virtual LAN, groups network devices logically regardless of location. It divides a huge…
Q: Define data management and its importance in the context of modern businesses.
A: Data management comprises strategies, policies, and procedures that enable organizations to…
Q: Explain the concept of Q-in-Q (VLAN stacking) and its use cases in network design.
A: Q-in-Q, also known as VLAN stacking, is a network technology that allows multiple VLANs (Virtual…
Q: How large (in bytes) is this structure on a
A: The question asks for the size, in bytes, of a structure named ListElement on an x86-64 Linux…
Q: What are the challenges and benefits of implementing a Master Data Management (MDM) system in a…
A: Master Data Management (MDM) is an approach to managing and integrating critical data across various…
Q: How does VLAN tagging work, and why is it necessary for VLAN communication?
A: VLAN (Virtual LAN) tagging groups network devices into logical networks within a physical network.…
Q: Discuss the CAP theorem in the context of distributed systems. What does it entail, and how does it…
A: The CAP theorem, proposed by computer scientist Eric Brewer, is a fundamental concept in the field…
Q: How does fault tolerance play a crucial role in distributed systems? Discuss various fault tolerance…
A: Fault tolerance in distributed systems is the ability of the system to continue functioning and…
Q: Discuss the various architectural models of distributed systems, such as client-server,…
A: Distributed systems are a fundamental part of modern computing, enabling the sharing of resources,…
Q: How does the concept of sharding work in distributed databases, and what benefits does it offer in…
A: Sharding is a sort of database partitioning that divides huge databases into smaller, quicker,…
Q: Explain the concept of VLANs and why they are used in netwo
A: Virtual Local Area Networks, commonly known as VLANs, are a fundamental concept in computer…
Q: 3. [Indirect addressing] Write a program that first displays all the elements of an array, e.g.…
A: Data Definition:Define CloudArray and MistArray arrays with the same size, containing a mix of…
Q: How do distributed systems handle concurrency control and synchronization among multiple nodes?…
A: Concurrency control and synchronization are critical aspects of distributed systems, ensuring that…
Q: Explain the purpose of VLANs in a network architecture and provide an example of a scenario where…
A: The requirement for flexibility, security, and efficient resource management has become critical in…
Q: What are the architectural patterns for microservices in a distributed system, and how do they…
A: In this question we have to understand the architectural patterns for microservices in a distributed…
Q: Explain the concept of consensus in distributed systems and its importance in achieving consistency…
A: In distributed systems, where multiple components operate concurrently and potentially…
Step by step
Solved in 3 steps

- To not let any process wait longer than 500 ms, a system developer programs the Round Robin procedure with a dynamic time quantum size. With ‘n’ processes ready, the time quantum Q is set to 500 ms/n. What do you think of this scheduling strategy? (In which situations is this strategy feasible, and when is it not? Are there edge cases?) Explain your reasoning.Question no 02: Consider the following set of processes, with the length of the CPU burst given in seconds: Process Burst Priority P1 32 4 P2 24 1 P3 4 2 P4 36 2 P5 12 3 NOTE: The processes are assumed to have arrived in the order P1, P2, P3, P4, P5, all at time 0. Draw four Gantt charts that illustrate the execution of these processes using the following scheduling algorithms: FCFS, SJF, non-preemptive priority (a larger priority number implies a higher priority), and Round Robin (quantum = 8). What is the turnaround time of each process for each of the scheduling algorithms in part a? What is the waiting time of each process for each of these scheduling algorithms? Which of the algorithms results in the minimum average waiting time (over all processes)? Which of the algorithms results in the minimum average turnaround time (over all processes)?A real-time system executing four different periodic tasks Ti(p,t) is given, with p and t representing the period and the execution time of the task, respectively. Each task's deadline matches its period p. The system is executing the following set of tasks: S = {T1(10,2), T2(4,1), T3(10,3), T4(7,1)}. Is this real-time system schedulable under Rate-Monotonic (RM) scheduling? Is this real-time system schedulable under Earliest Deadline First (EDF) scheduling? Explain your answers using the concept of overall CPU utilization.
- We are dealing with 6 processes p1;p2; : : : ;p6:(a) Processes p1;p2 in p3 arrive at time 2 ms, respectively. Each of those processesneeds 5 ms of CPU time.(b) Process p4 arrives at time 10 ms and needs 3 ms of CPU time.(c) Processes p5 in p6 arrive at time 19 ms. Process p5 needs 7 ms, while process p6needs 4 ms of CPU time.Scheduling is preemptive, where there process switch takes 1 ms. For the Round-Robinalgorithms with quantum 2 ms illustrate the execution of those processes on a timeline.Then determine the average turnaround time.Consider the following set of processes, with the length of the CPU burst given in seconds: Process Burst time Arrival time P1 10 1 P2 04 2 P3 05 3 P4 03 4 Draw four Gantt charts that illustrate the execution of these processes using the following scheduling algorithms: FCFS, SJF preemptive and Round Robin (quantum = 3). What is the turnaround time of each process for each of the scheduling algorithms in part a? What is the waiting time of each process for each of these scheduling algorithms? Which of the algorithms results in the minimum average waiting time (over all processes)? Which of the algorithms results in the minimum average turnaround time (over all processes)?2. Consider the following processes with their associated CPU burst times. The processes have entered the system in the order that they are presented in the table. Process : BurstTime P1 : 7 P2 : 1 P3 : 13 P4 : 4 P5 : 5 For each of the following scheduling algorithms, draw a Gantt chart that illustrates the order of execution for each of these processes. Also, compute the average waiting time for each algorithm. a. First Come First Served b. Shortest Job First c. Round Robin (with time quantum of 3)
- Question no 02: Consider the following set of processes, with the length of the CPU burst given in seconds: Process Burst Priority P1 32 4 P2 24 1 P3 4 2 P4 36 2 P5 12 3 NOTE: The processes are assumed to have arrived in the order P1, P2, P3, P4, P5, all at time 0. a. Draw four Gantt charts that illustrate the execution of these processes using the following scheduling algorithms: FCFS, SJF, non-preemptive priority (a larger priority number implies a higher priority), and Round Robin (quantum = 8). b. What is the turnaround time of each process for each of the scheduling algorithms in part a? c. What is the waiting time of each process for each of these scheduling algorithms? d. Which of the algorithms results in the minimum average waiting time (over all processes)? e. Which of the algorithms results in the minimum average turnaround time (over all processes)?Consider the following data [Figure].Suppose round robin scheduling is applied on the given data with time quantum=Floor (XX % 3) units. It is also given that scheduling of a process or context switch will take 1 unit of time. What is the completion time and turnaround time of process P4?Where XX is the last two digits of your roll number. XX=18Apply the following scheduling algorithms to the list process. 1. Shortest Remaining Time 2. Round Robin:Quantom =3 For each process scheduling algorithm, provide the following: a. Finish time Turnaround time Waiting time b. A detailed gantt chart c. The average turnaround time d. The average waiting time
- Consider the following set of processes, with the length of the CPU burst given in milliseconds: Process Burst Time Priority Arrival Time P1 20 2 0 P2 10 1 1 P3 80 4 2 P4 40 2 3 P5 50 3 4 Draw the GANTT Chart for the schedule of the processes, the waiting time for each process, the average waiting time, the turnaround time for each process and average turnaround time using the following scheduling algorithm. c.…Consider the following set of processes, with the length of the CPU burst given in milliseconds: Process Burst Time Priority Arrival Time P1 20 2 0 P2 10 1 1 P3 80 4 2 P4 40 2 3 P5 50 3 4 Draw the GANTT Chart for the schedule of the processes, the waiting time for each process, the average waiting time, the turnaround time for each process and average turnaround time using the following scheduling algorithm. b.…Draw Gantt charts that illustrate the execution of these processes using the following scheduling algorithms and calculate the average waiting time. Round-Robin (RR) with Time quantum = 4











