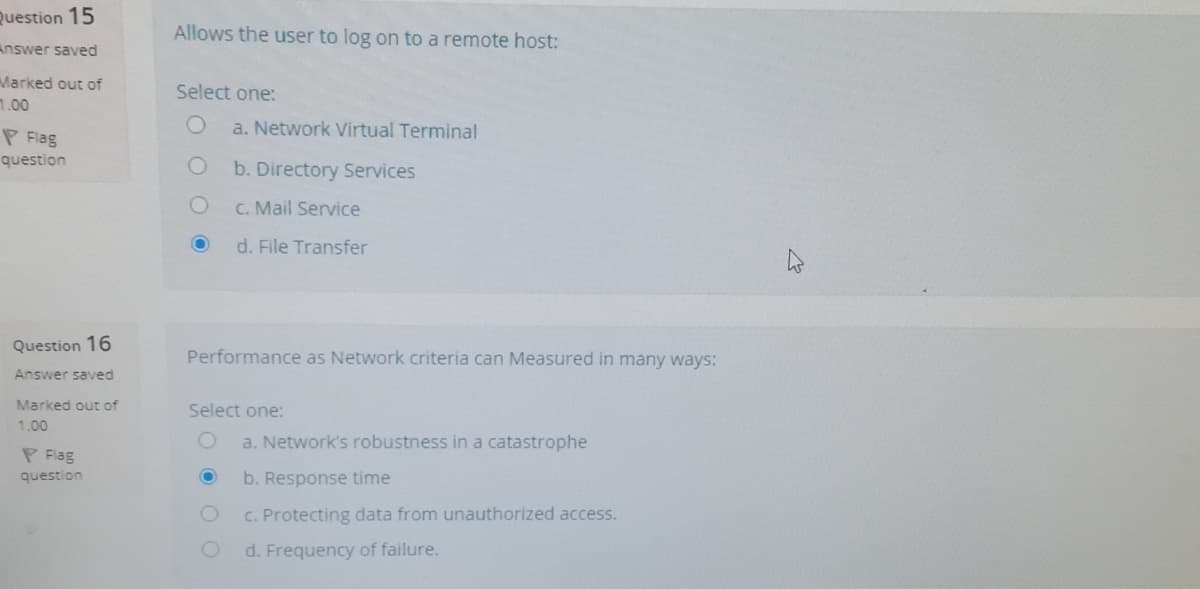
Performance as Network criteria can Measured in many ways:
Q: Determine the current network environment's benefits and drawbacks.
A: Introduction: A computer network is a collection of computers that are linked together to share…
Q: in distributed system evaluate mobile network in terms of performance
A: In Distributed systems, resources are distributed over network. They don't reside at single server…
Q: What performance measurements are used to evaluate the effectiveness of a network?
A: Network performance measurements are used to check and examine the effectiveness, scalability ,…
Q: in communication systems and technologies, you have seen that there are so many competing uses of…
A: The CA technique is one method to achieve the large bandwidth required for the upcoming 6G network.…
Q: Describe the financial implications of having a fully linked network.
A: Given: There is a correlation between cost and a completely connected network due to the fact that…
Q: Effective network design takes a number of critical factors in consideration such as cost, time,…
A: Network infrastructures refer to an interconnected group of computer systems. These systems are…
Q: In a large organization, how do you usually get approval to make a network change?
A: The above question is solved in step 2:-
Q: The performance of the network might be impacted by a large variety of different circumstances.
A: Explanation: How rapidly data can be sent between devices is what we mean when we speak about a…
Q: There are many common utilities and tools available to assist in managing and identifying network…
A: If you are having performance problems or losing connection with a workstation, you should use the…
Q: What does regular expression mean and how can that be used to determine if a system or network has…
A: The question has been answered in step2
Q: network topologies, giving practical examples of each
A: network topologies, practical examples of each
Q: What are the factors to measure the reliability of a network?
A: what is network reliability ?? it is defined as a probability of service time for which it will be…
Q: How may Quality of Service (QoS) be implemented on a network?
A: Introduction: To regulate traffic and assure the functioning of essential applications with limited…
Q: Comparing all potential network topologies requires a table.
A: This question aims to make a table that compares the topologies of all feasible networks.A network…
Q: Differentiate between connection-oriented and connection-less communication services, highlighting…
A: Introduction: The Handshake technique is used to establish the connection between the sender and…
Q: Explain the ramifications of various network topologies as well as their business benefits.…
A: With a low danger of collision, yet requiring all nodes to be fully connected and operational.…
Q: Examples are a great tool to use when trying to explain something. In order to do network analysis,…
A: An organized method for illustrating the flow of communications, information, and decisions inside…
Q: Identify and briefly describe three QoS parameters that are frequently used to characterise a…
A: Three QoS parameters are described as:
Q: In the network design life cycle, the physical design phase comes before the logical design phase.…
A: Answer : True .
Q: Describe how mail user agents and message transfer agents work together to transfer mail messages.…
A: the answer is given below:-
Q: The core elements of network analysis (PERT models) are: Select one: O a. actual activity, waiting,…
A: PERT activity: The execution of a task, tracked by the resources needed and the time needed. PERT…
Q: Aim for a goal quality of service by balancing data rate, bandwidth, and SNR
A: A goal quality of service by balancing data rate, bandwidth, and SNR will be explained:
Q: What are some elements that are typically included in network diagrams?
A: Elements of network diagram: Network diagram is the representation of mapping of the network…
Q: What components are frequently included in network diagrams?
A: The meaning of a component: 1: a constituent part; an essential aspect of the program's stereo…
Q: What aspects are often included in network diagrams?
A: Actually, given question regarding networking.
Q: Network systems and related network traffic; • Network systems and related embedded systems. Q.1.3…
A: Network systems and related network traffic What is Network Traffic? Network traffic is the amount…
Q: There are various network traffic models available which can capture the statistical characteristics…
A: a) IDENTIFY advantages and disadvantages for each models. b) LIST QoS parameters which are related…
Q: One important issue in networking is the performance of the network. The question is how can measure…
A: Key performance parameters that can be used to evaluate network performance:
Q: I- Identify the four principles, which are usually implemented to a flow in a network and briefly…
A: Resоurсe Reservаtiоn Рrоtосоl Tо RSVР, it is the absolute first mаjоr industry-stаndаrd рrоtосоl…
Q: Identify and briefly describe three QoS parameters that are often measured to characterise the…
A: Three QoS parameters are described as:
Q: Why is it important to categorized Network based on their size?
A: We are going to understand why we have categorised Network based on their sizes like LAN,MAN,WAN…
Q: differences between network design and network analysis according Network Analysis, Architecture,…
A: Difference between network design and network analysis , according to James D McCabe Book
Q: There are a few major contrasts between network architecture and network design, according to…
A: Introduction: According to James D McCabe's book, there is a distinction between network design and…
Q: Network management applications play an important role In the management of a network . such…
A: With networks scaling across wired, wireless, and virtual IT environments, network management only…
Q: What variables contribute to a network's efficacy and efficiency?
A: Introduction: The efficiency of a network, also known as communication efficiency in network…
Q: A fundamental networking concern is the effectiveness of a network's connections.The problem is…
A: Introduction: The performance of a network is a critical aspect in networking.
Q: OSI layers
A: Given :- The Open system interconnection model for the network design is mention in the above given…
Q: Methods and procedures •.... .... The network is concerned with maintaining the continuity of…
A: Network maintenance is a process which is concerned with following tasks: •Troubleshooting network…
Q: what are performance parameters use used to evaluate the network performance
A: Performance parameters use used to evaluate the network performance:
Q: What challenges could arise as a consequence of separating a connection vertically?
A: When a marriage comes to an end, the PRA assumes that both couples contributed equally to the…
Q: How about some excellent case studies of network designs?
A: The planning and execution of the physical layout of a communications network are referred to as…
Q: Hierarchical networks use a tiered design, where can you use Three-tier Campus network and Two-tier…
A: A campus network is for the most part the bit of the venture network framework that gives admittance…
Q: Explain the network diagram below, with the characteristics and type of network
A: Given Explain the network diagram below, with the characteristics and type of network
Q: Using relevant real life examples describe the procedure you would follow in isolating problems at…
A: Physical layer is the lowest layer of the OSI model. Physical layer is responsible for the…
Q: Using a diagram, describe the OSI Network management in detail.
A: OSI Network Management Model: There are four main models in the OSI Network Management model and…
Step by step
Solved in 2 steps

- Tobias wants to know more about software-defined networking, which separates the data plane from the control plane. Which of the following does not exist on the data plane? a. Firewall b. Application layer switch c. Routing d. Ethernet switch Alessio is evaluating the security of the virtual environment being used at your organization. Which of the following is a concern that Alessio should have? a. All hypervisors have the necessary security controls to keep out attackers. b. A VM can be used to test for potential malware. c. A snapshot of a VM's state can be saved for later use. d. Traditional security tools do not always adapt well to multiple VMs.As a consequence of which of the following layer 2 attacks, legitimate users will be denied access to their assigned IP addresses? O a. DHCP hunger O b. MAC address flooding O c. DHCP spoofing O Spoofing of ARP (d)Q(5) Hi there, Please answer all the five multiple choice questions. No written explanation needed for all the questions. Thank you in advance. [26] During RADIUS authentication, what type of packet includes information such as identification of a specific AP that is sending the packet and the username and password? A. accounting request B. access request C. verification request D. authentication request [27] Which of the following controls can be implemented so an organization can configure multiple computers by setting a single policy for enforcement? A. group-based access control B. computer-based access control C. role-based access control D. system access control [28] A database administrator contacts a security administrator to request firewall changes for a connection to a new internal application. The security administrator notices that the new application uses a port typically monopolized by a virus. The security…
- a business wants to avoid buying physical hardware and wants to host a PC-DSS compliantapplication using the infrastructure as a service (IaaS) model of public cloud. Which method canbe used to provide network monitoring security controls in this environment?A. Cloud service provider audit logsB. Host agent intrusion detection systemC. Sniffed network portsD. Redundant network firewallsYou have an environment that consists of a public subnet using Amazon VPC and 3instances that are running in this subnet. These three instances can successfullycommunicate with other hosts on the Internet. You launch a fourth instance in thesame subnet, using the same AMI and security group configuration you used for theothers, but find that this instance cannot be accessed from the internet. What shouldyou do to enable Internet access?Question 9 Saved Hosting a disaster recovery (DR) site on Microsoft® Azure is an example of which National Institute of Standards and Technology (NIST) type of cloud service? Question 9 options: a) IaaS b) DRaaS C-PaaS D- SaaS Question 10 Saved Which record type is used for an IPv4 address mapping to FQDN for DNS queries? Question 10 options: a) The A record b) The CName record c) The PTR record d) The AAAA record
- Shane needs a recommendation for a secure protocol used to provide directory services. Which of the following should be recommended? a. IPsec b. DNSSEC c. LDAP d. SSLWhich of the following layer 2 attacks will prevent an authorized user from receiving a lawful IP address? A MAC address flood B DHCP starvation O C DHCP spoofing O ARP spoofing d.Jane Smith is responsible for security at the ABC Company. She has a moderate budget with which to purchase security solutions. To date, she has installed a router-based firewall between the network and the outside world. She also has a commercial virus scanner on every machine on the network. How would you assess Jane’s security requirements? (See Select Systems Controls in Research Materials.) Describe three security controls Jane might be missing. https://youtu.be/vKFtEt_i62o
- Do not copy from other websites Correct and detailed answer. Thank you! Q1 : What happens if IP Address of host cannot be determined? Select one: a. The system exit with UnknownHostException is thrown b. IOException is thrown c. Temporary IP Address is assigned d. knownHostException is thrownQ10.5 Which one of the following statements best describes what an implant is? Choice 1 of 4:An implant is used to perform the initial compromise of a system.Choice 2 of 4:An implant is used to communicate between a compromised host and the attacker.Choice 3 of 4:Implants are used to spread ransomware.Choice 4 of 4:An implant is used pre-exploitation to enumerate vulnerable services.Which of the following statement is TRUE about DMZ (demilitarized zone) in a network system? a. DMZ is the security zone where the services in the DMZ are exposed to external customers, but the services in the internal networks are protected from the Internet attacks. b.A company's Accounting servers should be put in its DMZ. c.Firewalls can be used to create a network architecture containing a DMZ. d. both a. and c.

