Please answer the following questions in your lab report 1) Submit answers to the following questions based on the reports you generated. a) Did you find any vulnerability with the computer you scanned? b) What operating systems are running on the hosts you visited? c) List several services running on each computer? d) Identify one high severity vulnerability for each computer (if there is one). Describe the vulnerability and discuss control(s) to minimize the risk from the vulnerability.
Please answer the following questions in your lab report 1) Submit answers to the following questions based on the reports you generated. a) Did you find any vulnerability with the computer you scanned? b) What operating systems are running on the hosts you visited? c) List several services running on each computer? d) Identify one high severity vulnerability for each computer (if there is one). Describe the vulnerability and discuss control(s) to minimize the risk from the vulnerability.
Chapter10: Common Administrative Tasks
Section: Chapter Questions
Problem 9HOP
Related questions
Question
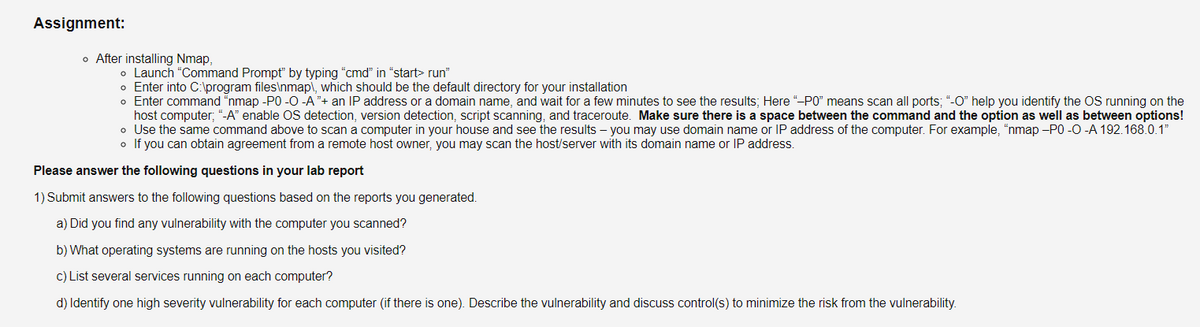
Transcribed Image Text:Assignment:
o After installing Nmap,
o Launch "Command Prompt" by typing "cmd" in "start> run"
o Enter into C:\program files\nmap\, which should be the default directory for your installation
o Enter command “nmap -P0 -O -A "+ an IP address or a domain name, and wait for a few minutes to see the results; Here "-PO" means scan all ports; "-O" help you identify the OS running on the
host computer; “-A" enable OS detection, version detection, script scanning, and traceroute. Make sure there is a space between the command and the option as well as between options!
o Use the same command above to scan a computer in your house and see the results - you may use domain name or IP address of the computer. For example, "nmap -PO -0 -A 192.168.0.1"
o If you can obtain agreement from a remote host owner, you may scan the host/server with its domain name or IP address.
Please answer the following questions in your lab report
1) Submit answers to the following questions based on the reports you generated.
a) Did you find any vulnerability with the computer you scanned?
b) What operating systems are running on the hosts you visited?
c) List several services running on each computer?
d) Identify one high severity vulnerability for each computer (if there is one). Describe the vulnerability and discuss control(s) to minimize the risk from the vulnerability.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 4 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,