Please design this in frizing/tinkercad
Q: What is short stroking, and how does it affect the relative cost per gigabyte of SSDs?
A: Intro Short stroking Short stroking is a technique for formatting a hard disc drive or a hard…
Q: why do device driers ned -to be inedalted whin the blos alveddy has Code to Connect with the…
A: -> The BIOS only has code to communicate with a limited subset of devices required to boot the…
Q: What might be the effects of not using encryption on network or Internet traffic?
A: The solution to the given question is: If the data is not encrypted , the data is in readable form…
Q: Tom is a big Green Bay Packers and Aaron Rodgers fan. He claims that Aaron Rodger's average number…
A: According to the information given:- We have to find out the hypothesis test, correct null…
Q: How do you identify, list, and define the six components of an information system?
A: IS (Information System): The term "information system" refers to a system that organises, stores,…
Q: final final 5. final 4.
A: State a b 1 2 6 2(final) 3 3 3(final) 4 4 4(final) 5 5…
Q: Write and assembly procedure called divide. the procedure takes two numbers saved in Ax and BX and…
A: Solution: Given,
Q: Define a Rectangle class that also inherits from Quadrilateral, with the following methods:…
A: We need to inherit rectangle from quadrilateral in python, for the given scenario.
Q: When working with an array, what can cause an off-by-one error to occur?
A: Solution: Off-by-one error to occur: Problem: Suppose, if we have array with 5 elements. array =…
Q: The "value per pound" greedy strategy didn't work to solve the 0-1 knapsack problem. Would the…
A: We need to find algorithm, if solution is optimum, else provide a counter example.
Q: What is open source in computer science?
A: This question comes from Internet Technologies which is a paper of computer science. Let's discuss…
Q: Compare and contrast the top-down and bottom-up approaches. The following points should be included…
A: Algorithms in programming languages are generally constructed in one of two ways: top-down or…
Q: Describe the components of a communication system.
A: Intro Communication Systems: A communications system, often known as a communications network, is…
Q: Which level scope is applicable for local variables (including parameter variables) inside a method?…
A: Explanation : In class level scope the variables of a class are declared at the class level, but…
Q: Distinguish between distributed and centralized architectural patterns. Discuss the advantages and…
A: Distributed architectural patterns works on single logical data network, which is being installed in…
Q: Explain why you believe a web server is the ultimate system.
A: Intro Web server: An explanation of a web server may be regarded the ultimate system. The final…
Q: We've already tried comparing 3 numbers to see the largest among all, so let's try a more…
A: Algorithm 0. Start 1. Ask user to enter five integers and store it in variables first integer,…
Q: Install Linux on a computer and provide an overview of some commonly used commands by demonstrating…
A: Introduction: To install Linux on your PC, you'll need the Linux operating system's.is file.The ISO…
Q: Describe the tools and technologies that are used to facilitate the management of information…
A: INITATION: To make the growth of information technology transparent, IT project management is…
Q: computer science - What Can Information Systems Do to Improve Process Quality?
A: Introduction: An information system can be an effective instrument for increasing the overall…
Q: What is the purpose of an embedded computer?
A: Introduction: A tiny computer that is integrated into a larger system, device, or machine is known…
Q: What is the significance of Charles Babbage being referred regarded as "the father of the computer?"
A: Charles Babbage: Charles Babbage was a British mathematician, inventor, philosopher, and mechanical…
Q: Explain why pure interpretation is a viable implementation strategy for a number of current…
A: Introduction: It is allowed to use pure interpretation when the computation is short enough that the…
Q: When a software program is not in operation, it is impossible to keep instructions and data in…
A: Storage and Memory: Main memory, primary storage, primary memory, main storage, internal storage,…
Q: 1- What are the main advantages and disadvantages in ad hoc networks. 2- Can you connect 10 PCs in…
A: Ad-Hoc network Ad-Hoc network is a type of Multi-hop wireless network (MHWNs) nodes in network are…
Q: Show the design of 1-bit comparator Show the block diagram for 4-bit comparator Develop a look ahead…
A: As per guidelines I can answer only three sub-parts. I hope you will understand. Thank You.
Q: Design a 5x32 decoder using: a) 4x16 decoders with active-high Enables and minimum gates.
A: Designing 5x32 decoder using :- 4x16 decoders with active-high enable and minimum gates
Q: nition
A: Band stop filters are channel circuits that eliminate a band of frequencies called a stopband, from…
Q: What separates embedded systems programming from ordinary application development?
A: Intro An embedded programming language is a programming language that designers use in embedded…
Q: Could you perhaps provide a more in-depth breakdown of the metrics involved in the software…
A: Introduction: Well, one of the most important stages in software development is software…
Q: Distinguish between point-to-point ethernet and FDDI network protocols.
A: Introduction: In local area networks, Ethernet is the most commonly used network technology, and it…
Q: Please help me by pointing me to the correct address. main.c 1 #include 2 Instructions: 3 int…
A: #include <stdio.h> int main(void){ int n; printf("Enter the destination number: ");…
Q: Discuss briefly the different types of interruptions and explain how interrupts are important to…
A: Intro Interrupt and its type An interrupt is a signal sent to the CPU by hardware or software,…
Q: In this case, why is Access superior to Excel when it comes to keeping track of this data?
A: MS Access and MS Excel: MS Access and MS Excel are two programmes that may be used to create…
Q: What is one of the problems in machine learning? unbiased data biased data weak software strong…
A: Answer: Data bias in machine learning is a sort of blunder wherein certain components of a dataset…
Q: What is the impact of global cooperation on information management? What role does digital democracy…
A: Introduction: Global information management (GIM) is the discipline of science that is concerned…
Q: What role does a motherboard play in a computer?
A: Components of a computer system: Computers may be made up of distinct specialized parts and…
Q: Computer science Short answer List and describe the steps involved in data analysis.
A: Introduction: The process of analyzing, cleaning, manipulating, and modelling data with the…
Q: 10. Show the encryption of Cipher Text using the One-Time Pad from the data following. ( F* -&E*EN…
A: We need to show the encryption of given text, using one time pad.
Q: 1. Given the following, can you prove the unicorn is mythical? How about Magi- cal? and Horned?…
A: According to bartleby guidelines, i can solve only first question and his subparts. Please post it…
Q: (Rounding Numbers) Function floor may be used to round a number to a specific decimal place. The…
A: Program Explanation: 1) Implement the header file. 2) Using the namespace. 3) Declaring the integer.…
Q: Explain how assignment compatibility affects argument passing in a few words.
A: Methods: Methods are a set of statements that are combined to conduct an operation. The primary…
Q: Controlling which processes have access to the untrusted programme and which processes and data the…
A: Introduction: Confinement Assuming that the only activity of the programme is to compute the total…
Q: Computer science What are some of the privacy issues that customers may have while buying on a…
A: Introduction: Identity theft, financial fraud, and other issues can arise when personal information…
Q: What does it mean when a memory block has "address space"?
A: Introduction: An address space is a range of valid addresses in memory that is made accessible for…
Q: Discuss why it is necessary for Systems Analysts to model an information system's subject-domain…
A: Introduction: The primary goal of System Analysis was to determine whether or not the product met…
Q: AI is often used in pattern recognition, i.e. Technical Analysis. However, Technical Analysis…
A: Technical analysis, sometimes called charting or chart watching, is the practice of analyzing…
Q: What role does ethics play in information technology?
A: Introduction: The following are some of the most serious ethical challenges in data-driven…
Q: ter systems and their progress in terms of
A: Computer history begins around 2000 years ago in Babylonia (Mesopotamia), with the invention of the…
Q: Security subject. Why might vendors propose proprietary encryption methods rather than using…
A: "Proprietary encryption algorithms kept secret by their designers to enhance additional security are…
Please design this in frizing/tinkercad
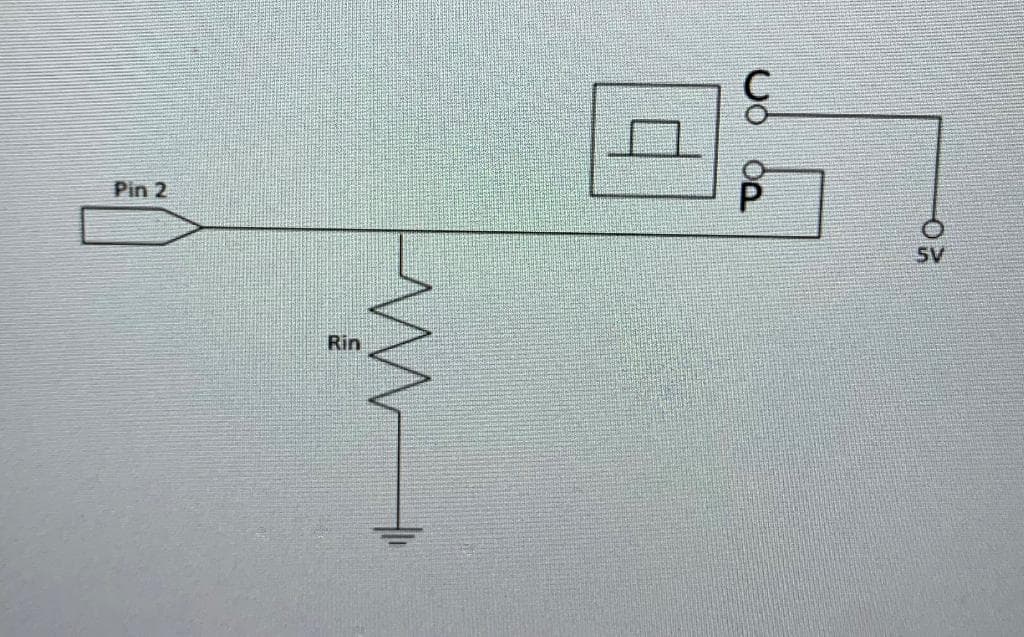
Step by step
Solved in 2 steps with 1 images

- 275. The term that means data is sent over four wires at the same time is a. 4S b. 4D c. 4W d. 4RSheet4 There is a buzzer connected to the 0 pin of PortB. Write a program that turns the buzzer on 3 different tones with 25% pulse time with the button at bit 0 of Port A, 50% pulse time with the button at bit 1 of Port A, and 75% pulse time with the button at bit 2 of Port A.Answer fast in 15 min.

