Please fix the code see picture for error.
Programming Logic & Design Comprehensive
9th Edition
ISBN:9781337669405
Author:FARRELL
Publisher:FARRELL
Chapter7: File Handling And Applications
Section: Chapter Questions
Problem 6PE
Related questions
Question
Please fix the code see picture for error. Thank you
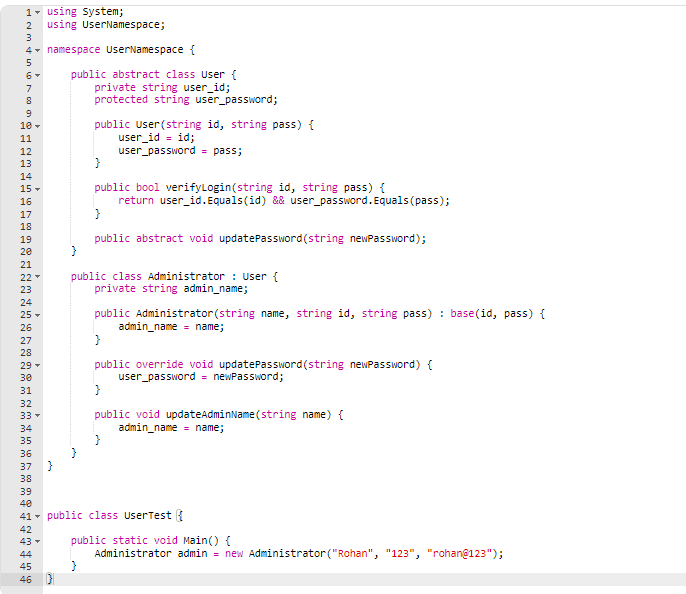
Transcribed Image Text:1▾ using System;
2 using UserNamespace;
3
4
5
6 -
7
8
9
10-
11
12
13
14
15-
16
17
18
19
20
21
22
23
24
25-
26
27
000
WN
stin
UND OHNEN 99
28
29 -
30
31
32
33 ▾
34
35
36
37
38
namespace UserNamespace {
$
public abstract class User {
private string user_id;
protected string user_password;
public User(string id, string pass) {
user_id = id;
user_password = pass;
}
public bool verifyLogin(string id, string pass) {
return user_id.Equals(id) && user_password. Equals(pass);
}
public abstract void updatePassword (string newPassword);
public class Administrator: User {
private string admin_name;
public Administrator (string name, string id, string pass) : base(id, pass) {
admin_name = name;
}
public override void updatePassword (string newPassword) {
user_password = newPassword;
}
public void updateAdminName(string name) {
admin_name name;
public static void Main() {
Administrator admin = new Administrator ("Rohan", "123", "rohan@123");
}
39
40
41 public class UserTest
42
43 -
44
45
46 }
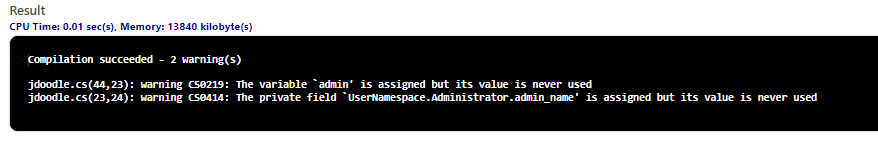
Transcribed Image Text:Result
CPU Time: 0.01 sec(s), Memory: 13840 kilobyte(s)
Compilation succeeded - 2 warning(s)
jdoodle.cs(44,23): warning (S0219: The variable `admin' is assigned but its value is never used
jdoodle.cs(23,24): warning (S0414: The private field `UserNamespace.Administrator.admin_name' is assigned but its value is never used
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 4 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage