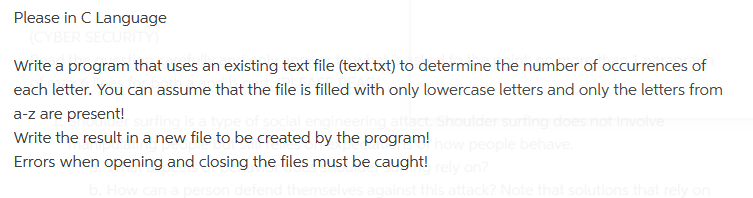
Please in C Language (CYBER SECURITY) Write a program that uses an existing text file (text.txt) to determine the number of occurrences of each letter. You can assume that the file is filled with only lowercase letters and only the letters from a-z are present! Shoulder surfing does not involve Write the result in a new file to be created by the program! how people behave. Errors when opening and closing the files must be caught! rely on?
Q: Examined are the many forms, benefits, and drawbacks of cloud data storage. (maximum of 250 words)
A: What is cloud data storage ? Cloud storage, a cloud computing paradigm that saves data on the…
Q: Figure 2. Binary-to-Gray Code converter. Figure 2 shows a binary-to-gray code converter. (Gray code…
A: X4 X3 X2 X1 X0 = 01110 X4 X3 X2 X1 X0 = 01110 X4 X3 X2 X1 X0 = 10101 X4 X3 X2 X1 X0 = 11100
Q: Wireless network flaws might lead to problems. Describe the effects of three of these issues on the…
A: Given: Wireless networks are prone to flaws that cause issues. Describe three of these concerns and…
Q: What are the three conditions that must be met in order for a network to operate in an efficient and…
A: Introduction: At this stage, production a planners decide how and where products will be…
Q: Why is the spiral model better than the waterfall model? Justify your position in three short…
A: We need to discuss why is the spiral model better than the waterfall model and describe the…
Q: What are the main distinctions between firewalls that are hardware-based and software-based? Is…
A: A firewall's software: An application that runs on a computer or server is a software firewall.…
Q: Think about how crucial wireless networks are in developing nations. Why do some businesses choose…
A: A wireless network is a computer network that uses wireless data connections between network nodes.
Q: Provide the type (I, R, or J) 1 0x, e.g., 0xAA230103) of the following instruction: SW $s1, 4($t2)…
A: Given : Instruction : SW $s1, 4($t2)
Q: demonstrate how trademark ownership and the freedom of expression are incompatible in the field of…
A: A trademark is a distinctive symbol, design, or phrase that distinguishes a product or service from…
Q: On the hard disk of a computer, files and directories may be created, analyzed, and managed by the…
A: INTRODUCTION: The file system is the area of the operating system that controls files and…
Q: What are a few advantages of storing data on the cloud? What are the many models, and what are each…
A: Introduction: Essential cloud storage is a distributed computing strategy in which data is stored…
Q: What are the advantages and disadvantages of storing data on the cloud? Give some examples of…
A: Storage of clods: We can access data stored in the cloud without any additional hardware or…
Q: What are the benefits and drawbacks of each generation of networks?
A: 1G Technology:- 1G stands for first-generation. It can be used in mobile phones as a different…
Q: Write a C++ program that Ask user to enter an integer number and then determine whether the number…
A: We need to write a C++ program that Ask user to enter an integer number and then determine whether…
Q: Describe the advantages and disadvantages of the different Wi-Fi security measures.
A: A wireless system is far more challenging to get around or get past because there are no wires to…
Q: What are the main benefits of reusing application systems as opposed to creating custom software to…
A: We will first familiarize ourselves with both ideas. Reusing existing application systems Assume you…
Q: epts of integrity.
A: Still, you probably remember receiving some information about your academy's academic honesty policy…
Q: What are a few recommended firewall management techniques? Explain.
A: introduction: A firewall serves as a barrier to keep out traffic that could be intended to…
Q: An example will help to clarify the concept of an operating system as a resource allocator.
A: Given: An operating system allocates resources.
Q: These days' developing nations need cellular networks more than ever. In certain places, physical…
A: Introduction: The widespread use of wireless LANs is largely attributable to their practicality,…
Q: How may discrete data be created from a still image? How is video's source code produced?
A: The Answer is in given below steps
Q: What examples of dynamic programming are there?
A: Introduction: Dynamic programming: Efficient approach of problem/subproblem solving Breaks/divide…
Q: Digital memory comes in a variety of forms, including cache memory, random access memory (RAM),…
A: A hard disk drive (HDD) is an obsolete storing contraption that uses mechanical platters and a…
Q: What are some of the challenges faced by quantum computing?
A: Better algorithms and hardware are both necessary for quantum computing. The challenges facing…
Q: What Constitutes the Components of a Computer System? Briefly describe what you're aiming to…
A: Introduction: A type of semiconductor memory called DRAM is used to store data or programme code…
Q: Use your own words to define "sub-band coding" in the context of acoustics and describe the role it…
A: Given: Give your own explanation of what sub-band coding in acoustics means and how it affects MP3…
Q: Is it possible to formalize the object-oriented programming analysis and design process?
A: Given: A system is represented as a group of connected components. The class, state (its data), and…
Q: What issues arise from non-integrated information systems
A: Non-integrated information systems: Separate or not integrated EDI is a standalone portal that is…
Q: How may discrete data be created from a still image? How is video's source code produced?
A: Images come in two varieties. 1.Analog 2.Digital Analog: Analog photographs resemble the images that…
Q: For the given IP address 196.62.146.174/27, answer the following questions: a. Subnet Mask b. Number…
A: Answer: Given 196.62.146.174/27 And we need to find the following answer
Q: What are the main distinctions between firewalls with software and those with hardware? Is one of…
A: A Firewall is an organization security gadget that screens and channels approaching and active…
Q: In a dual core processor, consider first four letters of your name coming as p
A: The answer is
Q: e routing? Describe the distance vecto
A: Solution - In the given question, we have to tell what is routing and also describe the distance…
Q: Look at how wireless networks are used in developing nations. Why do some businesses choose wireless…
A: Advantages of Wireless Networks Efficiency improvement: Faster information movement inside firms and…
Q: Please make a table that contrasts engineering and computer ethics and provides five examples of…
A: Answer is in next step.
Q: Explain The Distributed Cellular Genetic Algorithm.
A: Genetic Algorithm : Genetic algorithms can be defined as iterative algorithms that start by randomly…
Q: A list of the top five network topology types should be included. Which of them, in your view, has…
A: Introduction: 1) Signals aren't routed to every workstation like in Bus topology, which enhances…
Q: What is the main distinction between procedural and object-oriented programming?
A: Programming is a a technique to create set of instructions executed by computer system to achieve…
Q: What are the most crucial things to think about while implementing an ALL-IP network? List the top…
A: The All-IP network (AIPN) is a development of the 3GPP framework to satisfy the rising needs of the…
Q: What are a few recommended firewall management techniques? Explain
A: To prevent problems in the future, it's crucial to take potential security threats into account…
Q: According to section 5-3 in the PIC Mid-Range MCU Family Reference Manual, how is the central…
A: Central Processor Unit (CPU):The central processing unit (CPU) of a computer is one of its…
Q: When you refer to the "Principle of Non-Repudiation," what do you actually mean?
A: Principle of Non-Repudiation: If you employ non-repudiation, you won't be able to challenge the…
Q: demonstrate how trademark ownership and the freedom of expression are incompatible in the field of…
A: Introduction: A trademark is distinguishing sign, design, or phrase that identifies a product or…
Q: Q23. The following Adjacency Matrix represents 123456 1030000 2000000 30 700 50 40 10000 5000 900…
A: The question has been solved in step2
Q: Topic: Investigating the Impact of Implementing Cloud Technology within an Organisation 1.Data…
A: 1. Data Analysis and Interpretation :- For conducting these type of research on the topic…
Q: Is it accurate to say that a digitizer is a piece of technology that converts analog data to…
A: The Written answer is in step-2.
Q: What are the advantages, disadvantages, and probable future developments of cloud data storage? Give…
A: Introduction: To begin, cloud computing is the practise of storing data and accessing computer…
Q: Exactly what is the routing? Describe the distance vector routing in detail.
A: Routing happens in the Networking layer and is the process of choosing a path across one or more…
Q: These days' developing nations need cellular networks more than ever. In certain places, physical…
A: Definition: Wireless networks enable mobile clients to access real-time data while roaming your…
Q: Exactly what is the view? What does the word "view" exactly mean? Anytime the data described in a…
A: Introduction: In reality, a view is a SQL a statement that is recorded in the database under a…
Step by step
Solved in 3 steps with 3 images

- 1. Write a program that asks the user for the name of a file. The program should display only the 3 lines of the file's contents. If the file contains less than 3 lines, it should display the file's entire contents. Use the file: lorem_ipsum.txt to test your program. Comment your source code and describe your code to someone who may be viewing it for the first time. PLACE SCREENSHOTS OF THE PYTHON CODE AND ALL I/O BELOW. Please use Python ProgrammingWrite a program which reads the first two characters from the file “chars.txt” and writes thesum of their ASCII code values as a number into “codesum.txt”. Use an editor to create theinput file “chars.txt”. Your program is responsible to create the output file “codesum.txt”.You can safely assume that the content of the input file will be valid.(Please write in C programming language).Chapter 4. PC #6. File Letter Counter (page 264) Write a program that asks the user to enter the name of a file, and then asks the user to enter a character. The program should count and display the number of times that the specified character appears in the file. Class name: FileLetterCounter Hints: Hint 1. To read a single character from the keyboard, you need to read a full line and then take the first character in position 0. Hint 2. To count the occurrences of a given characters in a file you need to read the file line-by-line using a while loop, then for each line check all characters in all positions and increment the character counter for each occurrence. This will require to have a for-loop nested inside the while-loop. Here is a working code Please modify it so it passes the test cases because I run it it does not work: mport java.io.File;import java.io.FileNotFoundException;import java.util.Scanner;public class FileRead {public static void main(String[] args)…
- Chapter 4. PC #6. File Letter Counter (page 264) Write a program that asks the user to enter the name of a file, and then asks the user to enter a character. The program should count and display the number of times that the specified character appears in the file. Class name: FileLetterCounter Hints: Hint 1. To read a single character from the keyboard, you need to read a full line and then take the first character in position 0. Hint 2. To count the occurrences of a given characters in a file you need to read the file line-by-line using a while loop, then for each line check all characters in all positions and increment the character counter for each occurrence. This will require to have a for-loop nested inside the while-loop. Here is a working code Please modify it so it passes the test cases because I run it it does not work: Also I do not need Goodbye And I run it through hypergrade which it has all the test cases it does not work. mport java.io.File;import…Chapter 4. PC #6. File Letter Counter (page 264) Write a program that asks the user to enter the name of a file, and then asks the user to enter a character. The program should count and display the number of times that the specified character appears in the file. Class name: FileLetterCounter Hints: Hint 1. To read a single character from the keyboard, you need to read a full line and then take the first character in position 0. Hint 2. To count the occurrences of a given characters in a file you need to read the file line-by-line using a while loop, then for each line check all characters in all positions and increment the character counter for each occurrence. This will require to have a for-loop nested inside the while-loop.Chapter 4. PC #6. File Letter Counter (page 264) Write a program that asks the user to enter the name of a file, and then asks the user to enter a character. The program should count and display the number of times that the specified character appears in the file. Class name: FileLetterCounter Hints: Hint 1. To read a single character from the keyboard, you need to read a full line and then take the first character in position 0. Hint 2. To count the occurrences of a given characters in a file you need to read the file line-by-line using a while loop, then for each line check all characters in all positions and increment the character counter for each occurrence. This will require to have a for-loop nested inside the while-loop. Test Case 1 Please enter the file name or type QUIT to exit:\nQUITENTER Test Case 2 Please enter the file name or type QUIT to exit:\nbadfilename.txtENTERFile: badfilename.txt does not exist.\nPlease enter the file name again or…
- Chapter 4. PC #6. File Letter Counter (page 264) Write a program that asks the user to enter the name of a file, and then asks the user to enter a character. The program should count and display the number of times that the specified character appears in the file. Class name: FileLetterCounter Hints: Hint 1. To read a single character from the keyboard, you need to read a full line and then take the first character in position 0. Hint 2. To count the occurrences of a given characters in a file you need to read the file line-by-line using a while loop, then for each line check all characters in all positions and increment the character counter for each occurrence. This will require to have a for-loop nested inside the while-loop. Here is a working code. Modify this code so it will pass the test cases. import java.io.File;import java.io.FileNotFoundException;import java.util.Scanner;public class FileRead {public static void main(String[] args) throws FileNotFoundException…D) Create a program that will read a text file with the answers to 10 multiple-choice questions and compare them to the correct answers stored in a tuple. correct answers: 'A','B','C','D','D','C','B','A','A','C' After the answers have been read from the file, the program should display a message indicating whether the answer stored on the file was correct or not. If the answer was was incorrect, display the correct answer. The program should display the total number of correct and incorrect answers, followed by a message of "Good job!" if the file has 8 or more correct answers. PYTHONThis class prints the first several lines of a file. The default is to print 5 lines, but the -n flag can specify a different number. If no file is specified on the command line, read from standard input. The code bekoow is to help get started. #include <stdio.h> #include <stdlib.h> // You may assume that lines are no longer than 1024 bytes #define LINELEN 1024 static void usage (void); int main (int argc, char *argv[]) { return EXIT_SUCCESS; } static void usage (void) { printf ("head, prints the first few lines of a file\n"); printf ("usage: head [FLAG] FILE\n"); printf ("FLAG can be:\n"); printf (" -n N show the first N lines (default 5)\n"); printf ("If no FILE specified, read from STDIN\n"); }
- Python Code: Below is an open link to file needed in this program Spots: https://drive.google.com/file/d/1uaqwxYYn4AHJlFB0ukxm3PD8ISoakz6F/view?usp=sharing libraries numpy as np and matplotlib.pyplot as plt must be imported and then used. Write a program which reads the data from the file spots.txt (linked above), and then calculates the mean, median, mode and standard deviation of the data. Using the above information, the program should then plot a histogram of the number of sunspots/month distributed over 50 bins. Use the plt.hist() function to help you with this.I have a "user.json" file that looks like this { "something@somewhere.com": "maybe", "john@beatles.uk": "lennonj!", "paul@beatles.uk": "mccartney", "mick@rollingstones.uk": "jaggerm!" } using java script i have to parse this file and then check this email and file conbinations against user input This is the code i m using to parse the file. function lookUpCredentials(filePath, cb) { fs.readFile(filePath, (err, fileData) => { if (err) { return cb && cb(err); } try { const object = JSON.parse(fileData); return cb && cb(null, object); } catch (err) { return cb && cb(err); } }); } lookUpCredentials("./user.json", (err, data) => { if (err) { console.log(err); return; } credentials = data; }); and this is the code i m using to get input from the user app.post('/login', (req, res) => { let username =…in C++ Im triying to open a text file using argc and argv[] without using strings i can only use the c strings such as char test[100]; how would i do that? this is what i have so far #include <iostream>#include <fstream>using namespace std; int main(int argc, char *argv[]){string filename = argv[1];ifstream input (argv[1]);return 0;}



