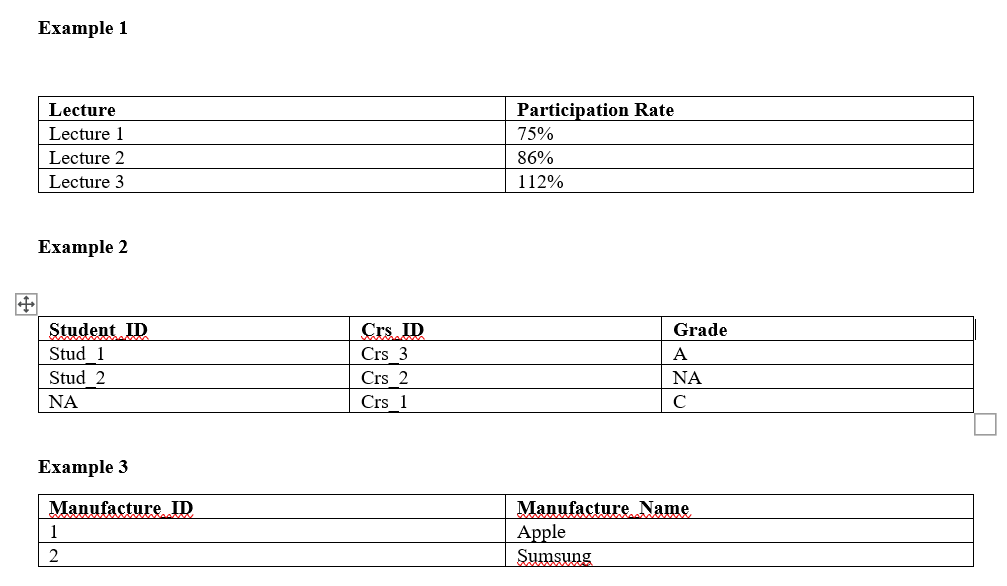
Please look at Example 1-3 in the image and explain which type of Integrity Constrains Violation do they belong to.
Q: You have an Active Directory forest named csmtech.local and two Active Directory domains in the…
A: There are usually two scenarios that people want to pursue: Translation of fully qualified DNS names…
Q: Your data warehouse team is debating whether a prototype should be carried out before…
A: A data warehouse is an integrated, subject-oriented, time-variant and non-volatile database that…
Q: When the cursor is on the initial letter of a word in vim, you type x then p. Describe what…
A: The answer is given below step.
Q: How do you change the Text property on a form?
A: To change the Text property on a form.
Q: rvice attack is one in which a large number of persons try to concurrently bring down a website. How…
A: One person can slow down a network of sites. It all depends on the attack methods/types. Previous…
Q: f
A: resend the question
Q: How would you briefly summarize the development of wireless LAN technology?
A: The solution is given in next steps for your reference.
Q: You must write a 2-Dimenional loop to programmably replace the character. To do this you must list…
A: Program Approach:- 1. Include header file 2. Define macro 3. Use the for loop and check the…
Q: According to you, what aspect of software engineering is the most important?
A: Software engineering principles are a collection of approaches, styles, philosophies and best…
Q: image segmentation and edge detection using contrast and contrast. Why is edge detection so…
A: Edge Detection Segmentation: Edge detection is a method of image processing that locates the edges…
Q: To answer this question, let's take an example of a university faculty with six professors (3 men…
A: Answer is in next step.
Q: Given the following directed graph, how m there from B?
A: Number of Cycles: 1) B itself contains a self-loop and it can be considered as a cycle. 2) A-B has…
Q: Possible thesis topic in the field of Computer Engineering. Describe it completely.
A: Introduction: Careers in computer engineering are on the upswing. Designing, developing, and…
Q: When the cursor is on the initial letter of a word in vim, you type x then p. Describe what…
A: Actually, the data provided is The current character, which is the first letter of the word, will be…
Q: Which four advantages of discrete event simulation stand out?
A: Discrete event simulation (DES) is the method of codifying the behaviour of a complex system as an…
Q: What function does the creation of software serve? Do you think the software development process…
A: Introduction: It is impossible to exaggerate the potential of software development to create and…
Q: What categories of triggers are there? What function do they fulfill? In Access 2016, how do you…
A: Answer is in next step.
Q: Using the Local Area Network (LAN), individuals and computers in the same region may communicate…
A: Introduction The abbreviation for "Local Area Network" is "LAN." A Local Area Network (LAN) is a…
Q: What use does discrete event simulation serve?
A: Answer:
Q: Did you ever wonder what the purpose of the Atlas Computer was?
A: The question has been answered in step2
Q: How is the boot-up strategy for the router specified?
A: The following steps make up the boot procedure for the router: Turn the router's power switch to the…
Q: Describe how dependability and availability are related in the context of computer networks. For the…
A: Introduction: A network, in its broadest sense, is any connected collection of individuals or…
Q: which of the following problems now affects the software engineering community the most
A: Given: We have to discuss which of the following problems now affects the software engineering…
Q: Is it possible to define the primary goal of software development? What or who are you referring to?
A: The answer to the question is given below:
Q: 5. Trace the output of the following code. Writing PHP Function with Parameters function…
A: Dear student, the answer is provided below.
Q: Investigations of wireless networks in poor countries are important. Wireless networks are being…
A: One sort of computer network is known as a wireless network, and it differs from other types of…
Q: How is a message authentication hash value protected? Can a MAC algorithm be exploited in the…
A: MAC is also known as Message Authentication Code.
Q: Is it possible to define the primary goal of software development? What or who are you referring to?
A: The answer to question is given below:
Q: Of the following three, which three are examples of discrete event simulations?
A: Given: Identify three applications for discrete event simulation. Modeling network protocols: The…
Q: Utilize a named entity recognition software to demonstrate how to use it.
A: INTREODUCTION: Named entity recognition focuses on identifying the exact meaning of a word and…
Q: You've decided to order a pizza for dinner. The restaurant you're ordering from has three sizes of…
A: The C++ code is given below with code and output screenshot You can delete this line from code if…
Q: How is edge computing implemented?
A: Edge computing is implemented in different ways, but one of the most common implementations is…
Q: What does "green computer" mean?
A: The answer is given in the below step
Q: e definition of the t
A: Computer: A computer is an electronic device that stores and processes data, usually in a binary…
Q: A communication adapter is connected to a phone line via a modem. What is the function of this…
A: A communication adapter allows a computer to connect to other computers via phone line. The most…
Q: Do software developers have a professional obligation to provide maintainable code even if their…
A: The question has been answered in step2
Q: For instance, if you are launching a media company and require graphic designers and media…
A: Data that is currently in use is copied using a backup storage device: Making copies of data that is…
Q: Which mental image do you have of an email? An email's journey begins and ends in the same place.…
A: Email: Also known as electronic mail, email sends information or data from one system to another.…
Q: When you think about email, what images spring to mind? How does an email go from point A to point B…
A: Getting started using email: It is described as a service procedure that enables us to transmit…
Q: How may services and applications be hosted in a cloud-based network?
A: Virtualization is how cloud hosting works. It employs a technique known as cloud servers to divide a…
Q: A smart modem may automatically dial, reject, and respond to incoming calls. Who gives the modem the…
A: Here is to discuss an intelligent modem has the ability to dial, refuse, and reply to calls that are…
Q: Examine the benefits and drawbacks of multipurpose microcontroller pins.
A: A micro controller is a somewhat small device that controls how various parts of a computer system…
Q: Which mental image do you have of an email? An email's journey begins and ends in the same place.…
A: This is the solution. An email is sent via the Simple Mail Transfer Protocol (SMTP) and then…
Q: Since its introduction, it has been extensively implemented into third- and fourth-generation…
A: DBMS is also known as database management system.
Q: What specifically does software engineering's foundational theory ignore? Explain?
A: Concept for Software Engineering Let's start by defining software engineering. Software engineering…
Q: Your data warehouse team is debating whether a prototype should be carried out before…
A: If a prototype is created, it should be used to test certain business hypothesis and to ensure that…
Q: There might be two identical files in your account. Assume that the current directory is called…
A: Current Directory: The current directory, also known as the a working directory or current working…
Q: A distributed denial of service attack is one in which a large number of persons try to concurrently…
A: Attack causing widespread denial-of-service (DDoS): The DDoS attack was devised to generate attacks…
Q: What may happen if the mouse is left on an incorrect line of code for a long time?
A: A Mistake in Code Called: "A code error is considered a defect when it is discovered by a tester, a…
Q: Which four advantages of discrete event simulation stand out?
A: Answer:
Please look at Example 1-3 in the image and explain which type of Integrity Constrains Violation do they belong to.
Trending now
This is a popular solution!
Step by step
Solved in 4 steps with 4 images

- Computer Science A pharmaceutical company writes contracts with its chemical suppliers that ensure each container has the proper amount of chemical within some allowable range. For example, a one liter container is permitted to contain between 997 cm3 and 1,003 cm3. Design a test suite for testing the company’s quality control using a liter container of a different amount of chemical for each different test case.Computer Science Erd (Entity relation diagram) Make an ER diagram about an online scheduling program of appointments between doctors and patients - patients - doctors - appointments between doctors and patients - payments -reports files that users(doctors or patients) make it. and can be accessed by the adminER diagram needed
- ABC is a pharmaceutical company that recruits volunteers for clinical trials on drugscurrently under development at the company. The company conducts multipleclinical trials concurrently. Each clinical trial is assigned a trial code together with description of theclinical trial, start date, end date, and the lead scientist. Each clinical trialinvolves at least one treatment, and each treatment belongs to only one trial.Treatment has its conduct date. When volunteers sign up for a treatment of a clinical trial, their contact detailsincluding full name, address, contact number, email address, as well as theirunique volunteer number are recorded. Each volunteer is involved in at leastone treatment, while each treatment is tested on at least 30 volunteers. In addition, medical details for each volunteer including weight, height, bloodtype, race, gender, and medical condition are also recorded separately. At each treatment each volunteer involves a specific drug of certain type,…ABC is a pharmaceutical company that recruits volunteers for clinical trials on drugscurrently under development at the company. The company conducts multipleclinical trials concurrently. Each clinical trial is assigned a trial code together with description of theclinical trial, start date, end date, and the lead scientist. Each clinical trialinvolves at least one treatment, and each treatment belongs to only one trial.Treatment has its conduct date. When volunteers sign up for a treatment of a clinical trial, their contact detailsincluding full name, address, contact number, email address, as well as theirunique volunteer number are recorded. Each volunteer is involved in at leastone treatment, while each treatment is tested on at least 30 volunteers. In addition, medical details for each volunteer including weight, height, bloodtype, race, gender, and medical condition are also recorded separately. At each treatment each volunteer involves a specific drug of certain type,…I need an ER diagram for the following information For Hotel: HotelID (unique) and ANoOfRooms (number of rooms in the hotel) For Hotel: HotelID (unique) and ANoOfFloors (number of floors in the hotel) For each Room: RNO (partially unique, unique in the hotel) and ANoOfBeds (number of beds in the room) For each customer: CID (unique), CName (unique), For each manager: MID (unique), MFullName (composed of MFName and MLName), MBonus (not every manager has a bonus), MSalary, multiple MPhones For each employee: EID (unique), EName Each hotel has one or more rooms Each room is located on exactly one floor Each room is cleaned by one or two employees Each employee cleans 1-3 floors Each employee cleans 6-15 rooms Each customer has one or many rooms Each customer has booked one or mamy rooms Each room is booked by a customer or no one Each floor has one or many rooms Each manager resides in exactly one room Each manager resides on exactly one floor Each hotel either has one manager residing…
- Topic: UML Diagrams Convert this activity diagram into a sequence diagram.(Must be done in MatLab) Assume you have a four-column matrix named BoltStock25 containing information about quarter-inch-diameter bolts your company has in stock. The first column contains the bolt length The second column contains the number in stock The third column contains the minimum stock that should be maintained (based on usage) The fourth column contains the maximum number allowed in stock (based on storage space). You wish to determine how many bolts of each type to order according to the following guidelines: If the number in stock falls to less than the minimum stock desired plus 50 for any specific length, more of that length should be ordered. All orders must be in multiples of 100 of any specific length. The current stock plus the number ordered for a specific length must not exceed the maximum allowable stock. When an order is placed for a specific length, the total stock should then be as close as possible to the maximum allowed stock. You may assume that the…Please make a crowsfoot diagram about the er diagram below. Same context.

