Q1) Write a C++ program to compute the value of S using function, where the value of S(x, n)= X/2! - (X')/4! + (X/6! - ( X')/8! . +( X@-1)/2n!. Define the function Compute_S(x, n) to compute the value of S, given the value of x, andn as parameters list. Use a function called pwr(x.y) to compute xY terms and a function called Fact(n) to compute factorial n (i.e. n!) in the equation of S.
Q1) Write a C++ program to compute the value of S using function, where the value of S(x, n)= X/2! - (X')/4! + (X/6! - ( X')/8! . +( X@-1)/2n!. Define the function Compute_S(x, n) to compute the value of S, given the value of x, andn as parameters list. Use a function called pwr(x.y) to compute xY terms and a function called Fact(n) to compute factorial n (i.e. n!) in the equation of S.
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter6: Modularity Using Functions
Section: Chapter Questions
Problem 7PP: (Numerical) Heron’s formula for the area, A, of a triangle with sides of length a, b, and c is...
Related questions
Question
i need the answer quickly
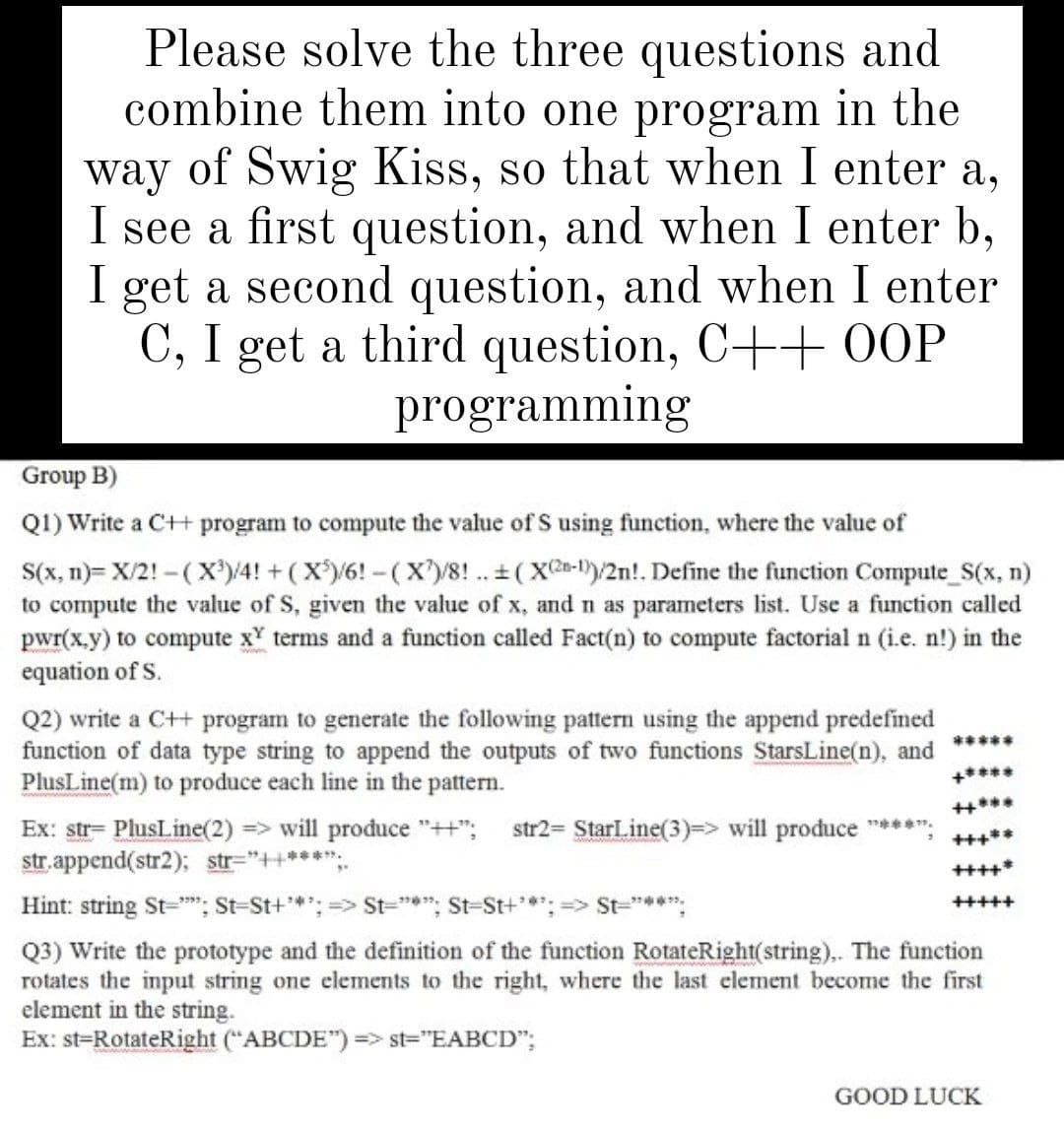
Transcribed Image Text:Please solve the three questions and
combine them into one program in the
way of Swig Kiss, so that when I enter a,
I see a first question, and when I enter b,
I get a second question, and when I enter
C, I get a third question, C++ 0OOP
programming
Group B)
Q1) Write a C+H program to compute the value of S using function, where the value of
S(x, n)= X/2! - (X®)/4! + ( X)/6! - (X)/8! .. + (X-1)/2n!. Define the function Compute_S(x, n)
to compute the value of S, given the value of x, and n as parameters list. Use a function called
pwr(x.y) to compute x' terms and a function called Fact(n) to compute factorial n (i.e. n!) in the
equation of S.
Q2) write a C++ program to generate the following pattern using the append predefined
function of data type string to append the outputs of two functions StarsLine(n), and
PlusLine(m) to produce each line in the pattern.
*****
+****
Ex: str= PlusLine(2) => will produce "++";
str. append(str2); str="++***";.
str2= StarLine(3)=> will produce ****:
+++**
++++*
Hint: string St="; St-St+*; => St="*"; St-St+*: => St="***:
+++++
Q3) Write the prototype and the definition of the function RotateRight(string),. The function
rotates the input string one elements to the right, where the last element become the first
element in the string.
Ex: st=RotateRight ("ABCDE") => st="EABCD";
GOOD LUCK
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 4 steps with 3 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning