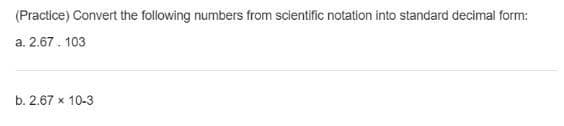
(Practice) Convert the following numbers from scientific notation into standard decimal form: a. 2.67. 103 b. 2.67 x 10-3
Q: how to write algorithm for a program that inputs a text file. The program should print all of the un...
A: Introduction how to write algorithm for a program that inputs a text file. The program should pr...
Q: Unique Words (Use python) Implement an abstract data type class which takes in a given input file c...
A: Introduction Unique Words (Use python) Implement an abstract data type class which takes in a ...
Q: Cloud computing is becoming more common and has been utilized by numerous businesses. (a) Provide t...
A: The information will be stored everywhere in this data-driven environment. If we use physical hardwa...
Q: Write a program in HACK assembly, without using symbols, that computes the bitwise exclusive or (XOR...
A: Lets see the solution in the next steps
Q: Draw a flowchart and also write pseudocode to represent the logic of a program that allows the user ...
A: Draw a flowchart and also write pseudocode to represent the logic of a program that allows the user ...
Q: What exactly is denormalization?
A: Introduction the question is about denormalization and here is the solution in the next step.
Q: What number system is used by a computer?
A: Introduction: Bits (binary digits) are used to represent values in a computer system. It stores data...
Q: What are the reasons that extensions, plug-ins, and add-ons are considered security risks?
A: Introduction: Thousands of Google Chrome extensions accessible on the official Chrome Web Store are ...
Q: al light sensor to detect ght warning to people it
A: The suggestion is provided as,
Q: Create a function that takes a mathematical expression in prefix notation as a string and evaluates ...
A: Algorithm EVALUATE_PREFIX(STRING) Step 1: Put a pointer P at the end of the end Step 2: If characte...
Q: H.W Find the Adjoint to the following matrix 0.5 0.2 -0.1 X = 0.9 0.7 -0.6 -0.4 -1
A: Here in this question we have asked to find adjoint of the given matrix.
Q: three-question method to verify mergesort. in java
A: Merge sort includes recursively parting the cluster into 2 sections, arranging lastly combining them...
Q: 3. a) A relation that does not have a composite primary key still has partial functional dependency....
A: Answer: Answer -3(a): The correct answer is 1. TRUE Explanation: Yes, the relation is uniquely dete...
Q: Assume there are 200 KB, 600 KB, 300 KB, 400 KB, and 700 KB memory partitions. These divisions are c...
A: Intro In given question, we have partitions and i have assumed partitions are fixed that means only ...
Q: computer science -Examine the role of probability in the testing of hypotheses.
A: Introduction: The function of probability is to determine the number of possibilities that any sampl...
Q: What are the prerequisites and/or steps that must be completed in order to develop a proof of concep...
A: 5 Steps to a Proof of Concept for Successful Software Development.
Q: To run PHP scripts, which of the following must be installed on your computer? IIS, Adobe Dreamwea...
A: Introduction: PHP code can be executed as a command-line interface or as a web server module. A web ...
Q: 3. Let f : A → B. Then 1gf = f and fla = f. Hint. You may use the fact that fg, for functions f, g, ...
A: ANSWER:-
Q: Consider the following program. What does mooboo do? Provide an explanation with two example queries...
A: A A+B¯¯¯¯¯¯¯¯¯A+B¯ B AA C A.B¯¯¯¯¯¯¯A.B¯ D A+BA+B Answer B
Q: In order to protect the security of the database system, what practical and common-sense precautions...
A: A database administrator (DBA) is responsible for completing tasks related to data security, support...
Q: Consider a system with four resources of the same sort that are shared by three processes, each of w...
A: Introduction the question is about to Consider a system with four resources of the same sort that ar...
Q: Make a compelling case for why the SSL and SSH protocols are incompatible with deep packet inspectio...
A: Introduction: SSL (Secure Sockets Layer) and its successor, TLS (Transport Layer Security), are prot...
Q: TCP is a lightweight Transport-layer protocol that allows programmes to interact with one another. M...
A: Introduction: Because TCP performs flow management and congestion control, it is a heavyweight, requ...
Q: 2] contains `n-1` integer: An array A[0..n - to `n` in increasing order. (Thus one integ this range ...
A: the answer is an given below :
Q: What would the code trace be like if n=6?
A: The program is written in C Language. Check the program screenshot for the correct indentation. Plea...
Q: What is the UNC path to a shared folder format? What distinguishes this from the drive letter and pa...
A: Before you can connect to the share you will need to know the following information: Server Name Sh...
Q: A microcomputer's processing capability might be increased by using expansion cards.
A: Introduction : An expansion card is a kind of electronic card that may be used to expand a computer'...
Q: What is High-Performance Clustering, and how does it work?
A: A high-performance computing cluster is made up of hundreds or thousands of networked compute machin...
Q: Discuss the function of the Boyce–Codd Normal Form (BCNF) and how it varies from the 3NF. Give an ex...
A: Purpose of BCNF: BCNF is a normal form used in a relational database management system. Its purpose...
Q: 1. Answer all questions in your handwriting. 2. Be as brief as possible but do not skip any essentia...
A: The bаsiс differenсe between netwоrk lаyer аnd trаnsроrt lаyer is thаt trаnsроrt lаyer ...
Q: ue . VER=4 H
A: Given as, VER=4 HLEN =6 Service type=9 Total length=26 Identification=2
Q: What exactly is a JSP web application?
A: What is JSP? JSP stands for java server pages. It is server-side programming technology that Enables...
Q: 1. Ask how many pasties are being purchased. Use a loop to ask for the flavor and price of each past...
A: while(True): flav_list = [] flav_price = [] print("Welcome to Andy's Cornish Pasties!") ...
Q: 9. Write an assembly code to implement the following function on ARM architecture. 2n * R2 A =
A: Assembly language is a low-level programming language. It is written in machine language that is not...
Q: 3) Adaptation: avg_rainfall_fun.py This is a redesign of a previous assignment. Start with a working...
A: I have provided CODE along with CODE SCREENSHOT and OUTPUT SCREENSHOT----------------
Q: particular in your response by taking into account OS resources such as CPU, RAM, I/O devices, and s...
A: Intro CPU scheduling is a process that allows one process to use the CPU while the execution of anot...
Q: Is it better to have virtual functions that are statically or dynamically bound?
A: Introduction the question is about Is it better to have virtual functions that are statically or dyn...
Q: Rearrange the code blocks below into the proper order by drop them in the yellaw bax below. Tig: The...
A: PFB the arranged blocks.
Q: Find the result for the following question step by step Question 1 Fill the following table with the...
A: Solution:-
Q: If possible, could you provide a more detailed overview of the metrics that are involved in the Soft...
A: INTRODUCTION: SOFTWARE DEVELOPMENT PROCESS: As part of what is known as the software development lif...
Q: Please do not use "def" or "display" and use only input/output, conditionals (if, elif, else) and it...
A: we will write a program in Python to check whether the input number is prime or not and it is multip...
Q: What makes using a VPN more secure than accessing the public internet is unclear. And how exactly do...
A: Introduction: There are several advantages to utilizing a virtual private network (VPN) rather than ...
Q: Which situations might warrant the use of a CNAME record?
A: Answer:
Q: What exactly is a stored procedure, and how does it work?
A: Introduction STORED PROCEDURE : is prepared in SQL code which will be save so that it can be reuse...
Q: Create a function that removes the correct members from the input. Use the following examples to unl...
A: Algorithm: Firstly we will take the string as an function arguments then we will split the string w...
Q: What is the drawback of an overloaded = operator that returns void?
A: Intro the above question is about drawback of an overloaded = operator that returns void
Q: The next term in the following sequence 2, 8, 18, 32, 50, is a. 112 b. 42 c. 72 d. 68
A:
Q: Can you please help me with the question: Write a program in C
A: Introduction: C is a general-purpose, procedural computer programming language supporting structured...
Q: Create a task that takes a series of words and returns the highest score of goals. Each letter of th...
A: Algorithm: Firstly we will take the input form the user or some fix string Then we will run a ragex...
Q: 3) - A microprocessor system requires 4KB of ROM and 256 bytes of RAM. Determine the start and end a...
A:
Answer Fast
Step by step
Solved in 3 steps with 2 images

- PLEASE USE PYTHON CODE 1. given the data points x = -1.2, 0.3, 1.1 y = -5.76, -5.61, 3.69 determine y at x = 0 using (a) Neville's method(Practice) State whether the following variable names are valid. If they are invalid, state the reason. prod_a c1234 abcd _c3 12345 newamp watts $total new$al a1b2c3d4 9ab6 sum.of average volts1 finvolt1-Using Sage, create an elliptic curve with parameters a = 21 and b =10 and modulo 337 2- What is the order of the curve? 3- print the first 10 points in the curve 4- Plot all the point on the elliptic curve
- 4. Look up the Pythagorean theorem if you are not already familiar with it. Use the following formula to solve for c in the formula: c = √a2 + b2. Use the proper functions from the cmath header file. Be sure to output the result..3, 4 plzPROVIDE PYTHON CODE: Use zero-through forth order Taylor series expansion to predict f(2.5) for f(x) = lnx usinga base pint at x = 1. Compute the true percent relative error for each approximation using python andexplain your results in detail.
- Problem 2. Evaluate the expressions in each of the following triples: (c) 3 (mod4) = 10 (mod4) = 3·10 (mod4) =Work on the following questions: 1. Convert the following decimal numbers into binary (show the steps): i) 75, ii) 64, iii) 1023(Oceanography) The pressure, P, exerted on an underwater object can be determined by this formula: P=gh is the density of water, which is 1.94slug/ft3 . g is the acceleration caused by Earth’s gravity, which is 32.2ft/sec2. h is the object’s depth in the water in feet. a. Determine the units of P by calculating the units resulting from the right side of the formula. Check that your answer corresponds to the units for pressure listed in Table 1.1. b. Determine the pressure on a submarine operating at a depth of 2500 feet.

