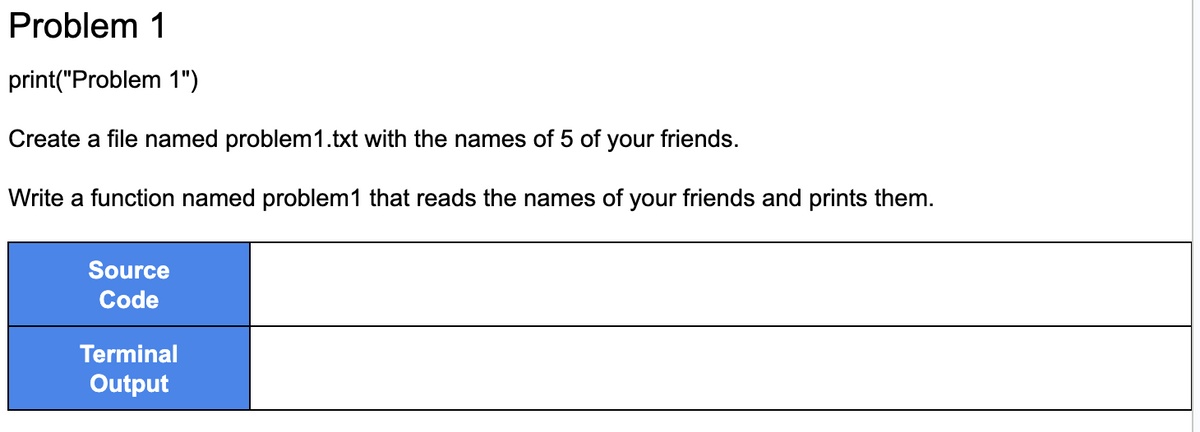
Problem 1 print("Problem 1") Create a file named problem 1.txt with the names of 5 of your Write a function named problem1 that reads the names of your friends and prints them. Source Code Terminal Output friends.
Q: What exactly is the point of creating a prototype in the field of software engineering?
A: What exactly is the point of creating a prototype in the field of software engineering?
Q: Give an example of how virtual servers are used in education and explain how they are used.
A: Introduction: Virtual servers have revolutionized the way education is delivered and received by…
Q: A poorly made web application for an online shopping site keeps the price of each item as a hidden…
A: According to the data, when constructing an e-commerce portal's web application, the consumer was…
Q: iven the following truth table, abc F 000 1 001 1 010 0 011 1 100 1 101 0 110 0 111 0 a) Find the…
A: answer:-To design a digital circuit based on the given truth table, we need to identify the minterms…
Q: Your company has suffered a breach in security, and it is possible that unauthorized individuals…
A: When investigating a security breach and attempting to determine the origin of the attack, you…
Q: Think about the good and bad things about cloud computing. How much does it cost to move to the…
A: Cloud computing provides internet-based computing services like network, storage, database, etc.…
Q: I
A: Introduction: RedHat Enterprise Linux is a popular operating system used by many organizations for…
Q: Create an original, in-depth post on the following topic: What role does the Internet of Things…
A: What exactly is meant by the term "Internet of Things" (IoT), and why is it significant in the…
Q: Talk about the ways in which the themes in the exhibit are related to each other. Explain why it's…
A: The query was about designing network networks. Based on the demands of the customer company,…
Q: What is the name of the procedure that begins with the start symbol of a grammar, continues with the…
A: The name of the procedure that starts with the initial symbol of the grammar, proceeds through a…
Q: While migrating from on-premises servers to a cloud-based IaaS architecture, do you anticipate any…
A: The answer is given below step.
Q: For p = 7, q= 11, e = 13, and n = pq, find the multiplicative inverse of e, reduced modulo (n) using…
A: Hello student Greetings Hope you are doing great. Thank You!!! The extended Euclidean algorithm is…
Q: Let's say that at the network layer, one computer sends a packet to another computer on the…
A: Introduction: In computer networking, communication is typically organized into layers, with each…
Q: Explain how the ideas of user-centered design relate to the different stages of the software…
A: Software development life cycle: Software life cycle models (process models) illustrate the software…
Q: How do different system models work and what are their pros and cons?
A: There are several system models that are commonly used in the field of information systems. Each of…
Q: Give an example of how virtual servers are used in education and explain how they are used.
A: Remote server: In contrast to dedicated servers, virtual servers allow many operating systems to use…
Q: What are the strenghs and weaknessess of information system in automative art?
A: Information system: Information systems (IS) are critical in the automotive industry, particularly…
Q: Write a C program that takes in an array of integers and uses pointers to sort the array in…
A: According to the information given:- We have to write a C program that takes in an array of…
Q: What is the meaning of the Logical Link Control (LLC) sublayer?
A: It supplies the required logical addressing in order to identify the device being used. It offers a…
Q: What does the following program open "source.txt" to do? #include int main() { FILE *fp; } fp return…
A: Introduction: The given program is written in C language and uses the standard input/output library…
Q: a) Why is Hashing preferred over other method of searching? b) Explain the differences between open…
A: Answer the following questions: a) What is the reason for preferring Hashing as a searching method…
Q: Describe the three basic steps of testing for a commercial software system you've used in a few…
A: Commercial software, also known as payware, is a category of software that is either used for…
Q: Keep in mind that you can figure out the complement of a DFA by just switching the accept and…
A: Turing Machine: It is a mathematical model of computation that is used to study the limitations and…
Q: Explain the purpose (and/or how to use) an "added variable
A: Explain the purpose (and/or how to use) an "added variable plot".
Q: Look at the many applications of IT in today's world.
A: It is important to keep in mind that decision support systems, management support systems (MRS), and…
Q: People and information systems drive technological advances, so why is this assumption true
A: Technology is not created or advanced in isolation, but rather through the efforts of the people and…
Q: How are conventional software development and web-based software development distinct from one…
A: We have to explain how are conventional software development and web-based software development…
Q: How did information systems change over time, and what were the most important people and events?
A: Explain the evolution of information systems, focusing on the key figures and events that shaped the…
Q: Can I see an example of how virtual servers can be used in the classroom and other educational…
A: Internet-accessible PCs are virtual. Virtual screens can be viewed anywhere because the operating…
Q: The function fopen return NULL when: An error occurred while opening the file. An error occurred…
A: Your answer is given below with an explanation.
Q: What are the traits of network designs? Explain your response.
A: Introduction: Network design refers to the process of planning, implementing, and maintaining a…
Q: 6. Construct a right-linear grammar for the language L ((aaab ab)*). 7. Find a regular grammar that…
A: The start symbol S generates the string "aa" followed by A, or the empty string. The nonterminal A…
Q: A user is executing a tracert to a remote device. At what point would a router, which is in the path…
A: The solution is given below for the above-given question:
Q: 4 Which sorting method's first shift will be to move the 50 to the first position? [123, 50, 1, 56,…
A: sorting method whose first shift will be to move the 50 to the first position is Selection Sort
Q: Write a python function that accepts a string object and counts the number of vowels in the string…
A: The following Python code defines a function named countvowels that accepts a string object as input…
Q: Compare and contrast the four ways to use reuse?
A: Comparison of the four methods of reuse in software engineering: Ad hoc reuse: Ad hoc reuse refers…
Q: Is there anything to be wary about in terms of governance while making the move from on-premise…
A: Answer: The infrastructure of the charity information is maintained by the charity administration…
Q: What are cloud computing, the Internet of Things, and the wireless revolution?
A: Introduction: Cloud computing, the Internet of Things (IoT), and the wireless revolution are three…
Q: How would you explain and compare the six main ways software is sold?
A: Six software sources: IT firms: 2. Software packagers 3. Enterprise software suppliers 4.Cloud…
Q: How does the REA Model compare to a commercial system? What are its pros and cons?
A: The REA (Resources, Events, and Agents) model is a conceptual framework used in accounting and…
Q: How many main memory chips are needed to provide a memory capacity of 2^9 bytes of RAM and 2^4 bytes…
A: To provide a memory capacity of 219 bytes of RAM and 24 bytes of ROM, we need to calculate the…
Q: 19. Consider the following C program: int fun (int *i) { *1 += 5; return 4; } hot?
A: Introduction: Computer programming is a crucial skill in today's world, and understanding the…
Q: Choosing between a VPN appliance and an operating system Contrast and compare
A: Operating system (OS) OS acts as a mediator between the user and the operating system. An operating…
Q: Why do we need to control how things flow? Tell me about the most common ways to control the flow of…
A: Answer is
Q: What does a foreign key mean in terms of database integrity? What can you say to justify this…
A: Introduction: The foreign key is called the child table. The table containing the candidate key…
Q: What problems do businesses face while making the switch to cloud-based infrastructure? I was…
A: Cloud-based infrastructure refers to a type of computing infrastructure where computing resources…
Q: Please explain the key distinctions between the Internet and the World Wide Web.
A: Introduction: The Internet and the World Wide Web are two terms that are often used interchangeably,…
Q: To compute (15)(15)(15) mod 23, what can you do? Select all that apply. Take the product…
A: To compute (15)(15)(15)mod 23
Q: with 1 2 3 4 5 Complete the code to finish the function. area Triangle(base, height): return 0.5 *…
A: The complete Python program for the given problem is as follows: # Define a function called…
Q: Give the meanings of the words "CRUD" and "REST.
A: Answer is
Step by step
Solved in 4 steps with 2 images

- (Inventory) Create an ASCII file with the following data, or use the shipped.dat file available on this book’s Web site. The headings aren’t part of the file but indicate what the data represents Using this data file, write a C++ program that reads the file and produces a report listing the shipped date, part number, first name, last name, and company name.(Data processing) Write a C++ program that reads the file created in Exercise 4, permits the user to change the hourly wage or years for any employee, and creates a new updated file.Write a function called countWord(). It takes 2 parameters: The name of a text file(e.g. gettysburg.txt) and a word to be searched within that file. Your code should returnthe number of times the given word appears in the file.>>> countWord('gettysburg.txt', 'people')3
- Assuming that a text file named FIRST.TXT contains some text written into it, write a function namedcopyupper(), that reads the file FIRST.TXT and creates a new file named SECOND.TXT contains allwords from the file FIRST.TXT in uppercase. (write c++ code)1-) Write a code to do following operationsa-print the contents of filewrite a function to print the contents of a given file on screen. Your function prototypeshould be in given format.void PrintFileContent(FILE* fptr)b-copy contents of one file to another filewrite a function to copy contents of one file to another file. Convert all characters intouppercase while copying the content. You are allowed to use toupper() function in ctypelibrary. Your function prototype should be in given format.void copy_file(FILE* fptr1,FILE* fptr2)c- count the Number of Characters in a Filewrite a function to count the Number of Characters in a File. Your function prototypeshould be in given format.int findNumberofChar(FILE* fptr)Please design your main.c file as follow1- Open a text file to read in your directory.2- Create an empty text file for writing and reading in same directory.3- Check if both files are opened.4- Print the contents of first file by calling PrintFileContent function.5- Call…Please write a function named search_by_name(filename: str, word: str), which takes a filename and a search string as its arguments. The function should go through the file and select all recipes whose name contains the given search string. The names of these recipes are then returned in a list.
- Write a function to output patient information that are stored in a file. One of the parameters of the function must be no. of patients to output and another one the name of the file where the patients’ information is stored.create a function it takes a file name as an arguments and returns whether it exist or not, if it then it's a folder or a file. This task is from shell scrptingQuestion 55 Write a function that takes two parameters, a file name to create and an integer. The function should write all the even numbers between 0 and the integer to the file name passed in. The numbers should be all on one line of the file For example: write_evens("even_file.txt",20) This should create a file called even_file.txt that contains 0 2 4 6 8 10 12 14 16 18 20 Full explain this question and text typing work only thanks
- Function________________ writes a line to a specified fileWrite a function void saveByDept(char *fileName, char *deptName , student allStudents[], int size) that will save the information of all students who belong to the department with name pointed to by deptNameinto a text file. The name of the file is given as an input parameter, fileNameWrite a function sum_file(f) that takes a filename f. Each line in f contains asingle number. You should write to the last line in the file the sum of all thenumbers written in the file.



