Problem 1. Input three strings s1, s2, and s3 from the keyboard such that s1 "Hello out there. How are you this morning?" s2 = "Did you watch the movie that was on TV last night?" s3= "Yes, we didd!" a. correct the spelling errors in s1 and s3 (find and replace) and re-display the strings. Also, replace "TV" with Netflix"!. b. concatenate all 3 strings but insert "**" between them. c. Print each string on a separate line d. print string s2 and s3 on the same line.
Problem 1. Input three strings s1, s2, and s3 from the keyboard such that s1 "Hello out there. How are you this morning?" s2 = "Did you watch the movie that was on TV last night?" s3= "Yes, we didd!" a. correct the spelling errors in s1 and s3 (find and replace) and re-display the strings. Also, replace "TV" with Netflix"!. b. concatenate all 3 strings but insert "**" between them. c. Print each string on a separate line d. print string s2 and s3 on the same line.
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter9: Completing The Basics
Section9.4: Character Manipulation Functions
Problem 7E
Related questions
Question
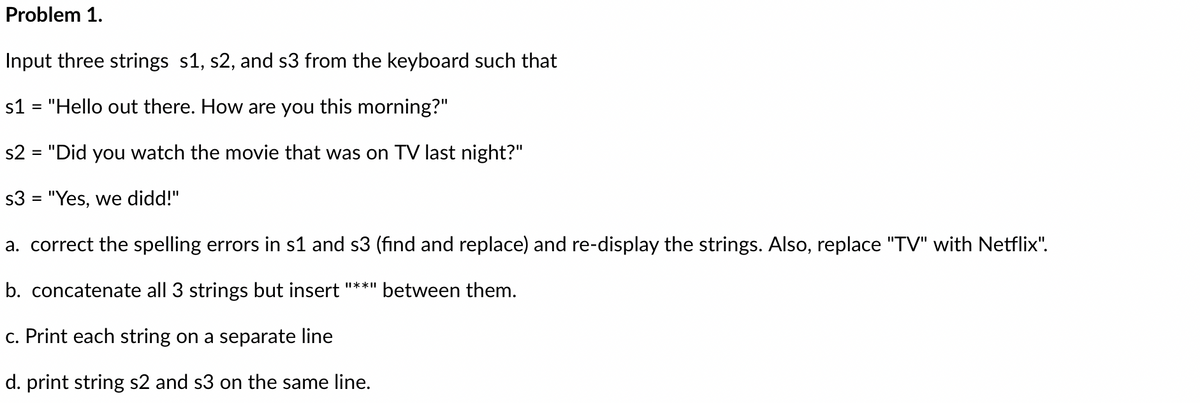
Transcribed Image Text:Problem 1.
Input three strings s1, s2, and s3 from the keyboard such that
s1 = "Hello out there. How are you this morning?"
s2 = "Did you watch the movie that was on TV last night?"
s3 = "Yes, we didd!"
a. correct the spelling errors in s1 and s3 (find and replace) and re-display the strings. Also, replace "TV" with Netflix".
b. concatenate all 3 strings but insert "**" between them.
c. Print each string on a separate line
d. print string s2 and s3 on the same line.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr