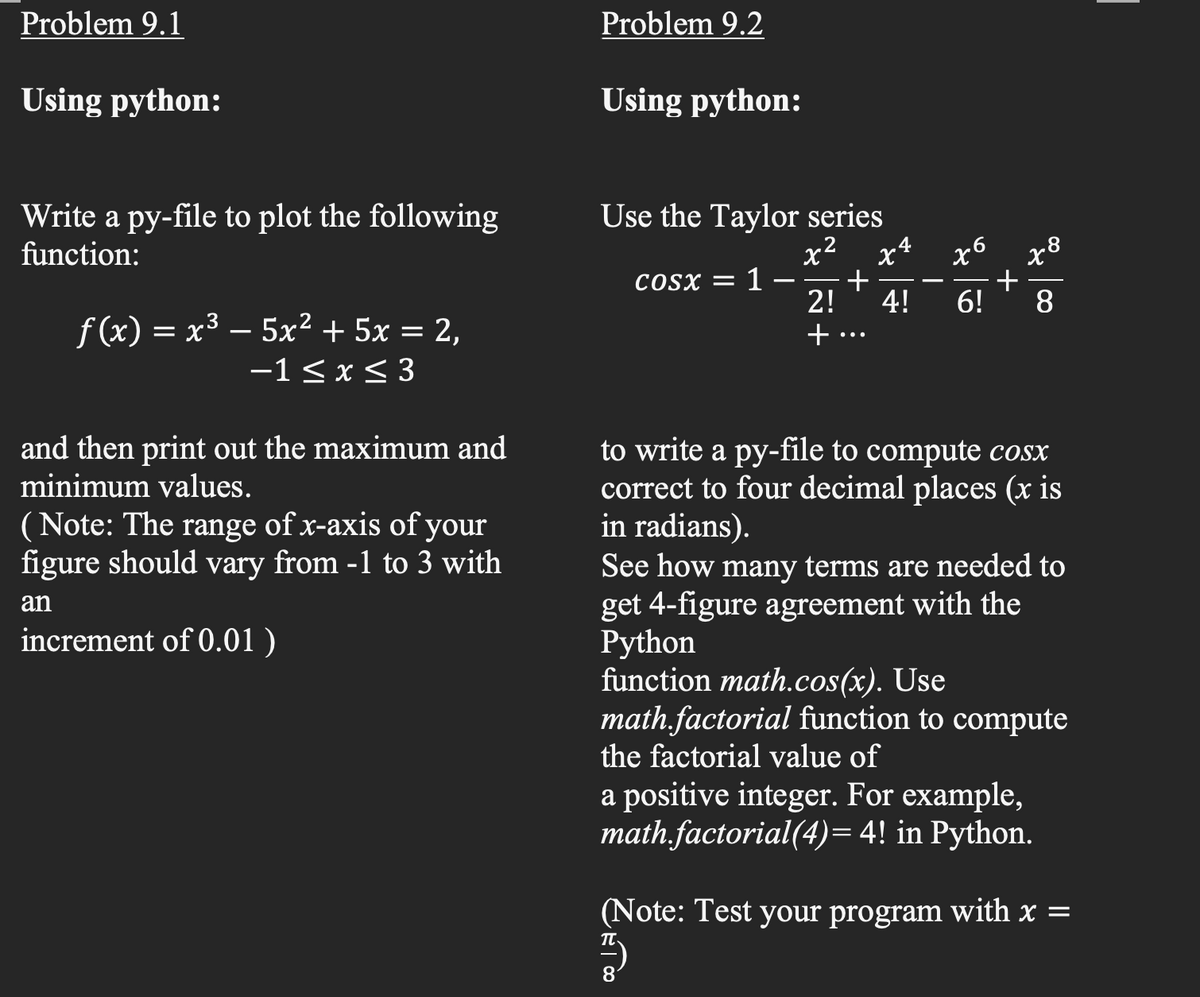
Problem 9.1 Problem 9.2 Using python: Using python: Write a py-file to plot the following function: Use the Taylor series x2 x4 + 2! x8 + 6! x6 COSX = - - 4! 8 f(x) = x³ – 5x² + 5x = 2, -1 < x < 3 + ...
Q: Specifically, how is SEH used in hidden flow control mechanisms?
A: Control Mechanisms: A method of controlling the behaviour of a process or system. Control mechanisms…
Q: As a developer, what role do you play in discovering and resolving security issues? What exactly…
A: Introduction: Engineers are software specialists, and they are well-positioned to safeguard their…
Q: arnt about web design and develo
A: Below the learn about web design and development?
Q: What are the advantages of applying integrity constraints during database design and implementation…
A: Introduction: What are the advantages of applying integrity constraints during database design and…
Q: Demonstrate how the local/global nexus affects and influences the design of web-based application…
A: During the planning phase of web application development, there are a number of issues to consider.…
Q: Computer science What are the most prevalent forms of errors and what do they mean?
A: Introduction: In computer science, mistakes are most likely to occur during program execution. This…
Q: What are the advantages of arrays? The greatest number of dimensions that an array can have is. What…
A: Explanation: THE ARRAY - An array is a collection of contiguous memory allocations that contain…
Q: What is the definition of data granularity?
A: Data Granularity: Granularity is a term used in computer science to describe the breaking down of…
Q: figuring the price of espresso drinks so baristas can have time to chat Juliette Is Pulling For Us…
A: Given code: <!doctype html><html><head><meta…
Q: Who invented/founded Python programming? What is the nickname given to him?
A: Guido van Rossum invented the python programming. The perfect troll is the nickname given to the…
Q: Distinguish between the design o
A: Q)Distinguish between the design of conversation and that of an interface? Answer: There are two…
Q: The following is a list of recent research papers that use machine learning methods.
A: Given: Thousands of research articles on Machine Learning are published each year in prestigious…
Q: Using an IoT “Smart Meter” example, describe the deployment and operating perspective, resources,…
A: In an Internet of Things system, the deployment and operating views are as follows: The Internet of…
Q: Computer science Short answer What is Content filtering?
A: Introduction: Occasionally, web content may contain information that is regarded offensive,…
Q: Convert below base7 number into base36 number (65)base7 = (?)base36
A: INTRODUCTION: Here we need to convert base 7 number into base 36 number.
Q: I need to write code to plot a star with 8 corners. My code comes close but the final line does not…
A: Matlab code to plot a star with 8 corners.
Q: Below are two popular Fingerprinting Algorithms.
A: Fingerprinting Algorithms: An arbitrarily large data object (for example, a computer file) is mapped…
Q: Indicate the number and kind of expansion slots available on the motherboard. Is the board's P1…
A: Motherboard plays very important role in computer. It is used for the communication of CPU and other…
Q: To what extent are vectors better at storing data efficiently than arrays?
A: According to the question the vectors are the sequence containers and it utilize continuous with the…
Q: Discuss the difficulties and challenges of using real-time speech recognition technologies. Compare…
A: Given: Use this opportunity to discuss the problems and limitations of employing real-time speech…
Q: Is pZoom a reference to the second member of an array called Arr, or does it relate to the first…
A: The referencing operator & is used to obtain the address, but the dereferencing operation * gets…
Q: Do you know the meaning of the term "collaboration?" Write out all of the situations in which…
A: Collaboration: Collaboration is a method of working in which people come together for a common goal…
Q: This class is going to mainly discuss Layers 1-4 (Transport, Network, Data Link, & Physical) in this…
A: So, from above four layers .we would like to discuss about DATA LINK LAYER . Data Link Layer (DLL)…
Q: What does the term "networking" mean? What are the system's advantages and disadvantages?
A: Introduction: A network node is a computer that links other computers in the context of computer…
Q: Which layer is concerned with the physical path the data takes?
A: Data is raw facts and figures which is required to collect meaningful information. Data…
Q: Discuss about the techniques to implement blockchain and the challenges in implementation to…
A: The question was to know about the techniques to implement blockchain and challenges to implement…
Q: What are some instances where you may expect computer intelligence to outperform human intelligence?
A: Introduction: Computers outperform humans in a lot of ways. They have more memory, allowing them to…
Q: How is GitHub (or any other git product) used to manage source code? Please provide a detailed…
A: GitHub GitHub is a for-profit company that offers a cloud-based Git repository hosting service.…
Q: What does it mean to be a MAN? What exactly is the distinction between MAN and WAN?
A: Introduction: There are many different types of networks in networking, such as lan, man, and wan.…
Q: What are two of the most critical activities or concepts to concentrate on while learning a new…
A: Definition: A variable is a Variables are the foundation of every programme and every programming…
Q: Q1/ write code in matlab for figure below :- wwwww w m w 505 NOTE/ PAM , FM=5
A: PAM Output:
Q: How closely related are the concepts of object-oriented programming and abstract data types? This is…
A: Agreement Disagreement: Students should recall that understanding is a key underlying element of…
Q: Ist necessary to utilise a computer to acquire accurate results from a simulation? Explain.
A: Simulation enables the manager to quantify and observe the behavior of the system. Whether the…
Q: Computer science Short answer Demonstrate each form of abnormality.
A: Introduction: There are three type of anomalies: Demonstrate each form of abnormality.
Q: Consider a Multilevel Queue scheduler with two queues, numbered 1 and 2. Queue 1 has higher priority…
A:
Q: Computer science Implications of this study "An Examination of Health Effects Due to Use of Gadgets"
A: Introduction: This study's data analysis An Examination of the Health Effects of Gadget Use
Q: How important is software now in terms of product quality?
A: Quality is unquestionably critical since it promotes predictability, helps to avoid rework, and also…
Q: Computer science Explain how the primary key in the same relation is referenced.
A: Introduction: The primary key constraint requires that each row in the relational database…
Q: It's important to understand what mapping means for user interface design. Are there any specific…
A: Mapping is a procedure that aims to bridge the gap between users' or customers' requirements and the…
Q: When it comes to computer graphics, what is the significance of the reflection vector? Using at…
A: Reflection Vector in Computer Graphics: In computer graphics, reflection is used to represent…
Q: 4) Complete the Java code for the following for loop: for (int i= 1; i <= 6; i++){ // your code here…
A: Answer: Java Source Code: public class Main{ public static void main(String[] args) { int number…
Q: Do you know how many steps are involved in Web development? Describe each stage and explain why it…
A: Do you know how many steps are involved in Web development? Describe each stage and explain why it…
Q: What are two of the most critical activities or concepts to concentrate on while learning a new…
A: Defining variables: Variables are the foundation of every programme and every programming language.…
Q: Let p, q, and r be the propositions p :You get an A on the final exam. q :You do every exercise in…
A: This is a question of Discrete Mathematics. As per the question we have to write a proposition for :…
Q: If I declare a final double, what is the convention for capitalizing the identifier in Java? Give an…
A: Final is a non-access modifier applicable only to a variable, a method, or a class. When a variable…
Q: What is the function of a multidimensional array?
A: An array is a data structure that contains the elements of the same type. Properties of array: It…
Q: Write a class encapsulating a web store, which inherits from Store. A web store has the following…
A: import java.util.Scanner; class Store{ public final double SALES_TAX_RATE = 0.06; private…
Q: et E = a(a+ b*) + b be a regular expression over the alphabet E = {a, b}. emplate method to…
A: Step by Step e-NFA onstruction:- Step1:- Step 2:-
Q: PLEASE BE GUIDED A. MODIFY THE GIVEN PROGRAM USING THE PYTHON FUNCTIONS Temperature Conversion…
A: Given Program is almost correct you just have to handle the input E and other input and also You…
Q: How do you alter the view in Visual Studio
A: Introduction In Visual Studio, you can modify the position, size, and conduct of windows to make…
Trending now
This is a popular solution!
Step by step
Solved in 6 steps with 4 images

- x=[10,1,20,3,6,2,5,11,15,2,12,14,17,18,29] for i in range(0, len(x)): m = x[i] l = i # Finding the minimum value and its location for j in range(i+1, len(x)): if(m >x [j]): m= x[j] l = j # Now we will do the swapping tmpry = m x[l] = x[i] x[i] = tmpry print(x) 8.The code above is written in Python programming language. In this sample, there are many sectors where you can apply knowledge of code refactoring. Mention each criteria where this code lacks and provide appropriate suggestions to improve. (Hint: Code Smells e.g: Naming Convention, Code length, Assertion etc.)translate the following MIPS code to C. Assume that the variables i, j, and k areassigned to the registers $s0, $s1, and $s2, respectively. Assume that the baseaddress of the array A is in registers $s6.Loop: blt $s0, $s1, Exitbge $s1, $s2, Exitaddi $s1, $s1, 5j LoopExit:addi $t0, $zero, 4ble $s0, $t0, Donesll $t1, $s0, 2add $t2, $s6, $t1sw $zero, 0($t2)Done:(Practice) Although the total number of bytes varies from computer to computer, memory sizes of millions and billions of bytes are common. In computer language, the letter M representsthe number 1,048,576, which is 2 raised to the 20th power, and G represents 1,073,741,824, which is 2 raised to the 30th power. Therefore, a memory size of 4 MB is really 4 times 1,048,576 (4,194,304 bytes), and a memory size of 2 GB is really 2 times 1,073,741,824 (2,147,483,648 bytes). Using this information, calculate the actual number of bytes in the following: a. A memory containing 512 MB b. A memory consisting of 512 MB words, where each word consists of 2 bytes c. A memory consisting of 512 MB words, where each word consists of 4 bytes d. A thumb drive that specifies 2 GB e. A disk that specifies 4 GB f. A disk that specifies 8 GB
- This problem is adapted from an earlier edition of P&H, and should be submitted.Consider the following code used to implement a new instruction: foo $t3,$t1,$t2:mask : . word 0xFFFFF83Fs t a r t : l a $t0 , masklw $t0 , 0 ( $ t 0 )l a $t3 , s h f t rlw $t3 , 0 ( $ t 3 )and $t3 , $t3 , $ t 0a ndi $t2 , $t2 , 0 x 0 0 1 fs l l $t2 , $t2 , 6o r $t3 , $t3 , $ t 2l a $t5 , s h f t rsw $t3 , 0 ( $ t 5 )s h f t r : s l l $t3 , $t1 , 0Add meaningful comments to the code and write a brief (2 sentence max) description of what foo does. Thisis not the same as saying how it does it - e.g., when asked to describe what a pedestrian is doing, you wouldsay they are walking, not that they are ilfting their left leg, angling it forward, putting it down, . . ..State at least one reason why writing “self-modifying code” such as this is a bad idea (and often times notactually allowed by the operating system)?Write a complete MIPS program to multiply two 4x4 matrices. Initialize two floating point (double-precision) arrays in the data segment. Initialize two floating point (double-precision) arrays in the data segment. The 16 zeros represent initial values for three 4x4 matrices where the first four values constitute the first row, so on and so forth. Use loops to input 16 double type values from the user for y and z. The result of the multiplication of y and z will be saved in the x array. Use a nested loop to print the values of x in a matrix format (4x4).Write a C program to create two processes A and B. Jobs of these two processes are as following: Process A: This process generates eight random numbers (>30 and <500) and will forward these numbers to process B through pipe. Process B: This process generates five random numbers (>20 and <600). This process receives the numbers from process A are holes in the main memory and the numbers generated in process B are successive segment requests from the CPU. Identify the hole that is taken for successive segment requests by using First Fit algorithm.
- Implement nibble_swap() function. Take in 4 byte integer and returns integer with swapped nibbles in first two bytes. Use a 3 bit register. The template below is for your reference. The code in the Assembly code portion needs to be completed in Assembly x86-64 #include extern "C" int nibble_swap(int var); int main(int avgc, char** avgs) { int v = nibble_swap(0xCAFEBABA); //answer: 0xACEFABAB printf("Swapped Variable is : 0%X \n", v); return 0; } ----------------Assembly Code --------------------------- ;yasm -f elf64 var.asm section .text global start : ;put ur code here retAssume that the following are concurrent VHDL statements: (a) L <= P nand Q after 10 ns; (b) M <= L nor N after 5 ns; (c) R <= not M; Initially at time t = 0 ns, P = 1, Q = 1, and N = 0. If Q becomes 0 at time t = 4 ns, (1) At what time will statement (a) execute? (2) At what time will L be updated? (3) At what time will statement (c) execute? (4) At what time will R be updated?CODE IN MACHINE LANGUAGE USING LC-3 Write an assembly program to set R0=1 if there's a 5 in one of ten memory locations, starting at x3100. At the beginning of the program, set R0 = 0. If no 5 is found, it should leave R0 set to 0. Please submit your assembly program below. I will run it with my data. Extra credit - 20 points: If a 5 is found, output the following message to the console. "A 5 was found at x31xx." 31xx is the hex address of the 5. Here is the test data I used to generate the screen print below. It is not the test data I will use to grade your project. .ORIG x3100.FILL #10.FILL #20.FILL #30.FILL #40.FILL #50.FILL #5.FILL #70.FILL #5.FILL #90.FILL #100.END
- I have the following MIPS assembly code: .data prompt1: .asciiz "Enter integer A: " prompt2: .asciiz "Enter integer B: " result_add: .asciiz "A + B = " result_sub: .asciiz "A - B = " result_and: .asciiz "A & B = " result_or: .asciiz "A | B = " result_xor: .asciiz "A ^ B = " .text # Print prompt and read integer A li $v0, 4 # syscall code for printing string la $a0, prompt1 # load address of prompt1 into $a0 syscall li $v0, 5 # syscall code for reading integer syscall move $t0, $v0 # save integer A in $t0 # Print prompt and read integer B li $v0, 4 # syscall code for printing string la $a0, prompt2 # load address of prompt2 into $a0 syscall li $v0, 5 # syscall code for reading integer syscall move $t1, $v0 # save integer B in $t1 # Calculate and print A + B add $t2, $t0, $t1 li $v0, 1 # syscall code for printing integer move $a0, $t2 # load…Translate the following MIPS code to C. Assume that the variables f, g, h, i, and jare assigned to registers $s0, $s1, $s2, $s3, and $s4, respectively. Assume that the baseaddress of the arrays A and B are in registers $s6 and $s7, respectively and that A and B are arrays of words. addi $t0, $s6, 4lw $t0, 0($t0)add $t0, $t0, $t0sw $t0, 0($s6)(Practice) a. Using Figure 2.14 and assuming the variable name rate is assigned to the byte at memory address 159, determine the addresses corresponding to each variable declared in the following statements. Also, fill in the correct number of bytes with the initialization data included in the declaration statements. (Use letters for the characters, not the computer codes that would actually be stored.) floatrate; charch1=M,ch2=E,ch3=L,ch4=T; doubletaxes; intnum,count=0; b. Repeat Exercise 9a, but substitute the actual byte patterns that a computer using the ASCII code would use to store characters in the variables ch1, ch2, ch3, and ch4. (Hint: Use Appendix B.)

