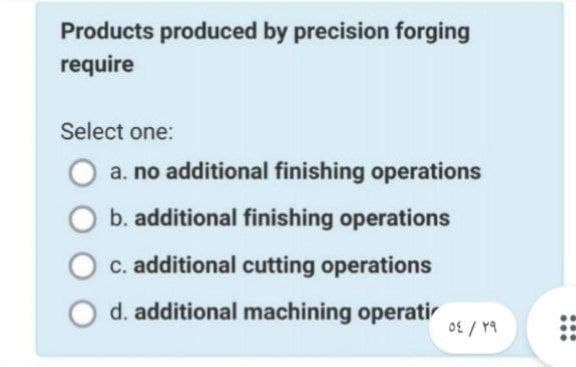
Products produced by precision forging require Select one: a. no additional finishing operations b. additional finishing operations c. additional cutting operations d. additional machining operati ٥٤ / ۲۹ ...
Q: 2. #include int main() { int num, count, sum = = 0; printf("Enter a positive integer: ");…
A: Answer: As per guidelines I can solve only first question. So i request you to please repost other…
Q: How virtual reality will transform the world.
A: Virtual Reality (VR) has seen significant growth in 2019. These technologies have the potential to…
Q: Consider how important wireless networks are in poor countries. Why do some companies choose…
A: Families with many electronic devices, such as PCs, laptops, and other mobile devices, are…
Q: Consider a processor that contains eight 16-bit registers. Design a complete Register file and…
A: Answer
Q: What exactly does it imply when someone refers to a "wifi access point"? What exactly is the working…
A: Answer:
Q: Compare and contrast the traditional Waterfall model with the more modern Rational Unified approach.
A: Waterfall Model is the oldest model used throughout the development life cycle to build a system in…
Q: What are some of the considerations that go into the design of the software component of an…
A: Answer: Information system software: The computer era brings corporations, colleges, and other…
Q: Provide an explanation of how you may defend your home network using personal firewalls in addition…
A: Introduction: Here we are required to explain how we may defend your home network using personal…
Q: The throughput of wireless networks is much lower compared to that of traditional networks. What…
A: Wired network: Computers are linked together with physical wires and cables in a wired network.…
Q: Programming environments and user environments are explained via examples.
A: A programming environment combines hardware and software that enables a developer to create apps.…
Q: Q2/Rewrite the Programmed by using "spc" Private Sub Command1_Click() Font.Name = "times new roman":…
A: Statistical technique manipulate (SPC) is described as using statistical techniques to control a…
Q: What is a mantrap? A fake network set up to lure in and catch a hacker A trap…
A: According to the information given:- we have to choose the correct option to satisfy the statement.
Q: Provide samples for each of the three most used file management methods.
A: Given: Give instances of each of the three main techniques to file management. Ordinary files,…
Q: It would be helpful if you could explain the difference between integrity limitations and permission…
A: Answer: integrity limitations: Integrity constraints are a bunch of rules. Keeping up with the…
Q: How does the description of the issue vary when it comes to a business case as opposed to an actual…
A: Start: Software configuration management (SCM or S/W CM) is a programme engineering process that…
Q: For CPU and memory usage, do you favour a synchronous or asynchronous bus? a bus that never stops…
A: BUS: A bus is a form of internal connection that operates at a fast speed. Buses transmit data and…
Q: Both read-only memory (ROM) and random access memory (RAM) make up the main memory of a personal…
A: Computer memory is of two basic type – Primary memory(RAM and ROM) and Secondary memory(hard…
Q: What steps can we take to ensure the success of our projects? What exactly does it mean when a…
A: To guarantee that our project succeeds, there are a few critical steps to take. Ensure that the…
Q: Create a table that differentiates between the functional and non-functional needs of the…
A: The answer is that any information system must pass two types of tests. There are two distinct…
Q: You want to establish a Disaster network for telecommunication. Which type of topology will you use…
A: In a network there are some types of topologies: 1.Bus Topology. 2.Star Topology. 3.Hybrid Topology.…
Q: What is the difference between having a license to use software and having copyright over it?
A: The issue here is the distinction between software licensing and copyright. Copyright Copyright…
Q: Shape1. Shape =5 will make the shape control appears as a rectangle O square O oval O rounded square
A: The Option Box control lets the user select one of the choices. Only one Option Box can be selected…
Q: Applying the concept of Zeller's congruence discussed earlier, solve for the day of the week of…
A: Christian Zeller created the Zeller's congruence algorithm to determine the day of the week for any…
Q: What are the FOUR (4) benefits of using the Incremental Model as opposed to the Waterfall Model?
A: Given: The first model in the software development life cycle was the waterfall model. The output of…
Q: Discuss in some detail the three types of testing: unit testing, integration testing, and system…
A: A software development life cycle or SDLC is a process that defines different stages that are…
Q: Tom loves strings very much but he loves palindromic strings even more. Today he found an old rope…
A: The program is written in Java. Check the program screenshot for the correct indentation. Please…
Q: What exactly does it imply when someone refers to a "wifi access point"? What exactly is the working…
A: Answer:
Q: PROBLEMS ENCOUNTERED 1. NO INTERNET 2. 3. 4. 5. ACTION TAKEN CHECK YOUR NETWORK SETTINGS OR THE…
A: Here are some of the problems and their fixes:
Q: Please provide an explanation of the three principles governing integrity. Please include an…
A: In most database systems, data integrity is ensured by integrity constraints or rules. The…
Q: Compilers and assemblers may be designed to sequence assembly language instructions in such a manner…
A: Assembly language: A pipeline may be made to have the fewest possible dangers by designing compilers…
Q: B/convert this equation below for coding in V.B?
A: For first expression , we can write it using functions in methods of the System.Math class. here,…
Q: Ravi loves strings very much but he loves palindromic strings even more. Today he found an old rope…
A: Algorithm: First line of input contains a single integer T denoting the number of test cases.…
Q: Which of the following is true? O In a simple if state, the command right below the CMP is the…
A: let us see the answer:- The correct option is a) i.e. In a simple, if the state, the command right…
Q: Why do we need virtual LANs if we can already create many subnets on a single switch, and users on…
A: To route between various Volans, you'll need a router. Also, those two Volans cannot share the same…
Q: Is the issue with the computer's hardware or its software when you power it on for the first time…
A: Computer's hardware: Computer hardware consists of the physical components a computer system needs…
Q: There is more than one kind of digital memory that may be used, such as a hard disk drive (HDD),…
A: Start: There are numerous digital memory standards, so if there is only one SSD format with various…
Q: An explanation of how you may defend the network in your house using personal firewalls as well as a…
A: Firewall for your home network: One of the primary functions of firewalls is to protect your…
Q: Think about the importance of wireless networks in countries that are still developing. Why do some…
A: Launch: Families with many electronic devices, such as PCs, laptops, and other mobile devices, are…
Q: In the field of computer science, what is the abbreviation for "accelerated graphics port"?
A: Introduction: According to the question An Accelerated Image Port AGP is a channel point used for…
Q: How are Deadlock Prevention and Deadlock Avoidance Distinct from One Another?
A: A deadlock occurs when one process in a group possesses a resource and at the same time waits for…
Q: 6) Draw the Lexemes and Token of the following Java Statement a. Salary = num 50-10;
A: We are going to find out the lexemes and token of given java statement. Lexemes are the actual…
Q: 3 Write a function to generate a date string given numeric values for month, day, and year, and a…
A: dictornary = {1: ('January', 'Janvier', 'Januar'), 2: ('February', 'Février',…
Q: When a customer phones the help desk and says, "My computer won't boot," a skilled help desk…
A: If a user complains, "My computer won't boot," the help-desk expert should ask the following…
Q: Is there a distinction to be made between the phrases "Internet" and "World Wide Web"?
A: Internet: The internet is used to link several networks of computers at the same time. Because the…
Q: How does the widespread availability of digital technology make it possible for nearly anybody to…
A: Launch: We must discuss how digital technology allows everyone to produce multimedia. People may now…
Q: What exactly do you mean when you use the phrase "Principle of Non-Repudiation"?
A: Non-Repudiation Principle: You won't be able to reject the veracity of a statement if you use…
Q: To better understand the distinction between ethics in engineering and ethics in computing, please…
A: Start: Ethics is a collection of moral rules that regulate an individual's or a group's conduct. The…
Q: An instruction may be retrieved and carried out without requiring the use of a CPU cycle.
A: The instruction cycle is the amount of time required by the CPU to execute a single line of code.…
Q: It is important to determine the fundamental components that make up an information system. What…
A: Information system components: A system is the collection of interrelated components that produce…
Q: Which is preferable, why are both packet and circuit switches required today?
A: Introduction: The question was really about packet switch and circuit switch. Switching circuits:…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- What exactly does deoptimisation entail? When and why could you need it?Briefly describe three types of operations that can easily be performed with OLAP tools.Draw the shortest job first (SJF non-premptive) Gantt chart showing the execution of CPU considering the given data. Draw the shortest remaining time first (SRTF) Gantt chart showing the execution of CPU considering the given data.
- Correct answer will be upvoted else Multiple Downvoted. Computer science. You are given a multiset of abilities of two. All the more unequivocally, for every I from 0 to n selective you have cnti components equivalent to 2i. In one activity, you can pick any one component 2l>1 and partition it into two components 2l−1. You ought to perform q inquiries. Each inquiry has one of two sorts: "1 pos val" — appoint cntpos:=val; "2 x k" — ascertain the base number of tasks you really want to make basically k components with esteem lower or equivalent to 2x. Note that all inquiries of the subsequent kind don't change the multiset; that is, you simply work out the base number of activities, you don't perform them. Input The principal line contains two integers n and q (1≤n≤30; 1≤q≤2⋅105) — the size of cluster cnt and the number of inquiries. The subsequent line contains n integers cnt0,cnt1,… ,cntn−1 (0≤cnti≤106). Next q lines contain inquiries: one for each line.…How can generative design algorithms be applied to the prototyping of customized products?MCQ1004: Efficiency in a software product does not include ________ a. responsiveness b. licensing
- design a possible conceptual framework with the study entitled "Employing Audio Reading Material in Improving Reading FluecyComputer Architecture question Could you draw the k-map and sum the product terms. I have provided an example in the picture. Please follow the example to complete a and b. Thank you.From the given suggested research topics on computer architecture, select a topic and look for a related published research work/paper/journal/study. Create a short write up, answering the following: 1. What is the research work/paper/journal/study all about? Summarize by pointing out the main findings of the work 2. What is interesting about the research work/paper/journal/study? Why did you choose it? 3. What do you think would be the next concept/idea that can be derived from the paper research work/paper/journal/study?
- The mechanics of overclocking are laid forth, along with the potential upsides and downsides of engaging in this practice. Processor overclocking: pros and cons Kindly respond to each and every inquiry.Can you please give an example on how division algorithm is being used in Seawater Desalination? I've been reading and trying to understand different studies but I'm having difficulty on understanding it. Can you show me a process on how division algorithm is used in desalination? Please and thank you.x amswer with respect to solidworks software

