Prove Total
Q: briefly describe the dangers to data security.
A: A security risk is something that could bring about the trade off, misfortune, inaccessibility or…
Q: Please list the three C++ classes that may be used to build output streams.
A: Output streams are used to hold the output for particular data consumer which includes printer,…
Q: earn to d
A: The provided C code is done as per your requirements. "Screenshot of the program code" for better…
Q: 17824 bits of data is to be transferred from a station A to station B. Assume a call setup time of…
A: According to the information given:- We have to follow the instruction mentioned and calculate total…
Q: Write a function called Divisors which takes an integer and print all its divisors on the screen.…
A: Since no language is given in the question. I am using c++ langauge See below step
Q: What does the XSLT (extensible stylesheet language transformation) stand for?
A: Solution:: XSLT ((able to be made longer or more complex) Stylesheet Language Changes) is a…
Q: Draw an ER diagram for the following scenario: A designer has a store of designer dresses…
A: ER diagram is in proper manner:
Q: Develop the algorithms The challenge in the project is developing algorithms that accomplishes basic…
A: Pseudo Code Minimum : - Minimum(arr, n) min ← ∞ for i ← 0 to n if arr[i] < min…
Q: What does Interrupt Processing actually entail?
A: Process of Interrupt: An interrupt is an occurrence that modifies the execution order of the…
Q: Compare the roles played by programmers, systems analysts, information systems managers, the CIO,…
A: The question is to compare the roles played by programmers, systems analysts, information systems…
Q: Describe software packages, such as office packages, cloud packages, specialist packages, and…
A: The suite of programs and applications: A grouping of computer programs that are often application…
Q: 1. Prove the following propositions: (a) For all real numbers x and y, if x is rational and y is…
A: QUESTION 1 a. The sum of a rational number plus an irrational number is always irrational, therefore…
Q: Write a checked exception that passes the String message "Exception 429: Too Many Requests" into the…
A: Throwing cheecked exception in constructor .
Q: How does the typical system development lifecycle change as a result of the agile methodology?
A: Given: What kind of an effect does using an agile approach have on the standard system development…
Q: What are the differences among sequential access, direct access, and random access?
A: Random Access is a method of moving data to or from memory where every memory address can be easily…
Q: Consult the MIME RFC to find out how base64 encoding handles binary data of a length not evenly…
A: We will solve the first question for you. If you want any specific question to be solved then please…
Q: need help In Java, please solve and don't copy from wrong answers. I need the JAVA CODE, not an…
A: The JAVA code is given below with O(n) time complexity and O(1) space complexity The code and output…
Q: On the IAS, what would the machine code instruction look like to load the contents of memory address…
A:
Q: Explain the differences between the internet, intranet, and extranet
A: Internet This is the global network of computers available to anybody who knows their Internet…
Q: Please list the three C++ classes that may be used to build output streams.
A: In the given question there are three output stream classes in c++. They are ostream, ofstream and…
Q: When is it required for a system to organise its data using a page table?
A: Introduction: The data structure used by a virtual memory system in a computer operating system to…
Q: Using c++ language, 1. Write the function int isEven (int x); that returns 1 if x is an even number;…
A: Algorithm: Start Declare variables. Read the input any integer Use if else for conditions call the…
Q: What more strategies might be used to safeguard data privacy?
A: Data protection is a set of strategies and processes you can use to secure the privacy, availability…
Q: What is the private network's url? Should a datagram with an address from a private network ever be…
A: Please check the step 2 for solution
Q: Describe how a 3-layer neural network
A: The 3 layer neural network and how a hidden layer may overcome the perception's drawback are as…
Q: What does Interrupt Processing actually entail?
A: An interrupt is an event that breaks the sequence in which the processor executes the instructions.…
Q: A compiler is known to translate a program written into a high level programming language (Human…
A: Compilers are classified into two phases: analysis and synthesis. From the specified source code,…
Q: Consider the communication network in figure 1. E 2 B F 4 Figura 1: Graph representing a data…
A:
Q: What function does MVC serve in the overall design of web applications? What advantages can MVC…
A: Model view controller is referred to as MVC. The Model, View, and Controller components make up the…
Q: Please explain viruses and hacks, as well as how a business can stop someone from breaking in and…
A: Introduction: Hacker and virus protection is the security of information systems against theft or…
Q: 1 Bike bikeA - (Bike) mb; 2 MountainBike mountainBikeA 3 MountainBike mountainBikeB 4 MountainBike…
A: 1 Compiles and runs 2 Compiles and runs
Q: What would you enter to remove the configuration that was saved in NVRAM?
A: It is only necessary to input whether you wished to clear the NVRAM settings, according to the…
Q: Encrypt the message " MATH " by translating the letters into numbers and then applying the…
A: Assign a number to each letter: A=0,B=1,C=2,D=3,E=4,F=5,G=6,H=7,I=8,…
Q: Please list the three C++ classes that may be used to build output streams.
A: Classes for Output Streams The order in which data may be captured is determined by the output…
Q: Please explain viruses and hacks, as well as how a business can stop someone from breaking in and…
A: Introduction: The security of information frameworks against burglary or harm to their equipment,…
Q: In the context of information security, what exactly is privacy? Do all age groups have the same…
A: Information protection: The term "privacy" in the context of an information system refers to how the…
Q: #, please Rare Collection. We can make arrays of custom objects just like we’ve done with ints and…
A: Coding is given below. #include <iostream> #include <stdlib.h> #include <time.h>…
Q: What are the differences among direct mapping, associative mapping, and set associative mapping?
A: In Direct mapping, one one possible cache line used for mapping. Each block of main memory s mapped…
Q: Q. Give example of H3 and h4 tags in html?
A: <html><body> <h3>HELLO!</h3> <h4>HELLO!</h4>…
Q: How are a two-tiered application structure and a three-tiered application structure different? Which…
A: Architecture of Databases with Two Tiers - In a two-tier architecture, the application logic is…
Q: What are the differences among sequential access, direct access, and random access?
A:
Q: Explain how aspect interference can arise and suggest what should be done during the system design…
A:
Q: A multicast overlay effectively pushes streaming content from a single source to multiple…
A:
Q: Design an application that uses three identical arrays of at least 20 integers. It should call each…
A: 8 Sorting Benchmarks Bubble Sort Selection Sort Insertion Sort hmgnn gfg
Q: For the 0-1 knapsack problem using breadth-first-search algorithm: We have 5 items with price and…
A: This question is from the subject knapsack problem. Knapsack problem has two variants. One is…
Q: For the 0-1 knapsack problem using breadth-first-search algorithm: We have 5 items with price and…
A: BFS stands for Breadth first search which is also known as level order traversal. When we are using…
Q: Based on the following context free grammar: E-> E+TIT T-> TxF/F F-> (E) | a Give a parse tree for…
A:
Q: In this problem we explore the relationship between password length and cryptographic security.…
A: The answer for the above question is given in the below steps for your reference
Q: Determine a good asymptotic upper bound on the recurrence T(n) = 5T([n,
A: The answer is
Q: For the given parent class, write a child class that satisfies the following requirements: • child…
A: parent class- name Berry import java.io.ObjectStreamClass;import java.sql.Connection;import…
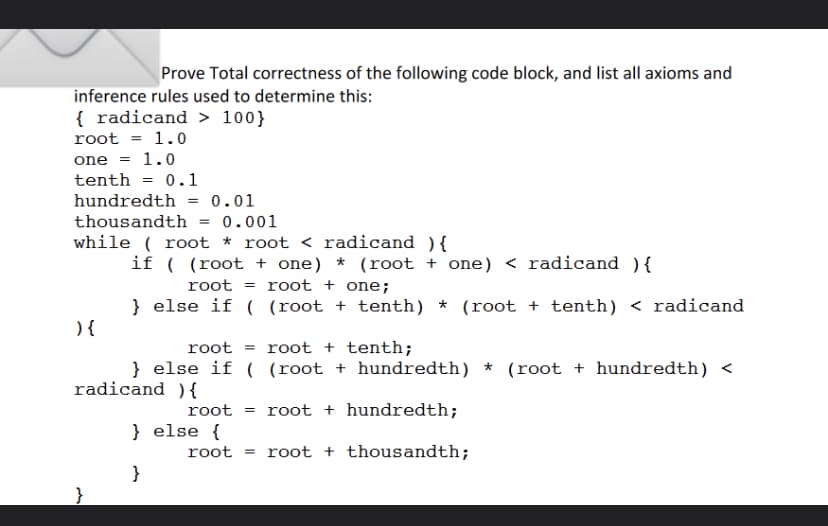
Step by step
Solved in 2 steps

- Rewrite the following expressions into prefix polish notation form, construct their corresponding Order Rooted Tree and evaluate their value 1- (3*(1-x))/((4+(7-(y+2)))*(7+(x/y))) 2-(3-(2+x))+((x-2)-(3+x))Provide an example of a recursive function in which the amount of work on each activation is constant. Provide the recurrence equation and the initial condition that counts the number of operations executed. Specify which operations you are counting and why they are the critical ones to count to assess its execution time. Draw the recursion tree for that function and determine the Big-Θ by determining a formula that counts the number of nodes in the tree as a function of n.1. i. (⌐ p ↔ q) is logically equivalent to ii. what is first truth - tree decomposition rule that should be used on the following wff: ⌐ (⌐ R ↔ R) implication of D b. simplication of biconditional D c. Double negation conditional D d. Negation of biconditional D
- Provide an example of a recursive function in which the amount of work on each activation is constant. Provide the recurrence equation and the initial condition that counts the number of operations executed. Specify which operations you are counting and why they are the critical ones to count to assess its execution time. Draw the recursion tree for that function and determine the Big-© by determining a formula that counts the number of nodes in the tree as a function of n.-Use course material of CMSC 451 and additional sources. Need reference also . Note dont copy from any other sites including chat gpt also . Previous ans here was also copy from chat gpt .Provide an example of a recursive function in which the amount of work on each activation is constant. Provide the recurrence equation and the initial condition that counts the number of operations executed. Specify which operations you are counting and why they are the critical ones to count to assess its execution time. Draw the recursion tree for that function and determine the Big-© by determining a formula that counts the number of nodes in the tree as a function of n.-Use course material of CMSC 451 and additional sources. Need reference also . Note dont copy from any other sites(a) Describe the structure of a complete binary tree of height h with maximum number of nodes.Derive the minimum number of nodes, n(max) (h), of this tree as a function of h.(b) Describe the structure of a complete binary tree of height h with minimum number of nodes.Derive the maximum number of nodes, n(min)(h), of this tree as a function of h.(c) Derive an expression for the height of a binary tree h in terms of the number of nodes, n.
- Create a bottom-up insertion technique based on the same recursive approach, a red-black representation, and balanced 2-3-4 trees as the underlying data structure for an implementation of the fundamental symbol-table API. Only the sequence of 4-nodes (if any) at the bottom of the search path should be split by your insertion technique.Mathematical Logic First-order or predicate logic. Show that the sum relation, {(m,n,p)|p=m+n}, is not definable on (N; ∙). Hint: Consider an automorphism of (N; ∙) that interchanges two primes. Where N is the set of natural numbers. Please be as clear as possible. Show and explain all the steps. Thank you very much.Devise a branch-and-bound algorithm for the SET COVER problem. This entails deciding: (a) What is a subproblem? (b) How do you choose a subproblem to expand? (c) How do you expand a subproblem? (d) What is an appropriate lowerbound? Do you think that your choices above will work well on typical instances of the problem? Why?
- Consider the following prefix expression:+ – ↑ 3 2 ↑ 2 3 / 6 – 4 2(i) Draw the rooted ordered tree for the prefix expression.(ii) Evaluate the prefix expression.What scenario is possible for a node-based situation in computer science. Please explainin set of 9 nodes, every node has 3 branches In a set of 9 nodes, one node has two branches, and the rest have exactly three.Answer the given question with a proper explanation and step-by-step solution. You are asked to pick up a project on building highways to connect all cities in the country. The cost of building a highway between two cites i and j is c(i, j) > 0. If you were in charge from the beginning, this would have been a minimum spanning tree problem and could be solve easily with the algorithms covered in class. Since you pick it up halfway, however, some suboptimal choices have already been made by your predecessor. In other words, highways were already built between some pairs of cities. Design an algorithm to find a cost minimizing set of highways to built subject to the choices already made. Do not copy others.

