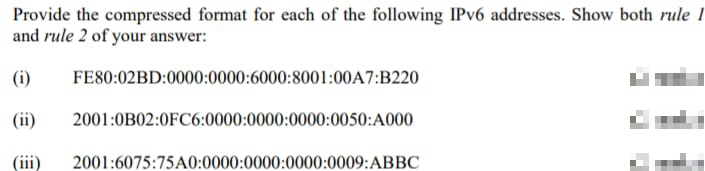
Provide the compressed format for each of the following IPv6 addresses. Show both rule I and rule 2 of your answer: (i) (ii) FE80:02BD:0000:0000:6000:8001:00A7:B220 2001:0B02:0FC6:0000:0000:0000:0050:A000 2001:6075:75A0:0000:0000:0000:0009:ABBC
Q: Write a scenario that could be used to help design tests for the wilderness weather station system.
A:
Q: Indices can speed up query processing, but it's usually a terrible idea to index every attribute,…
A: Introduction: You can use an index, a type of database structure, to enhance the efficiency of…
Q: ain why TIME. WAIT is a somewhat r bus problem if the server initiates the if the client does.…
A: Introduction: Below describe the why TIME. WAIT is a somewhat more serious problem if the server…
Q: Use Karnaugh map to reduce the following Boolean expression then draw the digital circuits for the…
A: Given boolean expression: F= A'BC+ABC'+ A'B'C+A'B'C' +A'BC' The given expression consists of 3…
Q: a) A language is a finite set of strings over some finite set of alphabets. A language L can be…
A: As per company guidelines, only 3 sub parts will be answered. So, please repost the remaining agian.…
Q: Name at least three tasks performed by the WinMain (startup) procedure.
A: Answer:
Q: Write a program that prompts the user to input an integer between 0 and 35. If the number is less…
A: The input is taken in num variable from the user. int diff = num - 10; //asciiOfA to be…
Q: Write a program that draws 5 dice on the screen depicting a straight (1, 2,3, 4, 5 or 2, 3, 4, 5,…
A: Lets see the solution.
Q: am[20] index=0 for 1 to 20 //get user input value into array arr[index]=input index=index +1…
A: As per the requirement first program is developed in c++. Note: As per our guidelines we are suppose…
Q: A micro instruction format has micro operation field which is divided into 2 subfields F1 and F2,…
A: Logic , if there are n micro- operation then we can represent it in form of 2n where n will…
Q: ORIGINAL SOLUTIONS ONLY PLEASE. I NEED TO EXPLAIN IN WORDS/ EXPLANATION NO ACTUALL CODING TO ANSWER…
A: Greedy algorithm for coin change program: The coin array is sorted in descending order. Initialise…
Q: Label the Recursion Requirements. int fact (int n) { int result; } if(n==1) return 1; result fact…
A: ANSWER:
Q: Construct an appropriate SQL query (Create Table) for the following i. Member ii. Make
A: “Since you have asked multiple questions, we will solve the first question for you. If you want any…
Q: What will happen if traceroute is used to find the path to an unassigned address? Does it matter if…
A:
Q: Suppose two hosts A and B are connected via a router R. The A-R link has infinite bandwidth; the R-B…
A: Here is explanation regarding the graph.
Q: The statement PORTD = 0b11010110 will map the 7-segment LEDs in this order; BAFG.EDC Select…
A: The given statement; The statement PORTD = 0b11010110 will map the 7-segment LEDs in this order;…
Q: What is an outlier? Why do we need to treat outliers carefully?
A: The answer is provided below.
Q: Write a program that takes in a positive integer as input, and outputs a string of 1's and O's…
A: Function IntegerToBinary(integer x) returns nothing integer array(32) binaryNumber integer i integer…
Q: The program should then print positive integer as follows: The number of integers entered (not…
A: Since no language is asked in the problem. I am using c language. Here is c program implementation…
Q: Suppose the round-trip propagation delay for Ethernet is 46.4 µs. This yields a minimum packet size…
A:
Q: Write the language denoted by the following regular expressions: (i) (?∗?∗)∗ (ii) ?(?|?)∗? (iii)…
A: The question has been answered in step2
Q: Write a c++ code that takes a 4-digit binary number as an input and converts it into decimal then…
A: Here is c++ program to implement the 4 digit binary number and convert into decimal point. See below…
Q: a) If M be the DFA whose state diagram is shown in the figure, Then Construct the transition table…
A: “Since you have posted a question with multiple sub-parts, we will solve first three subparts for…
Q: The telephone system uses geographical addressing. Why do you think this wasn't adopted as a matter…
A:
Q: Regular expression is an algebraic notation for describing sets of strings. A regular expression…
A: Regular expressions are the patterns which are used to match the character combination in the…
Q: In your own words, describe what happens at every step of our network model, when a node on one…
A:
Q: Which of the following is not a Python type-conversion function?a) float b) round c) int d) abs
A: Introduction A specific range of values is utilised to store data for each type of data in Python.…
Q: ode structure for how to merge 2 seperate strings using ONLY C. eg; string 1 = ''i eat pie'' and…
A: Algorithm : 1. Input two strings from the user. 2. Pass the string inputs to a function…
Q: Explain why design conflicts might arise when designing an architecture for which both availability…
A:
Q: In your own words, describe what happens at every step of our network model, when a node on one…
A: Computer Networks refers to the set of the computers that are interconnected by the transmission…
Q: Draw Gantt Chart and calculate the average waiting time using the given table ?? Burst Time 10 1 2 1…
A: Below is the following solution of your question:
Q: Aim Create a class called TabletCamera and a class called Facial_recognition that will be the base…
A: The code is given in the below step
Q: A method that returns the value of an object's instance variable is calleda(n)a) mutator b) function…
A: A variable that is declared in a class but not within constructors, methods, or blocks is known as…
Q: Let L be a language defined over a unary alphabet Σ = {0}: L = {0k | k = 0 mod 2 or k = 0 mod 3}…
A:
Q: Write a C++ program that reads strings until "QUIT" input, which then displays all strings in the…
A: According to the information given:- We have to follow the instruction in order to get desired…
Q: 1 import java.util.Scanner; 2 3 public class MaxOf Two { 4 5 6 7 8 9 .0 1 _2 min 6 3 4 5 -6 7 .8 _9}…
A: In method getUserValues, we will use for loop that varies from 0 to array size -1 to input array…
Q: 2. What are the main benefits of using encapsulation in Java?
A: Introduction: Encapsulation is one of the four pillars of Object-Oriented concepts along with…
Q: Why is encapsulation called Data Hiding?
A: Introduction Data encapsulation, otherwise called data hiding, is the system by which the execution…
Q: Write a program that calculates the cost per square inch of a circular pizza,given its diameter and…
A: We need to find the per square inch of any circular pizza where diameter and price of pizza will be…
Q: You are a software engineering manager and your team proposes that model-driven engineering should…
A: Model driven engineering is a software development methodology that focuses on model creation,…
Q: Many documents use a specific format for a person's name. Write a program whose input is: firstName…
A: Step-1: Start Step-2: Declare a variable name and take input from the user Step-3: Declare an array…
Q: Find out the generic format for TCP header options from Request for Comments 793.
A: TCP Header TCP header holds several information fields with the host address of source and…
Q: Given the variable names pathName contains a string describing a directory path, write a statement…
A: Note- since programming language is not specified we providing answer in python programming. Answer…
Q: PART A) Write a Python statement to create a List structure containing the names of the seasons of…
A: answer for this given in step2.
Q: Write a C++ program that reads strings until "QUIT" input, which then displays all strings in the…
A: I have provided C++ CODE along with CODE SCREENSHOT and also provided OUTPUT SCREENSHOT------…
Q: Assume that a string variable named myStuff has been declared and contains some string value. Write…
A: The below-given program will obey the following rubrics: Declaring a string variable, myStuff with…
Q: nto two subnets, and divide the 72.16.0.0 (class B IP address) into
A: The answer is
Q: *Data Structures and Algorithm Professor Holmes came up with the idea of a sorting algorithm that…
A: Trinary Sort has the below features:- Claimed to be asymptotically faster than merge sort. Splits…
Q: Write the following SQL queries based on the following relational schema: Student (stdID: char(5),…
A: Ans:- So let’s start solving the problem here I give the complete SQL query of the problem and…
Q: You are a software engineering manager and your team proposes that model-driven engineering should…
A: The field of computer programming offers new instruments every once in a while. Whenever utilized…
Step by step
Solved in 2 steps with 2 images

- Provide short answers to the following: How do you determine whether an IP address is a multicast address? What is the TTL field in the IP header used for? What is the maximum length of options bytes that can be carried in an IPv4 header? Why do we have to multiply the offset field of an IP datagram by eight to obtain the real offset for the first byte of the datagram?Question 9 Convert the following IPv4 address into dot decimal address, and determine which type of these addresses are. a) 10000001 00001011 00001011 11101111 b) 11000001 10000011 00011011 11111111 c) 11100111 11011011 10001011 01101111 Computer network Full explain this questionProvide short answers to the following: How do you determine whether an IP address is a multicast address?==solve What is the TTL field in the IP header used for?==solve What is the maximum length of options bytes that can be carried in an IPv4 header?==solve Why do we have to multiply the offset field of an IP datagram by eight to obtain the real offset for the first byte of the datagram?====need to solve this question
- Write the following IPv6 address in its smallest or most abbreviated format: AD89:00C0:0204:0000:0000:ABC0:000B:0000Determine whether or not the following IPv6 address notations are correct:•::0F53:6382:AB00:67DB:BB27:7332•7803:42F2:::88EC:D4BA:B75D:11CD•::4BA8:95CC::DB97:4EAB•74DC::02BA•::00FF:128.112.92.116Using the two rules of IPv6 compression, edit each IPv6 address until it is in the shortest form possible. 2b06:0000:0000:1f2b:d77f:0000:0000:89ce 0e56:11c2:0e75:8d23:3528:7e0d:419b:bdce 00eb:0000:0000:0000:d8c1:0946:0272:0879 ad93:a0e4:a9ce:32fc:cba8:15fe:ed90:d768 558c:0000:0000:d367:7c8e:1216:0000:66be 8bfa:99f0:d4c5:0b8c:0f6f:04df:2804:283d 5d66:5ec9:0046:0000:2576:004f:7159:0639 7d2b:00a9:a0c4:0000:a772:00fd:a523:0358 00c8:b434:06ee:ec2f:03c9:01ce:765d:a66b 9930:cafa:0000:0052:04cc:7b7a:0037:27e6
- Compress the following IPv6 addresses into their shortest expression 2100:1CB0:0032:FA30:0000:0000:A000:5/64Given the following IPv6 address 2ABCD:0000:0000:0000:00B7:0000:0000:00C6 rewrite it in its shortest possible format?For each IPv4 network prefix given (with length), identify which of the subsequent IPv4 addresses are part of the same subnet. (a). 10.0.130.0/23: 10.0.130.23, 10.0.129.1, 10.0.131.12, 10.0.132.7 (b). 10.0.132.0/22: 10.0.130.23, 10.0.135.1, 10.0.134.12, 10.0.136.7 (c). 10.0.64.0/18: 10.0.65.13, 10.0.32.4, 10.0.127.3, 10.0.128.4 (d). 10.0.168.0/21: 10.0.166.1, 10.0.170.3, 10.0.174.5, 10.0.177.7 (e). 10.0.0.64/26: 10.0.0.125, 10.0.0.66, 10.0.0.130, 10.0.0.62
- Subject rcs511 In an IPv4 datagram, the M bit is 0, the value of HLEN is 10, the value of total length is 400 and the fragment offset value is 300. The position of the datagram, the sequence numbers of the first and the last bytes of the payload, respectively areFor the following Ips, write the network name, BC address, Prefix length, and thedefault maskNet name BC Prefix length default mask 11.45.3.5 180.90.27.89 190.35.177.98 192.76.19.1 200.30.50.90 100.100.100.100 107.39.50.20 192.3.5.6 For IP address: 175.30.101.205, use the provided version of the subnet mask to calculate the: slash notation binary subnet mask dotted decimal subnet mask Increment Network ID Broadcast ID Host Range Complete the Increment by determining the value of the last network bit for the given subnet mask. It is easiest to observe in the binary representation. Since network IDs will always be multiples of the increment (after the zero subnet) – in the octet that holds the last network bit, use the increment to determine the network ID, broadcast, and host range for the IP address displayed above

