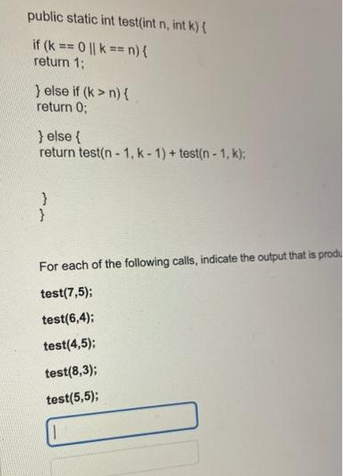
public static int test(int n, int k) { if (k == 0 || k == n) { return 1; } else if (k>n) { return 0; } else { return test(n-1, k-1)+ test(n-1, k); } For each of the following calls, indicate the output that is produ test(7,5); test(6,4): test(4,5); test(8,3); test(5,5);
Q: What does it mean for the transport layer to offer the network layer a packetizing service? What is…
A: Transport layer and Network layer are the two layers of the network which are present adjacent to…
Q: Explain distributed denial of service (DDoS) attacks in detail.
A: We need to discuss DDoS attacks.
Q: We'll go over array notation writing in this part.
A: An Array Notation: The majority of arrays may be written literally using array notation, often…
Q: Data communication is the transmission and reception of information between two sites using…
A: Definition: Two or more people connect and share ideas, thoughts, files, documents, and so on via…
Q: Which of the following is one of the set operators? Select one: O A, B, C, D
A: Answer: 1) The set of operators in SQL are 1.UNION 2.UNION ALL 3.INTERSECT 4.EXCEPT…
Q: What makes address alignment such a crucial concept in computer science?
A: Introduction: Unaligned memory access is the access of data with a size of N number of bytes from an…
Q: ent from ot
A: Assembly language: In computer programming, assembly language (or constructing agent language, or…
Q: What does "Ethernet" mean in terms of networking?
A: The standard method for establishing connections between devices in a wired LAN or WAN is Ethernet…
Q: How does assembly language function in the real world?
A: Introduction: A single line of text translated into one computer command is an assembly language…
Q: you are required to write two classes: one that represents a TCP server and the other represents a…
A: Hello student
Q: botnets and the DDoS assa
A: The phrase "botnet" is short for "robot network," which describes a collection of robot machines…
Q: What distinguishes assembly language from other coding languages?
A: Assembly language: Assembly language, also known as building agent language, symbolic machine code,…
Q: It is necessary to describe how botnets are generated and how they are used in DDoS attacks.
A: Let's learn what is a Botnet , how it is created and how it can be used in DDoS attack
Q: What is an illustration of a well-designed metaheuristic that shows both its benefits and drawbacks?
A: Given: We have to discuss what is an illustration of a well-designed metaheuristic that shows both…
Q: What distinguishes von Neumann architecture from other forms of art?
A: It is a sort of digital computer architecture in which the design is based on the concept of…
Q: What "numbering hexadecimal" implies is explained.
A: Introduction Hexadecimal : Hexa is a Greek word that signifies six. Hexadecimal is a positional…
Q: We'll go over how to create a botnet and use it in a DDoS attack in this article
A: A botnet is comprised of multiple computers working together with the objective of completing…
Q: Instructions for Part 2 In part 2 (and probably in every part) I'm going to use "matrix" and…
A: Answer:
Q: Ethernet may be used to describe the physical media.
A: Answer is
Q: Can you find objects that support Comparable in an unordered list? What makes you believe that is…
A: Definition: Assembly language is similar to C++ and Java. Assembly language is a low level…
Q: Discuss how a Cloud computing-based infrastructure may support the operations and decision making in…
A: Question: Discuss how a Cloud computing-based infrastructure may support the operations and decision…
Q: E_DFA Running Time Low that EDFA = {(D) | Di
A: I have proved that given DFA belongs to P
Q: What makes address alignment such a crucial concept in computer science?
A: Address the significance of alignment. Address alignment is the organisation of the memory's stored…
Q: What terms may be used to describe network designs?
A: We need to describe the terms used for network design.
Q: How do logical and linear addresses differ from one another, and how do they connect to one another?
A: Introduction What are logical and linear addresses, and how do they relate to one another?
Q: Countermeasures should be stated as specific plans of action to manage and reduce risks associated…
A: Introduction: A strategy or tool for neutralising or compensating for the effects of another The…
Q: Find the applications of the following in logic programming languages. Expert Systems for the…
A: The question has been answered in step2
Q: You found an exciting summer job for five weeks. It pays, say, $15.50 per hour. Suppose that the…
A: I have solved your required logic in C++ and defined comments for each line , kindly check it out ,…
Q: Write a program that reads in a set of coin descriptions from a file. The input file has the format…
A: Question Write a program that reads in a set of coin descriptions from a file. The input file has…
Q: What Advantages Do Networked Communications Offer?
A: A network is a collection of computers that are linked to one another to make it easier for users to…
Q: he difference between Harvard and von Neumann systems in terms of computer a
A: the difference is an given below :
Q: What makes address alignment such a crucial concept in computer science?
A: Aligned Address: The address must be multiple of the transfer size in order for the access to be…
Q: There are two VPN protocols listed. Describe the steps involved in creating Virtual Private Networks…
A: The data transmission between your computer (or another device) and the VPN server is governed by a…
Q: When it comes to firewall security, what should you permit and what should you block? Why?
A: This is achieved by permitting or blocking specified data packets depending on predefined security…
Q: All facets of the DNS are explained, including iterated and united queries, authoritative and root…
A: Given: We have to discuss All facets of the DNS , including iterated and united queries,…
Q: Detail the features of the Python library file for pandas.
A: - We have to talk about python library pandas
Q: Why is it important for the network layer protocol to offer the transport layer packetizing…
A: Introduction: Network Layer: The network layer of the OSI model is the layer that enables the host…
Q: What are the benefits and drawbacks of using an array?
A: Introduction: An array is a collection of elements of the same data types that are stored in…
Q: What is the formal definition of assembly language and how does it really function?
A: Firstly, it doesn’t offer cease-to-cease encryption. TOR encryptsyour information whilst it enters…
Q: Do you understand how a network is put together?
A: Introduction: Network: A network is a grouping of two or more connected computers or other…
Q: Identify the most important considerations for classes and constructors.
A: Introduction Class and Constructor: When a class is created using the NEW function, a particular…
Q: What does it mean for the transport layer to offer the network layer a packetizing service? What is…
A: System layer: In the PSI model, the network layer is the one utilised to give the host's ability to…
Q: A management information system (MIS) does exist in Peoples’ Choice Bank. Management at the bank are…
A: 1. Firstly what is MIS? Management Information System (MIS) is a management system that is used by…
Q: DDoS attacks can be started by a single individual, but how do they operate?
A: Introduction: DDoS attack: It entails saturating the network of a website or live service with…
Q: omeone refers to an operating system? What, in your opinion, are the two core responsibilities of an…
A: An operating system (OS) is responsible for managing a computer's hardware and software resources…
Q: Using suitable illustrations, discuss: A. The different flavours of machine learning and explain,…
A: NETWORK SOLUTIONSComputer networks, including the Internet, play critical roles in business and…
Q: consider a real world distributed system you are familiar with, deduce and discuss how the…
A: Challenges and implementations of distributed systems:
Q: Here is a list of the five different kinds of DoS assaults.
A: Denial of Service (Dos) attack explanation An person or group's malicious effort to attack a network…
Q: Using examples, describe how traditional personnel practices are combined with controls and…
A: Information Protection: It is characterised as method to protect data from unauthorized access.…
Q: What is the frequency of peering between two Internet service providers (ISPs) at the same level? An…
A: The four major kinds of Internet Services are shown in the following figure. Services for…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- public class solution { public static int countZerosRec(int input){ if(input<10){ if(input==0){ return 1; }else{ return 0; } } if(input % 10 == 0){ return countZerosRec(input/10)+1; } else{ return countZerosRec(input/10); }.coding need complete.A pentagonal number is defined as n(3n−1) ∕ 2 for n = 1, 2, . . ., etc.. Therefore, the first few numbers are 1, 5, 12, 22, . . . . Write a method with the following header that returns a pentagonal number:public static int getPentagonalNumber(int n) For example, getPentagonalNumber(1) returns 1 and getPentagonalNumber(2) returns 5. In Java, Write a test program that uses this method to display the first 100 pentagonal numbers with 10 numbers on each line. Numbers are separated by exactly one space.Complete the method definition to return the hours given minutes. Output for sample program:3.5 -java code- import java.util.Scanner;public class HourToMinConv { public static double getMinutesAsHours(double origMinutes) { /* Your solution goes here */ } public static void main (String [] args) { Scanner scnr = new Scanner(System.in); double minutes; minutes = scnr.nextDouble(); // Will be run with 210.0, 3600.0, and 0.0. System.out.println(getMinutesAsHours(minutes)); }}
- 7 public static int test1(int x1, int x2){ 8 9 if(x1==0){ 10 x1=10; 11 } 12 if(x2==0){ 13 x2=10 14 } 15 16 return x1*x2; 17 } 18 19 public static int test2(int x2, int x1){ 20 return x2-x1; 21 } 22 public static int input(){ //Don’t need to trace through //this method to show how it works. Just assume it pulls //the value for the user. 23 Scanner keyboard = new Scanner(new BufferedReader(new InputStreamReader(System.in))); 24 int counter=0; 25 System.out.print("Please enter an integer: "); 26 while(counter<3 && !keyboard.hasNextInt()) 27 { 28 System.out.println(); 29 String temp=keyboard.next(); 30 System.out.println(temp+" is not an integer. Please reenter an integer."); 31 counter++; 32 33 } 34 return keyboard.nextInt(); 35 } 36 37 38…What is the probability that in a classroom of x people, at least 2 will be born on the same day of the year (ignore leap year)? Use a Monte Carlo Simulation and a frequency table to write a program that calculates this probability, where the number of people (x) in the simulated class is given by the user. PLEASE USE the outline of the code GIVEN to answer this question: import mathimport random # create and initialize frequency table:ft = []k = 0while(k < 365) : ft.append(0) k = k+1 # Allow the user to determine class size:print("Please type in how many people are in the class: ")x= int(input()) success = 0 # Simulate:c = 0while(c < 10000) : # Step 1: re-initialize birthday frequency table (it must be re-initialized for each play-through (why?): k = 0 while(k < 365) : ft[k] = 0 k = k+1 # Step 2: randomly get x birthdays and update frequency table: k = 0 while(k < x): # your code goes here ########################## k = k+1 # Step 3:…please answer correctly Algorithm Running Time package test; import java.util. *; import java.util.Random; public class Test { private long start = 0; public Test() { start = System.currentTimeMillis(); } public double elapsedTime() { long now = System.currentTimeMillis(); return (now - start) / 1000.0; } private static long constant_value(long paramInt) { long l = 0L; for (int i = 0; i < paramInt; i++) l += 1L; return l; } private static long logarithmic(long paramInt1, long paramInt2) { long l = 0L; for (int i = 1; i + i <= paramInt1; i += i) l += constant_value(paramInt2); return l; } private static long sqrt(long paramInt1, long paramInt2) { long l = 0L; int i = 0; for (int j = 0; j < paramInt1; i++) { l += constant_value(paramInt2);j += i; } return l; } public static long linearithmic(long paramInt1, long paramInt2) { if (paramInt1 == 0)…
- What is the probability that in a classroom of x people, at least 2 will be born on the same day of the year (ignore leap year)? Use a Monte Carlo Simulation and a frequency table to write a program that calculates this probability, where the number of people (x) in the simulated class is given by the user. The probability for a class of size 23, should be right around 50%. NO language of "break" or "true" please! Please use the outline given below for the code:A pentagonal number is defined as n(3n-1)/2 forn = 1 , 2 , …, and so on. Therefore, the first few numbers are 1, 5, 12, 22,. . . . Write a method with the following header that returns a pentagonalnumber:public static int getPentagonalNumber(int n)For example, getPentagonalNumber(1) returns 1 and getPentagonalNumber(2) returns 5. Write a test program that uses this method to display thefirst 100 pentagonal numbers with 10 numbers on each line. Use the %7d formatto display each number.What is the probability that in a classroom of x people, at least 2 will be born on the same day of the year (ignore leap year)? Use a Monte Carlo Simulation and a frequency table to write a program that calculates this probability, where the number of people (x) in the simulated class is given by the user. The probability for a class of size 23, should be right around 50%. NO language of "break" or "true" please! PLEASE USE THE OUTLINE GIVEN BELOW TO WRITE THE CODE: # What is the probability that in a classroom of x people, at least 2 will be born on the same day of the year (ignore leap year)?# I have given you the skeleton and some of the code... you complete it using a frequency table!# Note: In a classroom of only 23 people, the probability is about 50.7% !# Try first with 10000 trials and then try with 100000 trials. This code runs somewhat slowly in repl.it import mathimport random # create and initialize frequency table:ft = []k = 0while(k < 365) : ft.append(0) k = k+1…
- Write a recursive method called digitCount() that takes a positive integer as a parameter and returns the number of digits in the integer. Hint: The number of digits increases by 1 whenever the input number is divided by 10. Use Java. Ex: If the input is: 345 the method digitCount() returns and the program outputs: 3 Ex: If the input is: 0 the method digitCount() returns and the program outputs: 1 import java.util.Scanner; public class LabProgram {/* TODO: Write recursive digitCount() method here. */public static void main(String[] args) {Scanner scnr = new Scanner(System.in);int num, digits;num = scnr.nextInt();digits = digitCount(num);System.out.println(digits);}}IN JAVA - Write a program whose input is two integers, and whose output is the first integer and subsequent increments of 5 as long as the value is less than or equal to the second integer. End with a newline. Ex: If the input is: -15 10 the output is: -15 -10 -5 0 5 10 Ex: If the second integer is less than the first as in: 20 5 the output is: Second integer can't be less than the first. For coding simplicity, output a space after every integer, including the last. BASE CODE: import java.util.Scanner; public class LabProgram { public static void main(String[] args) { /* Type your code here. */ }}Java program Write a test program that inputs, sorts, outputs Integer and Float. And call the isEqualTo method.

