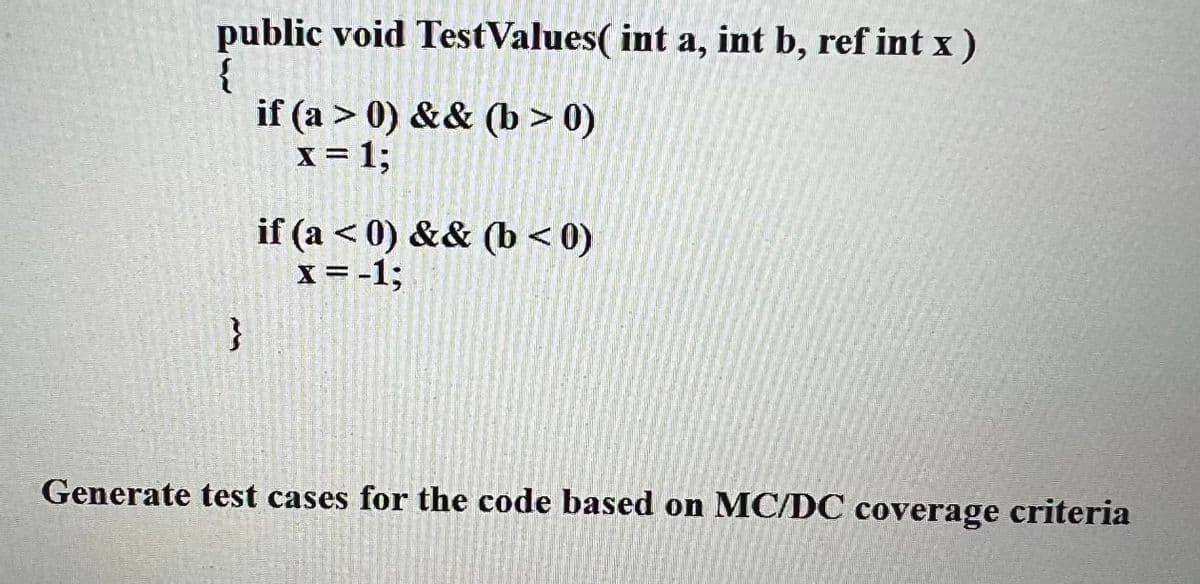
public void Test Values( int a, int b, ref int x) { } if (a > 0) && (b> 0) x = 1; if (a <0) && (b<0) x = -1; Generate test cases for the code based on MC/DC coverage criteria
Q: Which steps while utilizing an application to access a database are mostly the same?
A: The procedures for using an application to access a database must be highlighted.
Q: Is it possible for a data leak to materially affect cloud storage security? Can anything be done to…
A: We have to explain that it is possible for a data leak to materially affect cloud storage security.
Q: What does XBRL imply by the phrases fact, concept, and taxonomy?
A: Taxonomy: In taxonomy, living things are categorised into kingdoms, phyla, classes, orders,…
Q: In the majority of retail locations, barcode scanners are already standard equipment. Include one…
A: Given: Optical scanners include barcode readers and barcode scanners. These scanners can decode…
Q: Do you agree that "there is no concept of client and server sides of a communication session" in a…
A: The answer of the question is given below
Q: What are mobile apps exactly, and why are they so crucial?
A: Introduction: Apps are the intended to operate on mobile devices such as tablets, phones, watches,…
Q: Understanding the factors that lead to video data requiring and using more storage space than other…
A: Introduction: Why do video data need more storage space than other data types. A video is a picture…
Q: 4. (Looping statement) java Given an integer, display its reversed order. Sample Output:…
A: Coded using Java Language.
Q: In your opinion, which video game genre has reached a "turning point" in its evolution? Why
A: Answer : PUBg is one of the turning point for all the game genre because it play all over the world…
Q: Do you believe that it is still feasible to improve cloud security after a data breach has already…
A: Introduction : What is data breach : A data breach is an incident in which sensitive information is…
Q: The relationship between digital devices and mobile cellphones, as well as the current convergence…
A: The question has been answered in step2
Q: What is a horse of Troy? Three instances
A: Horse of troy Trojan horse or horse of troy is a program that is downloaded and installed on a…
Q: What do we find so and its components
A: Delegation even model For handling events in GUI programming languages, the Delegation Event model…
Q: What precisely is a Trojan horse and how does it work? Please provide three examples to support your…
A: A computer virus is a type of computer program that when executed replicates itself by modifying…
Q: Question 7 Match the items on the left with the ones on the right. Hint: program using sizeof…
A: Hey dear, I hope you will be fine the above questions are done below.
Q: Since our birth in this century, dubbed as the Information Age, everything from computers to tablets…
A: The answer is given below.
Q: What is a Trojan horse, and how does it operate? Provide three concrete instances.
A: These question answer is as follows
Q: In the majority of retail locations, barcode scanners are already standard equipment. Include one…
A: Introduction: Optical scanners include barcode readers and barcode scanners. These scanners can…
Q: How important is it to have spreadsheet software skills?
A: Given :
Q: Selection structures are frequently used in programming, however they are not perfect. For a variety…
A: Introduction: The terms "frontend" and "backend" are the most frequently used in web development.…
Q: how those technologies relate to mobile smartphones is vital.
A: Current digital device convergence trends are as follows: Device convergence is the display of…
Q: Can you explain why authentication is still a challenge in the modern information age?
A: Authentication is the process of determining whether someone or something is, in fact, who or what…
Q: An understanding of the present convergence of digital gadgets and how those technologies relate to…
A: The question has been answered in step2
Q: Do you agree that "there is no concept of client and server sides of a communication session" in a…
A: P2P (or peer-to-peer) is a file-sharing technique that is used in the field of computer networking.…
Q: An understanding of the present convergence of digital gadgets and how those technologies relate to…
A: Introduction Digital gadgets: Digital devices, sometimes known as gadgets, are innovative…
Q: Activity Description: The aim of this activity to check students' understating about modeling the…
A: A DFD , 'data flow diagram' is a graphical representation of the drift of the information thru an…
Q: in computer organization and architecture create a simple program to evaluate the performance of a…
A: INTRODUCTION: The quantity of work a computer system can complete is called its performance. The…
Q: This thorough book will cover everything from DNS records to authoritative servers to iterative and…
A: DNS transforms domains to IP addresses, allowing: Web browsers access the Internet. Each network…
Q: What actions may be made to improve the security of cloud storage after a data breach? What are some…
A: It has become very common to have data breaches.
Q: int x //x coord of the center -int y // y coord of the center -int radius -static int count //…
A: Solution: Code // Circle.h #ifndef CIRCLE_H_ #define CIRCLE_H_ #include <string> using…
Q: Selection structures are frequently used in programming, however they are not perfect. For a variety…
A: Given: The terms "frontend" and "backend" are the most frequently used in web development. Although…
Q: Draw a NDPA for L = {a^mb^n|0 ≤ n ≤m} Draw a graphical representation and table representation List…
A: The given Language is:- L = {a^m b^n | 0 <= n <= m} i.e., L = {aab, aabb, aaabb, aaab, .....}
Q: Give the names of the three different kinds of servers that a local bank could use.
A: Here we describe three servers a local bank may utilise. DESCRIPTION Today, technology is…
Q: When explaining the DNS, be sure to mention authoritative and root servers, iterated and…
A: DNS authoritative and root servers The 13 DNS root nameservers are known to each recursive…
Q: In many ways, laptop computers and mobile devices seem to be very unlike. Your argument should be…
A: Answer: ->Mobiles and tablets have less storage capacity than computers, and their components…
Q: What are some of the authentication procedure's goals? Compare the pros and downsides of various…
A: We need to discuss authentication procedure's goals and compare the pros and downsides of various…
Q: Describe the most successful ways for discovering images that may be used without authorization.
A: Steps to take: The best approaches to look for photographs that are copyright-free must be…
Q: mpare the difference between a resource template and a text analysis packa
A: Lets see the solution.
Q: What do you think are some possible solutions to the issues that these people confront, and what…
A: The answer is given in the below steps Happy to help you ?
Q: Every aspect of our culture has been influenced by computers, including the workings of our economy,…
A: The development of computers has had a significant influence on human existence, and artificial…
Q: What precisely do you mean when you state authentication's objectives? Contrast and compare the…
A: The response to the question is Your sign-in procedure is more secure when authentication mechanisms…
Q: What does ransomware really accomplish in terms of computer security?
A: Given: When ransomware infects a computer, it encrypts the user's data and locks it until the user…
Q: How do DNS records, iterated and non-iterated requests, authoritative servers, and root servers fit…
A: The answer is given in the below step
Q: It is possible to describe an isochronous connection and a synchronous connection by comparing and…
A: The answer of the question is given below
Q: Give five recommendations to help stop ransomware attacks.
A: Five recommendations to help stop ransomware attacks. If you have been unfortunate enough to be the…
Q: Debate against the following statement: "It is unethical to share photographs or recordings of…
A: Answer : No . it's not like that if any photo of any person is looking good and beautiful than it…
Q: How can a computer processor avoid wasting computation cycles when it executes many instructions…
A: Solution:
Q: The relationship between digital devices and mobile cellphones, as well as the current convergence…
A: Digital convergence is simply the process of digital material being accessible via many…
Q: Make a distinct contrast between the kinds of typefaces, the font sizes, and the font styles.
A: Required: Make a clear difference between the types of typefaces, the sizes of the fonts, and the…
Q: How does ransomware function in terms of computer security?
A: Infected computers get infected with ransomware, which encrypts and locks the user's data until a…
Step by step
Solved in 2 steps

- When the given integer variable numberOfTools is: less than 14, output "Small tool box". between 14 inclusive and 39 inclusive, output "Mid-sized tool box". greater than 39, output "Need wall storage". End with a newline. Ex: If the input is 13, then the output is: (in java) Given Code: import java.util.Scanner; public class ToolDetails {public static void main(String[] args) {Scanner scnr = new Scanner(System.in);int numberOfTools; numberOfTools = scnr.nextInt();Java Program Fix this Rock, Paper and scissor program so I can upload it to Hypergrade and it can pass all the test cases. Here is the program: import java.util.Random;import java.util.Scanner;public class RockPaperScissors { public static void main(String[] args) { if (args.length != 1) { System.out.println("Please provide a seed as a command line argument."); return; } long seed = Long.parseLong(args[0]); Random random = new Random(seed); Scanner scanner = new Scanner(System.in); System.out.println("Enter 1 for rock, 2 for paper, and 3 for scissors."); do { int computerChoice = random.nextInt(3); int userChoice = getUserChoice(scanner); if (userChoice == -1) { continue; } System.out.println("Your choice: " + choiceToString(userChoice) + ". Computer choice: " + choiceToString(computerChoice) + "."); int result =…public class Turn{public static void main(String[] args){// Different initial values will be used for testingint x = 1; int y = 1; // Turn the arrow by 90 degrees System.out.print("x:", y + 90);System.out.println(x);System.out.print("y: ", x - 1 );System.out.println(y); // Turn the arrow again System.out.print("x:", y - 1);System.out.println(x);System.out.print("y: ",x + 90);System.out.println(y);}}
- Submit in python or c++. Error code will downvoted. Every cell (x,y) contains an integer ax,y signifying the course of how the ball will move. ax,y=1 — the ball will move to one side (the following cell is (x,y+1)); ax,y=2 — the ball will move to the base (the following cell is (x+1,y)); ax,y=3 — the ball will move to one side (the following cell is (x,y−1)). Each time a ball leaves a cell (x,y), the integer ax,y will change to 2. Mr. Chanek will drop k balls successively, each beginning from the primary line, and on the c1,c2,… ,ck-th (1≤ci≤m) sections. Decide in which segment each ball will wind up in (position of the ball in the wake of leaving the network). Input :The principal line contains three integers n, m, and k (1≤n,m≤1000, 1≤k≤105) — the size of the framework and the number of balls dropped by Mr. Chanek. The I-th of the following n lines contains m integers ai,1,ai,2,… ,ai,m (1≤ai,j≤3). It will fulfill ai,1≠3 and ai,m≠1. The following line contains k integers c1,c2,……The questions should be completed with OCaml. Running screenshots should be provided. The background information is given by the picture. Question 1: Provide 5 good test cases each for eval_success_tests and eval_failure_tests, following the format of: let eval_success_tests : ((truth_assignment * formula) * bool) list = [] let eval_failure_tests : ((truth_assignment * formula) * exn) list = [] Question 2: Implement the function eval : truth_assignment -> formula -> bool. let eval (state : truth_assignment) (formula : formula) : bool = raise Not_implemented You are evaluating boolean formulae instead of float arithmetic. You also need to use the correct boolean value for each variable. We recommend using Variable_map.find_opt to perform lookups in the truth assignment. If a variable is needed but does not appear in the truth assignment, you must raise an Unassigned_variable x exception, where x is the unassigned variable. Once again, you may use any functions you want and…4.2.3: Method definition: Volume of a pyramid. Define a method pyramidVolume with double parameters baseLength, baseWidth, and pyramidHeight, that returns as a double the volume of a pyramid with a rectangular base. Relevant geometry equations: Volume = base area x height x 1/3Base area = base length x base width.(Watch out for integer division). import java.util.Scanner; public class CalcPyramidVolume { //answer goes here// public static void main (String [] args) { Scanner scnr = new Scanner(System.in); double userLength; double userWidth; double userHeight; userLength = scnr.nextDouble(); userWidth = scnr.nextDouble(); userHeight = scnr.nextDouble(); System.out.println("Volume: " + pyramidVolume(userLength, userWidth, userHeight)); }}
- Write in the programming language Pythona pushdown automaton simulator (a program that simulates a pushdown automaton) where: V = {w | w ∈ {a, b}* and w starts and ends with the same symbol}.Complete the method definition to output the hours given minutes. Output for sample program: 3.5 import java.util.Scanner;public class HourToMinConv { public static void outputMinutesAsHours(double origMinutes) { /* Your solution goes here */ } public static void main (String [] args) { Scanner scnr = new Scanner(System.in); double minutes; minutes = scnr.nextDouble(); outputMinutesAsHours(minutes); // Will be run with 210.0, 3600.0, and 0.0. System.out.println("");}}public class TestShape { public static void main(String[] args) { /* Circle c1 = new Circle(2.67); System.out.println("c1: "); System.out.println(c1.toString()); System.out.println(); Circle c2 = new Circle(3, false, "Red"); System.out.println("c2: "); System.out.println(c2.toString()); System.out.println(); Rectangle r1 = new Rectangle(3, 2, true, "Blue"); System.out.println("r1: "); System.out.println(r1.toString()); System.out.println(); Rectangle r2 = new Rectangle(3.2, 4, false, "Red"); System.out.println("r2: "); System.out.println(r2.toString()); */ } }
- Create a program that provides visualization for three-dimensional plane: Animate your solution using any animation programming language like matlab please. (so the output should show graph of the exponential function inputted by the user)the system should be user-input, and the output should show graph of the exponential function inputted by the user) The topic is all about Inverse Laplace Transform on Exponential function.Create a java program using user defined function. Create a function/method void:-showinfo with parameter student number, first name, last name, middle initial, and age. Create a function/method return:-getSchoolName() that return the school name Far Eastern University-subtractit with parameter num1 and num2 that return the subraction result of 120-20-divideit with parameter num1 and num2 that return the division result of 50/2 No scanner method will be used, all outputs are defined and called using "user-defined" fuctions. Parameter specification: variable namesstudent number = A1first name = FNlast name = LNmiddle initial = MIage = A2 num1 = num1num2 = num2 Sample Output:Student Number: 1First Name: AnnaLast Name: PerezMiddle Initial: A.Age: 15Full Name: Anna A. Perez (Concatenation of first name, middle initial and last name)-----------------------------Student Number: 2First Name: TroyLast Name: S.Middle Initial: MedinaAge: 16Full Name: Troy S.…How do solve it? and what is output of this code: import java.util.*; public class Main {public static void main(String[] args) throws Exception {final double G= 9.8;double time; double velocity; double distance; System.out.print("Enter a value for time: ");time = keyboard.nextDouble( ); keyboard.nextLine(); velocity = G * time; distance = 0.5 *G *time * time;System.out.printf("Acceleration = %3.1f\n", G);System.out.printf("Velocity = %3.1f\n", velocity); System.out.printf("Distance = %3.1f\n", distance);}}











