put me back onto the main building page with a pop up that says 'A understand why this keeps happening!" Nhich design principles have been breached? Select one or more: O a. Strive for consistency O b. Constraints O c. Offer informative feedback O d. Natural mapping O e. Reduce short-term memory load O f. Support internal locus of control
put me back onto the main building page with a pop up that says 'A understand why this keeps happening!" Nhich design principles have been breached? Select one or more: O a. Strive for consistency O b. Constraints O c. Offer informative feedback O d. Natural mapping O e. Reduce short-term memory load O f. Support internal locus of control
Chapter7: Microsoft Edge
Section: Chapter Questions
Problem 2EYK
Related questions
Concept explainers
OOPs
In today's technology-driven world, computer programming skills are in high demand. The object-oriented programming (OOP) approach is very much useful while designing and maintaining software programs. Object-oriented programming (OOP) is a basic programming paradigm that almost every developer has used at some stage in their career.
Constructor
The easiest way to think of a constructor in object-oriented programming (OOP) languages is:
Question
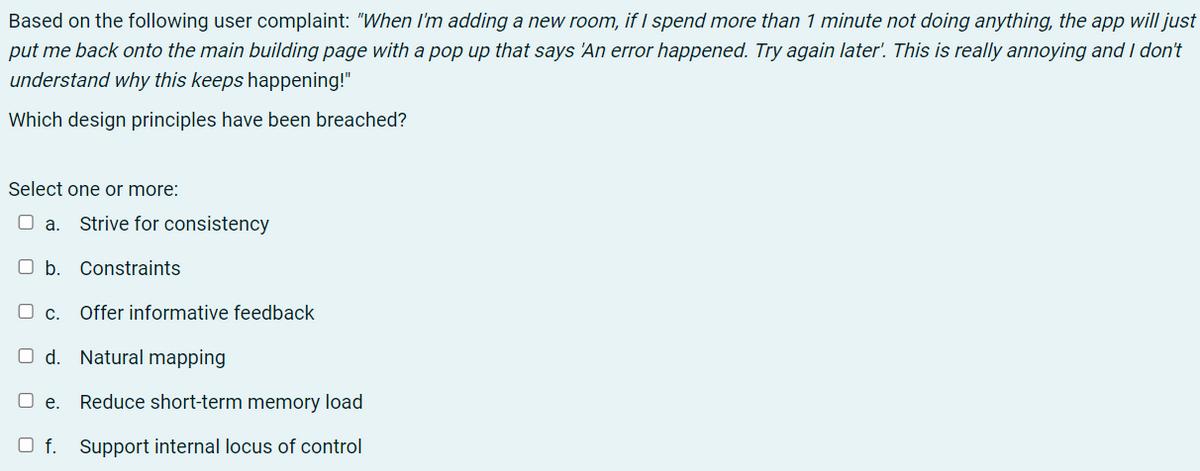
Transcribed Image Text:Based on the following user complaint: "When Il'm adding a new room, if I spend more than 1 minute not doing anything, the app will just
put me back onto the main building page with a pop up that says 'An error happened. Try again later'. This is really annoying and I don't
understand why this keeps happening!"
Which design principles have been breached?
Select one or more:
O a. Strive for consistency
O b. Constraints
O c.
Offer informative feedback
O d. Natural mapping
O e.
Reduce short-term memory load
O f. Support internal locus of control
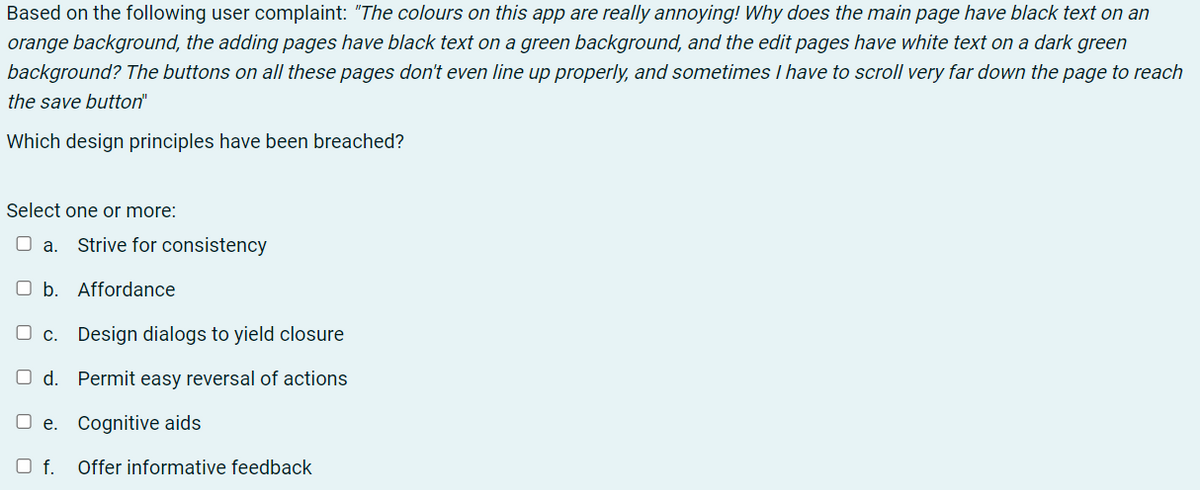
Transcribed Image Text:Based on the following user complaint: "The colours on this app are really annoying! Why does the main page have black text on an
orange background, the adding pages have black text on a green background, and the edit pages have white text on a dark green
background? The buttons on all these pages don't even line up properly, and sometimes I have to scroll very far down the page to reach
the save button"
Which design principles have been breached?
Select one or more:
O a.
Strive for consistency
O b. Affordance
c. Design dialogs to yield closure
O d. Permit easy reversal of actions
O e. Cognitive aids
O f.
Offer informative feedback
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Microsoft Windows 10 Comprehensive 2019
Computer Science
ISBN:
9780357392607
Author:
FREUND
Publisher:
Cengage

Microsoft Windows 10 Comprehensive 2019
Computer Science
ISBN:
9780357392607
Author:
FREUND
Publisher:
Cengage