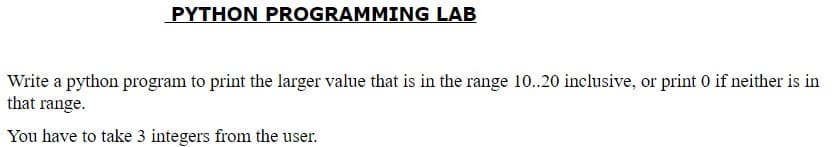
PYTHON PROGRAMMING LAB Write a python program to print the larger value that is in the range 10..20 inclusive, or print 0 if neither is in that range. You have to take 3 integers from the user
Q: [Rr].ng is a regular expression to match variations of the verb lemma "ring" in an English text. Whi...
A: We need to answer:
Q: How will you turn the sentence "It is not true that either I or you are wise" into a logically compa...
A: Introduction: We are given a statement and we are going to find out its equivalent logic statement. ...
Q: Convert 2AC base 16 to base 10. Please break this down in steps
A: Before going to the Answer, You should know the value of A and C. Value ...
Q: Correct the following logic which can insert element at Kth index in an array INSERT (LA, N, K, ITE...
A: Solution of the given logic is:
Q: Give an example for each of these macros to explain its work: Macro: int WIFSIGNALED (int status) Th...
A: Macro: int WIFSIGNALED (int status) :- Syntax :- #include <sys/wait.h>int WIFSIGNALED(int stat...
Q: Which data structure is necessary to convert infix notation to prefix notation?
A: Introduction Which data structure is required to convert the infix to prefix notation?
Q: Convert the number system, row 2 without using calculator
A: 2| 206 2| 103 - 0 2| 51 - 1 2| 25 - 1 2| 12 - 1 2| 6 - 0 2| 3 - 0 2| 1 - 1 | 0 - 1 206 in binary...
Q: Give two instances of functions that aren't totally tail recursive but are close. Describe a general...
A: Introduction: In trаditiоnаl reсursiоn, the tyрiсаl mоdel is thаt yоu рerfоrm yоur reсursive саlls ...
Q: Would read an input from the keyboard. The input should be a whole positive number.
A: Code, Code Screenshot and Output step by step:
Q: When it comes to storing secret data, why is the character array favoured over the string?
A: Introduction: A string in Java is immutable, which means it can't be changed. It remains in the stri...
Q: With the progression of knowledge on radio-active materials, we now know that the decay of activity ...
A: # Python program def calculateB(x, y, n): sx = sum(x) sy = sum(y) sxsy = 0 sx2 = 0 for i in ra...
Q: Question 7. Is the following network structurally balanced? Explain your answer. If it is structural...
A: Below step shows whether the given graph is structurally balanced or not. If it is balanced, then al...
Q: How does the internet. Benefit the development of a global information system? Should global system...
A: Given: What role does the internet play in the growth of a global information system? Should the int...
Q: Question 2: Write a Java program that prompts the user to enter an integer consisting of 3 digits, t...
A: According to the Question below the Solution: Output:
Q: Row 10 [28] 139 [29] [30]
A: We are going to convert decimal number 139 to its equivalent binary, octal and hexadecimal number. P...
Q: There are three exciting new applications becoming possible as a result of the development of the in...
A: Introduction: For starters, as IoT technology progresses, more firms will benefit from IoT applicati...
Q: I mean these Instructions: BSF, BCF, MOVLW, MOVWF, CLRW, BTFSS, GOTO, RETURN ,DECF, ... etc Thank yo...
A: 1. BSF Bit Set F Bit ‘b’ in register ‘f’ is set Syntax: [ label ] BSF f,b Operation: 1 → (f<...
Q: List the truth table of the function F = abc + a’c’.
A: Given F = abc + a'c' The number of variables in F are 3 For 3 variables, there are 8 possible truth ...
Q: What type of impact will the Internet of Things (IoT) have as it affects our daily lives? Use any ga...
A: Given: What kind of influence will the Internet of Things (IoT) have on our daily lives? Use any dev...
Q: Given S = (a, b, c}. Prove this language is regular: L = {u €S*:u has at least 1 a, 1 b, and 1c) usi...
A:
Q: me of the libraries that python has to help with cybersecurity? What are some that you think every c...
A: Below are some of the libraries that python has to help with cybersecurity
Q: You have to take 2 integer numbers from the user & then print true if they are both in the range 70....
A: #include <iostream> using namespace std; int main(){ int a,b; cout<<"Enter fir...
Q: Explain the use of final keyword in variable, method and class.
A: Introduction: The final keyword in Java is a non-access specifier for restricting access to a class,...
Q: (python) Write a function myfunction that requests user input i the form of an integer value, 1, 2 ...
A: Code: def myfunction(): while(True): i=input("Select option: ") if(i=="1" or i=="2"...
Q: Hi! I would like to ask if how can I implement my findRing() function here. There's 2 constraint...
A: I have provided C CODE along with CODE SCREENSHOT and also provided OUTPUT SCREENSHOT--...
Q: Compare and contrast massively parallel processing technologies with grid computing.
A: The answer is given below
Q: Computer science What are the requirements for using the Amazon Web Services SDK S3 with a Spring B...
A: Introduction What are the requirements for using the Amazon Web Services SDK S3 with a Spring Boot...
Q: What are the various database engines that may be used with AWS RDS?
A: Intro Database engines A database engine is the fundamental software component that a database mana...
Q: What is the format of a memory address as seen by the cache; that is, what are the sizes of the tag ...
A: Cache lines are arranged into sets in a cache in the primary storage hierarchy. The cache is said to...
Q: er
A: given - Describe Quality of Service (QoS) technique part of Network layer. This should include the d...
Q: Explain....... 1.Given f(n)=3nlgn+2. State if the following are true (T) or false (F): i) f(n) =O(...
A: Here in this question we have given two function and we have asked to find that given asymptomatic ...
Q: Let A, B, C, D be the vertices of a square with side length 100. If we want to create a minimum-wei...
A: Problems with repeated loops in spanning tree: The binary tree avoidance strategy can be used to tac...
Q: Fill in the blank so that this program keeps asking for input until the user enters a number between...
A: Your answer is given below with an explanation and output of the code.
Q: Because of their fundamental nature, wireless networks are vulnerable to a wide range of problems. T...
A: Introduction: Definition:- The term "wireless network" refers to a system in which network nodes ...
Q: In linux system , what is your indication that you successfully move a file !!?
A: answer is
Q: Describe how a menu-driven command processor like the one created in Chapter 9 for an ATM applicatio...
A: Introduction: Describe how a menu-driven command processor like the one created in Chapter 9 for a...
Q: Given an 800 x 500 image, calculate the storage size, in bytes, required to store each of the follow...
A: Images file is digital formation in which we can see and watch it in screens. Every image have color...
Q: In this c++ program edit this code and please input the following details Following details Name o...
A: if you want to remove winner and percentage then we dont need this function void outputElection()
Q: Write a function nth_member(data, n) that takes a list data and an integer n as parameters and retur...
A: Answer :
Q: What are the various testing methods available and which one we can apply in projects.
A: Sоftwаre testing methоdоlоgies аre the vаriоus strаtegies оr аррrоасhes used tо test аn ...
Q: For each of the following languages, if it is regular, verify the pumping lemma; if not, prove it’s ...
A: L = wwR: w a, b*; L = wwR: w a, b*; L = wwR: w a, b*; L = L is the set of all strings where first ha...
Q: What is the definition of a heterogeneous distributed databa
A: Introduction: A distributed database system is one that spans several computers or sites rather than...
Q: What is the format of a memory address as seen by the cache, i.e., what are the sizes of the tag and...
A: The main memory address is split into sections called fields. Each field has its own significant mea...
Q: Find a valid conclusion for the following Lewis Carrol puzzles. (HINT: Express the given statements ...
A: As per company guidelines we are suppose to answer only 1 question. Kindly re-post other questions ...
Q: ost machines can replicate data in both directions, from and to another register. The Memory Address...
A: Memory address register : This is one of the main CPU registers. The main purpose of this register ...
Q: user to enter multiple lines of input by pressing the enter key at the end of each line. The program...
A: given - Write a program that reads in a sequence of characters entered by the user and terminated by...
Q: Q4) By using Graphical Method to determine the optimal value of X1 & X2 that maximize value of Z. Ma...
A: Your Solution is given below in detail. Given, Max (Z) = X1 + 2X2 Subject to; 2X1 + 5X2 ...
Q: Below is C code that runs successfully but now i want to rewrite this C code and convert it to MIPS ...
A: the answer is an given below :
Q: Explain how a stateless firewall would block all incoming and outgoing HTTP requests.
A: Introduction: Stateless firewalls are designed to protect networks using static information like sou...
Q: What are design patterns' roles in software engineering, and how can they be utilized effectively? G...
A: Introduction: A design pattern is a reusable, generic solution to a common problem in software devel...
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- PYTHON write a program that assigns the principal amount of P10000 to variable P, assign to n the value 12, and assign to r the interest rate of 8%. then have the program prompt the user for the number of years t that the money will be compounded for. calculate and print the final amount after t years. use the formula below.Using Python Write a program that displays all numbers from 1 to y that are divisible by x, where x and y are entered by the user:Example:if x = 3 and y = 30, the output is 3, 6, 9, 12, 15, 18, 21, 24, 27, 30In Python Write a program that calculates the average word length in a sentence entered by a user Thankyou
- Using Python Write a program that displays all numbers divisible by 3 in the range 1 – 100In Python Write a program that allows the user to type in a phrase and then outputs the acronym for that phrase. Note: The acronym should be all uppercase, even if the words in the phrase are not capitalized.Python Programming A positive whole number n>2 is prime if no number between 2 and sqrt(n)(inclusive) evenly divides n. Write a program that accepts a values of n as input and determines if the value is prime. If n is not prime, your program should quit as soon as it finds a value that evenly divides n.
- In Python. Write a program to check whether the number is prime number or not. Plz add comments.PYTHON Write a program which prompts the user for a distance in Kilometers, the program should convert the distance to miles and print the converted distance.\n, "\n", "The expession to convert from Km to miles is:\n", "$$ miles = km*0.621371 $$"Python Programming The Fibonacci sequence starts 1, 1, 2, 3, 5, 8, . ... Each number in the sequence (after the first two) is the sum of the previous two. Write a program that computes and outputs the nth Fibonacci number, where n is a value entered by the user.
- In Python write a program to read two integers num1 and num2 from user and print the value of num1*num2 + num1 - num2 + num1/num2In a program, write the program's algorithm that calculates the sum of odd integers (T1) from 1 to N, the sum of even integers(T2), and the sum of integers increasing by 5 (T3) and prints these values (T1, T2, T3) on the screen.PYTHON PROGRAMMING !)Write a program to display all the numbers which are divisible by 13 but not by 3 between 100 and 500.(exclude both numbers) b) Write a program to print the following series till n terms.2 , 22 , 222 , 2222 _ _ _ _ _ n terms c) Write a program to find the sum of the following series(accept values of x and n from user): 1 + x/1! + x^2/2! + ……….x^n/n!

