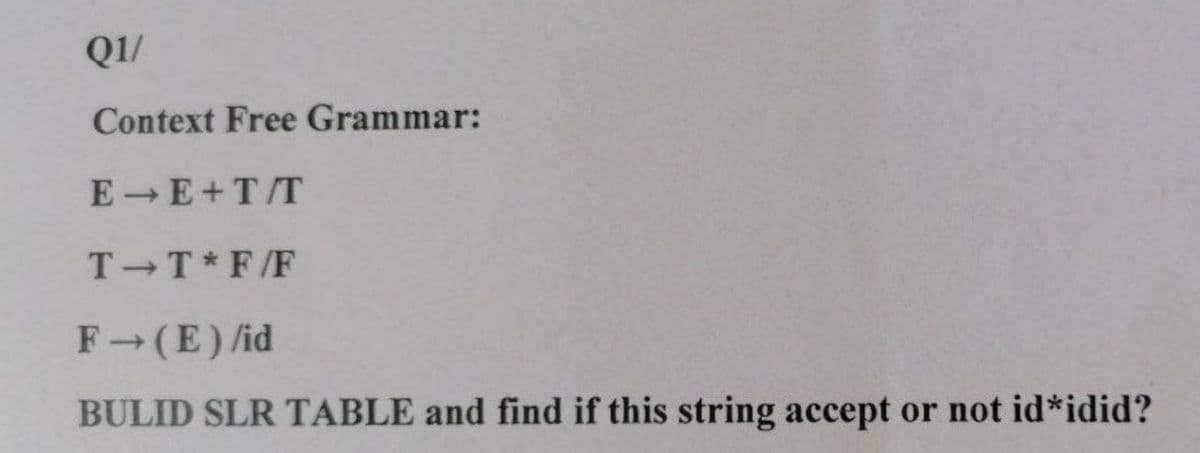
01/ Context Free Grammar: E→E+T/T T-T*F/F F→ (E) /id BULID SLR TABLE and find if this string accept or not id*idid?
Q: . pet_shopping_list For the purposes of this question, if you have a pet of a certain type, that…
A: PYTHON CODE: def pet_shopping_list(pet):if pet == 'mice':pet_list = ['mouse food', 'mouse treats',…
Q: Give some examples of the many various kinds of personality qualities and explain how you would…
A: The organisation recommends the following personality traits for employees: Every employee must…
Q: Discuss the need of backups and how to perform preventative maintenance to avoid data loss or…
A: The practice of producing and preserving copies of data that can be used to protect businesses…
Q: What exactly is the wi-fi evildirect assault technique, and how does it work?
A: The solution to the given question: EXPLANATION METHOD OF ATTACK USING Wi-Fi evil direct You can…
Q: It is the attribute of a control, much as it is the attribute of other controls, that decides…
A: Definition: Attribute Control Charts are a subset of control charts that were created with the goal…
Q: What technological innovation enabled the development of microcomputers? Why?
A: Technological breakthrough paved the way for the creation of microcomputer will be explained :
Q: It is essential to take thorough notes on the input and output configurations of the system.
A: Given: Take detailed notes on the systems' input and output settings. Configure the input and…
Q: 5. Write a program that displays the information of the input value. a) Request a single character…
A: algorithm step 1: start step 2: initialize the do-while loop : read ch check it…
Q: Define collision and discuss the linear probing approach for collision resolution.
A: Intro During hashing there may be cases when an element is already present at the hashed address…
Q: The Database Administrator or the Server Administrator is responsible for ensuring that regular…
A: Overview: As we all know, making backups is a necessary activity that must be done on a regular…
Q: In an effort to utilise structured English, please describe the methods that are not included in the…
A: Structured English: The introduction will be written in structured English, and structured English…
Q: Consider, as an example, a PictureBox control with the name myPicture that is shown in the graphical…
A: The Visible attribute of a PictureBox: A "PictureBox" is a control that may be used to show a…
Q: You could discover that using structured English is useful for you when discussing about processes…
A: Here is the solution:
Q: 3) What will be the contents of BX after the following instructions execute? mov bx, 5 stc mov ax,…
A: 8086 multiprocessor it is the microprocessor which is the enhanced version of the 8085…
Q: It is possible to save time and effort by using statements that have been written in advance. Why?
A: Here is the solution:
Q: 11) When a repeat prefix is used with STOSW, what value is added to or subtracted from the index…
A: 2 is added to the index register.
Q: It is the attribute of a control, much as it is the attribute of other controls, that decides…
A: Start: Attribute Control Charts are a subset of control charts that were created with the goal of…
Q: Q3/A- Estimate the result when you execute the following code by using Qbasic programming For m take…
A: Here is the result:
Q: A computer's central processing unit (CPU) is in charge of executing software instructions.
A: Introduction: A computer's central processing unit (CPU) is in charge of executing software…
Q: How do you keep track of the elements that have data in an array that is only half-filled?
A: Filled Array: An array is considered half-filled when there are indexes within the collection that…
Q: What exactly is the distinction between vulnerability scanning and penetration testing? What…
A: Introduction: Scanning for vulnerabilities and performing penetration tests are two separate…
Q: 23) How do you prevent a field or a method of any class from inheriting to sub classes?
A: We need to discuss how to prevent a field or a method of any class from inheriting to sub-class.
Q: Determine the phrases used to describe hackers.
A: Answer: The world's main dictionaries define "hacker" in various ways, but they all refer to the act…
Q: Do you have a working knowledge of the concepts "static" and "function"?
A: Java Programming Language Java is an object-oriented programming language that allows developers to…
Q: Students, interns, and business owners all need to have a working knowledge of operations management…
A: Start: Operations management frequently plans, controls, and supervises manufacturing and…
Q: Explain how the major components of the BI architecture interact to form a system.
A: Introduction: how the BI architecture's primary components interact to produce a system. A gadget…
Q: Let's imagine, for the sake of illustration, that a packet is now being sent from one site to…
A: Given: Processing delay and Network delay are the two components that contribute to the end-to-end…
Q: What kinds of preventative actions can you take to stop sudden spikes in the amount of electricity…
A:
Q: Describe the two most important factors influencing cloud computing efficiency.
A: Introduction:- Cloud computing is a combination of virtual servers (in the cloud) offering…
Q: "Consider the three strings given below. Write a Python program that extract the grade from each…
A: For this we need to extract all the numbers from the string using regular expression findall()…
Q: It is essential to take thorough notes on the input and output configurations of the system.
A: Answer: Input-Output ConfigurationThe figure shows an outline of the input and output gadget. The…
Q: What factors determine the speed of a microprocessor?
A: Answer: There are some main characteristics that affect the microprocessor speed : 1) clock speed.…
Q: The user experience and the user interface are two distinct aspects that must always be considered…
A: Answer: The look of a website is the responsibility of a user interface designer. All facets of a…
Q: What does it mean to have security in the cloud, and why is it important? How can the security of…
A: Given: Cloud security is essential for every organisation and individual user. Everyone desires to…
Q: Q4: Switching Techniques can be Classification in many types, list these types?
A: What Is Switching? The activity of directing a signal or data element toward a specific hardware…
Q: Demonstrate how machine learning and deep learning models vary in terms of data and computational…
A: Models ML and DLAI systems that can self-learn based on an algorithm are referred to as machine…
Q: Give some examples of the many various kinds of personality qualities and explain how you would…
A: The following is a list of some of the personality traits that an employee of the organisation is…
Q: Consider a file currently consisting of 100 blocks. Assume that the file control block (and the…
A: From the given data, Contiguous: file is usually accessed sequentially, if the file is smallLinked:…
Q: What are the security techniques/mechanisms that could be utilised to protect vehicular…
A: Introduction : With the capacity to sync with mobile phones, vehicular communication is developing…
Q: Is starving still feasible if deadlock-avoidance strategies prevent deadlock? Explain your response.
A: Intro When the set of transactions in a system is such that each transaction is waiting for another…
Q: Describe the different components of an information system. What role does the individual play in…
A: Intro These components interact to create information systems. Also, an academic education of…
Q: hat are the two main distinctions between SMF and MMF fibre optics?
A: In this question, we are asked the two differences between SMF and MMF fiber optics. Fiber cables…
Q: Which function do you use when you want to show the string value that an enumerator has?
A: String value of enumerator Enumeration is employed to define a collection of constant values within…
Q: What value determines which image from the ImageList is shown in a PictureBox, and how is this value…
A: Image List: This is a control component that enables you to store the number of photos that are…
Q: What are the three different types of backups that can be used in database recovery? Explain briefly…
A: Introduction: A database is just a way of storing data.
Q: 17) A 1000BASE-SX Ethernet connection operates on a multimode fiber optic cable at a frequency of…
A: Here is the solution:
Q: 1) (Choose only one answer) Why does a method to swap two array elements work correctly when a…
A: The question has been solved in step2
Q: Describe the purpose and applications of smartphones, digital cameras, portable media players, ebook…
A: Answer of the given question: Digital cameras should take pictures, media players play music,…
Q: What are the key differences between the information technology security solutions designed for a…
A: On Premises: Businesses that install software on their own servers are solely responsible for the…
Q: How to Tell the Difference Between Data Inconsistency and Data RedundancyThis comparison contrasts…
A: Introduction: Data redundancy happens when the same piece of data appears in several places, whereas…
Step by step
Solved in 2 steps

- Create a context-free grammar that is equivalent to N.Remove € production from the following grammarProblem Statement Study the following grammars and apply Bottom-Up Parsing stack by using Shift and Reduce Actions lexp → atom | list atom → number | identifier list → ( lexp-seq ) lexp-seq → lexp-seq , lexp | lexp Input = (36,a) decl → type var-list ; type → int | float var-list → id | id , var-list | id=n | id=n , var-list Input = int id = n , id ;
- Hello, I've finished answering part A of question 2.47. For part B, I'm looking for help in converting the pushdown automaton solution from part A into a Context-Free Grammar (CFG). Could you assist me with this using the answer I provided earlier? The specifics for part A can be found in the attached photo. Thank you for your assistance!Create a context-free grammar for the regular expressions. Include in your grammar the basis elements(empty set, empty string, single alphabet symbol), the primitive operators (Union, Concatenation, andKleene-closure), and parenthesized expressions. Include in the grammar nontermimal ⟨s⟩ that mayderive any alphabet symbol.For the dictionary containing the letters a,b,c,d,e,f,g,h and the numbers 012345, write the extended Backus–Naur form (EBNF) grammar of the expression that accepts all strings starting with abc and ending with a digit
- Consider the following context free grammar in BNF form for simple English sentences: (r1) <sentence> → <article> <noun> <verb> <adverb> (r2) <article> → a (r3) <article> → an (r4) <article> → the (r5) <noun> → apple (r6) <noun> → rose (r7) <noun> → umbrella (r8) <verb> → is (r9) <verb> → appears (r10) <adverb> → here (r11) <adverb> → there Give the derivation of the sentence “the apple is there” by using one or more of the above rules.Remove lambda rules from the following grammar. Your answer must include the NULL set.S → aS | bS | BB→ bb | C | λ C →cC | λRewrite the following EBNF grammar in BNF. <decl> → <ident_list> : (int | float | char); <ident_list> → <identifier>{,<identifier}.





