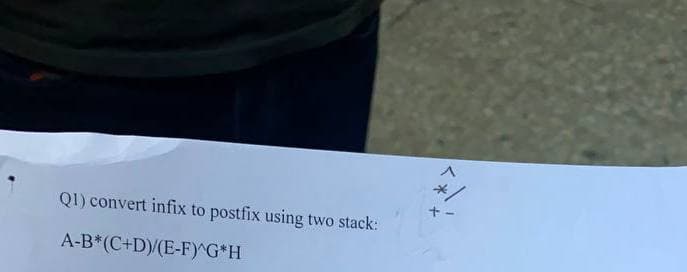
Q1) convert infix to postfix using two stack: A-B*(C+D)/(E-F)^G*H
Q: Investigate people's reactions to the computer and mobile application problems they've experienced…
A: Computer and Mobile application problems: People react unfavorably to software flaws that have not…
Q: To begin with, why is it necessary to divide the data into training and validation sets? What is the…
A: In general the Data set refers to the collections of the data which are related, which are discrete…
Q: When is it appropriate to use traditional files for data storage?
A: Introduction: The term "conventional file organisation" refers to the practise of storing…
Q: What are some concrete instances that you might use to teach the concepts of data manipulation,…
A: We must define data manipulation, forgeries, and online jacking with examples. Manipulation of Data:…
Q: 10. Inverted Number-Triangle by Julian Semblante Write a C program that will ask for a positive…
A: Answer: C Source Code: #include <stdio.h> int main() { for (int i = 5; i >= 1; i--) {…
Q: Give an efficient sorting algorithm for an array C[1,...,n] whose elements are taken from the set…
A: Find the required algorithm given as below :
Q: 10. What is the output of the following statement? int x=3; cout<<(++x* 2) <<"\"; cout<<(x--);
A: I will show output of this program.
Q: Discuss all the controls you will put in place to ensure that the system fully safeguards the…
A: The security of a computer system is mostly governed by three basic definitions or important steps,…
Q: Many different models are utilised in the construction of software, and the importance of each model…
A: Given: Software development includes thinking, defining, creating, programming, documenting,…
Q: * : Router device is work in WAN LAN All of above MAN connectivity Part time Full time Full time and…
A: It is defined as a device that connects two or more packet-switched networks or sub networks. It…
Q: What steps should you take if you accidentally remove a file from your computer?
A: If you accidentally remove a file from your computer then follow the below mentioned method:
Q: What exactly is the subinterface? Is there only one point of origin for interfaces?
A: Answer to the given question: A subinterface is a virtual connection point made by separating one…
Q: Design a relational database system using appropriate design tools and techniques, containing at…
A: Please find the detailed answer in the following steps.
Q: List and explain the challenges that may develop as a consequence of big data's vast volumes of…
A: Data mining for fresh insights is critical to company success, but the test should not be…
Q: The following is a list of the several ways files may be accessed. I am curious about the positives…
A: The following list outlines the benefits that come with viewing specified files both as a visitor…
Q: Write macro definitions with arguments for calculation of area and perimeter of a triangle, a square…
A:
Q: A website sells three products whose retail prices are: Product 1: $2.98 - Product 2: $4.50 -…
A: ExplainationHere is the way to deal with address the program 1 Create the cluster to store all the…
Q: What are the first 24 bits of a hardware address used for? IP (internet protocol) address Vendor…
A: Answer to the given question: The first 24 bits of a hardware address is used for Vendor…
Q: Privacy is affected by two to three (2-3) technological tools. Next, explain how the tools you've…
A: Technological tools: A device, whether electrical, digital, or physical, that enhances the human…
Q: Examine the differences between groups and roles in the context of the computer security access…
A: A collection of the users who have a common identity and are granted the same rights and…
Q: Do you have any suggestions for the topologies of network systems?
A: Network Topology A network topology is the physical and consistent plan of nodes and associations in…
Q: Talk about the possibilities for firms to increase or adjust their database use in this article.…
A: The following are the opportunities for the organization to increase or modify its use of the…
Q: What are the primary drawbacks associated with files that have been fragmented
A: Fragmentation is caused when data is erased from a hard drive and little holes are abandoned to be…
Q: In the context of the fields of business and information technology, please provide two instances of…
A: Given: Data may be anything, or, to put it another way, it can be facts and numbers. They're merely…
Q: Direct memory access functions
A: Direct memory access : In Direct Memory access CPU is idle and peripheral devices manages the…
Q: What exactly are sequence access files, and how exactly do they perform their functions
A: Please find the answer below :
Q: What should you do if you realise that you deleted a file by mistake but still need it?
A: What should you do if you delete a file by mistake and want it back: If you accidentally remove data…
Q: 3. A soccer team will play 3 games. Win (W = 1) can gain 2 points; Draw (D = 1) can gain 1 point;…
A: The team will play 3 games, in which the following notations will be used. Win (W=1) can gain 2…
Q: What exactly is it that the DEA.lng file is used for?
A: Introduction: LNG documents are generally utilised by language programmers and projects, although…
Q: Describe the financial implications of having a fully linked network.
A: Given: There is a correlation between cost and a completely connected network due to the fact that…
Q: What is the significance of software development? Would it be advantageous, in your opinion, if the…
A: Introduction: In this section, we must explain why software development is vital, as well as if the…
Q: In order to show the five applications for system design and modeling that are used most often,…
A: System Design encompasses a wide variety of design, modeling, and simulation services. These…
Q: Many different models are utilised in the construction of software, and the importance of each model…
A: Software development includes thinking, defining, creating, programming, documenting, testing, and…
Q: You have been asked to create a subnet that supports 16 hosts. What subnet mask ?should you use…
A: 1. Answer: 255.255.255.240 Maximum number of Hosts supported = 16. So, the Least Significant subnet…
Q: On empty AVL Tree: Insert these values: 6, 27, 19, 11, 36, 14, 81, 63, 75 and then Delete the…
A: Note: You won't mention programming language so I will write code in cpp. #include <iostream>…
Q: What exactly does "privacy" mean in the context of information security? Is there a correlation…
A: Here's the solution: Given:- Privacy is often defined as the ability to protect sensitive personal…
Q: Describe your solution to deploying the Mobile IP solution at ten machines on the current IPv4…
A:
Q: Which method is best for transferring data from a sequential-access device to a direct-access…
A: Sequential access: Sequential access is the simplest fundamental access technique. The data is…
Q: According to this particular standard form, none of the non-key attributes may be operationally…
A: Given: If Relation R is already in the first normal form (1NF), then it has already reached the…
Q: The element being searched for is not in an array of 100 elements. What is the maximum number of…
A: Let take and example of 5 element : 1 7 3 6 4 and search for 8 we have to compare with all five and…
Q: how did you run the file ?
A: Please upvote. I am providing you the correct answer below. Please please please.
Q: Because it illustrates the logical movement of data, a logical data flow diagram differs from a…
A: Here i discuss the difference between logical and physical data flow diagram: 1.Logical data flow…
Q: Structure data-entry fields in accordance with the following rules: Can you conceive of any…
A: Given: There aren't many rules regarding how to set up data input forms. Some queries, such as the…
Q: What are the benefits of a binary search tree over other data structures, such as a linked list or…
A: The whole solution is as follows: - Consider the following operations: You can get to any element.…
Q: What role does logic play in the process of creating software for computers? What types of…
A: Answer:
Q: Examine the ways in which users of desktop computers and mobile devices react to problems with…
A: Given: Desktop computers are often portrait-oriented, allowing for a wide expanse of information to…
Q: What is the status of the auxiliary carry flag after executing the instruction ADD AX, BX? (write 1…
A: ADD AX,BX will add values in AX,BX. If Carry is their then Auxiliary Carry Flag (It is one of the…
Q: The CCR model is always achievable in nature, not equal to the aggregate. prove it
A:
Q: CCR model
A: solution in below step
Step by step
Solved in 3 steps with 1 images

- Convert the following infix expression to postfix using a stack. (a * b / c) + (b2 + c3 – a) – (a + b) * (b + c)Convert the following expression from infix to postfix and show the contents of Stack and the output expression at each step ((A-((B+C)*D/E))/(F*G+H))Convert the following from postfix to infix using stacks: a b c - + d e - f g - h + / *
- Convert the following infix expression to prefix expression using stack Infix: (A+ B * C) (M * N - G) + (X/Y * N)1. convert the following from postfix to prefix using stacks: a b c + - d * 2. convert the following from infix to prefix using stacks: (5 - y) * (x + 3)Write a C++ code, which uses a Stack to convert the base-ten representation of a positiveinteger to base-two
- Given the following infix notation:(A + B) * (C / (D – E)) + F ^ G If your ID is 2401987180 (EVEN), convert the Infix notation above to Prefix notation using Stack. Apply data structures using C1) Convert the infix expereesion (a+b)*c+d into postfix expression. 2)Evaluate the postfix expression 5,6,2,+4,/,- using stackGiven the following notations.If your ID is even, evaluate the given Postfix notation using Stack:37+5/23^13+-+Apply data structures using C
- Look at this stack frame: Fill in the data types for the following procedure: SomeSub PROC, LOCAL val1: , LOCAL val2: , LOCAL val3: , LOCAL val4:Define a Stack data structure using Struct and Linked List (pointer) in C/C++. Your program should have the following menu in a switch-case loop: Is the stack empty or full? Inserting data to the Stack (push) Receiving data from the stack (printing to the screen and deleting it from the stack, that is, pop() ) Show all data in Stack from first to last ExitDo not copy from chegg and do it in c++ Write a program to convert an infix expression to a postfix expression. Input: an infix expression Output: the corresponding postfix expression Note: You must use the stack to implement this task. And you can use any one of the above stack implementations. Test your program using the following expressions: (a + b) * c (a - b) / (c +d) (a*b+c/d)/e

