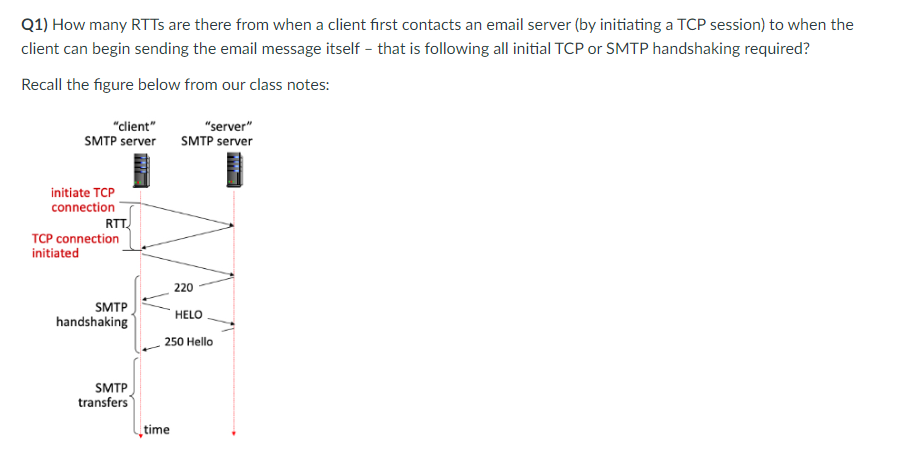
Q1) How many RTTS are there from when a client first contacts an email server (by initiating a TCP session) to when the client can begin sending the email message itself - that is following all initial TCP or SMTP handshaking required? Recall the figure below from our class notes: "client" SMTP server initiate TCP connection RTT TCP connection initiated SMTP handshaking SMTP transfers "server" SMTP server 220 HELO 250 Hello time
Q: Explain the concept of a distributed database architecture.
A: A distributed database architecture is a design approach in database management where data is…
Q: Discuss the importance of ergonomic design in computer mice and how it can contribute to user…
A: In this question we have to understand the importance of ergonomic design in computer mice and how…
Q: Describe the benefits and drawbacks of a distributed database architecture.
A: First we are going to learn about distributed databases in detail and then we will go through the…
Q: Context Free Grammar State whether it is ambiguous or unambiguous. If it is ambiguous give an…
A: The grammar provided is ambiguous. This ambiguity arises due to the lack of precedence and…
Q: Explain the purpose of CSS in web development and provide an example of its usage.
A: CSS, which stands for Cascading Style Sheets, is a fundamental technology in web development used to…
Q: Write a program in Java using ArrayList to remove duplicates in the array {0,1,4,5,8,0,9,4}.
A: Initialize Input ArrayDefine the input array inputArray containing elements with duplicates.Create…
Q: Discuss the evolution of mouse interfaces in virtual reality and augmented reality environments.
A: Virtual Reality (VR) and Augmented Reality (AR) are immersive technologies that utilize digital…
Q: Explain the concept of serverless computing in web development. How does it work, and what are the…
A: The answer will focus on understanding what serverless computing is, how it works, and the benefits…
Q: ole of Web APIs in enabling data exchange between web applications and external services
A: in the following section we will learn about the role of Web APIs in enabling data exchange between…
Q: What is database virtualization, and how does it impact database architectures in modern data…
A: Database virtualization is a technology that abstracts and separates the logical view of a database…
Q: Explain the concept of state management in web applications and discuss different techniques used…
A: State management in web applications refers to the process of maintaining and controlling the state…
Q: Discuss the importance of responsive web design and its impact on user experience across different…
A: Responsive web design is a crucial approach to web development that focuses on ensuring websites…
Q: Question g .There are different dimensions of a model. Which dimension do you find most important…
A: In the realm of modeling, there are various dimensions that contribute to the effectiveness and…
Q: What are web sockets, and how do they differ from traditional HTTP communication? Provide examples…
A: WebSockets: WebSockets are a technology or protocol used for communication between a web browser…
Q: Explain the concept of serverless computing in the context of web development. How does it differ…
A: In this question we have to understand the concept of serverless computing in the context of web…
Q: Define cookies and sessions in the context of web applications, and outline the key differences…
A: Cookies and sessions are crucial tools for managing user data across multiple interactions in the…
Q: Explain the concept of gesture-based mouse control and its applications in modern computing,…
A: Gesture based mouse control is a technology that allows users to interact with computers and digital…
Q: D
A: Web accessibility is a fundamental aspect of modern web design that aims to ensure that digital…
Q: Describe the architectural considerations for building a distributed database system that spans…
A: Building a distributed database system that spans multiple geographic regions is a complex endeavor…
Q: In a distributed database architecture, what are the challenges associated with maintaining data…
A: Maintaining data consistency in a distributed database system is complicated and crucial. In such a…
Q: Explain the concept of a data warehousing architecture and its role in modern data management
A: In step 2, I have provided brief answer about the question-----------------
Q: Analyze the challenges of cross-browser compatibility and the techniques used to address them in web…
A: The ability of a website or online application to work correctly and consistently across various web…
Q: The volatile main memory works in conjunction with the non-volatile memory to allow the instruction…
A: In the realm of computing, memory management is a critical aspect that governs how data is stored,…
Q: What is ACID (Atomicity, Consistency, Isolation, Durability) in the context of database…
A: ACID is an acronym that represents a set of properties that guarantee the reliability and integrity…
Q: Discuss the architectural considerations for building a multi-model database system that supports…
A: When it comes to creating a database system that can manage document-oriented data storage there are…
Q: Convert the following BNF grammar to EBNF: := while := | > | == | != := | ; := =…
A: BNF (Backus-Naur Form) and EBNF (Extended Backus-Naur Form) are notations used to formally describe…
Q: Discuss the CAP theorem and its implications for distributed database systems.
A: The CAP theorem, which was developed by computer scientist Eric Brewer in 2000 is a principle, in…
Q: Explain the concept of polyglot persistence and provide specific examples of scenarios where it…
A: Polyglot persistence is an approach, to database design where several types of database management…
Q: Explain the concept of data replication in a database cluster and its role in ensuring data…
A: Data replication in a database cluster is a fundamental concept used to enhance data availability,…
Q: JAVA Program Homework #1. Chapter 7. PC# 2. Payroll Class (page 488-489) Write a Payroll class…
A: Algorithm: Payroll Class1. Create a class called Payroll.2. Declare private fields in the Payroll…
Q: In the context of cloud computing, explain how serverless databases work and their implications for…
A: Serverless databases have appeared as a game-changing innovation, in the field of cloud…
Q: Translate the following C++ code to MIPS assembly language in Mars with
A: Writing MIPS assembly code is a common task for those who are working in computer science or related…
Q: Discuss the importance of responsive web design and its key principles.
A: Responsive web design is an aspect of web development.It involves designing and building websites in…
Q: Explain role of Business intelligence in any two of following domains: Fraud Detection, Market…
A: In this question we have to understand and explain the role of business intelligence from the given…
Q: How could you distinguish a problem with a balance from a user technique issue using the collected…
A: When examining the operation of a balance, it is crucial to identify any issues that may be present…
Q: How does responsive web design work, and why is it important for modern websites?
A: Create user interfaces and web content that organically adjust to a variety of screen sizes and…
Q: What is a columnar database, and how does it differ from a traditional row-based database?
A: A columnar database and a traditional row-based database are two distinct approaches to structuring…
Q: What is the role of HTML, CSS, and JavaScript in web development, and how do they interact?
A: Web development is the process of creating websites or web applications, and it involves several key…
Q: Discuss the importance of web accessibility and the key principles that developers should follow to…
A: Web accessibility involves designing and developing websites and web applications in a manner that…
Q: Explain the concept of data federation and its role in creating a virtual data warehouse.
A: A virtual data warehouse presents a contemporary approach to managing data. Instead of…
Q: Explain the concept of mouse acceleration and how it affects cursor movement. What are the…
A: Mouse acceleration is a feature in computer mice that affects how the cursor on the screen moves in…
Q: Explain the role of cookies and sessions in web applications. What are the security considerations…
A: Cookies and sessions are essential components in web applications that help manage user interactions…
Q: Which of the following topology arrangements is a point-to-point line configuration? A. Ring B.…
A: In this question we have to understand - Which of the following topology arrangements is a…
Q: How does 3D spatial tracking work in advanced mice, and what industries benefit from this…
A: The way we interact with computers and digital worlds has completely changed thanks to advanced mice…
Q: Describe the concepts of sharding and partitioning in database architecture. How do they improve…
A: In the realm of database architecture, sharing and partitioning are concepts, especially when…
Q: Describe the importance of web performance optimization techniques, such as lazy loading, image…
A: The speed with which a website's pages load and display in a web browser is referred to as website…
Q: What are the advantages and challenges of using WebRTC for peer-to-peer communication in web…
A: Peer-to-peer communication in online apps is made possible by WebRTC (online Real-Time…
Q: 1 public class Main { 2 4 5 6 7 8 9 10 1 2 3 4 5 16 8 } public static void main(String[] args) {…
A: There are three variables present in the program, namely, present, r, surprise.
Q: escribe the CAP theorem and its significance in distributed database architectures. Provide examples…
A: The CAP theorem, also known as Brewer’s theorem, is a concept in distributed database systems.Eric…
Q: Discuss the role of mouse acceleration and deceleration in user interface settings.
A: The concept of mouse acceleration and deceleration plays a crucial role in how we interact with…
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- A client application connects to a server and sends an operation, and gets a result back. What happens then? Is the connection open, so that the client can send more operations? Answer the question comparing the protocols SMTP, FTP, HTTP, POP and IMAP. What are the pros and cons of keeping the connection open or closing it down after each operation?1. Part A: • Develop a TCP server program in java that waits for clients to connect. • The server responds to the client with one of the following based on client’s request: *Export public key generated using KeyPairGenerator *Export Message Digest * Export Digital Signature * Send original text for the encrypted text received from client8.4 One of the non-payload options in Snort is flow. This option distinguishes between clientsand servers. This option can be used to specify a match only for packets flowing in one direction(client to server or vice-versa) and can specify a match only on established TCP connections.Consider the following Snort rule:alert tcp $EXTERNAL_NET any -> $SQL_SERVERS $ORACLE_PORTS\ (msg: “ORACLE drop tableattempt:;\ flow: to_server, established; content: “drop table_name”; nocase;\classtype: protocol-command-decode;)a. What does this rule do?b. Comment on the significance of this rule if the Snort devices is placed inside or outside of theexternal firewall.
- In Client-server paradigm, the clients need dynamic IP to communicate with each other. True FalseA client application establishes a connection to a server, transmits an action, and waits for a response. What happens then? Is the connection still accessible for other operations? Compare the protocols SMTP, FTP, HTTP, POP3, and IMAP. What are the advantages and disadvantages of maintaining or terminating the connection between operations?The Message structure and partial “server” code -using IPC mechanism message queue- seen below.a. Write needed code for creating message queueb. Write needed code for deleting message queuec. Write the corresponding partial “client” code for this partial server.Message Structure:typedef struct {long int msg_to; // Message in queue for this typelong int msg_fm; // Placed in the queue by this typechar buffer[BUFSIZ]; // The actual message}MESSAGE;Partial Server Code:1. while (1) {2. memset( msg.buffer, 0x0, BUFSIZ );3. if ((n=msgrcv(mid, &msg, BUFSIZ, SERVER, 0)) == -1 ) {4. perror("Server: msgrcv");5. return 2;6. } else if (n == 0) break;7. process_msg(msg.buffer, strlen(msg.buffer));8. msg.msg_to = msg.msg_fm;9. msg.msg_fm = SERVER;10. n += sizeof(msg.msg_fm);11. if (msgsnd(mid, &msg, n, 0) == -1 ) {12. perror("Server: msgsnd");13. return 3;14. }15. }
- q36- What a mechanism is used by TCP to provide flow control as segments travel from source to destination? Select one: A. Window size B. Acknowledgments C. Session establishment D. Sequence numbersI NEED ONLY CORRECT OPTION NO NEED TO EXPLAIN IN DEPTH,PLEASE SOLVE ALL THE QUESTION, DON'T LEAVE ANY QUESTION AND IF YOU DON'T KNOW THE CORRECT ANSWER THEN PLEASE LEAVE IT OTHERWISE I WILL DOWNVOTE IT.... 1. Which of the following statements are correct?I. The User Datagram Protocol (UDP) is used for applications that requires constantdata flow.Il.The header size in Transmission Control Protocol (TCP is small when compared tothe header size of User Datagram Protocol (UDP).I!.The Transmission Control Protocol (TCP) is byte oriented.IV. The User Datagram Protocol (UDP) is used for routing.(a) I, II, and III only(b) II, Ill, and IV only(c) I, Ill, and IV only(d) I, Il, and IV only 2. Which of the following statements are true when the block size in a fixed block size filesystem is increased?1. disk throughput is increased2. disk throughput is decreased3. disk space utilization is increased4. disk space utilization is decreased 3. What is the output of below…Find the class of the following two IP addresses (both are classful addresses),as well as their netid and hostid: a. 104.37.3.6 b. 208.34.54.12
- Assume that Computer A, which is connected through an Ethernet cable to the Switch S1, is just powered on. The user opens a browser and then types a website address to receive the website from the Server (as shown in Figure 1). Write down all the important protocols that come into play by the time the first frame containing HTTP request reaches R1. (Note: Before HTTP frame, other frames have already been sent by other protocol(s).) Write down all the protocols with reference to the TCP Model as follows? Application Layer: Transport Layer: Internet Layer: Link Layer:Tasks: Part A: Develop a UDP/IP server program in java that waits for clients to server. The server responds to the client with one of the following based on client’s request: Export secret key generated using KeyGenerator Export Text and Message Digest Export Text and Digital Signature Send original text for the encrypted text received from client Part B: Develop a UDP/IP client program that make request secret key, Message Digest, Digital Signature and original text by sending the encrypted text to server program developed (in Part A). This program will display the various objects received from server on its console.In this assignment, you will develop a simple Web server in Python that is capable of processing only one request. Specifically, your Web server will (i) Create a connection socket when contacted by a client (browser) (ii) Receive the HTTP request from this connection(iii) Parse the request to determine the specific file being requested(iv) Get the requested file from the server’s file system(v) Create an HTTP response message consisting of the requested file preceded by header lines(vi) Send the response over the TCP connection to the requesting browser. If a browser requests a file that is not present in your server, your server should return a “404 Not Found” error message. Your job is to code the steps above, run your server, and then test your server by sending requests from browsers running on different hosts. If you run your server on a host that already has a Web server running on it, then you should use a different port than port 80 for your Web server. Make sure to test your…

