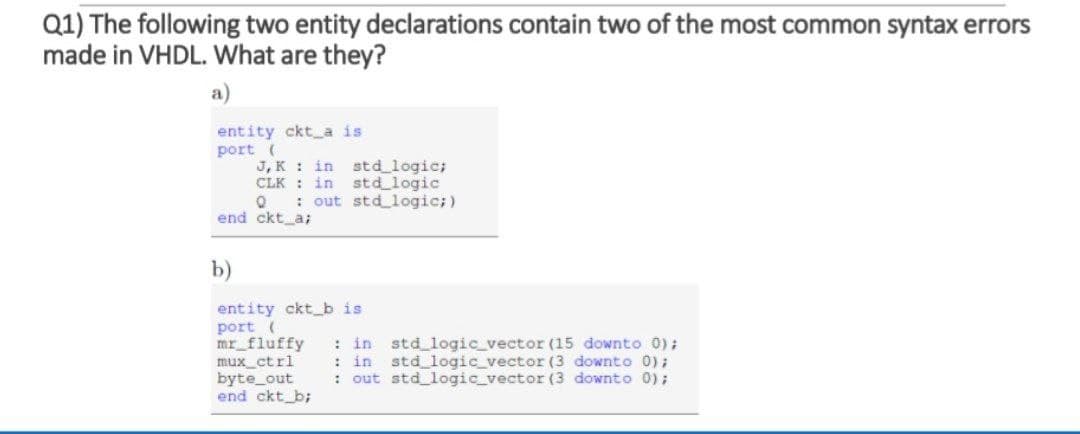
Q1) The following two entity declarations contain two of the most common syntax errors made in VHDL. What are they? a) entity ckt a is port ( J, K : in std_logic; CLK : in std logic : out std logic;) end ckt_a; b) entity ckt_b is port ( mr fluffy mux_ct rl byte_out end ckt_b; : in std logic_vector (15 downto 0); : in std logic vector (3 downto 0); : out std logic_vector (3 downto 0);
Q: Is there a way to lessen the overhead caused by page table shadowing?
A: The page table shadowing is also known as shadow page table.
Q: Do you know what daemon processes are and how crucial are they? Give examples of four.
A:
Q: lowchart of this pseudocode using online chart
A: Due to the rules given to us, I can solve only one question at a time. So, the flowchart of the…
Q: What other components can be changed to keep the same page size (and avoid rewriting the software)?…
A: Introduction: In the domains of information technology and computer science, a system is considered…
Q: Consider which stage of compilation could result in a syntax problem..
A: Compilation is the process the computer takes to convert a high-level programming language into a…
Q: Are you certain that employing wireless applications for mistake correction is more effective? You…
A: Introduction: "Yes," says the author, "the error correction is best employed with wireless…
Q: Cause Effect Material Process Material Defects Wrong Order Problem or Defect Statement No Training…
A: This is a fishbone or cause and effect diagram. It is used to root cause analysis. The main problem…
Q: In a given statement such as studname=name[5], what array operation is being implemented? Select…
A: Solution:-
Q: 1.) What is wrong in the given statement below? fmName.text = 123 Select one: a. text should be…
A: b. 123 should be “123”
Q: The creation of the RISC architectural paradigm
A: RISC Creation: The emphasis on "reduced instructions" prompted the it being known as a "reduced…
Q: What flaws in the router's layer 2 protocol have been discovered? What are the implications of this…
A: Introduction: Layer 2 Protocol IssuesThe Data Link layer is the second layer in the OSI…
Q: True or false, and please provide a short explanation for your response to the following questions:…
A: Introduction: Selective repeat protocol, commonly known as Selective Repeat ARQ (Automatic Repeat…
Q: Given the table below. What is the value of GRADE[2][4] ? 78 69 87 98 88 65 96 73 50 67 95 61 89 95…
A: 77
Q: Is it possible for you to explain the metrics that are used in the software development process? The…
A: Introduction: A software metric is the quantifiable or countable measure of programme properties.…
Q: The memory unit of a computer has 2M words of 32 bits each. The computer has an instruction format…
A: Given : Memory Unit = 2M words = 2 x 220…
Q: Given a number and a sorted binary tree, write function that inserts the number into the tree. Given…
A: The code for the above given question is given below:
Q: Consider the stochastic diflerential equation dX = VX,(1 – X;) dWt %3D where (W) is a Brownian…
A: #we initially define the upper and lower boundaries that are given as 2 and 0. #plot command will…
Q: Here, you'll learn about dynamic scoping, its use cases, the performance consequences of employing…
A: INTRODUCTION: Dynamic scoping: The term dynamic refers to something that is constantly changing.…
Q: Why do we employ MATLAB to tackle challenges in Computational Geometry?
A: Introduction: MATLAB is a high-performance computer language for engineers. It has a user-friendly…
Q: Watchdog clocks are crucial components of embedded systems.
A: Introduction: The importance of a watchdog timer in embedded systems is as follows: In the most…
Q: The use of the SSTF disc scheduling technique comes with a number of risks.
A: Solution:: SSTF disk scheduling set of computer instructions: Shortest Look (for) Time First…
Q: When it comes to computer architecture, is there a difference between it and computer organisation?…
A: The question is to write the difference between computer architecture and computer organisation.
Q: For system development, what does it take to be a successful team member? How do you ensure…
A: The solution to the given question is: Introduction Creating new software from concept to completion…
Q: Write a JAVA program for loop that will print out all the multiples of 3 from 3 to 36, that is: 3 6…
A: Algorithm Start var n=3 for i=n to 36, go to step 4 else to step 6 if(i%3==0), go to step 5 else to…
Q: A PKES system is most likely to be found in the following locations.
A: Introduction: Passive Keyless Entry and Start (PKES) systems are often found in high-end cars. This…
Q: Q1) Draw the ladder diagram for the logic circuits A&B А: A АВ в АВ + AB AB
A: The image of the circuit is of Exclusive-OR gate.
Q: It's important to know what a downgrade attack is and how to protect yourself against it.
A: Attack with a lower priority: It's a kind of computer system or communication protocol cryptography…
Q: t one: a. text b. label c. all of the choices d. size What is the correct syntax of for statement…
A: Lets see the solution.
Q: What are the most effective methods for assuring the resilience and availability of a LAN network?
A: Introduction: A local area network (LAN) is a data communication network that connects several…
Q: What considerations are made while updating a software project's Process Model?
A: Process Model is very important for software development.
Q: 2. A fibonacci sequence is a sequence such that, beginning with the third element, each term is the…
A: - We need to code for a fibonacci sequence using for loop using the initials provided. - We are…
Q: To what extent can you use SIMD with data or control-level parallelism? Is there a particular kind…
A: Introduction: In Flynn's taxonomy, single instruction, multiple data (SIMD) is a sort of parallel…
Q: one: a. textbox b. form c. label It provides a quick access to frequently used commands in…
A: Given : What object is needed to get data from the end user?Select one:a. textboxb. formc. label
Q: Create a program that declares variable to hold number of eggs of a chicken. Your program will…
A: The Scanner class is used to get user input.
Q: Mousing devices equipped with an optical sensor that detects mouse movement.
A: The optical mouse detects mouse movement with the use of an optical sensor. Optical mouse: - The…
Q: Explain how your offline decision-making process differs from your online decision-making process.…
A: Introduction: Consumer purchasing behavior is becoming increasingly important to all advertising…
Q: We're getting married Code in C language
A: The C programming language is a very efficient language that can be utilized for string…
Q: Create a program that outputs a result for a student based upon the mean grade of eight module…
A: We are using JAVA here: The complete program with output is given below.
Q: Which algorithm design technique uses selection sort? Why?
A: Find the answer given as below :
Q: Write an essay in which you compare and contrast CPU Scheduling Algorith
A: CPU scheduling can be defined as the process where the CPU keeps the one process on hold until the…
Q: Express the following queries in SQL: a) List first name, last name and department ID of all…
A: Find the required SQL queries given as below :
Q: What is the correct order for converting the source code into an executable file?
A: Source code the program code which is in high level language and this is in reader format. The…
Q: Why is it better to programme in a compiled language rather than one that is interpreted? Would you…
A: Introduction: Compilers convert compiled languages into machine code that the processor can execute.…
Q: Which algorithm design technique uses selection sort? Why?
A: Selection sort: selection sort is also called as in-place comparison sort. selection sort is known…
Q: Assume that every 18 months, the number of CPU cores available is doubled. How much extra off-chip…
A: Introduction: Each CPU core may support a maximum of two threads. In this case, a CPU with two cores…
Q: 8. Implement the following equations using a single 8x 3 ROM а. АВС + AВС b. ABC + ABC + ABC с. АВС…
A: The answer is as follows.
Q: Examine the three different kinds of IPv6 migration strategies available to you.
A: IPv6 The Internet Protocol Version 6 (IPv6) is an organization layer standard that allows data to…
Q: can you please further explain the thing you draawww
A: Internet and the web are directly related to each other. Internet means connecting network of…
Q: What distinguishes embedded computers from general-purpose computers is their lack of a hard drive.
A: Introduction: The main difference between an embedded system and a general-purpose computer system…
Q: The question is, whether kind of program-level parallelism (data or control) is best suited to SIMD.…
A: Introduction: A parallelism-based software may be coded successfully by more technically…
Step by step
Solved in 2 steps

- 1. Give the unifyiing substitition for (x,y,z are variables): f(a) f(b) 2. Give the unifyiing substitition for (x,y,z are variables): g(x,x) g(f(a),f(y)) 3. Give the unifyiing substitition for (x,y,z are variables): g(x,x) g(f(a0,f(b))(Signal Handling) Read the documentation for your compiler to determine what signals are supported by the signal-handling library (). Write a program that contains signal handlers for the standard signals SIGABRT and SIGINT. The program should test the trapping of these signals by calling function abort to generate a signal of type SIGABRT and by having the user type c ( C on OS X) to generate a signal of type SIGINT.Mark the following statements as true or false. i. An identifier can be any sequence of digits and letters. ii. In C++, there is no difference between a reserved word and a predefined identifier. iii. A C++ identifier can start with a digit. iv. The operands of the modulus operator must be integers. v. If a = 4; and b = 3; then after the statement a = b; the value of b is still 3. vi. The result of a logical expression cannot be assigned to an int variable. vii. Every if statement must have a corresponding else. viii. The expression in the if statement: if (score = 30) grade = 'A'; always evaluates to true. ix. The expression: (ch >= 'A' && ch = 'Z'. x. The expression !(x > 0) is true only if x is a negative number.
- Add a main function () to the code and organize it using mainline logic. You are also require to add variables, parameters and arguments in each function. def display_state_details(state_code,district_code): print(state_code,district_code,end="") def display_vechicle_number(vehicle_code,vehicle_number): print(vehicle_code,vehicle_number) state_code=input("Enter the state code:") district_code=int(input("Enter the district number:")) vehicle_code=input("Enter vehicle code:") vehicle_number=int(input("Enter the vehicle number:")) print("The genertaed licenses plate number is:") display_state_details(state_code,district_code) display_vehicle_number(vehicle_code,vehicle_number67. In BASIC language statement "300 LET A = 2(X+3)", syntax error is a. subtraction sign missing b. asterisk sign missing c. GO function is missing d. NET function is missingThe execution of SUB AL, BL is performed by _____. a. BIU b. both EU and BIU c. neither EU nor BIU d. EU
- (Conversion) a. Write a C++ program to convert meters to feet. The program should request the starting meter value, the number of conversions to be made, and the increment between metric values. The display should have appropriate headings and list the meters and the corresponding feet value. If the number of iterations is greater than 10, have your program substitute a default increment of 10. Use the relationship that 1 meter = 3.281 feet. b. Run the program written in Exercise 6a on a computer. Verify that your program begins at the correct starting meter value and contains the exact number of conversions specified in your input data. c. Modify the program written in Exercise 6a to request the starting meter value, the ending meter value, and the increment. Instead of the condition checking for a fixed count, the condition checks for the ending meter value. If the number of iterations is greater than 20, have your program substitute a default increment of (ending value - starting value) / 19.1. Mark the following statements as true or false. a. An identifier must start with a letter and can be any sequence of characters. (1) b. In C++, there is no difference between a reserved word and a predefined identifier. (1) c. A C++ identifier cannot start with a digit. (1) d. The collating sequence of a character is its preset number in the character data set. (2) e. Only one of the operands of the modulus operator needs to be of type int. (3) f. If ; and ;, then after the statement ; the value of b is erased. (6) g. If the input is 7 and x is a variable of type int, then the statement ; assigns the value 7 to x. (6) h. In an output statement, the newline character may be a part of the string. (10) i. In C++, all variables must be initialized when they are declared. (7) j. In a mixed expression, all the operands are converted to floating-point numbers. (4) k. Suppose . After the statement ; executes, y is 5 and x is 6. (9) i. Suppose . After the statement ; executes, the value of a is still 5 because the value of the expression is not saved in another variable. (9)Define a C++ language float literal using regular expression. A float literal in C language has an optional exponent part. If a float literal is written without exponent part, then it must have a decimal point which can appear at the start, at the end or in the middle of digits, as in following examples: 123.456 .456 456. If float literal is written with exponent, then decimal point in mantissa part is optional, and exponent is a whole number with optional sign, as in following examples: 123e78 123e+78 123e-78 123.456e78 .456e78 456.e78
- Define a C++ language float literal using regular expression. A float literal in C language has an optional exponent part. If a float literal is written without exponent part, then it must have a decimal point which can appear at the start, at the end or in the middle of digits, as in following examples: 123.456 .456 456. If float literal is written with exponent, then decimal point in mantissa part is optional, and exponent is a whole number with optional sign, as in following examples: 123e78 123e+78 123e-78 123.456e78 .456e78 456.e78 Subject : Compiler ConstructionDefine lexeme, token and pattern. Identify the lexemes that make up the tokens in the following program segment. Indicate corresponding token and pattern. void swap(int i, int j) { int t; t=j; i = j; j = t; }Add a main function () to the code and organize it using mainline logic: def display_state_details(state_code,district_code): print(state_code,district_code,end="") def display_vechicle_number(vehicle_code,vehicle_number): print(vehicle_code,vehicle_number)state_code=input("Enter the state code:")district_code=int(input("Enter the district number:"))vehicle_code=input("Enter vehicle code:")vehicle_number=int(input("Enter the vehicle number:")) print("The genertaed licenses plate number is:") display_state_details(state_code,district_code)display_vehicle_number(vehicle_code,vehicle_number)



