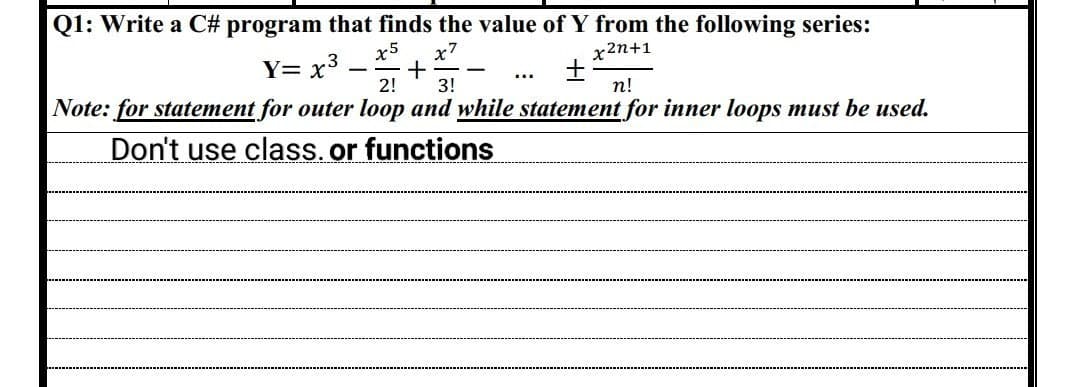
Q1: Write a C# program that finds the value of Y from the following series: x5 x7 x2n+1 Y= x³_ + ± 2! 3! n! Note: for statement for outer loop and while statement for inner loops must be used. Don't use class. or functions -
Q: Describe the voting process used by the Hough Transform feature extraction technique to locate…
A: Edge detectors, which collect pixels from an idea that sit on a preset curve in the picture space,…
Q: Describe the construction of botnets and the DDoS assaults that use them.
A:
Q: What does it mean exactly when someone refers to an assembly language in this way?
A: Computers and other programmable devices can be programmed in a more high-level language than…
Q: a) Assuming a 1 KB page size, what are the page numbers and offsets for the following logical…
A: a. assume 1KB page size where page number and page size find out 21112 5500050 b. consider page…
Q: distinguishes a wired internet connection from a wireless one
A: What precisely distinguishes a wired internet connection from a wireless one?
Q: What are the prevailing computer science network trends today?
A: The question has been answered in step2
Q: Q3: What the output of the following program: static void Main(string[] args) { int i =3 m = 20, n =…
A:
Q: Describe the operation of Google Dorks and its original purpose.
A: Google Docs is a free Web application for creating, editing, and storing documents and spreadsheets…
Q: What does network architecture communications? mean in the context of
A: Definition: TNA is an acronym for telecom network architecture. Telecommunication network…
Q: Convert the following signed decimal numbers into binary numbers: a. +11 b. -28 c. +0601 d. -0106
A: Decimal Number:- A decimal is a number that consists of a whole and a fractional part. Decimal…
Q: iopic Is there any way that staring at the OS and TCPPP odel encourages troubleshooting? Despite the…
A: The TCP/IP and PSI models need to be discussed and compared: Understanding the protocols at work and…
Q: Is there a better way to defend against DDOS attacks?
A: The question has been answered in step2
Q: What connections are there between C++, Java, and Assembly Language?
A: C++, Java, Assembly: It signifies that java only supports a limited number of pointers. Only the…
Q: Please write a c++ programming code that can work on codechum according to the instructions below.…
A: Algorithm: Input the rate of consumption from the user Calculate the total cost as follows. If the…
Q: List six techniques for getting in. Any wireless access should be classified as either residential,…
A: Get Online and Use Some Cool Stuff: Dial-up modems through telephone lines, hybrid fibre coaxial…
Q: It is necessary to describe how botnets are generated and how they are used in DDoS attacks.
A: The answer of this question is as follows:
Q: Is it necessary to compare the data rates of Standard Ethernet, Fast Ethernet, Gigabit Ethernet, and…
A: Yes, it is necessary to compare the data rates of Standard Ethernet, Fast Ethernet, Gigabit…
Q: Below is a detailed explanation of the connection between assembly language and machine language.
A: The answer is given in the below step
Q: How may a fork() system call be rectified if anything goes wrong?
A: Answer: We need to write the when fork system call be rectified if anything goes wrong. so we will…
Q: Which kind of routing path—static or dynamic—would you employ for a simple network? What makes you…
A: In the given question Static routes are configured in advance of any network communication. Dynamic…
Q: Why is assembly language so seldom utilized in the development of big applications?
A: The answer is given in the below step.
Q: c. By how much is the execution time of the program improved if the CPI of INT and FP instructions…
A: The answer is
Q: Why is it required for the network layer protocol to provide the transport layer with packetizing…
A: The answer to the question is given below:
Q: In what ways do networks get used in schools?
A: networks get used in schools: What kinds of networks are employed in educational institutions? is…
Q: It is commonly known that cybercriminals spread malware using social media.
A: Malware in document: Sending malware through email is a common tactic used by cybercriminals. This…
Q: I/O interfaces have a role, but what does it mean specifically?
A: The answer of this question is as follows:
Q: Let's start by defining an Internet Protocol (IP) address. What use do mnemonic addresses serve? Is…
A: Internet Protocol IP: Its routing capability makes a internetworking possible and, in essence,…
Q: What kind of storage device is ideal for users' data backups? Cost, speed, and capacity…
A: Every organization needs data backup to carry out its vital business operations and to continue…
Q: Explain distributed denial of service (DDoS) attacks in detail. Denial of Service (DOS) attacks are…
A: Given To know about the distributed denial of service(DDoS) attack.
Q: Is using a peer-to-peer network advantageous or disadvantageous?
A: Peer-to-peer network A P2P network is a gathering of PCs, every one of which goes about as a hub for…
Q: We'll go over how to create a botnet and use it in a DDoS attack in this article.
A: Definition: A botnet is a collection of computers that have been infected with malware and are under…
Q: What precisely is assembly language and how does it function in practice
A: Assembly Language: It is one type of programming language that is used as lower level programming…
Q: How many digits does the hexadecimal system
A: Hexadecimal system : It is a type of number system that has a base value equal to 16 . The symbols…
Q: What does "Ethernet" mean in terms of networking?
A: The standard method for establishing connections between devices in a wired LAN or WAN is Ethernet…
Q: Is it feasible to classify various computer networks according to their size?
A: Definition: We must make a distinction between several sorts of computer networks in accordance with…
Q: Identify the most important considerations for classes and constructors.
A: Introduction Class and Constructor: When a class is created using the NEW function, a particular…
Q: You may compare the complex features, benefits and drawbacks, price, usability, and other features…
A: Pfsense Opnsense Untangle Pfsense is a firewall that runs on BSD and supports both Windows and…
Q: Using examples, describe how traditional personnel practices are combined with controls and…
A: Information Protection: It is characterised as method to protect data from unauthorized access.…
Q: differentiate demand modelling and machine learning?
A: Machine learning is a branch of artificial intelligence and computer science which focuses on the…
Q: operating system a) Assuming a 1 KB page size, what are the page numbers and offsets for the…
A: We need to find answers to questions related to paging in operating systems.
Q: Which of the several network topologies appeals to you the best, please?
A: There are primarily six different types of physical topology in computer networks. These are: A bus…
Q: Here is a list of the five different kinds of DoS assaults.
A: A Denial of Service (DoS) attack is an attack meant to shut down a machine or network making it…
Q: Binary numbers are often used in computer programming.
A: Number System: Computer systems encode all data as a series of ones and zeros. Computer number…
Q: What are three creative and exciting applications of the internet of things come to mind?
A: Given: We have to discuss What are three creative and exciting applications of the internet of…
Q: Data communication is the transmission and reception of information between two sites using…
A: Two or more individuals connect and share ideas, thoughts, files, documents, etc., using electronic…
Q: Construct a truth tables for the following, g(a,b,c) = Σm(1,4,5)
A: a b c Minterms 0 0 0 (a'b'c') m0 0 0 1I (a'b'c) m1 0 1 0 (a'bc') m2 0 1 1 (a'bc) m3 1…
Q: What are the four steps in the development of a network?
A: Development of Network: Your developmental network is a select group of people who support you…
Q: Which of the several network topologies appeals to you the best, please?
A: Introduction: Network topology is essentially the physical or logical arrangement of how the nodes…
Q: Explain distributed denial of service (DDoS) attacks in detail.
A: We need to discuss DDoS attacks.
Q: Create a Turing machine that computes the function f(x) = 2x + 3, where x is a positive integer…
A: Process Change left most 1 to blank and write two a's at the end of the string on the tape Repeat…
Step by step
Solved in 4 steps with 2 images

- (Data processing) Years that are evenly divisible by 400 or are evenly divisible by 4 but not by 100 are leap years. For example, because 1600 is evenly divisible by 400, 1600 was a leap year. Similarly, because 1988 is evenly divisible by 4 but not by 100, it was also a leap year. Using this information, write a C++ program that accepts the year as user input, determines whether the year is a leap year, and displays a message telling the user whether the entered year is or is not a leap year.Numerical analysis) Given a number, n, and an approximation for its square root, a closer approximation of the actual square root can be found by using this formula: newapproximation=(n/previousapproximation)+previousapproximation2 Using this information, write a C++ program that prompts the user for a number and an initial guess at its square root. Using this input data, your program should calculate an approximation of the square root that’s accurate to 0.00001. (Hint: Stop the loop when the difference between the two approximations is less than 0.00001.)(cin within a loop) Write and run a C++ program that accepts 10 values of gallons, one at a time, and converts each value entered to its liter equivalent before the next value is requested. Use a for loop in your program. Use the fact that 1gallon=3.785liters.
- please code this for me in c++ using for loops, while loops, if and else statements, do while, switch statements (using only: include <iostream>) please don't use advanced or complicated code.C++ Programming Exercise: A real estate office handles, say, 50 apartment units. When the rent is, say, $600 per month, all the units are occupied. However, for each, say, $40 increase in rent, one unit becomes vacant. Moreover, each occupied unit requires an average of $27 per month for maintenance. How many units should be rented to maximize the profit? Write a program that prompts the user to enter: a. The total number of of units. b. The rent to occupy all the units. c. The increase in rent that results in a vacant unit. d. Amount to maintain a rented unit. The program then outputs the number of units to be rented to maximize the profit.(Pass or fail) Write a c++ program that prompts a student to enter a score.If the score is greater or equal to 60, display “you pass the exam”; otherwise, display “you don’t pass the exam”.Your program ends with input -1.Here is a sample run:Enter your score: 80You pass the exam.Enter your score: 59You don’t pass the exam.Enter your score: -1No numbers are entered except 0
- Question 14 Pap Write a program using loops in C, that takes an integer input from the user, and prints out next five integers. (Note: Submit the code as handwritten) For example: User Input: 2 Program Output: 3 4 5 6 7 Q.2: Write a program using loopThe Area, A, of a trapezoid is given by the formula A. Use this information to write a complete C++ program that asks the user to enter 10 values of trapezoid’s height1, trapezoid’s height2 and trapezoid’s base measurements, one at a time, and then the program calculates for each value entered the Area, A, of a trapezoid Using a for loop.1. Write a c program that accepts a string from the user and outputs the length ( do not use any buit-in functions ) (Hint you may use while loop – while the character read is not equal to ‘\0’ increment the count. ) 2. Using the code above. Add additional codes that will copy the characters in reverse order (Note: Write comments that explain what each main section of the code is accomplishing and how)
- For C programming!! Thank u so much! Write a program that will uses a loop to display a table of the Celsius temperatures 0-20, and the Fahrenheit equivalents. To convert temperatures from Celsius to Fahrenheit, you need to use the following formula: Fahrenheit = Celsuis + 32.This is C programming. Please fill in the blank. Code is to copy string and print backward. /* Requirement: We’ll initialize a string (I’ll use “Hello World”). Then, create a second string and copy the first string over, but backwards, using a loop. Print both strings. For example: string 1 is “Hello World”, string 2 would be “dlroW olleH”. */ /*Copy Strings Backward Input String1: Hello World*/ #include<stdio.h> #define str_len __1__ //str_len = hello + space + world + null char LEN __2__ print_string(__3__ str[__4__]); __5__ copy_string(__6__ s1[__7__], __8__ s2[__9__]); int main() { __10__ str1[]= "Hello World"; __11__ str2[__12__]; //loop and copy each character over // until the array reaches null character copy_string(__13__, __14__); //printing back by calling function print_string printf("String1: "); print_string(__15__); printf("\nString2: "); print_string(__16__); } /* Copy one string to another by looping backward. Need 2 index variables to keep track of each…(Guess the Number) Write a C program that plays the game of “guess the number” as follows: Your program chooses the number to be guessed by selecting an integer at random in the range1 to 1000. The program then types:I have a number between 1 and 1000.Can you guess my number?Please type your first guess.

