Q1: write a shell script which can read "N" number of command line arguments and it should print the sum of those arguments. 10 20 30 e.g. ./myscript.sh Output: 60
Q: What is Debugging utilized for when it comes to programming?
A: Introduction: It's termed debugging when a programme or piece of software is debugged to find and…
Q: How may block and stream ciphers exchange keys, and why should they be different?
A: Symmetric cryptography ciphers contains 2 main categories: block ciphers and stream ciphers.Block…
Q: Q5. The output of the following code is 'tiangong@tiangong.edu.cn'. import re pattern = '[a-zlt ?…
A: Here is the answer below:-
Q: Which encryption standard guarantees that data is not modified between transmission and reception?
A: In the emerging information society, cryptography ensures the permission, authentication, integrity,…
Q: What drawbacks does symmetric key management present?
A: The above question is solved in step 2 :-
Q: Can you share a case study of debugging
A: Introduction: Define and explain Debugging Debugging is a systematic procedure for finding and…
Q: There are five major sub-categories of internal control (a). Consider one aspect of internal control…
A: One of the most crucial components in any corporation is internal controls. Organizations implement…
Q: Education. In underdeveloped nations, IT provides highly advantageous educational chances for the…
A: Education: There is a big gap in learning and schooling in poor countries. Approximately 53% of all…
Q: What does poison packet attack actually entail? Please provide two instances of this kind of…
A: Please find the answer below :
Q: What's the difference between logical and physical data flow diagrams?
A: The business events that take place and the related data are listed in the logical DD. The actual…
Q: please solve with computer no with handwrite What are the major drawbacks of flooding and how…
A: Here in this question we have asked that what are drawback of flooding and how gossiping is…
Q: Lexical analyzers may be constructed in a number of ways. Explain why you believe this to be the…
A: A lexical analyzer's principal role is to separate tokens from the input programme and validate its…
Q: Explain why interrupts are not appropriate for implementing synchronization primitives in…
A:
Q: What benefits does the deep web provide companies that depend on information systems?
A: Launch: Business uses management information systems, also known as information management systems,…
Q: Discuss why documenting user requirements is essential for systems analysts.
A: User requirements:- also known as user needs, outline what the user…
Q: Mention any five characteristics of the human eye that enable it to capture images in the real…
A: Institution: The Human Eye really has five components that work together to acquire pictures in the…
Q: OSCAR OSCAR ID ACTOR_ID LAST_NAME MOVIE ID TITLE MOVIE MOVIE ID → TITLE NUMBER OF WINS NUMBER OF…
A: Following is the ER Diagram We have 4 entities 1. Oscar 2. director 3. Actor 4. movie
Q: Web servers use a range of technologies to generate personalized web pages that cater to the demands…
A: The web servers use the following technologies, in that order, to respond to client requests: It is…
Q: Question 14 Write pseudocode OR Python code that contains a While loop that asks the user to enter a…
A:
Q: Because microprocessor CPUs do not understand mnemonics as they are, they have to be converted to…
A: Introduction: The fundamental language of computers is machine code, which is also referred to as…
Q: Is this the case? The sequence of item addition influences the overall balance of a binary search…
A: Balanced Binary: According to the author of Form in Tonal Music, Douglass Green, a balanced binary…
Q: consider the problem of finding a minimum Pareto optimal matching. Let MIN-POM denote the problem…
A: considering the problem of finding a minimum Pareto optimal matching and proving that MIN-POM is…
Q: Comparing cypher block chaining to cypher feedback mode in terms of the number of encryption…
A: The DES (Date Encryption Standard) cypher block chaining mode is as follows: It is a sort of cypher…
Q: Wireless networks, for instance, are crucial in developing countries today. In many applications,…
A: LAN(Local Area Network) A local area network (LAN) is a network of computers that are located in a…
Q: What use does "debugging" serve?
A: The process of locating and resolving problems is called debugging. problems in software code that…
Q: of Ethics in brief d
A: Solution - In the given question, we have to describe the ACM Code of Ethics in detail.
Q: hich is the correct binary search tree constructed with the following numbers: 8 15 10 7 5 5 7 7 7 8…
A: Here in this question we have given some keys and we have asked which is correct Binary search tree…
Q: What is the size of the final message (in bytes) transferred by the lower layer?
A: The answer is
Q: In C # Assume a file named Student.txt contains a list of student names. Write a complete code…
A: Please preserve the student.txt withinside the equal operating listing or offer entire route…
Q: Compression techniques make it possible to create several copies of a video with varying quality…
A: Introduction: The process of altering, encoding, or transforming data's bit structure so that it…
Q: The causes of cyber harassment, as well as its societal ramifications and preventative strategies,…
A: Here we have given a brief note on causes of cyber harassment and its societal ramification with few…
Q: In DES, if the input to the below S-Box was 101010, then the output will be: S₁0 1 2 3 4 5 6 7 8 9…
A: In the DES algorithm, the first and last bit represent the row number in binary. Given input -…
Q: What's the difference between logical and physical data flow diagrams?
A: The above question is solved in step 2 :-
Q: Why are segmentation and paging sometimes combined into one scheme?
A: Segmentation: Segmentation is a virtual procedure that produces segments—groups of similar…
Q: How is the hash value of a message protected? Does it function without the secret key?
A: Message authentication is an additional kind of security. Data secrecy is guaranteed by the message…
Q: Which Zigbee data fields are encrypted when both confidentiality and message integrity are provided?…
A: basics of ZigBee: Using wireless ZigBee technology is secure. The IEEE 802.15.4 format's security…
Q: Given a main program that reads the number of one word names followed by the list of names, complete…
A: Below I have provided C++ Programming. Also, I have attached the screenshot of the code and output…
Q: The concepts of heredity and polymorphism need a comprehensive explanation.
A: Please find the answer below :
Q: What is a cost model that uses algorithms? What disadvantages does it have in comparison to other…
A: The Answer start from step-2.
Q: During which age of computer technology was the word "debug" coined?
A: Launch: The process of debugging is used in software development and computer programming to find…
Q: How can linear programming be used to make the most prudent financial decisions?
A: INTRODUCTION Linear programming is a course of upgrading the issues which are exposed to specific…
Q: How is digital privacy defined in the context of developing technology? Can you share concrete…
A: Digital privacy means the protection of individual's information by using the internet which…
Q: When a web client requests access, native authentication and authorization services are used to…
A: The possible security measures are as follows: A fixed access control is created in the access point…
Q: How is the data flow approach preferable than narrative descriptions?
A: Introduction: A diagrammatic model of information flow and exchange inside a system is called the…
Q: What are the pros and cons of debugging using manual walkthroughs as opposed to print statements?…
A: What Is RST Debugging, exactly?A developer will go through the debugging procedure. utilizes…
Q: 2. Analyze the below program segment and find the syntax error. /* Tracing The Error*/ cin >>…
A: In this segment of code, there is problem in the syntax of all three lines.…
Q: A decision support system (DSS) is an information system that aids a business in making…
A: See how the aforementioned issue is resolved next. The following are various parts of the DSS…
Q: . Using the RSA public key cryptosystem, with a = 1, b = 2, etc., a. If p = 7 and q = 11, list five…
A: Given: Using RSA public cryptosystem : a = 1 , b = 2 Part a) if p = 7 , q = 11 n = p * q =>…
Q: It may be difficult for application proxies to interpret end-to-end encryption due of its…
A: Security end-to-end: Proxy-based systems are insecure. Article on end-to-end security. Authenticity,…
Q: (a) Ethernet uses CSMA/CD as its medium access mechanism. Can you explain how the three concepts…
A: What is Ethernet? Local area networks (LANs), which connect computers inside a main physical…
Only in shell command line
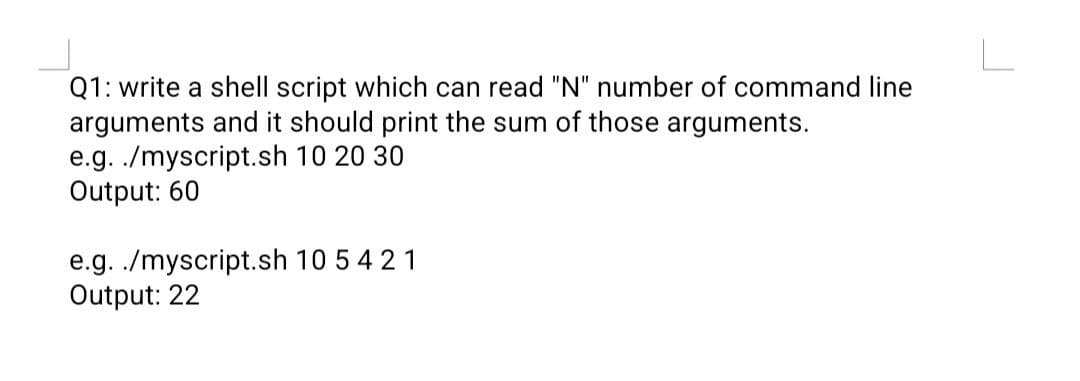
Step by step
Solved in 2 steps

- This needs to be done using Linux bash shell script. 2. Write a shell script display_digits to display all digits ( from leftright ) if the input is an integer, otherwise, show that the input isnot an integer, e.g.,"display_digits 1978 show "1 9 7 8", and"display Hahah12" should display "Hahah12 is not an integer"Hint: you will likely need to use the pipe | , echo command, and cut -ccommand. Also could you show screenshots.1. Explain the following unexpected result:$ whereis datedate: /bin/date ...$ echo $PATH.:/usr/local/bin:/usr/bin:/bin$ cat > dateecho "This is my own version of date."$ ./dateSunday April 14 10:00:49 PDT 2020 2. What are two ways you can execute a shell script when you do not have executepermission for the file containing the script? Can you execute a shellscript if you do not have read permission for the file containing the script? 3. What is the purpose of the PATH variable?a. Set the PATH variable so that it causes the shell to search the followingdirectories in order:• /usr/local/bin• /usr/bin• /bin• /usr/kerberos/bin• The bin directory in your home directory• The working directoryb. If there is a file named doit in /usr/bin and another file with the samename in your ~/bin directory, which one will be executed? (Assume thatyou have execute permission for both files.)c. If your PATH variable is not set to search the working directory, howcan you execute a program located…PLEASE USE MULTITHREADING IN THIS PROGRAM SO THAT MANY CLIENTS CONNECTED TO THE SERVER AND EACH CLIENT CAN SEND MESSAGE TO SERVER AND SERVER MESSAGE SHOWN TO ALL CLIENTS AND ONE CLIENT MESSAGE SHOWN TO ALL CLIENTS.PLEASE MAKE CHANGINGS IN THIS CODE. SERVER #include <stdio.h>#include <stdlib.h>#include <string.h>#include <unistd.h>#include <sys/socket.h>#include <sys/types.h>#include <netinet/in.h>#include <arpa/inet.h>#include <pthread.h>#define PORT 5500 void func(int connfd){ char buffer[1024]; int n; while(1) { bzero(buffer, 1024); read(connfd, buffer, sizeof(buffer)); printf("From client: %s\t To client : ", buffer); bzero(buffer, 1024); n = 0; while ((buffer[n++] = getchar()) != '\n'); write(connfd, buffer, sizeof(buffer)); if (strncmp("exit", buffer, 4) == 0){ printf("Server Exit...\n"); break; } }}int main(){ int sockfd, connfd, len; struct…
- Write a complete bash script that asks for a user name and uses the readcommand to accept the user name. (Use usernames C2456001 throughc2456030 to test.) The script reports if the user is logged in. Use the whocommand to obtain a list of users logged in then use grep in an if then elsestatement to match on the user name. Output whether that user is eitherlogged in or not logged in. (Usage: loggedIn.sh)You can configure your shell by editing the file~/.bashrc for instance to change the value of$ PS1 and $PAth permenatrly true or falseWrite a bash script that accepts aperson’s name as a command-line argument and simply prints out the following greeting: "Good day, <name_entered>! Nice to meet you!", where <name_entered> is a positional parameter (i.e., a command-line argument) passed to the script. If the user does notenter a command-line argument when invoking this shell script, you will simply output: "Hope you have a great day!", without any name displayed. How to do this??
- ******************SOLVE IN PowerShell, NOTHING ELSE******************** Write a function named ‘Generate-SSN' that generates all possible social security number in the form of ddd-dd-dddd. The output should be saved into a file named ssn.csv. Only the source code is required, do not submit ssn.csv.How to modify exitstatus.sh to print a message for each of the three exit statuses described in man ls. 0 - OK 1 - minor problem 2 - serious problem exitstatus.sh #!/bin/bash ls > /dev/null if [ $? -eq 0 ]; then echo "It seems to have worked, exit status 0" fi ls asdf 2> /dev/null if [ $? -eq 0 ]; then echo "It seems to have worked, exit status 0" else echo "An error occured, non-zero exit code." fi Solve fast pleaseIn Linux operating system: When writing shell scripts, we rely on the echo command to display output and prompt users for input. We know that the echo command will display exactly what we type on the command line unless we specify otherwise. What would be the command and option we would use to display what shell we are running followed by two newlines?
- Write a shell script to ADD two numbers? $ ./ADD 5 6 Output: Sum of 5 and 6 = 5+6 = 11 Use Switch Statement to solve the questionWrite Linux bash Shell Script, which will ask and display all information required to Student admission in Engineering and Sciences University. WEEK 3- Use following variables to write your CV in Linux bash script. Variable Script Output $0 $n $# $* $@ $? $$ $!In Command Prompt, we can run two commands on the same line independent of each other with the ampersand & (e.g. DIR & WHOAMI), and we can do the same in PowerShell with this character: Group of answer choices Comma , Semicolon ; Ampersand & Pipe |



