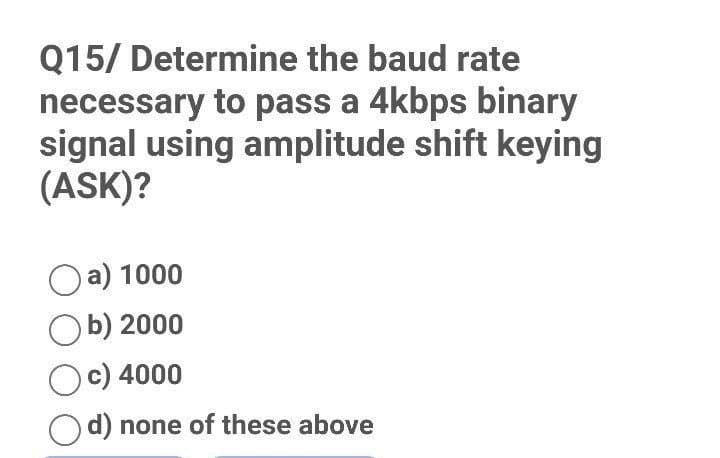
Q15/ Determine the baud rate necessary to pass a 4kbps binary signal using amplitude shift keying (ASK)? Oa) 1000 Ob) 2000 Oc) 4000 Od) none of these above
Q: Briefly define TinyOS and explain its goals as an embedded operating system.
A: Introduction Small, flexible, low-cost nodes that interact with their environment and each other…
Q: 5. Consider the following FIRST and FOLLOW sets, F, where S is the start symbol. a) Create the…
A: Below I have provided handwritten solution to the given question:
Q: using System; 2 using UserNamespace; // namespace 3 4 5 namespace UserNamespace 6 + { 7 8 9 // User…
A: The given code does not have any errors. it is just giving a warning saying that the value of…
Q: The act of opening a file serves what purpose exactly?
A: INTRODUCTION A file server is a focal server occurrence in a PC network that engages related clients…
Q: What do you know about wireless security? Discuss and evaluate your thoughts.
A: Examine and discuss your knowledge of wireless security. ANSWER: Unauthorized access to devices or…
Q: design an algorithm to find all the common elements in two sorted lists of numbers. For example, for…
A:
Q: What steps may be taken to decrease the dangers of cell phone use, and how can they be implemented?
A: Introduction: Use speaker mode, headphones, or earbuds to put more space between your head and the…
Q: In order for a network to be functional and efficient, what three things must it have? In your own…
A: An organisation should: Be able to choose whether or not to follow a set of rules. For a sustainable…
Q: laptop's OS is fundamentally different from the operating system that is used in the mainframe. If…
A: The differences and similarities in operating systems between a mainframe computer and a laptop…
Q: conversion from RGB to HIS colours is explained in detail
A: RGB process:- RGB stands for Red, Green and Blue colour. In the RGB process colours are represented…
Q: 14.28 Modify the quick sort so that it reverts to the insertion sort when the array size is below 8.
A: The sorting algorithm is used to re arrange the given array or list elements according to the…
Q: Develop a training programme for Telenor's assistant managers on the subject of employee engagement.
A: Training programme: A training programme is a sequence and mix of activities meant to help workers…
Q: A c# code please see pictures for more details. there is also a sample output. NOTE THAT THIS IS A…
A: solution in below step
Q: Fill in the blanks A child interface can inherit from parent interface(s) and override or revise the…
A: An interface can extend multiple interfaces i.e A child interface can inherit from multiple parent…
Q: When it comes to reviewing security operations and making suggestions for improvements, why would a…
A: To keep your company's data secure, security is crucial. High security prevents data breaches and…
Q: hat are the five most common applications of computer graphics?
A: Introduction: The following are five instances of computer fields where computer graphics are used:
Q: Q6/ Amplitude modulation is a) Change in amplitude of the carrier according to modulating signal b)…
A: Amplitude is the distance between the resting position and the maximum displacement of the wave .
Q: Distinguish between the three pillars of Enterprise Architecture based on data and information.…
A: NOTE :- Below i explain the answer in my own words by which you understand it well. The…
Q: When building software, what is the most important idea that should be kept in mind when working…
A: Building software: When developing software, a "build" refers to either the process of transforming…
Q: What are the three conditions for a network to be considered successful and effective? Let me know…
A: Efficiency is defined as the capacity to complete a task in the least amount of time, money, and…
Q: the usability of windows 11
A: 1. Windows 11 is more productive for remote working and calling out rival app stores. 2. User…
Q: Ada Lovelace is best known for what, exactly?
A: Ada Lovelace: Ada Lovelace was born on December 10, 1815. Her father was a famed poet Lord Byron.…
Q: Is it possible to explain how policy voids (computer ethics) arise? Detailed explanations are…
A: Computers are innovative and bring moral questions. I'll explain what makes computers different from…
Q: In the Unix file system, where are all the data and files of a certain user stored?
A: Given: Linux is a free and open-source Unix-like operating system based on Linus Torvalds' 1991…
Q: = . using a decoder and external gates, design the combinational circuit defined by the following…
A: The combination circuit diagram using decoder and external gates for the boolean function is given…
Q: Share some citation guidelines with us. Plagiarism has serious repercussions.
A: Students who engage in plagiarism or any other form of academic dishonesty risk significant…
Q: Explain briefly how the weighted approach may be used to convert decimal to ternary in a ternary…
A: Intro To the above-mentioned query. Please find the answer below. I'm writing the answer to this…
Q: Operating systems on laptops and mainframes are very different. What are the commonalities and…
A: Start: In answer to your query, The mainframe operating system is a piece of network software that…
Q: ?is a '=' Relational operator O Assignment operator O Operational operator O Arithmetic operator O
A: ? = is a
Q: When it comes to information security, what are the distinctions between the top-down and bottom-up…
A: Information security enables organisations to protect digital/analog information. Information…
Q: What data type in C# should I use in 1.0f / 2
A: What data type in C# should I use in 1.0f / 2
Q: Please help me with the errors I am e having the program below. There are two parts of the program.…
A: • Define EncryptMsg() method means to encrypt the original message. • Define DecryptMsg() method…
Q: Is it possible to avoid intrusions?
A: Is it possible to avoid intrusions?
Q: the usability of macos monterey
A: macOS Monterey was released to the public on October 25, 2021. Its release date was announced during…
Q: d array([['20', '60', '100', '140', '180'], ['12', '52', '92', '132', '172'], ['4', '44', '84',…
A: Code: import numpy as np d = np.array([['20','60','100','140','180'],…
Q: Direct access to essential technology is hotly discussed in today's culture.
A: solution in step
Q: When using MS Access to build our tables, how do we know which model to create?
A: Introduction: Access tables may be built by creating them in "View from the Design.
Q: For the purpose of offering customers the most value for their money, an airline sought a system…
A: The Pareto Principle is almost universally used. The income generated by 20% of your customers…
Q: Is it possible to explain how policy voids (computer ethics) arise? Detailed explanations are…
A: Computers are remarkable innovations that offer some unique ethical questions. In this essay, I will…
Q: Which of the following technology allowed dozens or even hundreds of users in the mainframe era to…
A: To use a system simultaneously we use threading. Multithreading is a way to utilize CPU for multiple…
Q: It is imperative that the topic of network security be addressed. Is there a difference between big…
A: This same integrity, confidentiality, and accessibility of computer networks and data are protected…
Q: Explain the AI Turing test in a nutshell? Briefly describe the role of the Turing test in the…
A: Explain the AI Turing test in a nutshell? Briefly describe the role of the Turing test in the…
Q: Which of the following codes would return a True result? (A) TRUE FALSE B) "user"== "user" False >=…
A: 9. Option D is correct D. -6*14>=17-101 10. Option D is correct D. reshape 11. Option A is…
Q: Make the representation of the following graph in Lucidchart Graph 1 Graph 2 V = {1, 2, 3, 4) V = {…
A: Graph1: Given vertices V= {1, 2, 3, 4} Edges={{1, 2},{2, 3},{3, 4},{4, 1},{1, 3},{2, 4}} Directed…
Q: Homework 12. Use NAND gates, NOR gates, or combinations of both to implement the following logic…
A:
Q: Discuss the importance of network security to you. Is the rationale for its importance different…
A: The three conditions that a network must meet in order to be successful and efficient are as…
Q: A serious accident occurred on the National Highway, so an ambulance arrived immediately and the…
A: Input/Output Process: First line contains five space separated integers N, M, R, X and Y denoting…
Q: List the different types of security and explain each one with an example.
A: Introduction: It is the safeguarding of data against unauthorised access, theft, damage, any…
Q: five quality objectives we outlined earlier?
A: solution in below step
Q: Determine which of the programming codes has less time (perform algorithmic complexity calculation…
A: Solution: Code 1, has less time.
Step by step
Solved in 2 steps with 1 images

- A(n) _____ operation transforms a 0 bit value to 1 and a 1 bit value to 0.Error Correction/Detection Hamming Algorithm ; Help with the following examples. For the Hamming code shown in Figure, when a check bit rather than a data bit is in error, would the Hamming Algorithm (1) not detect it; (2) detect it but cannot provide information to correct it; (3) detect and correct it? Can you please explain whyC programming in the bitwise exclusive or operator sets the output bit to 1 if at least one of the bits it runs on is 1(true or false)
- Calculate the difference of the following hexadecimal numbers: 5ED4 - 07A4. Assume the numbers are unsigned 16-bit values. Show your work.WAP to multiply first 10 numbers by using MPI_REDUCE(). wap-write a program mpi - parallel computing please explain how the code operates as wellASCII Codes can be helpful to find binary code of different decimal numbers and alphabets etc. You have to consider 65 and its equivalent code of 16 bits will be considered for bit sequence and a divisor for CRC. Follow this process; first 8 bits will be used for data while next 4 bits will be used for divisor (if there are 4 zeroes in your case then replace with 1001), neglect last 4 bits. Also check your answer.
- Fill in the blanks: Q. Broadcast __________________ Format is Better known as BWF.A. Subtract A0L(24)- 9NM(24)B. Convert to base 6 without converting it to base 10. QZA(36) X(6)4. Evaluate the mixed bit conditions: a) bit2 and bit6 are zero b) bit3 and bit 7 are one c) bit4 is zero and bit5 is one d) bit0 is zero, bit4 is one, bit7 is 1 **Clue: the solution can be stated with a mask + if-else condition

