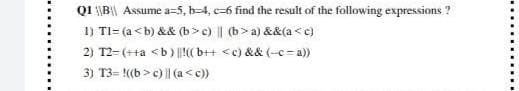
Q1B Assume a=5, b-4, e-6 find the result of the following expressions? 1) Tl= (a c) || (b>a) &&(a c) || (a
Q: Explanation with the diagram of the sequence diagram that represents a model for executing the…
A: Sequence diagram represents the interaction between the objects in a sequential order. This sequence…
Q: When both RAM (Random Access Memory) and cache memory are transistor-based, why do we need cache…
A: In terms of performance, cost, and proximity to the CPU, both RAM and cache offer benefits and…
Q: To what extent does "interdependence" differ from other terms used in system theories, and how does…
A: Interdependence is one of the most critical concepts in systems theory because most definitions of a…
Q: You work for a large soft drink company as a consultant. Explain to the organisation how the…
A: You work as a consultant for a big soft drink company. Outline for the organisation how the internet…
Q: First compile a list of all the distinct mathematical operations, and then sort the items on the…
A: A set of rules known as the order of operations dictates which mathematical functions should be…
Q: Please explain how to close a record in a database and provide a description of how to do it.
A: Data base: A database is an organised data structure that holds information. A company's database…
Q: Is a system development life cycle (SDLC) required for the creation of an LMS portal?
A: System Development Life Cycle (SDLC): The system development life cycle is a project management…
Q: Using a class B IP address with default subnet mask, what is the usable number of hosts available on…
A: The class of IP address is used to determine the bits used for network ID and host ID and the number…
Q: A comprehensive explanation of the properties and operations available on the Command Object
A: Introduction: The uses, purposes, and methods of command objects. The services, definitions, and…
Q: What are the similarities and differences between computer science and other academic fields? What…
A: Computer science is the study of computers and algorithmic processes, including their principles,…
Q: A look at how big data allows businesses to keep tabs on vast quantities of personal information.…
A: Extensive data collections that surpass actual databases and data processing infrastructures are big…
Q: Explain why you favour websites with simple visuals in certain cases and those with more elaborate…
A: The audience is given the impression of wealth through the presence of expensive objects and…
Q: Provide an explanation of the technical underpinnings of information technology, including its…
A: provide an explanation of the technical underpinnings of information technology, including its…
Q: Who are the people involved in the phases of Waterfall Model
A: In order to develop any software, the framework which is used to define the system is known as SDLC…
Q: Code in C, Implement a C program using the stack and queue operations Code a stack and queue test…
A: Answer
Q: Are there any new governance issues that may arise when moving from on-premise servers to a…
A: Introduction: The delivery model known as infrastructure as a service (IaaS) is used by charity…
Q: How does the iterative and incremental nature of the agile methodology relate to the more…
A: Agile methodologies attempt to create the best product by delivering tiny pieces of functionality…
Q: By stating four key traits, how can you distinguish systems from systems?
A: Important characteristics include: A system of systems is a phrase used in computing to describe a…
Q: Explanation of the Terms Used 1. The Software 2. The Hardware 3. The Operating System
A: Find the required answer given as below : As per company guidelines we are supposed to answer only…
Q: Define a function: Void Insert(char str1[], char str2[], int pos) to insert str2 to str1 from pos.…
A: Code: #include <stdio.h>#include <string.h>//Defining the required functionvoid…
Q: In the process of building an LMS portal, what sort of system development life cycle should we
A: Step 1 An LMS portal may be used by administrators: and content providers to create, distribute,…
Q: 2. Given the following NFA state diagram a,b a a 90 92 93 The input string to the above NFA is…
A: Given NFA state diagram contains, Set of states= {q0, q2, q3} Set of input alphabets= {a, b} Initial…
Q: Diffie-Hellman Key exchange is based on the difficulty of solving the Discrete Logarithm Problem.…
A: Answer in step 2
Q: When a timer interrupt occurs, describe the steps that take place, culminating in a context…
A: Given: The "timer interrupt," which is sent at regular intervals through a timer chip, is likely the…
Q: Give at least three CSS terms from today's lesson. Explain how the three keywords you've picked are…
A: KEYWORDS IN CSS: CSS properties feature several particular keywords that are sometimes used as…
Q: Under the umbrella phrase "personal data," there are a wide range of distinct types of information.…
A: The word "personal data" refers to a wide variety of distinct types of information, all of which are…
Q: Should firms or governments be able to purchase massive amounts of information about your purchasing…
A: Launch: Using data mining methods, consumer data warehouses may assist a corporation in suggesting…
Q: Q2. Define software quality ( . What is software ..)? Define unit testing and give an example…
A: Software quality The software quality means that the developed software should be error free that…
Q: During the transition from on-premise servers to a design based on IaaS, what are some of the…
A: The organization's administration uses a deployment pattern known as infrastructure as a service…
Q: Businesses should be able to identify a range of data preservation techniques.
A: Preservation Techniques: Drying, chilling, and fermentation are some of the earliest ways of…
Q: Please enumerate the eight design concepts that are most crucial for user interfaces. If you had to…
A: The design of user interfaces should adhere to these eight essential guidelines, which are listed in…
Q: This is the scenario as a result of the increasing power of modern computers. In recent decades,…
A: Introduction: Computers are unquestionably strong for a large number of reasons. They work…
Q: Upon completion of interrupt service, how does the application software resume its normal operation?
A: Application software: The operating system offers an interface between application software and the…
Q: -what types of data could be used to monitor the performance of a fast food restaurant
A: what types of data could be used to monitor the performance of a fast food restaurant . in the…
Q: What will occur if the mouse cursor in the code editor is kept on a jagged line for a lengthy period…
A: Mouse Cursor: In the left-hand column of the Devices screen, choose Mouse. Additional mouse choices…
Q: What if there is only one packet in the token ring, and station 1 retains it until it completes one…
A: The Token Ring protocol is a local area network communication mechanism (LAN). The topology of the…
Q: What can we learn, both in terms of advice and conclusions, by looking at cybercrime?
A: Cybercrime is any crime that is committed using a computer or other device connected to the…
Q: Arrange the following in order of which the systems looks into first when it searches for its price:…
A: Answer the above questions are as follows
Q: In healthcare, what are the best procedures for preventing data breaches?
A: Start: Answer to the question posedAn unauthorised individual gained access to private, sensitive,…
Q: Demonstrate the possibilities of Network APIs using the example of making a phone call.…
A: Introduction to Network API An Application Programming Interface, often known as a…
Q: Which approach is the most effective when it comes to installing and administering both physical and…
A: SDN controller: This item, which is referred to as the SDN controller, performs the tasks of a…
Q: What does main return? Consider the following program:
A: #include <stdio.h>int f(int x,int y);int a = 3;int b = 2; int main(void){ int c = a + b; //…
Q: Provide a minimum of ten (10) instances of different scenarios in which you are able to relate as a…
A: Given: List at least ten (10) situations to which you can relate as a function. The quantity of…
Q: How may regions and availability zones be used to improve the cloud application's resilience,…
A: Cloud Computing is becoming the norm. Of course, cloud resources are still physical devices that…
Q: First compile a list of all the distinct mathematical operations, and then sort the items on the…
A: Introduction: The order of operations is a collection of rules that dictates which activities should…
Q: If prototyping is used in the design of user interfaces, do you think it will be possible to solve…
A: Prototyping permits visual inspection: Prototyping is an iterative process in which design teams use…
Q: You can define numbering series for journal entries on the document Numbering screen under the…
A: Document numbering is often set up during SAP Business One implementation, but there are many…
Q: 4.A) Define the THREE (3) types of communication. unicast, broadcast, and multicast
A: Introduction: Multicast communication is a sort of correspondence wherein one host conveys…
Q: What is tensor flow and how does it apply to artificial intelligence?
A: Python's open-source module known as TensorFlow makes machine learning processes more streamlined…
Q: Two predicted virtualized operating system impacts should be identified and explained.
A: Virtualization: Virtualization on operating systems - Virtualization is dependent on the operating…
Max Function
Statistical function is of many categories. One of them is a MAX function. The MAX function returns the largest value from the list of arguments passed to it. MAX function always ignores the empty cells when performing the calculation.
Power Function
A power function is a type of single-term function. Its definition states that it is a variable containing a base value raised to a constant value acting as an exponent. This variable may also have a coefficient. For instance, the area of a circle can be given as:
Step by step
Solved in 3 steps

- (Physics) Coulomb’s Law states that the force, F, acting between two electrically charged spheres is given by this formula: F=kq1q2r2 q1isthechargeonthefirstsphere.q2isthechargeonthesecondsphere.risthedistancebetweenthecentersofthetwospheres.kisaproportionalityconstant. Write an assignment statement to calculate the force, F.C++ Angle Calculator Write a program that asks the user for an angle, entered in radians. The program should then display the sine, cosine, and tangent of the angle. (Use sin, cos, and tan library functions to determine these values.) The output should be displayed in fixed-point notation, rounded to four decimal places of precision.c## please Write a Console Application that reads two integers, determines whether the first is a multiple of the second and displays the result. [Hint: Use the remainder operator.]
- (Rounding Numbers) Function floor can be used to round a number to a specific decimal place. The statementy = floor(x * 10 + 0.5) / 10;rounds x to the tenths position (the first position to the right of the decimal point). The statementy = floor(x * 100 + 0.5) / 100;rounds x to the hundredths position (the second position to the right of the decimal point). Write a program that defines fourfunctions to round a number x in various ways:A. roundToInteger(number)B. roundToTenths(number)C. roundToHundredths(number)D. roundToThousandths(number)For each value read, your program should print the original value, the number rounded to the nearest integer, the number rounded to the nearest tenth, the number rounded to the nearest hundredth and the number rounded to the nearest thousandth.Problem: Feed Nibble Monster Till Full Write a program that generates a number in [0, 500] at the beginning -- this corresponds to how hungry the monster is -- and keeps asking the user to feed the monster until that number falls to zero. Each time the user feeds the monster a nibble, hunger decreases by the decimal value of the character (i.e. if the user feeds 'A' hunger decreases by 65). But when the user feeds the monster some character that isn't a nibble, the hunger increases by the decimal value of the character (since puking depletes energy). Use while loop. Sample runs: Notice the loop exits after one iteration, because hunger was very low and one nibble made the monster full: Notice hunger increasing after non-nibble (pink highlight): Notice that the program just keeps going when the user feeds the monster only non-nibbles. Do you think the program will keep running forever if the user never gives the monster nibbles?color: one of the following strings: 'red', 'blue', 'silver', 'white', 'black'year: year of manufacturing. A number between 1990 and 2018company: one of the following strings: 'Honda', 'Toyota', 'Ford', 'Chevrolet'model: one of the following strings: 'sedan', 'hatchback', 'SUV'Give a logical expression that evaluates to a True or False for a set of cars. e.g. Expression for "Red SUV cars" is (color == "red" and model == "SUV") Give an expression for "Ford sedan cars that are red or blue and were manufactured after 2000"
- Using class and objects write a C++ program which can read students' information (Name, Sex, Nationality, Age, Adress (village number and house number)) and: a) Display all the data in a tabular form b) Filter out only females and display the data in tabular form c) Filter out only students whose ages are less than 20 Remember that you should be using a C++ program that uses class and objects1. [LO 1, LO 2, LO 3 & LO 4, Treasure Hunter Description You are in front of a cave that has treasures. The cave can be represented in a grid which has rows numbered from 1 to , and columns numbered from 1 to . For this problem, define (x,y ) as a tile that is in the the-x row and the y-row. There is a character in each tile, which indicates the type of that tile. Tiles can be floors, walls, or treasures which are represented respectively by the characters '.' (period), '#' (hashmark), and '*' (asterisk). You can go through the floor tiles and treasures, but you can't get past the wall tiles.Initially, you are in a tile (??, Sy). You want to visit all the treasure squares, and retrieve the treasure. When you visit a treasure tile, the treasure is instantly retrieved, and the tile turns into a floor.In a move, if you are on a tile (?,y), then you can move to the right tile above (?-1,y), right (?,y + 1), down (? + 1, ), and left (?, 1) of the current tile. The tile you visit must…Driving costs - functions Learning Objectives Create a function to match the specifications Use floating-point value division Instructions Driving is expensive. Write a program with a car's miles/gallon and gas dollars/gallon (both floats) as input, and output the gas cost for 10 miles, 50 miles, and 400 miles. Output each floating-point value with two digits after the decimal point, which can be achieved as follows: print(f'{your_value:.2f}') Ex: If the input to your program is: 20.0 3.1599 the output is: The gas cost for 10 miles is $1.58 The gas cost for 50 miles is $7.90 The gas cost for 400 miles is $63.20 Your program must define and call the driving_cost() function. Given input parameters driven_miles, miles_per_gallon, and dollars_per_gallon, the function returns the dollar cost to drive those miles. Ex: If the function is called with: 50 20.0 3.1599 the function returns: 7.89975 def driving_cost(driven_miles, miles_per_gallon, dollars_per_gallon) Your program should…
- Using Figure 3, c) write a piece of code in C# that calculates the area of a triangle displaying the area in the area textbox. [5] d) write a piece of code in C# that changes the colour of the form to Red when the form is loading. [5] e) write a piece of code in C# that changes the colour of the colour of the Height textbox to lime when the mouse hoovers over the Base textbox.C++ Programming point* go_far(point* other) Return the point bearing the x- and the y- coordinates of whichever x- and y-coordinates is further from the origin. Identify which of the two points have the furthest x- and y-coordinates independently. Example: this point has (-5, 1) and the other point has (4, 9). In the x-coordinate of the two points, -5 is further from the origin than 4. In the y-coordinate of the two points, 9 is further from the origin than 1. Hence, we return a new point bearing the coordinates (-5, 9).The Barking Lot is a dog day care center. Design a flowchart for the following: A program that continuously accepts dogs’ data until a sentinel value is entered, and displays billing data for each dog.





