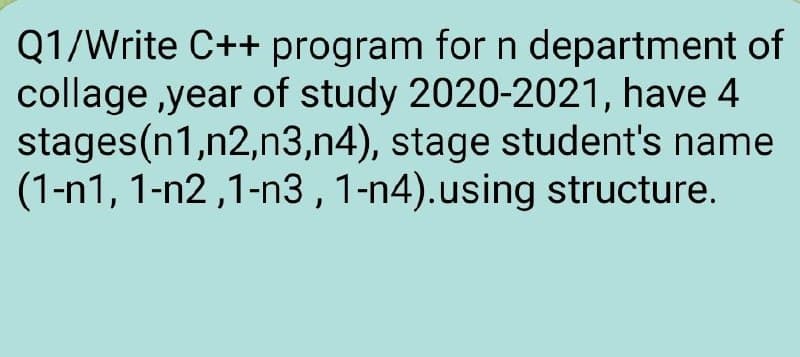
Q1/Write C++ program for n department of collage ,year of study 2020-2021, have 4 stages(n1,n2,n3,n4), stage student's name (1-n1, 1-n2 ,1-n3 , 1-n4).using structure.
Q: What are TCP/four IP's abstraction layers?
A: There are Four layers of The TCP/IP Model: Network access, internet, transportation, and application…
Q: List four criteria for comparing the packages used by enterprises to track software development…
A: Given statement: List four criteria for comparing the packages used by enterprises to track software…
Q: Describe how you use databases or applications connected to databases in your daily life. Consider…
A: A database: A database is the collection of information that is kept on a server. The data is…
Q: Describe basic C input/output functions. Name and describe standard input and output devices.
A: Have been submitted, we will respond to the first one. If you have a particular question that you…
Q: Consider the following proposition: The greatest threat to individual privacy in modern times is…
A: In fact, the following is the solution given:Procedure Number Two (Secondary)Privacy, in its most…
Q: What is a port scan, exactly?
A: answer is
Q: When a validation rule is violated, the Validation Text property box's text is shown. Why is it…
A: Introduction: The ValidationRule property can be used to establish data entry requirements for a…
Q: explain and clarify the term "non-technical" cyberattacks?
A: Given: Define and describe the situation Attacks against cybersecurity that aren't technically…
Q: in in bri
A: DMA represents Direct memory access . It is fundamentally a sort of technique it basically permits…
Q: What types of non-text data could you wish to store in a database? What problems can arise when…
A: Let discuss about the non-text data: Non text data can be of multiple types which includes images,…
Q: Find "Announcing the Advanced Encryption Standard (AES)" on the internet. This FIPS 197 standard…
A: Advanced Encryption Standard: It is encryption technology adopted by the United States government to…
Q: When making hardware decisions, what three factors are taken into account?
A: Answer: The components of a computer system used for input, processing, output, and storage are…
Q: How do you read, delete, or search a list of user id and passwords using a BST (Binary Search Tree)?
A: Binary Search Tree is a one-site binary tree data structure with the accompanying elements: The…
Q: Which one of the followings is FALSE for UML package diagrams?
A: which one is FALSE for UML package diagrams
Q: Discuss about the techniques to implement blockchain and the challenges in implementation to…
A: The question was to know about the techniques to implement blockchain and challenges to implement…
Q: Write down all 16 tests to satisfy Multiple Base Choice coverage (MBCC) for the second…
A: Introduction: Testing is about choosing elements from input domain. The input domain of a program…
Q: Describe basic C input/output functions. Name and describe standard input and output devices.
A: Answer Basic input and output in C: C language contains standard libraries which allow input and…
Q: Computer science What is Apache, and what function does it serve?
A: Introduction: Apache is merely one of the components required to provide online content in a web…
Q: Do you agree that using threading for loops will speed up execution time if we use loops?
A: Threading allows concurrent execution.
Q: Explain the key distinction between recurrent and non-recurrent neural network processing.
A: Answer Recurrent Neural Network: A type of artificial neural network where a directed cycle forms…
Q: Exercise 3: Building a Point of Sales (POS) using a linked list data structure. In a POS system, a…
A: Possible solutions include: Creating a linked list data structure for a point of sale (POS):…
Q: In a face recognition system, a query image with face id number q-10 is given, ane top-9 matching…
A: Mean Average Precision(mAP) is a metric used to evaluate object detection models such as Fast R-CNN,…
Q: Deployment diagrams show the hardware for your system.
A: Introduction: Deployment diagrams are nothing but the UML diagrams that helps in showing the…
Q: One of the most significant differences between a cell phone and a PDA is that a PDA may be turned…
A: Introduction: In addition to waiting for calls, a mobile phone maintains time synchronisation and…
Q: What does "infrastructure mode" mean for a wireless network? What mode of operation is the network…
A: In a wireless network, there are two modes of operation: infrastructure mode and other modes of…
Q: Computer science Explain how a Computer may be used by a) A manager of a Shopping mall
A: Introduction: For stock maintenance, official and employee information, displaying data, occasional…
Q: Q1. Chows the correct answer. 1. Maximum operating frequency of PIC microcontroller is 8 MHZ 12 MHZ…
A: We need to find the correct option regarding PIC microcontroller.
Q: If hierarchical inheritance requires to inherit more than one class to single class, which syntax is…
A: Inheritance is the feature of programming language through which one class can acquires/inherits the…
Q: what are the last two letters ( pronunciation of ed) of these verbs in the box.( hoped, missed ,…
A: Among the words - hoped, missed, laughed, begged, robbed, smelled, ended, presented
Q: Why do Chrome OS machines use less internal storage than other desktop operating systems?
A: Introduction Why do Chrome OS machines use less internal storage than other desktop operating…
Q: MARIE Simulator/MARIE Architecture Why do IR and MBR contain the identical contents at times but…
A: Answer: The data in MBR is later passed to IR (Instruction Register) IR – Holds the instruction…
Q: نقطتان )2( Multiple inheritance is When a class is derived from other two derived classes When a…
A: When a class is derived from two classes
Q: The Apple Interface Builder in XCode is a complicated tool with many unique capabilities. What about…
A: Introduction
Q: Computer science What is network protocol? Explain the following network protocols (in your own…
A: Introduction: A network protocol is a predefined set of rules that govern how data is delivered…
Q: iscuss the different forms of interrupts briefly, and then explain how interrupts are crucial to the…
A: Introduction: When a process or event requires rapid attention, an interrupt signal is issued to the…
Q: Organizational, administrative, and technological components of an information system include what?
A: Components of Technology: The technical component is a portion of a procedure or service payment…
Q: Please design an algorithm to detect the fake coin
A: => Fake coin problem, we have N number of coins all of equal weight, out of them, one is fake and…
Q: What do you mean by "worst case efficiency" of an algorithm?
A: In this question we are asked about an algorithm's "worst case efficiency". We have three types of…
Q: What are the advantages of using Firewall rules?
A: Introduction: There Are so many benefits benefits of Firewall.
Q: Do database designers need to be aware of any specific technique that, when used in certain…
A: Introduction: As certain that the system has the ability to expand in tandem with your data:
Q: complete the questions and answers. Used the word in brackets and in the evening some friends. (come…
A: Answer: and in the evening some friends came for diner . On Tuesday I had lunch with some…
Q: What are the four components of IEEE 802.11?
A: Given: IEEE 802.11 architecture is made up of four components. 1) Channels (STA) - All devices and…
Q: The "intermediary layer" is the layer that stands between a database and a client server.
A: True In the three-tier architecture, the intermediate layer between database and client servers
Q: Explain how the onion routing technique can help to improve communication anonymity.
A: Onion routing: Onion routing is a technique for anonymous communication over a computer network. In…
Q: In the context of computer language design, define orthogonality.
A: Introduction: The attribute orthogonality means that "changing X does not impact Y."
Q: What are the most popular interior and outside routing protocols in today's networks?
A: Introduction: It describes how routers communicate with one another to exchange information that…
Q: Computer science Why do many virtual machines use a stack-based intermediate form?
A: Introduction: Why do many virtual machines use a stack-based intermediate form? It's a…
Q: What are the dangers associated with database migration from one server to another?
A: Database Migration: When data is migrated to a new system or target system, certain data may not…
Q: The intermediate stage is the layer between the database and the client servers.
A: application server
Q: What are the benefits of DBMS?
A: Introduction: Examples of the advantages of DBMS, a Relational Database, and how to use one
Step by step
Solved in 2 steps with 2 images

- please complete the following program in c++ and avoid using any advanced manipulators, strings, or global variables. Thanks(Conversion) a. Write a C++ program to convert meters to feet. The program should request the starting meter value, the number of conversions to be made, and the increment between metric values. The display should have appropriate headings and list the meters and the corresponding feet value. If the number of iterations is greater than 10, have your program substitute a default increment of 10. Use the relationship that 1 meter = 3.281 feet. b. Run the program written in Exercise 6a on a computer. Verify that your program begins at the correct starting meter value and contains the exact number of conversions specified in your input data. c. Modify the program written in Exercise 6a to request the starting meter value, the ending meter value, and the increment. Instead of the condition checking for a fixed count, the condition checks for the ending meter value. If the number of iterations is greater than 20, have your program substitute a default increment of (ending value - starting value) / 19.please complete the following program in c++ and avoid using any advanced manipulators, strings, or global variables. Also please share your outuput results. (sample desired results are shown) Many Thanks
- Q7/ Write a program in C++ that asks the user to enter two numbers and prints the sum, product and difference of the two numbers by using function (Where there are three functions, the first for addition, the second for multiplication, and the third for subtraction).2. Write a complete C++ program to find the sum of prime numbers. You should prompt the values from the user. You MUST use Flag-controlled while loop structure. Prime numbers are whole numbers greater than 1, that have only two factors 1 and the number itself. Prime numbers are divisible only by the number 1 or itself. For example, 2, 3, 5, 7 and 11 are the first few prime numbers.Q3: Write a program of c++ that prints the day number of the year, given the date in the form month-day-year. For example, if the input is 1-1-2006, the day number is 1; if the input is 12-25-2006, the day number is 359. The program should check for a leap year. A year is a leap year if it is divisible by 4, but not divisible by 100. For example, 1992 and 2008 are divisible by 4, but not by 100. A year that is divisible by 100 is a leap year if it is also divisible by 400. For example, 1600 and 2000 are divisible by 400. However, 1800 is not a leap year because 1800 is not divisible by 400.
- 3. Write a program in C to concatenate two String S3 and String S4, to concatenate these strings call a function StrConcate()In C++ , please complete the program, whilst avoiding advanced manipulators or strings. ThanksComplete the blank in C++ program in Figure 1 below to display the space, lower case and upper case numbers for “Great Day\n”. The answer should be the appropriate built in function that will perform the operation based on comment given.
- Using C++; Define a struct, fruitType, to store the following data about a fruit: Fruit name (string), color (string), fat (int), sugar (int), and carbohydrate (int). Write a program that declares a variable of type fruitType, prompts the user to input data about a fruit, and outputs the fruit data.1. Write a c program that accepts a string from the user and outputs the length ( do not use any buit-in functions ) (Hint you may use while loop – while the character read is not equal to ‘\0’ increment the count. ) 2. Using the code above. Add additional codes that will copy the characters in reverse order (Note: Write comments that explain what each main section of the code is accomplishing and how)Write a program in C++ that should calculate the insurnace for a house. use questions below to write your programm. what is your first? what last name? how many people are living in the houes? how much did you bought the house for? how many bedrom does it have? what is the lenght in squre feet? - use Loop so everyone can repeat the programm. use function like "viod" and any other function. and finally use this formula: X/150*y/*50 x is the total price of the house y is the number of bedrooms s is the lenght in square feet.



