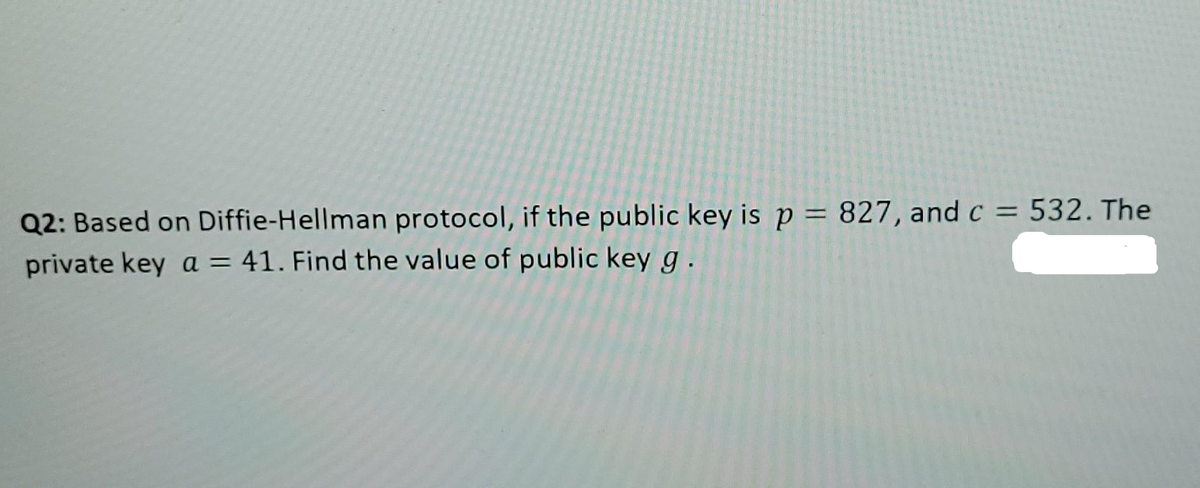
Q2: Based on Diffie-Hellman protocol, if the public key is p = 827, and c = 532. The private key a = 41. Find the value of public key g.
Q: Create your own original .csv file named lab16.csv, with at least 3 columns and 6 rows of data. You…
A: code: with open(r'lab.csv') as f: for line in f: list1 = line.split(",") for item…
Q: It is possible to see the advantages and disadvantages of both symmetric and asymmetric encryption…
A: symmetric encryption and how does it work: As the name implies, symmetric key cryptography is…
Q: Unable to connect to network. The LED lights near the computer's network interface are not lighted.…
A:
Q: A computer system's hardware and software are like two sides of the same coin. Discuss.
A: Given: The computer system has two essential parts: Computer Hardware and Software.Software.
Q: t reads the data of the dates and stock volumes into two separate lists. Output: The program must…
A: First, create the input file "data.txt" and then use the code below:
Q: Provide a brief description of 4GLs.
A: Answer
Q: Show that p Aq=q^p.
A: Propositional Logic: It is a collection of declarative statements which has either a truth value…
Q: 1. The National Earthquake Information Centre has the following criteria to determine the…
A: Richter scale is a logarithmic scale used to rate the strength or total energy of earthquakes.
Q: P4 The system should be tested against both user and system requirements.
A: Answer: User acceptance testing (UAT), also called User Acceptability Testing, Beta, Application, or…
Q: What does the word "System Mission" mean to you, and how would you describe it? What is the…
A: answer is
Q: 10)The Memory Data Register (MDR) is designed such that it _. a. is logically connected to all…
A: To find the Memory Data Register (MDR) is designed such that it ____________.
Q: What was the "Analytical Engine" and how did it work?
A: Engine Analytical: An analytical engine is a machine that was initially conceived by Charles Babbage…
Q: Distinguish between a security standard and an information security policy. Explain why they're both…
A: The given question that is the difefrence between the security standard and information security…
Q: Indices can speed up query processing, but it's usually a terrible idea to index every a
A: The answer is
Q: Why do we need official standards for copper cable and fiber-optic cable?
A: Dear learner , hope you are doing well , I will try my best to answer this question. Thank You!!
Q: What are two reasons why layered protocols are used? Give examples to illustrate your point.
A: Layered Protocols: Layered protocols are mostly utilised in networking technology. The two…
Q: When implementing a new system, list and define the most important activities.
A: Introduction: The most important responsibilities of system implementationThe initial job is…
Q: ow would you answer this? Explain how the E-mail message exchanges from Sender and Re
A: Lets see the solution.
Q: When comparing the ARM architecture with the core i3 architecture, what are the most significant…
A: Introduction: The ARM architecture is designed to be as functional as possible while using the least…
Q: How would you answer this? What is the difference between physical connection (Physical topology)…
A: here in the question they ask for the difference between physical connection and logical connection…
Q: What type of protection is provided by IPsec for VPN traffic? 4 O Hashing O User authentication O…
A: We are going to understand what are the services provided by the IPsec for VPN traffic.
Q: Public key cryptography, which uses asymmetric encryption techniques, has numerous advantages?
A: Public key cryptography Asymmetric encryption or the public key cryptography are the process of…
Q: 1. If we have the following java code: Bug bug = new Bug(); Bug spider = new Arachnid("red",…
A: => here given the code of java snippet , and in the question ask for output. => i provide my…
Q: 20)Memory is composed of _. a. 1-bit cells and each cell is addressable b. rows of 8-bit cells where…
A: Memory is made up of Large number of cells. Memory is made up of bits arranged in a two-dimensional…
Q: There are distinctions between hard and symbolic linkages.
A: Foundation: Symbolic linkages refer to paths. This may be anywhere in the system's file tree, and it…
Q: Give an explanation of the function a repository plays in the creation of systems.
A: REPOSITORY: A repository is a centralized area where all of the data and information is kept safe…
Q: 2.10 Consider the following program: int x = 0, y = 0; co x = x + 1; x = x + 2; // x = x + 2; y = y…
A:
Q: Input the Product name in upper case if the quantity is less than or equal to 20, and lower case if…
A: product name=input("enter the name") quantity=int(input("enter the value") if (quantity<=20):…
Q: My Solutions > MATLAB Documentation Reset FA1.5-3_Function Triangle_Area Create a function…
A:
Q: IMPORTANT: you need to complete the PDP thinking process for each program. 2 programs and a data…
A: code: with open(r'lab.csv') as f: for line in f: list1 = line.split(",") for item…
Q: In terms of email, what can be done to improve the process? Give clear instances of what you mean.
A: The technique helped in email communication: Email communication is a fundamental instrument for…
Q: Given the following min() method as well as the possible mutations of min(). provide reachability,…
A:
Q: Packages for Speech Recognition in Python are listed below.
A: Introduction to Speech Recognition: Speech recognition is a computer software that converts human…
Q: For example, consider the situation of a page fault. What part of the operating system do they have…
A: Extending a considerable distance away from a surface or area: As an illustration, a vast cavern, a…
Q: Which of the following (perhaps more than one) are network topologies? a st
A: The proper choices are the star and the bus. Different Types of Topology
Q: What do the various components of TCP/IP perform?
A: According to the question the TCP/IP was the developed by united sates of the department of the…
Q: 7)There are many situations in logic design in which simplification of logic expression is possible…
A: The NOR gate is a digital logic gate that implements logical NOR - it behaves according to the truth…
Q: . Assume the languages C++ and Java. Give as precise binding times as you can for the ollowing…
A: Binding is the process of associating an attribute with a name. Binding Time is the time where the…
Q: In this lesson, we'll talk about an application life cycle management environment and give two…
A: Given: The programmers use the design specifications (programming requirements) to code, test,…
Q: Examine how information and communication technology (ICT) may be utilized to enhance organizational…
A:
Q: Please be detailed as much as possible. Will give thumbs up if the answer has detailed explanation…
A: We are going to understand when do we prefer using adjacency list over adjacency matrix and when do…
Q: QUESTION 3 How do you model the following situation with a UML class diagram: There are multiple…
A:
Q: Is there a benefit to using Responsibility Driven Design? Explain with an appropriate example.
A: The advantage of using Responsibility Driven Design is as follows: Responsibility-driven design is…
Q: Describe the steps involved in doing a thorough walkthrough. During a walkthrough, who is…
A: Introduction: In a walk-through test, an auditor will examine how a transaction is begun and…
Q: Cryptography is a field of study that focuses on ensuring the safety of digital data. Which three…
A: Encryption is way for data like messages or files to be made unreadable making sure that only the…
Q: Which of the following (perhaps more than one) are network topologies? a star, a cloud bus, and a…
A: INTRODUCTION:Here we need to tell which of the following are network topologies.
Q: 13)The Control Unit determines the _. a. particular instruction to be executed by interpreting the…
A: Answer is : a particular instruction to be executed by interpreting the source code The control…
Q: ollowing the Function Design Recipe, create a complete function named get_consonant_cluster that…
A: According to the Question below the Solution: Output:
Q: It is the layer that connects a VB program to a database file
A: Answer: Data Access Layer (DAL)
Step by step
Solved in 2 steps with 1 images

- What is the Diffie-Hellman algorithm for exchanging a secret session key?Can you please help me with this: RSA can be used for: Digital Signature Encryption and Decryption Key exchange All the above RSA is secure because: Factoring large integers is easy Factoring large integers is hard Modular arithmetic is hard Modular arithmetic is easy Which description about the Diffie-Hellman Protocol is NOTcorrect? Diffie-Hellman Protocol is used to negotiate a key over a public channel. The base gand modulus pare publicly known. Diffie-Hellman Protocol authenticates each party. Diffie-Hellman Protocol is vulnerable to the Man-In-The-Middle Attack.q12- The security of symmetric encryption depends on the secrecy of the algorithm, not the secrecy of the key as the key is shared between the sender and receiver. Select one: True False
- Please enumerate and elaborate on the ideal qualities of a cryptographic hash function.Find the greatest common divisor of 26 and 5 using Euclidean algorithm. An encryption function is provided by an affine cipher ?:? → ?, ?(?) ≡ (5? + 8)??? 26, ? = {1,2, … , 26}Find the decryption key for the above affine cipher. Encrypt the message with the code 15and 19.In digital signature, the receiver uses the private key of the sender to decrypt the digital signature and restore the original hash of the message. True False
- Computer Science In the context of the ElGamal signature, the public key is (257, 76, x), where "x" is not known to you. Two packages were sent through the insecure channel as follows: (400, 54, 150) (321, 54, 149) Was there a re-use of the ephemeral key? If the answer is "yes", find it. If the answer is "no," answer "no" without the quotations.Can an AES key be shared secret encrypted? Justify your response Distinguish between hash and keyed hash See a real-world example of a one-keyed hash function.The contrast between private and public keys in cryptography
- In a public key, cryptosystem using RSA algorithm, user uses two prime numbers 5 and 7. He chooses 11 as Encryption key, find out decryption key. What will be the cipher text, if the plaintext is 2? Decrypt the cipher text, what will be the value of plain text?Can an AES key be encrypted using a shared secret? Defend your response Compare hash function with keyed hash function. View an example of a one-keyed hash function.1. Asymmetric Encryption and Message Authentication: a) The primitive root of a prime number is the basic principle of Diffie-Hellman. i) Is 3 the primitive root of 11? Show the proof with your calculation. ii) What are the important criteria for selecting a prime number in cryptography? Is 11 a good choice for such a purpose? b) Find the parameters stated using the Diffie-Hellman methods, given the user A and B shared a prime number and its primitive root of 23 and 5, respectively. i) If user A public key value is 8, find the A’s private key. ii) If user B public key value is 19, what is the common secret key? c) In the following scenario, we will compare the security services that are given by digital signatures (DS) and message authentication codes (MAC). We assume that James can read all messages send from Chan to Badrul and the other way around, too. James has no knowledge of any keys but the public one in the case of DS. State whether and…

