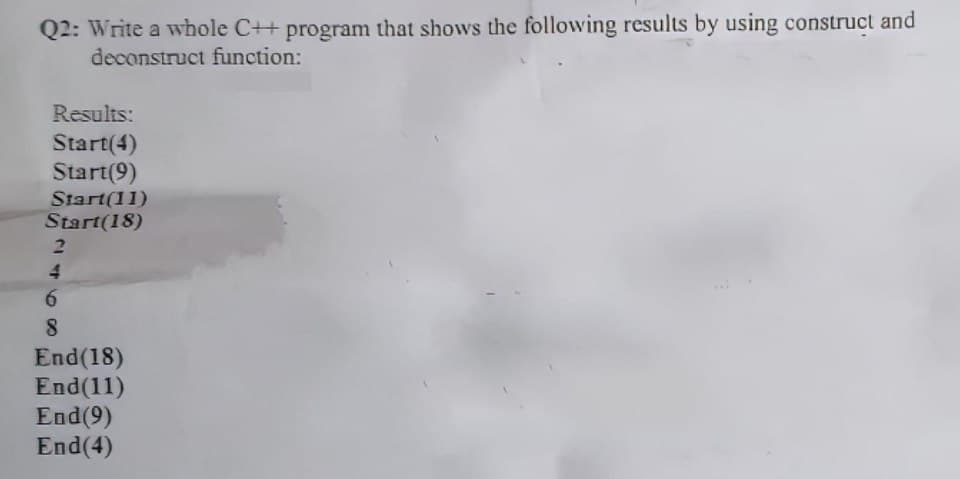
Q2: Write a whole C++ program that shows the following results by using construct and deconstruct function: Results: Start(4) Start(9) Start(11) Start(18) 2 4 6 8 End (18) End(11) End (9) End(4)
Q: How are sessions susceptible to being hijacked? Can anything be done to stop this from occurring?
A: Introduction: Session hijacking is a cyber-attack in which a vindictive programmer places himself…
Q: What does "predictive analysis" mean? Give a use example f
A: Predictive analytics is the use of data to predict future trends and events. It uses historical data…
Q: Each of the three units—the control, arithmetic, and logic—serves a particular function.
A: Arithmetic: The term arithmetic is used to describe the fundamentals of counting, measuring, and…
Q: What does "encapsulation" imply when used to object-oriented programming
A: Please find the answer below
Q: What does a data dictionary serve?
A: Please locate the solution in the following: A table that contains information on each of the items…
Q: When attempting to migrate their organisation to a cloud computing platform, businesses often…
A: Cloud computing is the online delivery of hardware and software by remote computers. These servers…
Q: Refer to the given brief system descriptoin and answer the questions (a-c) below using your…
A: Below I have provided the solution to the given subpart question
Q: Explain why deep access is preferable to shallow access from the standpoint of a programmer; do not…
A: Justify why deep access is like superior than shallow access from the standpoint of a programmer;…
Q: Identify the two key software application distribution channels. Discuss the advantages and…
A: In information technology: An application (app), application programme, or application software is a…
Q: Provide an example of how a challenge-response authentication system works. How much more secure is…
A: Given: To verify a difficult response, all you need is a question and an answer. The objective of…
Q: What is the Internet, exactly? Mention a few online applications. OR Describe the ways in which the…
A: The internet, also referred to as "the net," is a vast global network that connects various computer…
Q: What traits distinguish NoSQL databases?
A: Given: Dear student we need to explain about , What traits distinguish NoSQL databases.
Q: What advantages do both vertical and horizontal partitioning offer
A: Introduction: I won't go into the general benefits of partitioning since they can be discovered…
Q: Procedural programming and object-oriented programming are contrasted and compared. What character…
A: Basics: Object-oriented programming uses "objects" to store information and code as fields and…
Q: In computer programming, functions are vital since they are the fundamental building blocks of the…
A: Answer is
Q: What advantages do both vertical and horizontal partitioning offer?
A: The following is a list of benefits that may be gained from both vertical and horizontal…
Q: How does a cloud data breach affect cloud security? Below are some of the most prevalent defences.
A: A data breach is an occurrence in which the information contained inside the system is taken by the…
Q: A convenient method or instrument for providing computer-generated charts, diagrams, drawings, and…
A: Introduction: The field of computer science known as computer graphics is used to create pictures,…
Q: Which is a proper way to free the following dynamic array? double *sales = new double[ count ]; A.…
A: Explanation: In addition to dynamically assigning individual values, we can also dynamically…
Q: Please explain the benefits of employing user-defined functions as opposed to predefined ones.
A: Definition: 1. Users develop user-defined functionalities in accordance with their needs. 2. In…
Q: Give examples of the three most popular file management techniques.
A: Provide examples for the three primary file management techniques. Ordinary files, also known as…
Q: What is the difference between open source and commercial word processing/presentation software?…
A: Introduction A computer programme known as a "App" or "application software" enables users to do…
Q: How would you summarize the functions of each component in the kernel of a typical operating system?
A: introduction: The kernel of a typical operating system must be listed, along with a brief sentence…
Q: How can our online anonymity be protected?
A: The above question that is how can our online anonymity be protected is answered below step.
Q: In Python. Ask user to enter two float numbers. Using an infinite loop, ask the user whether they…
A:
Q: How may an individual's usage of the Internet assist them in meeting their health care requirements?…
A: Individuals use the Internet to improve their health in ways that are beneficial to them because the…
Q: What choices are there when it comes to getting software? Explain your perspective using concrete…
A: Introduction: A software system's core elements are referred to as its architecture, and the…
Q: Why must user-defined function prototypes be specified when a programme has user-defined functions
A: Please find the answer below :
Q: it preferable to hash a password saved in a file rather than encrypt it?
A: According to the policy we can only give the answer of first question, repost your remaining…
Q: What is the operation of the intrusion detection system?
A: Answer: Intrusion detection system An intrusion detection system (IDS) is a system that monitors…
Q: What does a Repository and Data Dictionary mean in terms of computers?
A: A repository is a location where data is stored. A data dictionary contains information about the…
Q: In order to defend and secure networks, firewalls are crucial. Remember to define the term and…
A: It is necessary to provide an explanation of the function of the firewall in terms of network…
Q: Q1 B// find the error and type and then bulid ST? #include "iostream" void main() 1 const…
A: There are many errors in the given c++ code:- The main blunder is in the fourth line of the code…
Q: How can I get access to Application Software? The most effective technique to convey your point is…
A: Introduction: Application software is made to assist with a wide range of functions, including…
Q: Can disabled individuals use the Internet? Which developing technology will benefit disabled…
A: People with little or no eyesight often benefit from the Internet. Due to the Internet, people may…
Q: Suppose a sequence of numbers was sorted in the following steps. Which sorting algorithm was likely…
A: The correct answer is given below with proper explanation Also demo code and output screenshot is…
Q: Why is hashing passwords preferable to encrypting them when storing them in a file
A: A cryptographic technique called hashing can be used to check the legitimacy and consistency of…
Q: What are the most essential aspects of data backup and recovery?
A: Introduction: It assumes a fundamental part to reestablish the data structure capacity with the goal…
Q: What make up a typical operating system's kernel components and how are they used?
A: Typical OS kernel components:- I/O Manager Cache Manager Object Manager Power Manager Virtual…
Q: What are the most important elements to keep in mind about data backup and recovery?
A: The most important thing is the speed and accuracy: To maintain track essential data and restore it,…
Q: What options are there in computer science for maintaining data integrity?
A: Introduction: The data developer must include aspects that improve the data's correctness and…
Q: What, in your perspective, does it mean to feel secure? Are there any physical security issues that…
A: Introduction: Safe" means not at danger. This isn't true. Everything and everyone is risky or…
Q: Give specific instances of session hijacking techniques. Such attacks need a robust defence.
A: Taking possession of a vehicle you don't own, such an aero plane, ship, or bus, is called hijacking:…
Q: What is the difference between open source and commercial word processing/presentation software?…
A: Given: A computer programme known as a "App" or "application software" enables users to do certain…
Q: What else should be considered about data backup and restoration?
A: Let's discuss what are the factors that need to be considered while doing data backup and…
Q: Computer science vocabulary includes phrases like Data Dictionary and Contrast Repository
A: Introduction: A repository is simply a hub for the storage and upkeep of data. A Data Repository is…
Q: Should the IT director answer to the company's president?
A: According to the information given:- We have to define the scenario where, Should the IT director…
Q: Assess the risks and benefits of cloud security from a security standpoint. Transitioning from…
A: Answer:
Q: Examine the many kinds of access control systems and how they vary. Identify the various types of…
A: Access control frameworks may be categorized into three groups: Discretionary Access Control (DAC),…
Q: What are the advantages of using the Internet for medical purposes as opposed to conventional…
A: The answer to the question is given below:
Step by step
Solved in 3 steps with 2 images

- Q3: Write a complete C++ program that contains the integer functions (main, funx and funy). The main function declares an integer (k), which is assigned a value using cin. Then print funx(k), where funx(n)=2*funy(n-1) if n >1 and funx(n)=1 if n1 and funy(n)=1 if nWrite a swap function, that swaps the values of two variables in main, but use pointers instead of reference parameters. WRITE IN C++In C programming, if the return type of a function is Void how can you implement assert statements? For example, Void ceasar(int n, char*x); //if char = c and n = 3 output == f how do i use assert statements as this does not work assert (caesar(3,c)==f);
- Q7/ Write a program in C++ that asks the user to enter two numbers and prints the sum, product and difference of the two numbers by using function (Where there are three functions, the first for addition, the second for multiplication, and the third for subtraction).Q13/ Write a program in c++ that asks the user to input two numbers. If the first number entered is greater than the second number, the program should print the message: "The first number is greater." Otherwise, it should print the message: "The first number is smaller." .By using functionsQ3 // Write a program in C++ that works as a calculator that performs operations (addition - subtraction - multiplication - division using functions to perform these operations and the command ( switch) to choose the type of operation
- What is the output of the following C++ program segment? Assume all variables are properly declared. for (j = 0; j < 8; j11){cout << j * 25 << " - ";if (j != 7)cout << (j + 1) * 25 - 1 << endl;elsecout << (j + 1) * 25 << endl;}In C++, please revise/fix the program below according to the instructions and all the criteria. I believe the problem is in int main(). Thank you. Instruction Write and test a function that returns a copy of its string parameter with no repeated characters. The functions ignore case when they compare letters. The functions return strings whose letters are upper case. Write 2 versions of the function: string remDups(const string& original); void remDups(const string& original, string& nodups); Suppose the original string is “Myrtle has big feet” The function returns MYRTLE HASBIGF Test the functions thoroughly. Criteria compile, run, test the test program compiles, runs, and calls both versions of the function without crashingthe test program tests the functions thoroughly function parameters and returns one function has one constant string reference parameter and returns a stringone function has one constant string reference parameter, one string reference parameter and…In C++, please write a program according to the instructions and all the criteria. Thank you. Instruction Write and test a function that returns a copy of its string parameter with no repeated characters. The functions ignore case when they compare letters. The functions return strings whose letters are upper case. Write 2 versions of the function: string remDups(const string& original); void remDups(const string& original, string& nodups); Suppose the original string is “Myrtle has big feet” The function returns MYRTLE HASBIGF Test the functions thoroughly. Criteria compile, run, test the test program compiles, runs, and calls both versions of the function without crashingthe test program tests the functions thoroughly function parameters and returns one function has one constant string reference parameter and returns a stringone function has one constant string reference parameter, one string reference parameter and returns void. function operations the function removes…
- Write a C99 function that includes the following sequence of statements:x = 21;int x;x = 42;Run the program and explain the results. Rewrite the same code in C++and Java and compare the results.Mark the following statements as true or false: a. To use a predefined function in a program, you need to know only the name of the function and how to use it. (1) b. A value-returning function returns only one value. (2, 3) c. Parameters allow you to use different values each time the function is called. (2, 7, 9) d. When a return statement executes in a user-defined function, the function immediately exits. (3, 4) e. A value-returning function returns only integer values. (4) f. A variable name cannot be passed to a value parameter. (3, 6) g. If a C++ function does not use parameters, parentheses around the empty parameter list are still required. (2, 3, 6) h. In C + + , the names of the corresponding formal and actual parameters must be the same. (3, 4, 6) i. A function that changes the value of a reference parameter also changes the value of the actual parameter. (7) j. Whenever the value of a reference parameter changes, the value of the actual parameter changes. (7) k. In C++, function definitions can be nested; that is, the definition of one function can be enclosed in the body of another function. (9) l. Using global variables in a program is a better programming style than using local variables, because extra variables can be avoided. (10) m. In a program, global constants are as dangerous as global variables. (10) n. The memory for a static variable remains allocated between function calls. (11)(Numerical) Write a program that tests the effectiveness of the rand() library function. Start by initializing 10 counters to 0, and then generate a large number of pseudorandom integers between 0 and 9. Each time a 0 occurs, increment the variable you have designated as the zero counter; when a 1 occurs, increment the counter variable that’s keeping count of the 1s that occur; and so on. Finally, display the number of 0s, 1s, 2s, and so on that occurred and the percentage of the time they occurred.



