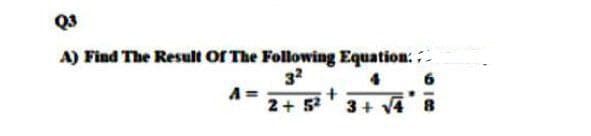
Q3 A) Find The Result Of The Following Equation: . 32 A= 2+ 5' 3+
Q: What is the most critical factor in a successful computer introduction?
A: Factors affecting computer performance
Q: Artificial Intelligence is defined as: O All of the options O Machine learning. Machines that's…
A: Answer is Machine Learning
Q: Assume that you have been assigned 192.168.111.0/28. 1. How many bits are borrowed to create the…
A: Given IP address:- 192.168.111.0/28 •/28 means 28 bit for network and 4 bit for host part. • It is…
Q: In Python, what exactly is inheritance?
A: Introduction Object-Oriented Programming: Object-Oriented Programming is based on objects. These…
Q: I need the answer and the c program code please. How many processes, excluding the original process…
A: #include <stdio.h> #include <stdlib.h> #include <unistd.h> int main(void) {…
Q: What is the difference between an interrupt service procedure and a normal subroutine?
A: Definition: A subroutine is a section of code within a bigger programme that performs a specific…
Q: The CPU suspends the current process to deal with an interrupt. Interrupt service is what it's known…
A: There are several steps you can take if an error occurs that causes process instances to be halted.
Q: When interrupting a computer, what is the difference between hardware interrupts and software…
A: Interrupts caused by hardware: Physical signals produced either within the microcontroller or via an…
Q: What are some of the advantages and cons of using TCP?
A: TCP stands for Transmission Control Protocol. It is a type of communication protocol which connects…
Q: hen video is transferred through a network, there is the possibility of redundancy. Techniques for…
A: Introduction: Encoding is the process of converting information or a specific grouping of…
Q: What methods would you use to assess a portable executable (PE) and determine whether it is…
A: Introduction: Malware is one of the topmost obstructions for the expansion and growth of digital…
Q: Create a form (html) to insert a new student as shown below. with mysql code
A: The answer is given below.
Q: Distinguish between disaster recovery and business continuity planning.
A: Introduction: Business Continuity and Disaster Recovery are Important.Business continuity describes…
Q: Given a same CNN model and its parameters, train the model with MNIST data using different…
A: Explanation: I have build cnn model using tensorflow library. I am solving this problem in google…
Q: Q2. Write C++ program, using loop statement to print the following pattern: 123456 78 87654321…
A: Step-1: Start Step-2: Declare two variable row = 12 and col = 8 Step-3: Start a for loop from i = 0…
Q: Describe the eof member function's purpose.
A: Introduction: When a file is created and saved, the special invisible character known as the eof…
Q: Summarize the Working with Data tutorials in your own words. Use critical thinking and an academic…
A: Introduction: The process of running Structured Query Language (SQL) in a database software is known…
Q: Describe the many sorts of Memories and how they are used.
A: 1. PROM ( PROGRAMMABLE ROM ) : PROM is used for storing permanent data in digital electronics. 2.…
Q: C
A:
Q: What are the different types of ROM memory?
A: ROM: ROM stands for Read-Only Memory. It is a memory that is non-volatile. When it is made, it is an…
Q: For what reason must the maximum packet lifetime include both the packet and its acknowledgements?
A: NOTE :- Below i explain the answer in my own words by which you understand it well.
Q: Interrupts are defined as follows: Describe in detail the different types of interrupts and why no…
A: Definition: An external device, such as a disc controller or a peripheral, sends a signal to the CPU…
Q: Three different C++ classes that can be used to build input streams are listed below.
A: Introduction: Input sequence for a stream from which data can be read. The keyboard is a common…
Q: 4. Examine the dendrogram: How many clusters seem reasonable for describing the data?
A: Let's see how to find the cluster in dendogram. Draw the vertical line through dendrogram. The…
Q: Which of the following is not the public ftp server that accepts file uploads? Question 25…
A: ftp.ieltf.org (First option), It is not the public ftp server that accepts file uploads.
Q: Distinguish between an adjacency list and a weighted graph representation.
A: In the below step we explained difference between adjacency list and weighted graph representation.
Q: Create the following table in your database with the following schema: Table: Sales | Column Name |…
A: Create a table Sales: CREATE TABLE Sales ( sale_id int, product_name varchar(255),…
Q: What does the term "critical consideration" imply? In terms of software development
A: Introduction: Consideration can manifest itself in a variety of ways. Factors from the past,…
Q: Write a program in Python that uses tkinter to display a window with 3 fields asking a user for…
A: Python provides the Tkinter toolkit to develop GUI applications. Now, it’s upto the imagination or…
Q: What precisely is an Interrupt? Explain why no hardware disruptions are expected by discussing the…
A: Hardware failures are predicted by describing the many forms of hardware failures: An external…
Q: Write SQL statements for following: Student( Enrno, name, courseId, emailId, cellno)…
A: Introduction This activity is utilized to select lines from a table (connection) that indicates a…
Q: Computer science Short answer discuss the advantages of frequent software upgrades.
A: Definition of Upgrading: We know that it is the process in which software product are replacing with…
Q: In what ways do hardware and software interruptions vary from one another, and when do they come…
A: Find the required answer given as below :
Q: a) What is the purpose of the assembler? What does it do with assembly language code? b) What is the…
A: I'm providing the answer to all questions. I hope this will be helpful for you..
Q: How do you make a temperature monitoring system?
A: Introduction: Temperature data is collected by thermocouple systems using a sensor, such as a…
Q: Datagram socket is the connectionless socket which uses FTP. Question 2 options: True False
A: The problem is based on the bascis of computer networks.
Q: Subtract the given number system. Show your complete and detailed solution. 1. 24325 – 1345 2. 32547…
A: Octal Number System has a base of eight and uses the number from 0 to 7. The octal numbers, in the…
Q: In what situations do hardware and software interruptions come into play, and how do they work…
A: Interrupt: An interrupt is a computer signal or a circuit that signals the computer to stop running…
Q: What part of a network can provide less tight security so that a web server can be accessed more…
A: Introduction: Generally, only limited transmissions will take place in the broadcast domains and so…
Q: Please give some examples on how to use the following in Python. Please do example codes Bool, int,…
A: Please refer below for your reference: Language used is python:…
Q: Evaluate: 20 %3 6.666 What will/be displayed/ by the following code? x457t4 y+2 coutee *wend None of…
A: Explanation: Here %(modulo operator) gives the result of a remainder when we perform division of two…
Q: This project requires the use of the employees.dat file (supplied). The record format in the file is…
A: Answer
Q: Convert in machine code for MIPS LW 55, 33(S2); Add R1, T3, S5;
A:
Q: What are some of the potential causes of a network outage?
A: Introduction: A network with several network components, both hardware and software, can fail owing…
Q: The predict() function allows us to predict the Y values that correspond to X values based on the…
A: As you can see, Linear model could be a quantitative output variable of y and for multiple predictor…
Q: Do the following: a. Build an AVL tree using the following 5 numbers: 8, 9, 10, 2, 1. You should…
A: Solution ::
Q: Write the body of an iterative function to compute n! for n 2 1.
A: Please refer below for code and output: According to company guidelines I am able to anser first…
Q: Ve feel like small digits are often under-appreciated, nost especially those of a 3-digit integer.…
A: let us see the code:- Hope this will help you
Q: Here is a Python function. def do_something(lst1, lst2): for element1 in lst1: for…
A: Please go through the below answer.
Step by step
Solved in 3 steps with 2 images

- Evaluate each of the following postfix/prefix expressions. Show your step-by-step solution to solving the expression. e.g. +2/*836 Solution: + 2 / * 8 3 6 + 2 / 24 6 + 2 4 6Evaluate the following infix expression using algorithm and choose the correct answer. a+b*c-d/e^f where a=1, b=2, c=3, d=4, e=2, f=2. i) 6 ii) 8 iii) 9 iv) 7q t Therefore, q ∨ t by ____

