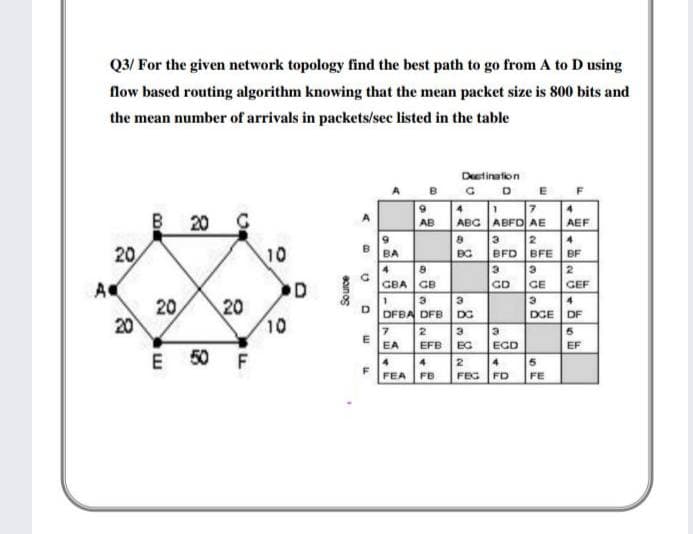
Q3/ For the given network topology find the best path to go from A to D using flow based routing algorithm knowing that the mean packet size is 800 bits and the mean number of arrivals in packets/sec listed in the table Detinalion BCD E B 20 7 ABG ABFO AE AB AEF 4. 20 10 BFD BFE BA BG BF 4 2. D GBA GB GD GE GEF A 20 20 20 10 DFBA DFB DG DGE DF EA EFB EG EGD EF E 50 F 4 2 4. FEA FB FEG FD FE onog
Q: Q1: Consider a computer network want to send data packets from router to destination router z. The…
A: Question 1. Consider a computer network that wants to send data packets from router to destination…
Q: 2. Write the necessary commands to configure Inter VLAN communication (Router on a Stick) for the…
A: According to the information given;- We have to write the command to configure Inter VLAN…
Q: Configure the given topology using RIP Routing Protocol. Also configure Static Route between Router…
A: Actually, IP stands for Internet Protocol.
Q: Consider delivering a series of packets from a sending host to a receiving host along a specified…
A: Define: The delays in processing, transmission, and propagation are all constant. This is due to the…
Q: Configure the given topology using RIP Routing Protocol. Also configure Static Routebetween Router 1…
A: Topology
Q: Consider the sender A transmits 12 data packets to B using stop wait protocol. If every 3rd packet…
A: Analysis:In stop and wait protocol, the data packets will be transmitted as follows:1, 2, 3, 3, 4,…
Q: Configure the given topology using RIP Routing Protocol. Also configure Static Routebetween Router 1…
A:
Q: Consider a router that transmits bits onto a transmission medium at the rate of 2 Mbps. Let the link…
A: Given: Bandwidth = 2 Mbps => 2 *106 bits/sec Distance = 3 km Speed = 3 * 108 meter/sec…
Q: Consider the network given below: R If flooding is used to send packets from A to E, then the total…
A: Introduction : Given , network diagramFlooding is used to send packet from A to E ,hop count for A…
Q: Suppose that a router receives simultaneously 3 packets (pkt1, pkt2, and pkt3) with length L1 = 1…
A: As per bartleby guidelines we have answered three questions and they are as follows.
Q: Consider a channel that can lose packets but has a maximum delay that is known. Modify protocol…
A: FSM of modified RDT 2.1 that includes sender timeout and retransmits:
Q: For the given network topology find the best path to go from A to K using flow based routing…
A:
Q: Q2/ For the given network topology find the best path to go from A to I based routing algorithm…
A: Your solution will be in next step
Q: A stage of an n x n banyan network consists of (n/2) 2×2 switching elements. The first stage directs…
A: Here we have given solution for the question asked. You can find the solution in step 2.
Q: Consider the network topology shown below with routers labeled A through F, inclusive. Each link is…
A: Answer is given below .
Q: Consider two hosts, A and B, connected by a single link of rate R bps. Suppose that the two hosts…
A: Given : 1)Two host A & B 2)Rate of transmission= Rbps 3) Length of the packet = L in…
Q: Q1: Use Any Routing Protocol To Build The following Network Topology (take screenshot to each step )…
A: Given:
Q: If delays are recorded as 10 bit numbers in a 50 router network, and delay vectors are exchanged…
A: Given that: If delays are recorded as 10 bit numbers in a 50 router network, and delay vectors are…
Q: Q3] Given the Adjacency matrix X shown below for a nine router interior routing network (the routers…
A:
Q: Suppose there are three nodes in a network, A, B, and C. A starts transmitting over the medium…
A: For CSMA/CD, nodes B and C have sensed the medium busy and will continuously keep sensing it until…
Q: Given a link with a maximum transmission rate of 34.1 Mbps. Only two computers, X and Y, wish to…
A:
Q: Suppose a message of length 10 Mbytes needs to be transmitted from the router to your home PC and…
A: Answer: This question from networking. and given message of length 10Mbytes and packet size 1000. we…
Q: Consider the network shown below, and Dijkstra's link-state algorithm. Suppose that Dijkstra's…
A: Given graph contains, Set of states= {A, B, C, D, E, F} Undirected weighted edges are present…
Q: Using the following topology, write the three routers R1, R2 and R3 routing table based on dynamic…
A: By using the following topology ,the three routers R1,R2 and R3 routing table based on dynamic…
Q: In a network, If P is the only packet being transmitted and there was no earlier transmission, which…
A: Question. In a network, If P is the only packet being transmitted and there was no earlier…
Q: 3.1 Consider a Go-Back-N ARQ protocol, whereby the window size is 6. Segments with sequence numbers…
A: Dear Student, According to Go-Back-N ARQ protocol if acknowledgment is not received for a single…
Q: Consider a message with 60 × 103 bits long, that is to be sent from a source to a destination, there…
A: Introduction
Q: Suggest the most appropriate routing methods to be implemented for a small network topology shown…
A: i give this question answer in next srep,
Q: Two endpoints are connected by a single link of rate R= 56kbps and the propagation speed along the…
A: The answer is...
Q: Consider two nodes (A, B) sharing the same broadcast channel of speed R =10Mbps. The propagation…
A: Given that, Nodes A and B are share same Broadcast address. Bandwidth of the channel= 10 Mbps…
Q: by a single link of rate R= 56kbps and the propagation speed along the link is 2* 10^8. a) If one…
A: The answer is
Q: A stage of an n x n banyan network consists of (n/2) 2 × 2 switching elements. The first stage…
A: Each stage has n/2 switching elements. Since after each stage we eliminate half of the network,…
Q: Suppose that KJ sends 3596 back-to-back packets, with each packet composed of 14,000 bits, to TA…
A: To find delay
Q: Dijkstra's algorithm is executed at node x, this will generate the forwarding table that router x…
A: Q1 answer> The different number associated to the links are cost or distance corresponding to the…
Q: A stage of an n x n banyan network consists of (n/2) 2 × 2 switching elements. The first stage…
A:
Q: Consider the network shown below, and Dijkstra's link-state algorithm. Suppose that Dijkstra's…
A: The above question is solved in step 2 :-
Q: Dijkstra's algorithm is executed at node x, this will generate the forwarding table that router x…
A: 1) those numbers represent the weights from node to node
Q: Suppose station X sends a message with 15 packets to station B using sliding window of size 4,…
A: Introduction :
Q: Q2/ For the given network topology find the best path to go from A to J using flow based routing…
A: Please check the step 2 for solution
Q: Consider two hosts, A and B, connected by a single link of bandwidth R bits per sec. Suppose that…
A: The answer is...
Q: Consider a packet of length L that begins at end system A and travels over three links to a…
A: Lets list down the given information for more clarity:Packet size = 1500 bytesPropagation speed Si =…
Q: Consider the network shown below, and Dijkstra's link-state algorithm. Suppose that Dijkstra's…
A: Link state routing is a technique in which each router shares the knowledge of its neighborhood with…
Q: Consider two hosts, A and B, connected by a single link of rate R bps. Suppose that the two hosts…
A: Objective: There are two hosts, A and B that are connected for transferring data through a single…
Q: Given a link with a maximum transmission rate of 34.1 Mbps. Only two computers, X and Y, wish to…
A: Given, =>Bandwidth(B) = 34.1Mbps =>Transmission start time (t) = 0 =>File X size = 19 MB…
Q: If there are N routers from source to destination, the total end to end delay in sending packet…
A: L-> number of bits in the packet R-> transmission rate
Q: Suppose that KJ sends 3596 back-to-back packets, with each packe composed of 14,000 bits, to TA over…
A: To find delay
Q: Configure the given topology using RIP Routing Protocol. Also configure Static Route between Router…
A: Actually, topology has given below:
Q: Consider two hosts, A and B, connected by a single link of rate R bps. Suppose that the two hosts…
A: The, answer has given below:
Q: Draw a space-time diagram similar to Figure 3.22 of textbook for the following problem: Sender is…
A: Answer:)
Step by step
Solved in 3 steps

- For the given network topology find the best path to go from A to K using flow based routing algorithm knowing that the mean packet size is 800 bits and the mean number of arrivals in packets/sec listed in the table.Consider a network with 4 links between two hosts where the maximum allowable packet size is 1000 bits; each link has a transmission rate of 2000 bits per second, except the second link has a transmission rate of 1000 bits per second. How long does it take to send 6000 bits from one host to the other? You may ignore propogation delay, assume there is no other traffic on the network, and assume that no routers drop packets due to queue length. Round your answer to two decimal places.Consider the GBN protocol with a sender window size of 4 and a sequence number rangeof 1,024. Suppose that at time t, the next in-order packet that the receiver is expecting has asequence number of k. Assume that the medium does not reorder messages. Answer thefollowing questions: What are the possible sets of sequence numbers inside the sender’s window at time t? Justify your answer.
- Consider the GBN protocol with a sender window size of 4 and a sequence number rangeof 1,024. Suppose that at time t, the next in-order packet that the receiver is expecting has asequence number of k. Assume that the medium does not reorder messages. Answer thefollowing questions: What are all possible values of the ACK field in all possible messages currently propagating back to the sender at time t? Justify your answer.0. AS1 has the following routing table, draw the network of AS’s that these paths imply: prefix path P1 AS2 P2 AS4 AS5 AS3 P1 AS4 AS2 P2 AS5 AS3 P1 AS5 AS2 Assuming AS 1 accepted all the paths advertised to it, what paths does AS4 advertise to AS1? What AS is P1 in? What about P2? AS5 no longer wants to forward packets destined for prefix P1 on behalf of AS1, but it is ok forwarding prefix P2, how would it change the paths it advertises to AS1? If AS1 sends a packet to AS4 destined for P1, what path will it take? How do we know AS4 won’t forward it back to AS1? If AS1 gets the following advertisement from AS4, P1 AS4 AS1 AS2 how would it update its table? Why?0. AS1 has the following routing table, draw the network of AS’s that these paths imply: prefix path P1 AS2 P2 AS4 AS5 AS3 P1 AS4 AS2 P2 AS5 AS3 P1 AS5 AS2 Assuming AS 1 accepted all the paths advertised to it, what paths does AS4 advertise to AS1? What AS is P1 in? What about P2? AS5 no longer wants to forward packets destined for prefix P1 on behalf of AS1, but it is ok forwarding prefix P2, how would it change the paths it advertises to AS1? If AS1 sends a packet to AS4 destined for P1, what path will it take? How do we know AS4 won’t forward it back to AS1? If AS1 gets the following advertisement from AS4, P1 AS4 AS1 AS2 how would it update its table? Why? NOTE: I would appreciate it if the solutions of the paths were hand-drawn so I can visualize it better.
- This elementary problem begins to explore propagation delay andtransmission delay, two central concepts in data networking. Consider two hosts, Aand B, connected by a single link of rate R bps. Suppose that the two hosts areseparated by m meters, and suppose the propagation speed along the link is smeters/sec. Host A is to send a packet of size L bits to Host B. d. Suppose Host A begins to transmit the packet at time t=0 . At time t= ?????? ,where is the last bit of the packet? e. Suppose ????? is greater than ?????? . At time t= ??????, where is the first bit of the packet?f. Suppose ????? is less than ??????. At time t= ?????? , where is the first bit of thepacket?In packet matching, one Echo packet may be the response for three request packets (Pattern: S1, S2, S3, E1), which of the following is ideal to represent the length of the connection chain? Question options: The average RTT of the three packets RTT betwee E1 and S1 RTT betwee E1 and S2 RTT betwee E1 and S3 The following figure shows the RTTs of all the packets collected from the beginning to the end of a connection chain, where Y axis represents the value of RTTs, and X axis represents the number of Send packets. How many hosts are compromised from the detecting host (also called sensor, count this host) in this case? Question options: 2 4 6 7For example, suppose your kid uses the school's wireless LAN to access the web by typing in www.google.com. Keep going with this hypothetical situation. (Or, you know, any other website that occurs to you right now) For clarity's sake, list the available routing protocols in the order in which they should be used.
- In this case, we will use the GBN protocol with a sender window size of 4 and a sequence number range of 1,024. Assume that, at time t, the next in-order packet that the receiver is awaiting has a sequence number of k, and that the receiver is expecting it. Assume that the medium does not rearrange the messages sent to and from it. Please respond to the following questions: What are the potential sequence numbers that could be contained within the sender's window at time t?Can someone help me with this question please? ASAP??!!! 6. Consider a packet of length L which begins at end system A and travels over three links to a destination end system. These three links are connected by two packet switches. Let di, si, and Ri denote the length, propagation speed, and the transmission rate of link i, for i = 1, 2, 3. The packet switch delays each packet by dproc. a. Assuming no queuing delays, in terms of di, si, Ri, (i = 1,2,3), and L, what is the total end-to-end delay for the packet? (10 Points) b. Suppose now the packet is 1,500 bytes, the propagation speed on all three links is 2.5×108 m/s, the transmission rates of all three links are 2 Mbps, the packet switch processing delay is 3 msec, the length of the first link is 5,000 km, the length of the second link is 4,000 km, and the length of the last link is 1,000 km. For these values, what is the end-to-end delay? (15 Points)In newer implementations, repeat ARP queries about a timed out entry are first sent unicast, in order to reduce broadcast traffic. What would have to happen to create a situation where the repeated unicast query for a given IP address fails, but a follow-up broadcast query for that same IP address succeeds?

