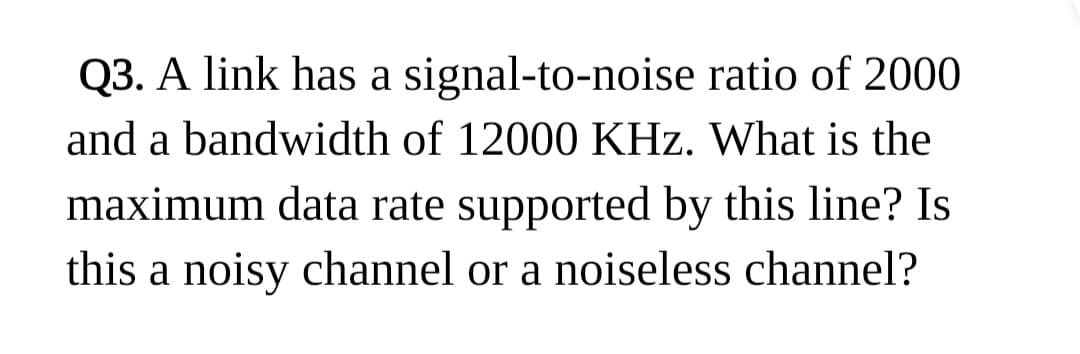
Q3. A link has a signal-to-noise ratio of 2000 and a bandwidth of 12000 KHz. What is the maximum data rate supported by this line? Is this a noisy channel or a noiseless channel?
Q: The getSelectedFile method of a JFileChooser object returns a File object. What exactly is this File…
A: javax.swing.JFileChooser is a specific part that permits the client to peruse the filesystem and…
Q: Take into consideration the reasons why "sudo" access is permitted. What are the benefits of logging…
A: Introduction: The "Sudo" command is used to give the currently logged-in user account root…
Q: The benefits of both Network+ projects should be emphasized. Make sure to include all aspects of the…
A: DEFINE: When applying for an IT job, you'll likely have to present a lot of CompTIA certification…
Q: 1): The prime factorization of 198 is 198 = 2 · 32 · 11 A): 2 · 3.3· 11 B): 2.33.3 C): 1.198 D):…
A: According to the guidelines, we can only answer first 3 questions please post the remaining question…
Q: Consider the following Java code fragment: int[] a {1, 6, 5, 3, 0, 2, 4); }; = int n = a.length;…
A: This question is based on control statements in Java.
Q: Which type of HTML element can have multiple values selected when the multiple="multiple" attribute…
A: Please refer to the following step for the complete solution to the problem above.
Q: Where do bytecodes vary from assembly languages?
A: Assembly language:- Assembly language is a low-level programming language that is used to write…
Q: what is a computer, anyway?
A: Introduction : An electrical device known as a computer processes data and performs calculations in…
Q: Can somebody explain to me why the output isn't showing how many questions the user got right or…
A: There are multiple inconsistencies in the provided code which are fixed in the provided one. Some…
Q: Just what is a DBMS, or database management system? Write out the benefits and drawbacks.
A: DBMS stands for database management system. It's a set of applications that manage database layout…
Q: Again, what kind of function concepts does Swift have? How does Swift differ from other languages in…
A: A function is a collection of statements that accomplishes a certain goal. It is given a name, and…
Q: Are identical MAC addresses feasible for many network interfaces? So, why is this happening, or why…
A: On a local network, no two devices should ever have the same MAC address. If that occurs, both…
Q: Can you post the code to solve these?
A: In this question, there are multiple parts to the python question. The first 3 parts are attended.…
Q: Where exactly can you find information that you can rely on while searching the internet, and how…
A: Search engine as an index for the web. The most relevant results will appear at the top of the…
Q: Which advantages does TDM have over other methods
A: Introduction Time Division Multiplexing( TDM) is a multiplexing fashion that allows the transmission…
Q: Which 32-bit constant do these instructions create? MOVEZ X9, 255, LSL 16 MOVEK X9, 255, LSL 0 O…
A: Answer: We need to write the what will be the value of after the execution of the given instruction…
Q: For what reasons are interruptions useful? I'm confused about the distinction between an interrupt…
A: Here is your solution step by step -
Q: haskell language -- with the help of the function "even", return those elements of the given input…
A: Note: In case of multiple questions we need to solve only 1 questions. Please find the solution…
Q: Pretend you are trying to get the Dean of your school to purchase a research program and provide a…
A: A software program, also known as a computer program or simply a program, is a set of instructions…
Q: Implement a stack S using two queues Q1 and Q2 so that operations PUSH (S, X) and POP(S, Y), where S…
A: One way to implement a stack using two queues is to use one queue (Q1) for inserting elements, and…
Q: Please elaborate on the need of a minimum frame size for CSMA/CD and provide your recommendation for…
A: CSMA/CD: CSMA/CD (Carrier Sense Multiple Access/Collision Detection) is a network protocol used in…
Q: Give an explanation for why CSMA/CD needs a frame size limitation, and what the absolute minimum…
A: CSMA/CD (Carrier Sense Multiple Access with Collision Detection) is a method used in Ethernet…
Q: Why should you use links in your presentation rather than keyboard shortcuts?
A: An electronic connection is a hyperlink. A highlighted word or picture in a presentation that may be…
Q: . Write a source code to implement the BFS algorithm for the graph in the below figure. Also, show…
A: The C++ source code of required program is as below: #include<iostream>#include…
Q: Can you explain what a ForkJoinTask is? Exactly how dissimilar are RecursiveAction and…
A: Here is the explanation:
Q: Using Java, write a function that calculates the factorial of a number N using recursive and…
A: Factorial of a number : The factorial of a non-negative integer n, denoted by n!, is the product of…
Q: An email address you offer someone will be transmitted from your ISP's outgoing e-mail server to the…
A: Simple Mail Transfer Protocol (SMTP) adheres to the push protocol. The email client connects to the…
Q: Is there a hard limit to how many times a branch operation may jump? Where would you put that longer…
A: Branching: A branch instruction in a computer programme causes the machine to start executing…
Q: please send me answer of this question immidiately and i will give you like sure sir. please answer…
A: Construct state space tree find profit of this using branch and bound techniques
Q: From a folder that contains 50 images, with each image labeled for a group they belong to {a,b,c}.…
A: Here is an example of how you could plot the histogram of labels and an image from each label group…
Q: 4) Compute the absolute and relative error with the exact value from question 1 and its 3 digit…
A: “Since you have posted multiple questions, we will provide the solutiononly to the first question as…
Q: Compiler and interpreter are two distinct tools.
A: Compiler: A compiler is a piece of software that converts high-level programming language code into…
Q: The separation of concerns is achieved throughout the analysis and design stages. One of the most…
A: Introduction: Separation of Concerns, or SOC, is a design philosophy that divides programming into…
Q: Which subset of microcontrollers specifies the processing speed that may be used in medical devices?
A: microcontroller: Microcontrollers may employ 4-bit words and 4 kHz frequencies to save electricity…
Q: There are many justifications that support the use of the undo tablespace as opposed to the backup…
A: Given: We have to discuss There are many justifications that support the use of the undo…
Q: Give examples of how the cloud's storage, processing power, and networking capabilities might be…
A: Introduction Cloud Computing: Cloud computing refers to on-demand access to computational services,…
Q: Please explain the concept of Optionals and how they are used in Swift programs.
A: In Swift, optionals are a way to represent the possibility of a value not being present. An optional…
Q: How are open-source projects different from traditional evolutionary prototyping?
A: methodologies that involve iterative improvements, but they differ in several key ways:…
Q: What is true about HTML heading levels and their usage?
A: In step 2, I have provided answer with brief explanation-------- In further steps , I have…
Q: The central processing unit (CPU) of a Nehalem processor is soldered onto the North or South bridge…
A: The above question is solved in step 2 :-
Q: What are the various data structures?
A: Introduction: A data structure is a group of a data type's "values" that have been arranged and…
Q: 10 Which ARMv8 instruction category performs multiply, add, or subtract for 32-bit operands? Quiet…
A: Given: We have to discuss Which ARMv8 instruction category performs multiply, add, or subtract for…
Q: It's not apparent what will happen if an incorrectly coded software is executed. What will happen…
A: frmProgram: FRM Program stands for Financial Risk Manager Program. It is a professional…
Q: To what extent is personal information protected, and what are the regulatory rules for handling…
A: Security breach notice laws, also known as information breach notice laws, require individuals or…
Q: Congratulations on your promotion to "Network level" guy. One of your first tasks as an employee was…
A: Basics: When sending data over the Internet, the Transmission Control Convention/Internet Protocol,…
Q: C program for implementation of KMP pattern searching
A: The Knuth-Morris-Pratt (KMP) algorithm is a string matching algorithm that is used to efficiently…
Q: Data transmission uses both periodic analogue signals and non-periodic digital signals; why?
A: In the following paragraph, you will find an explanation for this. There are two categories of data:…
Q: Exactly what is the function of the Open Daylight SDN controller's service abstraction layer?
A: Open Day light SDN controller: A free and open-source project developed in cooperation with the…
Q: Most machines can replicate both ways, from one register to another. The Memory Address Register…
A: Because of this, the majority of machines have a 2-way capability, meaning you may transfer data to…
question
Step by step
Solved in 2 steps

- Two channels, one with a bit rate of 100 kbps and another with a bit rate of 200 kbps, are to be multiplexed: a) How this can be achieved? b) What is the frame duration? e What is the frame rate? What is the bit rate of the link? And Please be clear, couldn't understand a bit from the last two answered1. Suppose, there are two channels to multiplex, one bits from each source and use TDM with 180Kbps and 190Kbps. Pulse stuffing is allowed if requires. What is the size of a frame in bits? (a) 1(b) 2(c) 4(d) Not available 2. Which can not be an implementation area of FDM?* (a) Cable TV (b) FM Radio Broadcasting (c) First generation cell phones (d)Air band radioYou are designing the Wi-Fi for a classroom of 20 students and all students are using Wi-Fi at the same time. The protocol efficiency is 40% and the channel utilization is 80%. Each students uses a throughput of 2 Mbps. What is the minimum PHY rate requirement for the radio in Mbps?
- 1. A pure ALOHA network transmits 200-bit frames on a shared channel of 200 kbps.What is the throughput if the system(All stations together)produces 100 frame per second.(Hints:44.5; 10.5) 2. what is the vulnerable time frame size of pure ALOHA?If the time unit is P then find it out.[Hints: 2P;0.2P]What is the total delay (latency) for a frame of size 78 million bits that is being sent on a same link with 9 intermediate devices having a queuing time of 83 μs and a processing time of 93 μs? The length of the link is 2000 Km. The speed of carrier inside the link is 2.8 × 108 m/sWhat are the differences between the following types of wireless channel impairments: pathloss, multipath propagation, interference from other sources?
- Earth to a distant planet is 9 x 10^10 m. A 64 Mbps point-to-point link using a stop-and-wait protocol for frame transfer has what channel utilization? Assume 32 KB frame size and 3 × 10^8 m/s light speed.explain and mention the difference between the following packet-switching using data gram and packet-switching using virtual circuits Selective-reject ARQ and Go-back-N ARQ internetwork and the Internetq2- What is the minimum number of bits in a PN sequence if we use Frequency Hopping Spread Spectrum (FHSS) with a channel bandwidth of B =4 KHz and Bss =200 kHz? Select one option: a. 6 b. 4 c. 5 d. 7 Clear my choice
- Use wireshark to capture packets on your network. Do some screen captures that illustrate the contents of ethernet, LLC, PDUs and mac frames.Consider a 10 km long broadcast LAN has 10^10 bps bandwidth and uses CSMA/CD. The signal travels along the wire at 2.5 x 10^8 m/s. What is the minimum packet size that can be used on this network? Correct answer will be appreciated , else downvoted.What are the differences between the following types of wireless channel impairments: path loss,multipath propagation, interference from other sources?

