Q3. Redraw with suitable modification in the same style given below after identifying errors in below DFD. (12)
Q3. Redraw with suitable modification in the same style given below after identifying errors in below DFD. (12)
Fundamentals of Information Systems
8th Edition
ISBN:9781305082168
Author:Ralph Stair, George Reynolds
Publisher:Ralph Stair, George Reynolds
Chapter6: Information And Decision Support Systems
Section: Chapter Questions
Problem 6SAT
Related questions
Question
100%
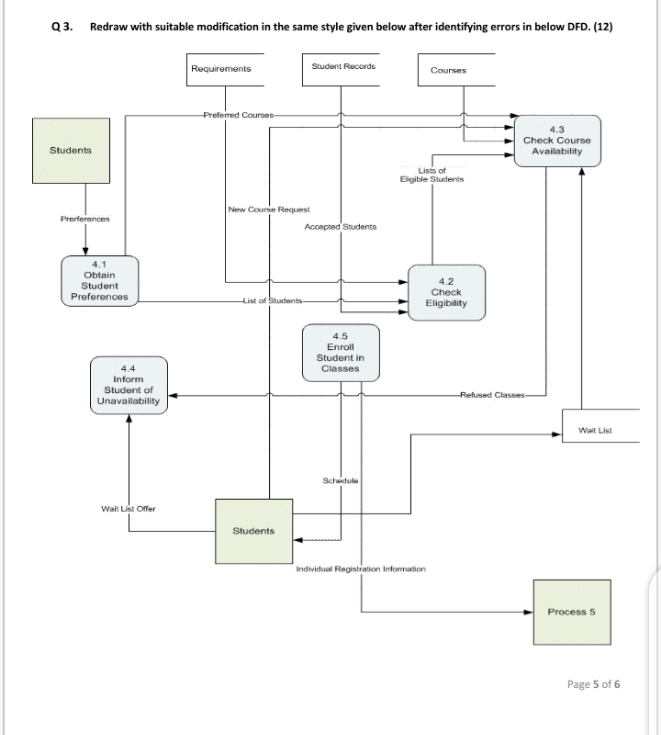
Transcribed Image Text:Q3. Redraw with suitable modification in the same style given below after identifying errors in below DFD. (12)
Requirements
Sudent Records
Courses
Prefered Courses-
4.3
Check Course
Students
Availability
Lists of
Eligible Students
New Counie Request
Prerferences
Accepted Students
4.1
Obtain
4.2
Student
Check
Eligibility
Preferences
List of Students-
4.5
Enroll
Student in
4.4
Classes
Inform
Student of
Unavailability
Refused Classes-
Wait List
Scheidule
Wait List Offer
Students
Inidividual Registratiori Information
Process
Page 5 of 6
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps with 6 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Fundamentals of Information Systems
Computer Science
ISBN:
9781305082168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning


Fundamentals of Information Systems
Computer Science
ISBN:
9781305082168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning
