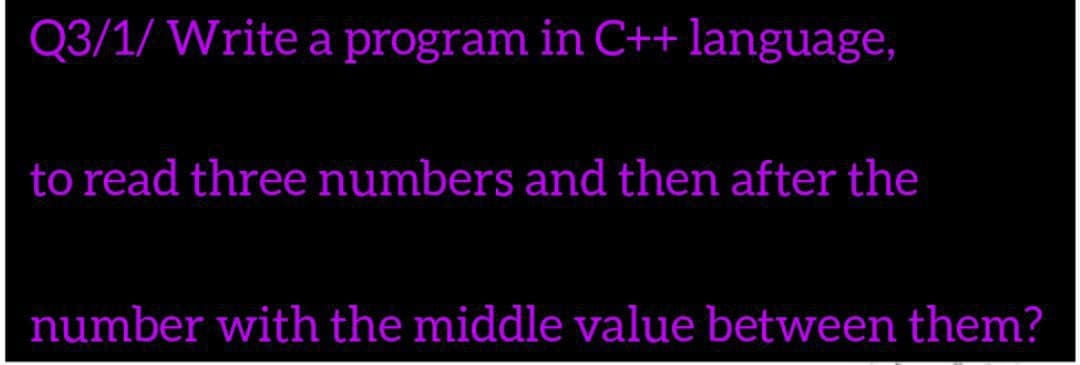
Q3/1/ Write a program in C++language, to read three numbers and then after the number with the middle value between them?
Q: In what ways is multifactor authentication used? What role does it play in protecting passwords from…
A: Introduction: MFA-Multi-Factor Authentication requires a user to submit two or more verification…
Q: Explain when law enforcement should be involved in an IRP or DRP operation, as well as the concerns…
A: Incident Response Plan: Incident Response Plan mainly focuses on the immediate response to an…
Q: what is the relevance of embedded systems in Smart Transport ,Agriculture and areas of home…
A: importance of embedded systems in Smart Transport - city transportation is an important part for…
Q: Explain the various data protection options available in MS-Excel. Why don't you include examples to…
A: Introduction: Routing is the act of moving from one page to the next one. A Single Page Application…
Q: Simultaneous integer multiplication is best suited for which type of program-level parallelism (data…
A: Introduction: Program-level parallelism is the process of decentralizing a single programme and…
Q: In the context of unsigned integers, what does overflow mean?
A: Unsigned numbers: Unsigned numbers are positive numbers. Unsigned numbers does not require an…
Q: Dissect the many types of computing resource failures.
A: Introduction: Component failures become the rule rather than the exception in large-scale networked…
Q: Describe four different interaction styles of your choice in detail.
A: Interaction styles: The four different interactions styles are as follows: Menu Selection Interface…
Q: The importance of wireless networks in emerging economies cannot be overstated. I's unclear why…
A: Introduction According to your question Wi-Fi is the wireless technology used for connect…
Q: Name and describe two ways for integrating IPv4 and IPv6 addresses in a single network.
A: Intro IPv6 is the most recent version of internet protocol which uses 128 bit addressing to find out…
Q: Using MATLAB draw the equation: U(theta)=cos(2theta) cos(3theta)
A: The following step provides the solution in MATLAB to plot a graph for the given equation…
Q: E-commerce has seen a significant spike in popularity. What are the primary causes of this…
A: Introduction: A method of conducting business using the internet is called e-commerce, sometimes…
Q: What does it mean to "fetch" an instruction?
A: Introduction: Fetch an instruction means to read the instruction from memory. The instructions of a…
Q: 51. Consider a game in which a player flips a fair coin three times. If all three coin flips have…
A: Hello student, hope you are doing well. The answer to the given question is attached below along…
Q: The efficiency of e-commerce has been boosted by two or more computer innovations.
A: Introduction: Companies may grow into new regions by using this distribution channel. E-commerce…
Q: How can the effect of each issue 1) Delay Latency, 2) Network Jitter, and 3) Packt Loss be minimized…
A: Introduction: Here we are required to explain how can the effect of Delay Latency, 2) Network…
Q: In computer programming ((1 + -2) * 3) = ? ( 3 * 4 ) % 3 + 2 = ?
A: Hello student hope you are doing well. Then answer to the question is attached below.
Q: Conduct a review of social media evidence-gathering techniques.
A: Introduction: The most typical technique of collecting evidence is to visit social networking…
Q: Make a list of the five database management functions. Explain the consequences of not fulfilling…
A: DBMS: A database management system (DBMS) is computing software that manages enormous amounts of…
Q: How does the Caesar Cipher outperform the mono-alphabetic cypher?
A: Introduction: we will look at how mono-alphabetic encryption is more secure than a Caesar cipher.
Q: To solve a risk situation, use the methods in Information Security Management. Computer science
A: Introduction: You'll learn about the many types of InfoSec policies and how to build and apply…
Q: Give one benefit and one drawback of the Microkernel operating system over the Monolithic operating…
A: Introduction: Memory management, file management, and process scheduling are all handled by the…
Q: So, what exactly does the term "reduced" imply in the context of a computer with a constrained set…
A: RISC (reduced instruction set computer) is a kind of microprocessor that is meant to execute fewer…
Q: Take it for granted that there isn't anything like relocatable software code. What methods can be…
A: introduction: Relocatable code is software that can have its execution address modified. In one…
Q: What factors contributed to the evolution of computer security into the current state of information…
A: Introduction: Computer security, often known as cybersecurity, refers to the safeguarding of…
Q: Could you perhaps explain the metrics involved in the software development process, if at all…
A: Introduction: A software metric is a quantifiable or countable measure of programme properties.…
Q: Is it true that non-parametric density estimators are correct?
A: INTRODUCTION: "YES ", It is true that non-parametric density estimators are correct.
Q: Is it possible to write an article comparing CPU Scheduling Algorithms?
A: Introduction: For comparing CPU scheduling techniques, a number of criteria have been proposed. Any…
Q: What do you name a programme that both interprets and executes high-level language instructions?…
A: Introduction: A high-level language is a computer language that has instructions written in English…
Q: Explain why learning assembly language programming is worthwhile.
A: Assembly language is important for the following reasons:
Q: WHY IS IT IMPORTANT TO HAVE AN O/S? WHAT HAPPENS IF A COMPUTER HARDWARE DOESNT HAVE AN OPERATIONAL…
A: INTRODUCTION: Operating systems : Operating systems (OS) are the programs that handle all other…
Q: How is a Wi-Fi adapter often linked to a smartphone's motherboard?
A: To define how the Wi-Fi adaptor is connected to the motherboard.
Q: The efficiency of e-commerce has been boosted by two or more computer innovations.
A: Introduction: Companies may grow into new regions by using this distribution channel. E-commerce…
Q: Is there a protocol that makes use of SSL or TLS to protect browser-to-webserver communications?
A: Introduction: Browser-To-Webserver Communications: A client-server system is made up of web browsers…
Q: Please use a Scanner to take a String input. Please Verify whether it belongs to one of the…
A: Step 1 : Start Step 2 : In the main method , declare the string findStr to store the pattern to be…
Q: It's difficult to tell the difference between the Internet and the telephone network.
A: Introduction: The Internet and telephone networks are the two networks that are utilised to…
Q: Computer Science What is the total number of addresses in IPv6 address scheme (give your answer in…
A: We need to answer questions regarding IPV6.
Q: Define a function named swap_values that takes four integers as parameters and swaps the first with…
A: Swap is a function that directly swaps values between two given variables of the same types.
Q: How can you tell whether an application is interfering with the output of a device? Is it possible…
A: Introduction: Overall performance, accessibility, and usability are all elements that contribute to…
Q: What is the difference between clear and completely associative cache? concepts.p
A: Introduction: Instead of constraining each memory address into a specific cache block, a fully…
Q: Exactly what is routeing and how does it function? Distinguish between two typical methods of…
A: Routers allude to interior directing tables to go with choices about how to course parcels along…
Q: Write a program in C++ to help Buddy (the sheepdog) calculate the average age of all his sheep. The…
A: Hello student, hope you are doing good. The code is attached below along with explanation and output…
Q: What exactly is normalization, and why is it required?
A: Given Question: What is normalization and why is it necessary?
Q: What are the five tools used to improve screen design and layout? Explain each of them independently…
A: Following are the following five tools used for a better screen design and layout: MockFlow: It is…
Q: 3. Iw $R1, 6($R3); Suppose we have values for register R1=5 and R3 = 5 and memory value at the…
A: Below is the answer to above question. I hope this will be helpful for you...
Q: Explain the Entity-Relationship model and how it works.
A: Introduction: They are also known as the ERDs or ER Models, and they use a preset collection of…
Q: Give a decision procedure (an algorithm) to determine if the set accepted by a DFA is cofinite (that…
A: Answer the above questions are as follows:
Q: Could you pls provide me an example of Data Parallelism?
A: Data parallelism alludes to situations in which a similar activity is performed simultaneously (that…
Q: What distinguishes an asynchronous bus from a synchronous bus?
A: Introduction Synchronous Bus: If the steps of the bus protocol are handled by a clock signal…
Q: 2. Write a method that takes any two nodes u and v in a tree T, and quickly determines if the node u…
A: We need method which will return whether u,v are descendants or ancestors.
Step by step
Solved in 3 steps with 1 images

- a. Write a c program that asks a user for an integer. Declare a variable num1. Let num1 = ++x; Display the values of x, and num1 b. Write a c program that asks a user for an integer. Declare a variable num2. Let num2 = x++; Display the values of x, and num2.a. Write a c program that asks a user for an integer. Declare a variable num3. Let num3 = --x; Display the values of x, and num3.b. Write a c program that asks a user for an integer. Declare a variable num4. Let num4 = x--; Display the values of x, and num4.short answers : c)Give an example of a common floating point arithmetic error due to the particular way in which floating point numbers are stored? d)Give an example of how when using C-strings and the functionstrcpy, things can go wrong.
- What is the output of the following C++ program segment? Assume all variables are properly declared. for (j = 0; j < 8; j11){cout << j * 25 << " - ";if (j != 7)cout << (j + 1) * 25 - 1 << endl;elsecout << (j + 1) * 25 << endl;}In C, Given a char variable c that has already been declared, write some code that repeatedly reads a value from standard input into c until at last a 'Y' or 'y' or 'N' or 'n' has been entered.Which of the following is not a reserved word in C++? (1) int include double const cin bool
- What does the following C++ program print? Why? #include <iostream> using namespace std; int a=480, b=380, c=42; void f(int x, int &y, int *z) { ++x; ++y; ++*z; } int main() { cout <<"a="<<a <<" b="<<b <<" c="<<c <<endl; f(a,b,&c); cout <<"a="<<a <<" b="<<b <<" c="<<c <<endl; }Q3: Write a complete C++ program that contains the integer functions (main, funx and funy). The main function declares an integer (k), which is assigned a value using cin. Then print funx(k), where funx(n)=2*funy(n-1) if n >1 and funx(n)=1 if n1 and funy(n)=1 if nwhat is the output of the following c++ statement: int a, b, c, d; a = 5; b = 4; c = (++b + a--); cout << a << " " << b << " " << c << endl;



