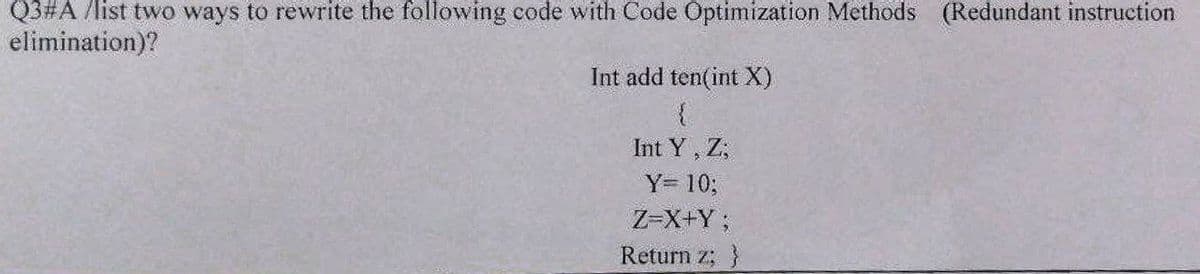
Q3#A /list two ways to rewrite the following code with Code Optimization Methods (Redundant instruction elimination)? Int add ten(int X) { Int Y, Z, Y= 10; Z=X+Y; Return z; }
Q: There are two categories of creatures that may be found in computing: viruses and worms.
A: Introduction: Human viruses are the inspiration for computer viruses. Viruses are dangerous…
Q: Tips and privacy features on how to make your IT work for you.
A: Introduction: Limit the amount of personal information you post on social media. Tips and privacy…
Q: How can different kinds of people get their hands on the same files? What are the advantages and…
A: Starting: Both index and direct file access are available in the present global system. It's also…
Q: When someone refers to a language that is used in assembly, what does it mean when they use this…
A: Launch: An assembler is a software that converts assembly language code into machine code. When…
Q: On the other hand, it is not always the case that computer databases and flat files or directories…
A: Introduction: A flat file is a collection of data kept in a two-dimensional database as rows in a…
Q: How do you keep track of the elements that have data in an array that is only half-filled?
A: Filled Array: An array is considered half-filled when there are indexes within the collection that…
Q: 9) What is the output of the following loop? int total = 27;
A: I have provided JAVA CODE along with CODE SCREENSHOT and OUTPUT…
Q: Give definition in your own words and provide an example 1. Hardware management- 2. Graphics User…
A: We need to define and give examples for: 1. Hardware management- 2. Graphics User Interface (GUI)…
Q: What are the benefits of e-commerce in computer science?
A: Introduction: The following are some of the benefits of e-commerce:
Q: What are the benefits of the edge flag algorithm?
A: The Answer is in next step
Q: It's important to understand what "computer programming" is and how it works. In order to choose a…
A: Computer programming: Computer programming is the process of instructing machines on what to do…
Q: 2. Suppose you have a group of people who need to be transported on buses and vans. You can charter…
A: According to the Question below the Solution: Output:
Q: Take the term "snapshot isolation" as an illustration of what a database for an airline would look…
A: Database System: When designing a database system for an airline, you might want to think about…
Q: Use Structured English for explaining non-systems analytical techniques.
A: It will be taught how to use structured English to describe processes that have nothing to do with…
Q: As the network administrator for your organisation, you have been given the job of constructing a…
A: Beginning: This query specifically addresses the computer network. We must define the topology of a…
Q: There are numerous issues that we confront in software development. Explain these issues in your own…
A: Here I explain about Software development then we discuss the problem in the software development.…
Q: What is the distinction between a Server computer and a Client computer?
A: Difference between server and client computer: • Client computer is a device or program to which web…
Q: 13) Write a method called allLess that accepts two arrays of integers as arguments, and returns true…
A: Step-1: StartStep-2: Declare two array arr1 and arr2, initialize with {45,20,300} and…
Q: What exactly is meant by the term "deployment of Web services"?
A: Answer : Deployment of Web Services means that to send or to make the perfect use of each and every…
Q: 01/ Context Free Grammar: E→E+T/T T-T*F/F F→ (E) /id BULID SLR TABLE and find if this string accept…
A: It is defined as a finite set of grammar rules is a quadruple (N, T, P, S) where : (i) N is a set of…
Q: What kind of an effect has the algorithm for removing files had on the operating systems used by the…
A: Introduction: Symbian is a discontinued smartphone OS and platform. [6] Symbian Ltd. invented the…
Q: What are the differences between the incremental and synoptic approaches
A: Synoptic approach: synoptic models presuppose comprehensive information for decision-making and…
Q: Which function do you use when you want to show the string value that an enumerator has?
A: String value of enumerator Enumeration is employed to define a collection of constant values within…
Q: File transfer utilities, downloading, and uploading are all defined.
A: Introduction: The File transfer utilities, downloading, and uploading:
Q: 5/ Select a right operation to type a valid expression in MATLAB: •,' ) 1 1 1. x = 509;
A: Given:
Q: What's the distinction between computer organization and computer architecture?
A: Solution: Difference between Computer Organisation and Computer Architecture The study of the…
Q: What are the three different types of backups that can be used in database recovery? Explain briefly…
A: Introduction: A database is just a way of storing data.
Q: Differences between a synoptic and an incremental strategy are discussed here.
A: Solution:: The following information is given: What are the differences between the synoptic and…
Q: It is the attribute of a control, much as it is the attribute of other controls, that decides…
A: Definition: Attribute Control Charts are a subset of control charts that were created with the goal…
Q: What is the significance of access limitations in today's society? Please include at least two…
A: Introduction: In a computing context, access control is a security approach that restricts who or…
Q: What are the several methods in which application software may be purchased or downloaded? Computer…
A: System specifications: Your machine must fulfil minimal hardware and software requirements in order…
Q: Q1/ Write the correct answer after executing the following commands: 1. If a(i)=eye(3), then…
A: Given: if a(i) = eye(3), then sum(a(i)) is .... eye(n) is a pre-defined MATLAB function which…
Q: Explain any two features that can enhance a hub's intelligence.
A: Answer: As a multiport repeater, a hub is similar to that. In a star architecture, for example, a…
Q: What are the two most compelling reasons for using layered protocols? Provide instances to support…
A: Layered protocol: A layered protocol architecture provides a conceptual framework for…
Q: What variables influence an organization's data privacy policies?
A: Introduction: Data privacy is a branch of data security involved in the proper handling of…
Q: Q3/estimate the results when you execute the following code: y-l Z=1 tl=x+y*z
A: I have provided PYTHON CODE along with CODE SCREENSHOT and OUTPUT-----
Q: Methods for developing and modelling software are not identical. It is essential to specify each…
A: Methodology for Software Development : A software process is the segmentation of development…
Q: When it comes to software development, what is
A: Solution - In the given question, we have to tell about prototyping in software development.
Q: Define special alert control with two examples
A: The above question is solved in step 2 :-
Q: When it comes to software development, what is prototyping?
A: Introduction: "Prototyping" is a term used in software development.
Q: 20)Explain, as simply and clearly as possible, what the following method does when passed an…
A: Java ArrayList class is like a dynamic array for storing the elements. The array has no size limit.…
Q: What are some of the most common Agile software development approaches?
A: Introduction: Agile software development is a collection of iterative software development…
Q: What do you mean by "sta
A: Semantic Rules That Aren't Changeable: These principles are frequently connected with the…
Q: In the process of developing a system, which of the following types of internal controls do you…
A: Internal Controls should be part of every organization's financial and operational rules and…
Q: 15) What method do you need to write, to implement the Comparable interface?
A: Java Comparable interface is used to order the objects of the user-defined class. The interface is…
Q: Explain how UNIX/Linux and Windows use the idea of least privilege in various ways.
A: Launch: Privileges are the authorization of computer resources that may only be accessed by the…
Q: What kind of an effect has the algorithm for removing files had on the operating systems used by the…
A: Overview: Symbian is a defunct mobile operating system (OS) and computing platform that was designed…
Q: What are the two most typical kinds of files that people use? What distinguishes these two file…
A: File management system: A file management system is used. For file management or maintenance, It is…
Q: Is a computer system characterised by any particular traits?
A: The word "system" may be abbreviated as "SYSTEM." The system is a connected and planned set of…
Q: 22) All classes in Java inherit methods from the class.
A: To perform a specific task some set of grammatical rules and vocabulary used for give instruction to…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- iv) Write a JAVA program to merge two sorted arrays into a single sorted array. Take the sample arrays given below and print the result in the output. The time complexity of the program should be O(N+M) where N and M are the sizes of both the arrays. int []arr1 = {1, 6, 10, 14} int []arr2 = {2, 4, 5, 11, 16, 19} Print the merged array in the output.Q#2 Write a recursive function zeroCount ( int a[ ], int s, int e) that receives an array of integers a [], a start index s, and an end index e. The function should return the number of zeros in that array between s and e. int zeroCount ( int a[ ], int s, int e); Trace your function given the following array and function call. Draw your steps. int a[ ] = {1, 0, 0, 5}; int zeros = zeroCount(a, 0, 3); language c++c++ Implement a function that recursively calculates the nth number in the Fibonacci sequence of numbers. The Fibonacci sequence starts at 0 and 1. Each number thereafter is the sum of the two preceding numbers. This gives us the following first ten numbers: 0,1,1,3,5,8,13,21,34, .... Input Expected output0 01 17 139 34
- 12. Consider the recursive function int gcd( int a, int b) int gcd( int a, int b){ if (b > a) return gcd(b,a); if ( b == 0 ) return a; return gcd( b, a% b); } How many invocation (calls) of the gcd() function will be made by the call gcd(72, 30)?I need help in 5: 5. Recursively Reverse a List Mke a recursive function that reverses a list. For example, given [1, 2, 3, 4], the function would return this list [4, 3, 2, 1]. It does not print anything. Instruction is below Practice writing recursive functions in python3 Make the five recursive functions described below in python3 by using the starter code recursive_functions.py. For each function, figure out how to solve it conceptually : write down the base case (when recursion stops) and how each recursive function-call moves towards the base case. The functions should not print anything (except you may add temporary print statements to help debug them). You can test your program by using the provided program test_recursive_functions.py. Don't edit the test program. Put it into the same directory (folder) with your recursive_functions.py and run it. It will import your functions as a module, test your functions, and tell you when each function is returning correct results. 1.…I need help in 5: 5. Recursively Reverse a List Mke a recursive function that reverses a list. For example, given [1, 2, 3, 4], the function would return this list [4, 3, 2, 1]. It does not print anything. Instruction is below Practice writing recursive functions in python3 Make the five recursive functions described below in python3 by using the starter code recursive_functions.py. For each function, figure out how to solve it conceptually : write down the base case (when recursion stops) and how each recursive function-call moves towards the base case. The functions should not print anything (except you may add temporary print statements to help debug them). You can test your program by using the provided program test_recursive.py. Don't edit the test program. Put it into the same directory (folder) with your recursive_functions.py and run it. It will import your functions as a module, test your functions, and tell you when each function is returning correct results. 1. Factorial…
- 4. Given the following recursive definitionseq(1) = seq(2) = 1seq(n) = 2 ∗ seq(n − 1) + 3 ∗ seq(n − 2)implement the corresponding program and use it to calculate seq(5).How many invocations are made to the function seq when calculating seq(5)?by using c++. How can I solve this? Kindly, no class, linked list, and pointers shall be used in this program. Kindly use only SELECTION, ITERATION, INPUT, AND OUTPUT, FUNCTION, ARRAY, AND STRING ONLY.C/C++ & MIPS The function ?add(?,?) for two positive integers 0≤?, and 0≤?, is defined as the following:?add(?,0)=?; ?add(?,?)=?add(?,?−1)Write a recursive version of ?add() in C or C++, then use this program to develop a MIPSprogram that gets as input two integers 0<? ≤255, and 0<? ≤255, and returns theresult of ?add(?,?) in $v1.Your deliverable should be the C/C++ code and the MIPS assembly function-code
- Please written by computer source Question 1: Suppose we wish to write a procedure that computes the inner product of two vectors u and v. An abstract version of the function has a CPE of 14–18 with x86- 64 for different types of integer and floating-point data. By doing the same sort of transformations we did to transform the abstract program combine1 into the more efficient combine4, we get the following code: Our measurements show that this function has CPEs of 1.50 for integer data and 3.00 for floating-point data. For data type double, the x86-64 assembly code for the inner loop is as follows: Assume that the functional units have the characteristics listed in Figure 5.12. **See last page for figures A. Diagram how this instruction sequence would be decoded into operations and show how the data dependencies between them would create a critical path of operations, in the style of textbook Figures 5.13 and 5.14. vmovsd vmovsd vmulsd vaddsd | | | |…In Python: Create one recursive function, rec_list(n), that takes in the user input n and returns an array of integers from 2 through n (i.e. [2, 3, 4, …, n]). Input:The input is an integer from the range 2,200 (inclusive). Assume that the input is always valid. Sample Output (if input is 20) rec_list(20)[2,3,4,5,6,7,8,9,10,11,12,13,14,15,16,17,18,19,20]1.The following is the C code that you need to implement for this lab: uint8_ t f(uint8_tn) return(n<2)?(n):(f(n-1)+f(n-2)); The main function can be assumed as follows: int main() uint8_ t x; x=f(???); return 0; Obviously, " ? ? ? " is representing a value used to test the algorithm! Is "f"recursive? a.No answer text provided. b.Yes c.no d.depends on whether it is in for main 2.First, make the code in the previous question an actual C program so that it can be compiled and it runs. Play with it so that you feel comfortable with the logic of the code. Then implement the code in TTPASM. Note that you need to preserve the actual C code structure, this means you cannot it into a non-recursive subroutine. Furthermoreall conventions discussed in class regarding subroutines must be followed. The idea is that I should be able to substitute f with my own code, and main should work. Or, I can substitute main with my own, and f should work. Attach the source code of your assembly…



