Q3| EVALUATIONS: Memory at address 0x00100250 contains the following 16 bytes of data: 00100250 58 89 02 10 00 01 23 45 67 ab cd ef 00 01 10 11 Q3.1 Show the contents of the %eax register after execution of these instructions: movl Ox00100250, secx 4 (%ecx), %eax movl Seax = Q3.2 Show the hex value of the seax register and state of the specified condition flags wwww after executing the instruction. .text xor! seax seax Seax = CF SF ZF OF Q3.3 Write another assembly language instruction (not using the xor instruction) that will get the same result as above. II II II
Q3| EVALUATIONS: Memory at address 0x00100250 contains the following 16 bytes of data: 00100250 58 89 02 10 00 01 23 45 67 ab cd ef 00 01 10 11 Q3.1 Show the contents of the %eax register after execution of these instructions: movl Ox00100250, secx 4 (%ecx), %eax movl Seax = Q3.2 Show the hex value of the seax register and state of the specified condition flags wwww after executing the instruction. .text xor! seax seax Seax = CF SF ZF OF Q3.3 Write another assembly language instruction (not using the xor instruction) that will get the same result as above. II II II
Chapter11: Operating Systems
Section: Chapter Questions
Problem 22VE
Related questions
Question
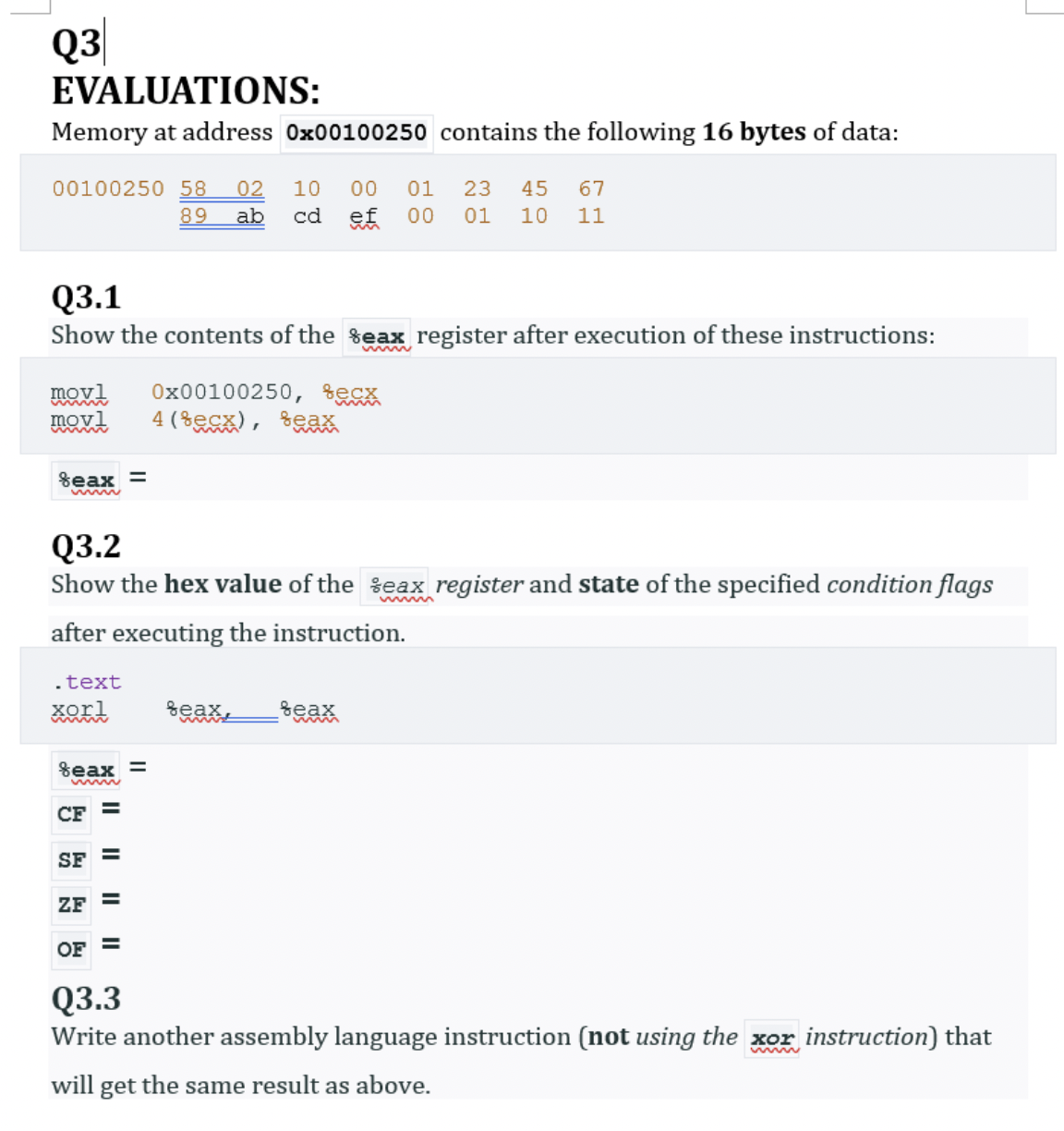
Transcribed Image Text:Q3
EVALUATIONS:
Memory at address 0x00100250 contains the following 16 bytes of data:
00100250 58
89
02
10
00
01
23
45
67
ab
cd
ef
00
01
10
11
Q3.1
Show the contents of the %eax register after execution of these instructions:
movl
Ox00100250, secx
4 (%ecx), %eax
movl
Seax =
Q3.2
Show the hex value of the seax register and state of the specified condition flags
wwww
after executing the instruction.
.text
xort
seax
seax
Seax =
CF
SF
ZF
OF
Q3.3
Write another assembly language instruction (not using the xor instruction) that
will get the same result as above.
II
II
II
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning