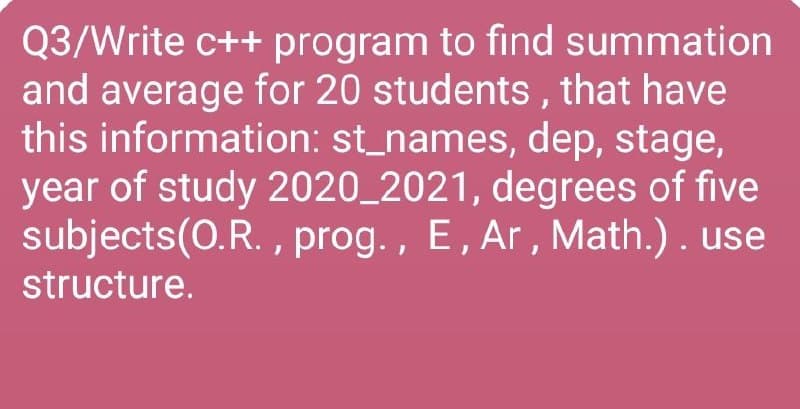
Q3/Write c++ program to find summation and average for 20 students , that have this information: st_names, dep, stage, year of study 2020_2021, degrees of five subjects(0.R. , prog. , E, Ar, Math.). use structure.
Q: What exactly is a Compiler?
A: Compiler: The compiler is a program that translates source code into an executable form.
Q: What are the benefits and uses of packages? computer science
A: Packages: A package is a namespace that organizes a collection of classes and interfaces that are…
Q: Explain why XML is extensible.
A: XML stands for eXtensible Markup Language XML was deigned to store and transport data It is similar…
Q: Why is the public-key method of encryption so crucial in internet commerce?
A: IN ELECTRONIC COMMERCE, ENCRYPTION THAT USES THE PUBLIC KEY METHOD IS VERY IMPORTANT : For…
Q: What are the most popular interior and outside routing protocols in today's networks?
A: Foundation: Its internet layer or network layer offers necessary addressing information to enable a…
Q: To demonstrate the notion, provide two examples of internal and external fragmentation. Utilize…
A: Fragmentation: Fragmentation is a problem in computer storage in which storage space, either primary…
Q: 2. Which is semi-decidable? One of the following sets is semi-decidable, and the other is not. Which…
A: The solution for the above-given question is given below:
Q: Which DBMS component is responsible for concurrency control?
A: Introduction: Concurrency control: Concurrency control ensures the serializability of transactions…
Q: Consider the experiment where a penny is flipped, a quarter is flipped, and a 6-sided die is rolled.…
A: In the below step you can find the complete explanation in handwritten.
Q: What is the definition of a popular website? What options are available to small enterprises if they…
A: Website: A group of interlinked and well structured Web pages that exist on the same domain is…
Q: phishing assaults on your network: how to prevent falling victim to their tricks In order to prevent…
A: phishing: Phishing is a sort of social engineering assault that is often used to obtain sensitive…
Q: The Apple Interface Builder in XCode is a complicated tool with many unique capabilities. What about…
A: Interface Builder is a product development tool for Apple's macOS operating system. It is required…
Q: What is the definition of the "Principle of Non-Repudiation"?
A: Introduction: The certainty that someone cannot deny the legitimacy of anything is known as…
Q: What makes Chrome OS computers utilize less internal storage than competing desktop operating…
A: Operating System (OS): OS is the term that acts as an interface between the hardware and the user.…
Q: Database recovery can be done both forward and backward.
A: Database recovery is required in the event of a database instance failure (which is then restarted)…
Q: What makes Chrome OS computers utilize less internal storage than competing desktop operating…
A: Operating System (OS): Operating System (OS): The word "operating system" refers to the software…
Q: are particularly useful with larger teams. Use case diagrams Free form diagrams O Network diagrams O…
A: Let's understand every diagram carefully so that we can know which digram is useful . Use case…
Q: What was the driving force behind the creation of programming languages for computers?
A: Introduction: Computer programming language, for example, is a language for displaying a certain set…
Q: NAME and EXPLAIN in DETAIL the six (6) roles performed by the TCP?
A: TCP: Networking your computers improves their capacity to communicate, and most computers are used…
Q: What are TCP/four IP's abstraction layers?
A: There are Four layers of The TCP/IP Model: Network access, internet, transportation, and application…
Q: fraud in computers: kinds and outcomes What can be done to stop cybercrime?
A:
Q: what are the last two letters ( pronunciation of ed) of these verbs in the box.( hoped, missed ,…
A: Among the words - hoped, missed, laughed, begged, robbed, smelled, ended, presented
Q: What are the possible consequences of a data breach in terms of cyber security? Explain
A: Introduction A data breach occurs when unauthorized parties get access to sensitive information…
Q: Which of the following option is correct about DBMS (Data Base Management System)? Choose an answer…
A: The data is collected from different sources. The raw facts and figures which are collected are…
Q: What is the definition of a popular website? What options are available to small enterprises if they…
A: Enterprise: A for-profit firm or corporation is known as an enterprise, however it is most typically…
Q: Photographs are stored in a database, and the design/structure we've chosen includes some really…
A: That method must be secured to protect all images from malicious actions. We must protect our files,…
Q: al, and technolo
A: Information system is a term used to allude to an organized assortment of symbols and cycles that…
Q: Why Do You Use a Linear Data Structure?
A: Introduction A linear data structure is a data structure in which data components are ordered…
Q: What are the dangers and repercussions of a cyber security breach for a company?
A: Introduction What are the dangers and repercussions of a cyber security breach for a company?
Q: Computer science What are virtual registers? What purpose do they serve?
A: Introduction: A virtual register is a set of fields that are layered on top of a memory, generally…
Q: Which programme loads executable code into the CPU for execution from main memory?
A: Introduction: The executable code is loaded into the programme.
Q: When is it OK to store data in traditional files?
A: Mostly Data redundancy problems occur from traditional files and Inconsistency. In these files…
Q: explain the types in the Interaction Design Pattern
A: The question is to explain the types in the Interaction Design Pattern.
Q: There is thorough coverage of iterated and non-iterated GET requests, authoritative and root server…
A: Initiation: On the Internet, the Domain Name System is known as "the phonebook." Humans may access…
Q: Describe basic C input/output functions. Name and describe standard input and output devices.
A: Hey, since there are a lot of questions, we'll start with the first one. Please only send us the…
Q: What's the difference between procedural and logic programming, and how do they differ?
A: Logic Programming is Declarative, rather that procedural or functional. • Logic Programming…
Q: What are the difficulties in analyzing a system? What are some of the components in examining a…
A: What are the difficulties in analyzing a system? challenges: While working on the system it is…
Q: What is the difference between keeping hashed passwords in a file and using a computer to store an…
A: Password Database: The user's password is concatenated with a static salt and a randomly generated…
Q: Following graph is representing a program, write down, which paths the required tests should cover…
A: That graph shows a program flow. There are some activities/paths or methods i.e A, B, C, D, E, F,…
Q: Describe the features of recursive functions.
A: Introduction: The following are the characteristics of recursive algorithms:
Q: Explain normalised form in a few words.
A: Introduction: The process of building a relational database in normalised form is known as…
Q: What is a port scan, exactly?
A: A port scan can help an attacker find a weak point : A port scan a network server displays which…
Q: Describe basic C input/output functions. Name and describe standard input and output devices.
A: Have been submitted, we will respond to the first one. If you have a particular question that you…
Q: What are the advantages of floating point number over integers.
A: Introduction What are the advantages of floating point number over integers.
Q: How would you describe technology?
A: Introduction: Technology is the application of scientific knowledge to the practical goals of human…
Q: Computer science What is network protocol? Explain the following network protocols (in your own…
A: Introduction: A protocol is a set of rules that govern how data is formatted and processed.
Q: One of the most significant differences between a cell phone and a PDA is that a PDA may be turned…
A: Introduction: In addition to waiting for calls, a mobile phone maintains time synchronisation and…
Q: Describe the relationships between items and how inheritance works
A: Introduction Inheritance is a feature of Object oriented programming languages.
Q: No such port Your uncle has given you a new computer monitor. When you try to connect it, none of…
A: Introduction
Q: Deployment diagrams show the hardware for your system.
A: Introduction: Deployment diagrams are nothing but the UML diagrams that helps in showing the…
Step by step
Solved in 2 steps with 1 images

- write a code in c++ to solve any question with any function an any value to solve using newton raphson method numerically and take screenshot contains the codePLEASE CODE THIS IN C AND NOT C++. ONLY USE IF/CASE AND USER-DEFINED FUNCTIONS. PLEASE DO NOT USE LOOPS,STRUC, AND POINTERS. PLEASE ONLY DECLARE AND CALL VARIABLES IN THE MAIN FUNCTION, EVERYTHING ELSE IS IN A DIFFERENT USER-DEFINED FUNCTION. PLS CHECK IF IT WORKS TOO.Plz solve the question using c programming without using the library # include stdlib.h. or string.h .. Only use # include stdio.h and # include math.h And printf, scanf, fout, fin.
- 4-write functions to write a C++ program for solving the following computational problem: a)-Find the smallest Fibonacci number greater than 1,000,000 and greater than 1,000,000,000.Q1: Write a value-returning function in c++, isVowel, that returns the value true if a given character is a vowel and otherwise returns false.In C++ 1. Declare, define, and test the following function to check for order by name:bool isSortedByName(const Student * sa, int size);2. Declare, define, and test the following function to check for order by ID:bool isSortedById(const Student * sa, int size);3. To print out a Boolean value as true or false, rather than 1 or 0, precede each with boolalpha:cout << "True is " << boolalpha << true << ", False is " << boolalpha << false <<endl;
- Please write the answer readable write the Explicit and Recursive function for the sequence(plz use f and f(x)) -7, 1, 13, 29, 49In c++ please with clear indentation thank you so much Write the simplest program that will demonstrate iteration vs recursion using the following guidelines - Write two primary helper functions - one iterative (IsArrayPrimeIter) and one recursive (IsArrayPrimeRecur) - each of which Takes an array of integers and its size as input params and returns a bool such that 'true' ==> all elements of the array are prime, so the array is prime, 'false' ==> at least one element in array is not prime, so array is not prime. Print out a message "Entering <function_name>" as the first executed statement of each function. Perform the code to test whether every element of the array is a Prime number. Print out a message "Leaving <function_name>" as the last executed statement before returning from the function. Remember - there will be nested loops for the iterative function and there can be no loops at all in the recursive function. For the recursive function - define one…Use c++ Use WinBGIm graphic library Requirements Answer in .cpp and .hpp Implement all the items in the picture below Example: Pacman, Ghost and Wall No, rectangle example Creative
- In C++ Even if a problem does not directly tell you to use a function, you should aim to do so regardless. 2520 is the smallest number that can be divided by each of the numbers from 1 to 10 without any remainder. What is the smallest positive number that is evenly divisible by all of the numbers from 1 to 20?Plz solve the question using c programming without using the library # include stdlib.h . Only by using # include stdio.h And printf, scanf, fout, fin.C++ What is operator overloading? Write a program to find the sum and difference of any two complex numbers by overloading '+' and '-' operator.

