I need the answer as soon as possible
Q: I need the answer as soon as possible
A: The answer is Option B, that is wont we?
Q: Learn about private and public-key cryptography, and how they are different. Is it possible to…
A:
Q: What examples do you have of domestic terrorist groups that utilise the internet? What tactics do…
A: The most probably internet propoganda is the most common use by terrorist organization which uses…
Q: How many keys are required for public key cryptography, and how many keys are currently in use?
A: The Answer is in step2
Q: Is it feasible to encrypt a message with both message secrecy and message integrity? What makes you…
A: Will be explained :
Q: Why is elliptic curve cryptography advantageous?
A: Given: Elliptic curve cryptography is a way of encrypting data using a public key. It's a…
Q: answer as soon as possible
A: Given : A'.B+A.B'+((B.C)+A)+B.C'
Q: Discuss the need for asymmetric cryptography in the current situation where computing power is…
A: Asymmetric cryptography is used where a public key can be shared with anyone gets used to encrypt…
Q: A more secure way to authenticate a user is to do multi-factor authentication by combining two or…
A: Given: Multi-factor authentication, which combines two or more of the elements, is a more secure…
Q: What is IS followin
A: int i = 1, x = 4;while (++i <= 10){ x++;}cout << x;
Q: i need the answer as soon as possible
A: The space complexity of a computer program is the amount of memory required by an algorithm during…
Q: I need answer as soon as possible
A: Answer :-
Q: WHAT ARE THE LIMITATIONS ON THE INTERNATIONAL ADMISSION OF CRYPTOCURRENCY?
A:
Q: IC
A: The I2C bus is a simple and flexible method of transferring digital data between two electronic…
Q: Are there any possibilities for the data and connections to be encrypted from start to finish? What…
A: Solution: We need to discuss end-to-end encryption and its benefits. End-to-end data encryption…
Q: as soon as possible
A: Given:
Q: What is the correct Answer???
A:
Q: What are some instances of domestic terrorist organizations that make use of the internet? What…
A: Introduction: International terror: violent, criminal actions perpetrated by or connected with…
Q: Which other methods, besides message authentication, are there?
A: Introduction: A message authentication code (MAC) is a brief piece of information used to verify…
Q: WHAT IS CRYPTOCURRENCY AND HOW DOES IT WORK?
A: Answer: In 2009, the term "cryptocurrency" was used to describe a wide range of digital assets,…
Q: Why are random numbers necessary for network security?
A: INtro Random numbers are numbers that occur in a series such that two characteristics are met: (1)…
Q: Is it possible to encrypt not only the data but also the connection from starting point to finishing…
A: Assemblage: Link encryption is a kind of communication authentication in which all data on both ends…
Q: ick
A: Given if (x > 10) means that the number is thenumber is greater than 0 *
Q: What is the shortcut?
A: Shortcut: Shortcut is the concept in Microsoft windows, it is a kind of pointer which indicate a…
Q: What is secret key cryptography, and how does it work? Please include a short explanation, such as…
A: Given What is secret key cryptography, and how does it work? Please include a short explanation,…
Q: Q-
A: Display: You can dock the Command window at the top or bottom of the drawing area, or you can have…
Q: have
A: given - I have_____ English
Q: es
A:
Q: I need the solution quickly please
A: Before going to the solution we should first understand what MATLAB is. MATLAB means MAtrix…
Q: To avoid all the problems caused by spam how they can be reduced?
A: Electronic mail or email is one of the simplest and easiest channels through which we can transmit…
Q: Who is responsible for ensuring the security of the messages?
A: Introduction: Best practises for message security.
Q: Provide an explanation of how salt is used in cryptography to make it more difficult to crack…
A: salt: Salt is used by users who keep their passwords the same. There is a possibility that the…
Q: How many keys are necessary to be produced if public key cryptography is used, and how many keys are…
A: When it comes to secure communications, cryptography focuses on procedures that enable only those…
Q: oon as possible
A: Time Complexity The amount of time it takes for an algorithm to run as a function of the length of…
Q: We met -
A: The answer is: We met at noon.
Q: Authentication in the digital era is a difficult problem to solve.
A: The phrases digital authentication and electronic authentication (e-authentication) are…
Q: answer
A: QDS: It stands for quantum dot display, is a device for display that works on quantum dots which can…
Q: How many keys are necessary if shared secret key cryptography is used?
A: Given To know about the number of keys used when shared secret key cryptography is used.
Q: How many keys are needed if public key cryptography is used?
A: The many keys are needed if public key cryptography is use will be explained :
Q: qu
A: Given What is Tw?
Q: Which encryption standard guarantees that data will not be altered either after it has been…
A: Encryption : There are three different states that data might be in when it can be encrypted: at…
Q: the cybertext with RSA
A: Given :- In the above question, the statement is mention in the above given question Need to…
Q: Which keys are there? explains everything?
A: Encryption, authentication, and authorization are examples of cryptographic functions that can be…
Q: IS at
A: Q
Q: For an organization with 60 users, how many symmetric keys would be required, if symmetric key…
A: Here, Four options are given.
Q: soon as
A: Code: #include<iostream>using namespace std;int main(){ int row, col, i, j, arr[10][10];…
Q: Using PKI, Ali encrypted a message using Yahya's public key. Which key is required to decrypt this…
A: PKI - stands for Public Key Infrastructure. Public key encryption or Asymmetric key encryption is…
Step by step
Solved in 3 steps with 1 images

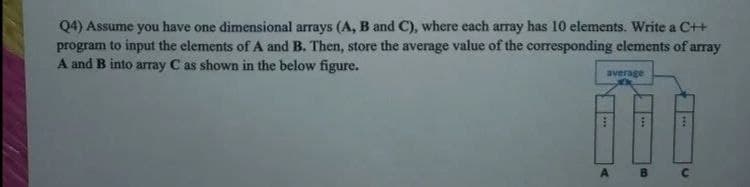
- (Electrical eng.) Write a program that specifies three one-dimensional arrays named current, resistance, and volts. Each array should be capable of holding 10 elements. Using a for loop, input values for the current and resistance arrays. The entries in the volts array should be the product of the corresponding values in the current and resistance arrays (sovolts[i]=current[i]resistance[i]). After all the data has been entered, display the following output, with the appropriate value under each column heading: CurrentResistance VoltsPart 4: JavaScript - Prompt Loop and Storing Input The next element of the program is to continue to prompt the user for input, storing each input into an array, until the user does not enter anything into the prompt dialog. First, you'll need an empty array. >> Add an empty array to the startup function. Name the array data. Declare the array as a constant array. Tip: Making our array a constant array prevents us from accidentally overwriting the entire array contents, but does not prevent us from adding data to the array. With the input storage ready, we can know work on our prompt loop. You will need to figure out how to continuously prompt the user for input using the prompt function, and either a while loop, or a do...while loop - either loop structure will work. You can ignore storing the input for now, and just focus on the prompt loop. >> Add code to the startup function to continuously prompt the user for input using either while or do...while, and the prompt…C++ QUESTION define an array with 10 elements, and enter the initial values from the keyboard. Compute the maximum value using function, finally print the result on the screen in the main function.
- char zetta[10] = {'B','A','D','G','U','Y','H','E',’L’,’P’}; Write a C programing code that will display the list of vowels and consonantsposition in the array, zetta.(5)Select the correct way to declare a two-dimensional array.A. int data[3][2] = {{3,4,3},{5,-1,12}};B. int data[3][2] = {{3,4},{3,5},{-1,12}};C. Neither.D. Both.Complete the following program should first fill in (by asking the user for input) and then list all the elements in an array: #include <_____>using namespace std;___ main(){int array[8]___for(int x=_; x<_; ___)cin>>______;for(____; x<____; ___)cout<<_____;return __;____
- c++ Below, write the code of the program that calls the desired functions in the main function and performs the desired operations. a) random (random number range should be set to be in the range of 5-15) 10 an integer with an element produces numbers and transfers them to an array called array A and displays them enter a function that prints. b) then this sequence takes the arithmetic mean of the elements of the sequence A,round the found average value to the nearest large integer and return it to variable A.enter a function that assigns and prints the variable A on the screen. c) then write a function that finds the factorial of the variable A value and assigns it to factorial A and prints it on the screenIn C++ float a[10] = {0.0, 1.1, 2.2, 3.3, 4.4, 5.5, 6.6, 7.7, 8.8, 9.9}; float *b = &a[2]; Write an expression that uses b to copy the 6th element of the array to the 3rd element. DO NOT use a in your answer.C++ Lexicographical Sorting Given a file of unsorted words with mixed case: read the entries in the file and sort those words lexicographically. The program should then prompt the user for an index, and display the word at that index. Since you must store the entire list in an array, you will need to know the length. The "List of 1000 Mixed Case Words" contains 1000 words. You are guaranteed that the words in the array are unique, so you don't have to worry about the order of, say, "bat" and "Bat." For example, if the array contains ten words and the contents are cat Rat bat Mat SAT Vat Hat pat TAT eat after sorting, the word at index 6 is Rat You are encouraged to use this data to test your program.
- C program, initialize two integer arrays, a[6] and b[6]. First print their elements in two rows, and then print them out in two columns. : Initialize the arrays with random integers in the range between 0 & 20, inclusiveprogram Credit Card Validator - Takes in a credit card number from a common credit card vendor (Visa, MasterCard, American Express, Discover) and validates it to make sure that it is a valid number (look into how credit cards use a checksum) - it's a C++ program so use #include <iostream> - And please use an array, use files, and use pointers in this program. -1. Write a program which reads 10 integer numbers into an array and display each of the valueinside the array. Then execute the following process:



