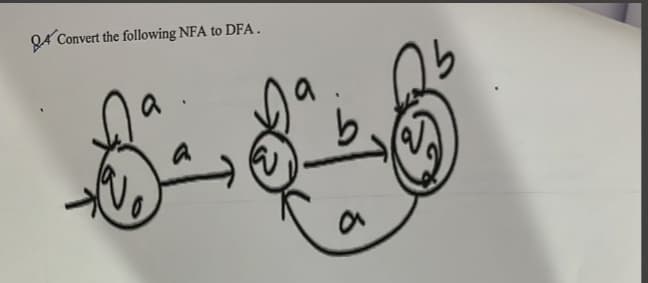
Q4 Convert the following NFA to DFA. ४
Q: How do customers and software developers work together?
A: The answer for the above question is given in the below step for your reference
Q: Shouldn't every known hazard category be included, arranged by frequency of occurrence, and…
A: all known threat types and order threats with URL evidence from more commonly encountered to least…
Q: To what resource may one go to learn the meaning of words like these? Exactly what is the…
A: The order of various operators with their operands is grouped according to precedence.
Q: How do customers and software developers work together?
A: Why is collaboration so important?We are aware that software engineers collect requirements and…
Q: 2. NxN Multiplication Table by CodeChum Admin Ask the user to input an integer n and print the…
A: To create a program to print a multiplication table for an integer n, you can use a looping…
Q: Question 9 2. Draw a finite automate that ends in 010. Additional Question: Do we typically…
A:
Q: Write code for given algrithm.
A: Sudo Code for the given algorithm:- Open a new spreadsheet Create the header row in every worksheet…
Q: Question 6 You must give a word count for any question with a maximum word limit. This question…
A: Understand the problem and gather information: Read the question carefully and make sure you…
Q: Why is the technique of "store-and-forward network" no longer used in general communications? Also,…
A: 1. A computer network refers to interconnected computing devices that can exchange data and share…
Q: When would a network administrator want to use a static route?
A: Static routing Static routing is suitable for networks with only a couple of routes, like a home…
Q: 14. Let R₁ and R₂ be relations on a set A represented by the matrices M-00--010 and MR₂ = MRI = Find…
A: In this question we have to Find the matrices representation for the following combinations of R1…
Q: I'm curious as to the steps necessary to begin utilizing cloud storage.
A: Cloud storage is a term that originates from the field of computer science and describes the process…
Q: One way to get into a network is for malicious data to be rerouted over virtual local area networks…
A: Introduction: A virtual local area network (VLAN) splits off certain groups while sharing the actual…
Q: Compare and contrast a three-tier and a two-tier application architecture by describing the…
A: In a multi-tiered application, the different parts of the application that do different things are…
Q: Let B(x) = "x gets a biscotti". Which statements below mean "Either everyone gets a biscotti or no…
A: Answer: The other statements are not equivalent to the statement "Either everyone gets a biscotti or…
Q: Provide a few examples of how you've taken control of a session before. To what extent can you…
A: Regarding the defense against session hijacking attacks, there are a few techniques that can be used…
Q: Write pseudocode to To insert ITEM after node NODE in a singly linked list START?
A: It is the simplest type of linked list in which every node contains some data and a pointer to the…
Q: elaborate on the significance of architectural design in the production of software.
A: 1. Programming is the process of creating a set of instructions that tells a computer how to perform…
Q: What should be the correct code below with the same problem? import math # Initialize the…
A: The Python code is given below with output screenshot
Q: make pseudo code to invokes proc network to compute the closeness centrality based on an undirected…
A: Answer: We need to write the pseudo code for the invoke proc network so we will see in the more…
Q: Spending more time on social media can ultimately benefit you. Key issues that need to be…
A: Autonomous computing in the cloud refers to the use of artificial intelligence (AI) and machine…
Q: Describe the functionality of one of the cache protocols.
A: Given: Describe one of the cache protocols in short. Answer: I'll talk about the MESI Protocol. The…
Q: Why is "scrubbing" so crucial in the context of RAID systems, and what does it relate to exactly?
A: Scrubbing Scrubbing data is a method of error revision. It looks for problems with the main memory…
Q: 2.Find the ronte with mininum cast in the fallowing figees. 10/ 12 8
A: Given graph contains, Set of vertices= {A, B, C, D, E, F, G, H, I, J} Source vertex= A Destination…
Q: Provide a few examples of how you've taken control of a session before. To what extent can you…
A: Depending on location and vector, attackers may hijack a user's session. Examples of session…
Q: Complete the Method to display the remaining elements during the binary search. public void…
A: Complete the Method to display the remaining elements during the binary search. Introduction: In…
Q: Describe the functionality of one of the cache protocols.
A: Provide a summary of one of the cache protocols. I will cover MESI Protocol: The MESI Protocol is…
Q: Between the OS and the user's program, two highly distinct images of the virtual machine are…
A: Answer is
Q: Take a database used by airlines and apply the concept of "snapshot isolation" to it. Is it fair to…
A: INTRODUCTION: Isolation in a Snapshot: Using row versioning, snapshot isolation circumvents most…
Q: Conference Planning The following table shows a training company's workshops, the number of days of…
A: Code for an application that lets the user select a workshop from one ListBox and a location from…
Q: the following Consider a binary classification with training data. Each data is described by 3…
A: To find the best attribute for the root node using the entropy method, we first need to calculate…
Q: What sort of a function does MVC play in relation to the whole process of building web applications?…
A: MVC, or Model-View-Controller, is a design pattern that is commonly used in building web…
Q: What are the key differences between a top-down and bottom-up strategy when it comes to protecting…
A: Answer is
Q: An undirected, connected graph with least weight edges is a subgraph that contains all vertices.…
A: A connected, undirected graph with minimal weights has a subgraph called a minimum spanning tree…
Q: What are the main ways in which the distinction between Web Services and Service-Oriented…
A: SOA architecture It divides a large software programme into service components that connect over the…
Q: What are the advantages and disadvantages of beginning a data modeling project using a packaged data…
A: A data model aids in a database's conceptual, physical, and logical architecture. Though the initial…
Q: Describe the differences between the two-tier and the three-tier application architectures. Which of…
A: In a multi-tiered application, the program's functionality is divided into distinct functional…
Q: Exercise 1.28 You are asked to write a C program to concatenate the binary formats of two given…
A: Here is one way you can write a C program to concatenate the binary formats of two given…
Q: Using the "Triad" at CIA. Please provide an example where I is more crucial than C. A justification…
A: Let's check the response: Introduction:- The confidentiality, integrity, and availability (CIA)…
Q: ompare and contrast the benefits and drawbacks of employing agile approaches throughout the system…
A: Agile approaches to system development are characterized by an iterative, adaptive process that…
Q: I'm getting an invalid syntax error
A: The correct java code is: import java.util.Scanner; public class LabProgram {public static void…
Q: This conversation is going to touch on a few different subjects, including mobile devices and…
A: cellular devices: A mobile device is any kind of portable computer. Many of these gadgets can fit in…
Q: Given the following code int num_1= 4, num_2= 8; double num_3=5; num_3=num_3/10+num_1/4;…
A: Find the output of the given Code statements. About the given code: Variables: Integers: num_1 = 4…
Q: Describe a fictitious login management scenario in your essay. Make a list of all the many methods…
A: In a fictitious login management scenario, a user would first need to prove their identity before…
Q: use page view while viewing your notes. Explain. Just answer in a couple of sentences.
A: SummaryPage ViewWhen a page of a website is loaded by a browser, the page is displayed. It is also…
Q: Think about the significance of wireless networks in developing countries. So why are some companies…
A: According to the question, WiFi networks (wireless communication) offer many more commercial…
Q: Different approaches have been presented for a processor that can decode encrypted data and system…
A: A central processing unit (CPU), often known as a main processor, central processor, or simply…
Q: Define Trigger and write a PL/SQL code for creating a trigger that can be triggered when the table…
A: We will talk about PL/SQL triggers in this chapter. Triggers are stored programmes that are launched…
Q: An exhaustive and in-depth analysis of the operation of the Domain Name System (DNS), including…
A: Please find the detailed answer in the following steps.
Q: List a handful of the messaging programs that are now most widely used. Do they adhere to the SMS's…
A: There are most popular messaging techniques the people are using in today's world in that most of…
please answer with proper explanation and step by step solution. i will give upvote for proper answer.
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

- Draw the ε-NFA from transition table below and convert it to its equivalent DFA State/Σ ε a b c -> p {} {p} {q} {r} q {p} {q} {r} {} r* {q} {r} {} {p}Given the NFA shown in FIG. 1(a), convert it to its equivalent DFA, and draw the DFA's state diagram. Provide detials.Please convert the below CFG into PDA. Σ = {a, b}.

