Q4: Evaluate the following postfix expression using stack. a) 6,9,3, /, ^, 12, /, 13, -, 2 ^
Q: To minimise access latency, buffers are used between different layers of memory hierarchy. List the…
A: Start: L1 cache memory is referred to as "level-1" cache memory, and it is often incorporated into…
Q: Pretend that a client can retrieve a file from a remote server at a known address using UDP. The…
A: UDP : The transport layer protocol User Datagram Protocol (UDP) is a connection-less-oriented…
Q: What is the default order by command value?
A: NOTE :- Below i explain the answer in my own words by which you understand it well. ASC is the…
Q: Which of these connections is false? A) A link to submit a form without a submit button B) A link to…
A: To solve this problem, we need to find the option that has a statement of deceptive behavior of a…
Q: Problem 5: A bi-directional associative memory has the following paired bipolar patterns & = (1, -1,…
A: Bi directional associative memory is a learning algorithm. Y=W. X given input vectors X and output…
Q: What are the four benefits of SQL?
A: Answer the above question are as follow:
Q: Discuss the social and ethical issues of integrating and utilising information technology in…
A: Introduction: The social and ethical implications of utilizing and implementing information…
Q: What would happen if either the AS (authentication server) or TGS (ticket granting server) goes…
A: Answer :
Q: What is the difference between hashing passwords stored in a file and saving them in a password…
A: Introduction: An encryption technique changes data in a database from a readable state to a…
Q: 26 Emphasizes the integration and sharing of data through-out the organization or at least across…
A: The database approach is said to be an improvement on the shared file solution as the use of a…
Q: What is the function of a computer's operating system? Identify a number of functions that this…
A:
Q: Define a Racket function 'sign', which returns -1 for negative inputs, +1 for positive inputs, and 0…
A: #lang racket/base (define (sign x) (cond [ (< x 0 ) -1] [ (> x 0) 1 ] [ else 0])) (sign…
Q: What is the difference between hashing passwords saved in a file and savin them in a password…
A: Justification: Validating passwords using hashing is a good idea. Even if an attacker receives the…
Q: Computer science What is the objective and major use of the GROUPING SETS subclause?
A: Introduction What is the objective and major use of the GROUPING SETS subclause?
Q: How would you address the issue of false sharing that can occur?
A: Basics : False sharing is a debasing usage design that might emerge in frameworks with appropriated,…
Q: What are the principles of programming language and how do you describe implementing subprograms in…
A: programming language: Orthogonality or simplicity, available control structures, data types and data…
Q: In computer architecture, what is the Extended form of MSI?
A: Introduction: The MSI file format is a package file type for Windows installers. Its name is derived…
Q: Create a flowchart and a pseudocode for resending an e-mail message that failed to be delivered.
A: Flowchart is a step by step process in which all the program is represented diagram with sequence of…
Q: PLEASE SIMPLIFY PLEASE!!!! truth table, simplified equation, and logical diagram. Show your…
A: Please refer below for your reference:
Q: algorithms
A: According to the question, we have to find the values of n for which n < 50*log2n So, we have to…
Q: Defineanomaly? What are the odds of discovering three outliers in a database? Discuss the…
A: This question discusses the likelihood of finding three outliers in a database and the ensuing…
Q: The intent of the Façade pattern is to provide a unified interface to a set of interfaces in a…
A: Ques: The intent of the Façade pattern is to provide a unified interface to a set of interfaces in a…
Q: The following is an instance of the conjunctive normal form (CNF) problem. (x1 V x2 V x3) ^ (x3 V…
A: Construct a graph G containing k clusters, each with a maximum of three nodes. A clause in…
Q: An open or non-hierarchical mesh network is one in which all nodes communicate with one another in a…
A: When employing a mesh network, nodes are connected to as many other nodes as possible directly,…
Q: cyber security dangers that you will be anticipating and planning for when you design a complete…
A: Introduction Cybersecurity danger refers to the likelihood of your company being exposed to or…
Q: Computer science what category of attack is a DoS attack an example? Group of answer choices 1.…
A: Introduction: what category of attack is a DoS attack an example?Group of answer choices1.…
Q: To add a new element to a list we use which Python command? A. list1.addLast(5) B.…
A: For adding a element in list append method is used. Also, insert and extend method is for adding…
Q: In general, computer experts advise increasing the computer's Random Access Memory (RAM) when the…
A: The following is an evaluation statement: Yes, having additional RAM will improve performance. It…
Q: Create a flowchart for the SWITCH sta
A: The switch case statement permits us to execute one code block amid many alternatives.Switch…
Q: What's the distinction between IP and MAC addresses?
A: Introduction: It is a special address that allows a device connected to the internet or a nearby…
Q: Identify various information security protocols/ policies (manual and automated) deployed in a…
A: There are various information security protocols/ policies that are deployed in a healthcare…
Q: What are the main characteristics of an ideal cryptographic hash function, and how do you define…
A: Introduction What are the main characteristics of an ideal cryptographic hash function, and how do…
Q: PLEASE SIMPLIFY THIS BOOLEAN ALGEBRA AND MAKE LOGICAL DIAGRAM y = A'C' + B'C'D + BC'D' + A'BD +…
A: Given Boolean expression is y = A'C' + B'C'D + BC'D' + A'BD + ACD' It has total five input symbols…
Q: You are to write a boarding system for a Cruise ship in java. The system will print a menu with…
A: Step 1 Algorithm: Start Create a class named Ship with name and year as its attributes Implement…
Q: Write the corresponding productions to the following context-free grammar G = ((S), (a, b}, S, P) of…
A: Below is the answer to above. I hope this will be helpful for you...
Q: From (Kali Linux) exploit (windows XP) by cracking password, give two useful information from…
A:
Q: e five risk-control strategies are listed and briefly described
A: Risk: Risk is defined as the likelihood of defining anything that will go wrong as a result of any…
Q: PYTHON CODING Find the Closest Point to the starting point We want to use the formula below to…
A: Try to iterate a for loop in each point of the remaining points list. Find the distance between the…
Q: As a computer scientist, how would you define magnitude?
A: The representation of a number's magnitude (decimal) in computer science is referred to as the…
Q: What are the different datatypes that may be used in C?
A: Intro Whenever a variable is defined in C, it has to be associated with a certain data type. This…
Q: Information technology What aspects should you consider while choosing a database management…
A: Introduction: A Database Management System (DBMS) is a system for storing and retrieving data. The…
Q: When a symbolic constant would suffice, why use a formal argument to provide data into a function?…
A: Definition A variable stated in a function's declaration is referred to as a formal parameter, By…
Q: Example. Convert NFA to a DFA. Convert this NFA to a DFA a 6. 8 5
A: Below is the answer to above question. I hope this will be helpful for you..
Q: Where can I find the criteria for selecting a node to serve as a supernode in a peer to peer…
A: A super-peer is a peer-to-peer (P2P) network node that acts as a server for both a customer network…
Q: What are some of the challenges and concerns with connecting devices to the Internet of Things…
A: 1. Erroneous access controlAdministrations presented by an IoT gadget ought to just be open by the…
Q: What is the core idea of adopting the prototype technique while building software?
A: Intro When constructing a system, prototyping is creating, evaluating, and tweaking a prototype…
Q: If N represents the number of elements in the collection, then the contains method of the…
A: Introduction: Here we are required to find out whether the given statements are true and false.
Q: What is the definition of the Candidate key?
A: Introduction: Candidate Key: candidate key is the smallest set of attributes that can uniquely…
Q: What is a hybrid language, and how does it differ from other languages?
A: Language Hybrid: A hybrid language is a computer language that supports many techniques for program…
Not Program Solved It on paper.. please create complete table link input ,output and stack
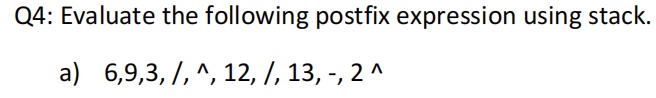
Step by step
Solved in 2 steps with 1 images

- Evaluate the following (postfix) expression using a stack. Assume A=1, B = 2 and C = 3. ABC+*CBA-+*Look at this stack frame: Fill in the data types for the following procedure: SomeSub PROC, LOCAL val1: , LOCAL val2: , LOCAL val3: , LOCAL val4:Q1- Write a program to insert five elements in the stack and print the top element using top() and print the size of the stack and check if the stack is empty or not.
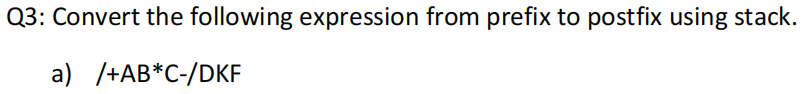
- 4. a) Using the stack diagram, convert the following infix expression to a postfix expression. A + B / C * (D – E) b) Referring to question 4 (a), give the value of postfix expression by using the stack concept if provided: A=13, B=20, C=4, D=30, E=253. a) Using the stack diagram, convert the following infix expression to a postfix expression. 4 + (9 – 3) / 2 b) Referring to question 3 (a), give the value of postfix expression by using the stack concept.T/F An error is thrown if the character '\n' is pushed in to the character stack.
- 1. a) Using the stack diagram, convert the following infix expression to a postfix expression. A* (B – C + D) – E / F b) Referring to question 1 (a), give the value of postfix expression by using the stack concept if provided: A=2, B=3, C=8, D=10, E=10 and F=25. fast please Convert the following infix expression into its prefix and postfix equivalents: a / b - (c + d * e) / f * g For any postfix, show the final transformed expression using the stack method for transformation as explained in class showing all the relevant steps. For the prefix, show any needed reversion and the final transformed expression using the stack method for transformation as explained in class showing all the relevant steps. Draw and sequence your diagrams clearly2. a) Using the stack diagram, convert the following infix expression to a postfix expression. A*(B + C* (D - E) ) / F b) Referring to question 2 (a), give the value of postfix expression by using the stack concept if provided: A=4, B=3, C=6, D=10, E=2 and F=4
- Q3: Write the C++ code of Stack which is performed multiple task which are given below and performed all task by using Arrays. Push values 10, 20, 5 , 50, 40, 60, 45 Pop values 45, 60, and 40 Sort all values in Stack Please create is empty and stack function for telling them stack is empty or full.NOTE: PLEASE SOLVE THE QUESTION PROPERLY AND ACCORDING TO THE REUIRED THINGS.None J. Operations required for reversing a word or a string using stack are push() and pop(). T/FConvert the following expression from infix to postfix and show the contents of Stack and the output expression at each step ((A-((B+C)*D/E))/(F*G+H))

