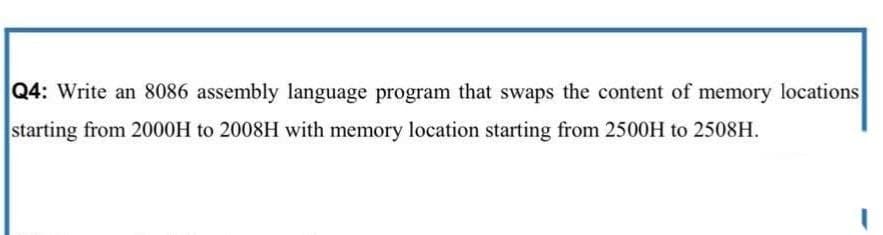
Q4: Write an 8086 assembly language program that swaps the content of memory locations starting from 2000H to 2008H with memory location starting from 2500H to 2508H.
Q: What are the advantages and disadvantages of a peer-to-peer network?
A: Introduction: This form of network is known as a peer-to-peer network when two computers or devices…
Q: Tips for being safe online include: You should be careful about what you post on social media and…
A: The Answer is given below step.
Q: Describe two services that the operating system provides for managing computer operations.
A: Introduction: The term "operating system" refers to the piece of software that is responsible for…
Q: 16. The mobile devices basically are identifying by: a. ICCID (Integrated Circuit Card Identifier)…
A: We need to find the correct option regarding mobile device.
Q: Examine the benefits and drawbacks of concurrent programming in great depth. Interaction between…
A: Concurrent programming is defined as the programming performed with multiple processes and executed…
Q: Please include material that is particular to the following topics: global problems (globalisation…
A: Globalization: "The greater interconnection and interdependence of nations and their people may be…
Q: 1. Briefly describe each of the following and discuss the knowledge benefits associated with them:…
A:
Q: Do you have an excellent example of an oops
A: Object-oriented programming: Object-oriented programming (OOP) is a programming paradigm in which…
Q: Given a class named Person with a private String field named name and a private integer field named…
A: part 1. function definition syntax acess_modifier data_type functionName(data type…
Q: 17. The SIM cards could be identified by: a. ICCID (Integrated Circuit Card Identifier) number; b.…
A: A SIM (Subscriber Identity Module) card holds all of the ICCID, PIN, and PUK numbers in it.
Q: There should be at least nine distinct components of a typical database environment stated
A: Introduction: The database framework has a lot of different. It details and supervises the processes…
Q: It is essential to provide users with information on how they may protect themselves against session…
A: Session hijacking:- Session hijacking is just what its name implies. An attacker may hijack a user's…
Q: In what ways does a successful back-up strategy differ from an ineffective one? The method of…
A: The Backup interaction is more perplexing than any time in recent memory, and keeping in mind that…
Q: evel cach _1 memor erage acc =. What is
A:
Q: A. Using algebraic manipulation to prove: A(A+B)(AB+C)(A BC + D)= ABCD B. Transform to only using…
A:
Q: Provide a copy of the code and screen shot for the output in the solutions’. Explain the working of…
A: We need to provide the output and code and explain the code.
Q: 14. The main files that store system setting information in MacOS are: a. Log files (extensions…
A: The question has been answered in step
Q: Write a Java program that computes and prints out the sum of 1 + 2 + .. + 100 Note: Your output…
A: Algorithm: 1. Declare value of i,num and sum. 2. Until i is less than equal to num then keep the…
Q: In this video, I'll discuss why I believe people and information systems are the driving factors…
A: SYNOPSIS: - The term "information system" refers to a collection of information systems is a set of…
Q: amic memory allocation, why i
A: Solution - In the given question, we have to tell what exactly is dynamic memory allocation, why is…
Q: Explain each of the addressing modes in detail with an example from each?
A: Introduction: The answer to the question suggests that address mode is a method for indicating…
Q: Educators should understand the benefits and cons of adopting educational information systems.
A: Educational information systems may be defined as a collection of pieces or components that are…
Q: The link between cohesion and coupling in software design may be summarised as follows:
A: Cohesion and Coupling: Coupling depicts the connections between modules. The relationship within the…
Q: What exactly is meant by the phrase "poison package attack" for people who aren't acquainted with…
A: Introduction: The most common kind of attack in which attackers actively introduce bogus data into a…
Q: In what ways does the usage of a siloed information system cause problems and difficulties?
A: Information systems are the system that makes use of the hardware and software systems designed in…
Q: Which can read data and convert them to a form that a computer can use? A. Logic B. Storage C.…
A: The correct answer of the question is given below
Q: es a substring with a new string. Example: >>> replace('The quick brown fox jumps over the lazy…
A: Given : Write a function that replaces a substring with a new string. Example:>>>…
Q: Explain the relevance (or lack thereof) of a TuringEquivalent machine/system or language.
A: Introduction: A Turing equivalent refers to the environment in which it is possible to create an…
Q: Explain in a nutshell what the key differences are between LL and LR parsing. Which of these is also…
A: LL: LL parser is a top-down parser for a subset of Context-free grammar. It reads the input from…
Q: Should we think about using many programmes on the computer at once? yes or no? justify your…
A: Given: Step describes whether or not a computer can multitask. Yes, a computer is capable of…
Q: What are some of the most major advantages of keeping data on the cloud, as well as some of the most…
A: The following are some of the benefits of storing data in the cloud: When you save the data on the…
Q: What is the most significant difference between mainframe operating systems and operating systems…
A: Introduction: The following are the key distinctions between two categories of operating systems:
Q: What what is the work that the Windows Service Control Manager is supposed to undertake, and how…
A: Introduction:- At system startup, the service control manager (SCM) is launched. It's an RPC server…
Q: Through taking this class, you will have a deeper understanding of social networking blogs, cloud…
A: Definition Blogs about social media such as Instagram, Facebook, and Tumble provide statistics or…
Q: Examine the fundamentals of Big Data Processing Architectures.
A: Introduction: Input, processing, and analysis of data sets that are either too large or too complex…
Q: Which model comes to mind first when you think about the Verification and Validation Model?
A: Verification and validation are not the same thing, although it is often confusing. Boehm briefly…
Q: What exactly does it mean to have one's privacy protected? The following is a list of five…
A: Answer: The right of an individual to have access to his or her own personal information that is…
Q: What is the most important phase of the SDLC, and can you support it with at least two circumstances…
A: Given: Project planning and requirements are the most essential parts of the SDLC. Without initially…
Q: Create a list of the many subfields that may be found under the umbrella of security, and then…
A: Information protection: It relates to preventing unauthorised access, theft, injury, as well as any…
Q: Is there anything in the way of an ethical conundrum that system analysts are required to deal with?
A: - We need to talk about the ethical issues that a system analyst may face to deal with.
Q: When developing computer systems, why is it beneficial to use an object-oriented approach rather…
A: Benefits of OOPs over traditional programming are: We can build programs from standard working…
Q: What are some of the different programming paradigms?What do the various programming paradigms…
A: Introduction: This programming paradigm is based on the premise that computer systems can sustain…
Q: A processor takes 24 cycles to complete an instruction 1 with frequency 4 GHz. The corresponding…
A: Hi there, Please find your solution below, I hope you would find my solution useful and helpful.…
Q: What is the distinction between cohesion and coupling, and how do they differ in software design and…
A: Introduction: Cohesion and coupling are used in the categorization approach to highlight…
Q: What are the main differences between a local-area network and a wide-area network that affect a…
A: Introduction: The key differences between a neighbourhood network and a wide-area network
Q: Please provide an illustration of the differences between the client-server architecture and the…
A:
Q: What is the best way to schedule processes in a time-sharing environment?
A: Time-sharing environment: Time sharing uses round robin scheduling. CPU schedulers allocate time to…
Q: What exactly is the CUDA architecture?
A: CUDA architecture: UDA Compute (CUDA) NVIDIA created the parallel computing platform CUDA. It boosts…
Q: Is there a link between the degree of cohesion and the degree of coupling in software development?
A: The passage or reference to the module is produced at the interface, which is where the complexity…
Q: The Value property indicates the state of the check box by taking on the value Value = 1, box is…
A: The value property is associated with the checkbox.
Step by step
Solved in 2 steps with 1 images

- 2. Write an 80x86 assembly program that accepts up to 10 integer test scores in the range of 0 to 100from the user and stores them in an array of words. Then the program should report how manyperfect scores were entered (i.e., scores of 100). MUST PROVIDE FULL CODE AND OUTPUT SCREENSHOTS PLEASE.Write a commented 8085 assembly language program in order to exchange 10 bytes of data stored from memory location 4200H, with 10 bytes of data stored from location 4300H.Which statement is correct for the memory segments in 8086 microprocessor? a. For Stack segment, the offset address can be a direct value. b. The offset address for program instructions is taken from SP register. c. Variables created in the Assembly program are stored in Data segment. d. Segment address for executing sub-routines is taken from ES register.
- write in program in 8085 SIMULATOR : with using LXI command how you will transfer one byte from memory location whose address is 11H to another memory location whose address is 13H.Topic: 8086 microprocessor Q 1c) AL= 53 CL=29 ADD AL, CL DAA What is the value of AL after execution? Q 1d) MOV AL, 4929H, what will be the value of AL after execution?Write down the machine code of the following assembly instructions for 8088/8086 processor inthe space on the right of each instruction. You can use the handout given to you for assembling theinstructions. AnswerMOV DS, AX; 8ED8XOR DI, DI;MOV DI, 1600;MOV CX, 256;SUB AL, AL;
- use assembly language 8086 to Write a program loads the block of memory locations from 0A1000H through 0A10FFH with number DDH using STRING INSTRUCTIONSwrite the code in program in 8085 SIMULATOR : with using LXI command how you will transfer one byte from memory location whose address is 11H to another memory location whose address is 13H.1- Write an X86 assembly program that searches through a block of 100H characters starting from data segment memory location BLOCKA. This program must count all lower-case letters and all upper-case letters. Byte-sized data segment memory location LOWER must contain the count of small letters, and data segment location UPPER must contain the count of capital letters. 2- Write an X86 assembly program that copies the contents of the previous byte-sized memory block (BLOCKA) into a new byte-sized memory block (BLOCKB) after converting the case of the letters taking into account the block BLOCKA ends with the symbol #. Hint: Use your name, ID No. and your points in our previous assignments and terminates the string using the character ‘#’ as follows: BLOCKA db ‘nAME sURNAME id nO. 16-155-777 aSSG1=90, aSSG2=100, aSSG3=60 sPRING 2020 #’
- There is an application that requires the following hardware: an Intel 8031, a Program ROM of 8Kx8, a Data ROM of 4Kx8 for look-up tables and a Data RAMs of 8Kx8. The memory map of the design: Program ROM should start at address 0000H. Then, the Data ROM should come above the Program ROM. Finally the Data RAM must go to the top of the memory map. There should be no gaps between the memory addresses of the external ROMs. Show the design’s address space on a memory map, starting with 0000H at the bottom and FFFFH at the top.There is an application that requires the following hardware: an Intel 8031, a Program ROM of 8Kx8, a Data ROM of 4Kx8 for look-up tables and a Data RAMs of 8Kx8. The memory map of the design: Program ROM should start at address 0000H. Then, the Data ROM should come above the Program ROM. Finally the Data RAM must go to the top of the memory map. There should be no gaps between the memory addresses of the external ROMs. Calculate the address space of the ROMs and RAMs of your design.Write an assembly program to display the largest of three variables. The three variables num1, num2 and num3 have values 89,20 and 56, respectively in 80x86 processors

