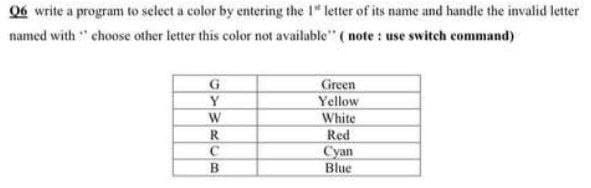
Q6 write a program to select a color by entering the 1" letter of its name and handle the invalid letter named with " choose other letter this color not available" (note: use switch command) G Green Y Yellow W White R Red C Cyan B Blue
Q: this is a normal Central Processing......... Unit used in communication with external .devices is…
A: Answer (1) Correct Option: (c) Microprocessor Explanation: Microprocessor used data base to…
Q: Why is the User Datagram Protocol, often known as UDP, not a viable option for the email program?…
A: The UDP is not a viable option for the email program and how the SMPT algorithm accomplishes its…
Q: It is true that we are not responsible for the way in which operating systems carry out the…
A: Introduction:- It is true that we are not responsible for the way in which operating systems carry…
Q: To utilize and access cloud-based apps and services.
A: This problem pertains to the use and access to cloud-based services and applications: Network…
Q: Which of the following are noun phrases? indicate all that apply "the woman" "the crispy apple"…
A: A noun phrases is a group of two or more word that is headed by a noun that include modifiers Even…
Q: In terms of search algorithms, what is the difference between a BFS (Breadth First Search) and a DFS…
A: BFS ( Breadth First Search ) : This alogithms is used to traverse the node present in tree/ graph…
Q: Is there an organization, management, and technology element of an information system?
A: Introduction: Information system An information system is a cohesive set of components that gather,…
Q: { int i, j; For (i=1;i<= 6; i++) { For (j= 1; j<= i; j++) Cout<<"$"; Cout << "\n"; }}
A: The C++ code implementation is given in the below step. The algorithm: The code first initializes…
Q: Is it better for a rapidly developing small firm to use an on-premise CRM system, an on-demand CRM…
A: Introduction: Tiger is the most fantastic choice for a small firm that is fast expanding. "Customer…
Q: A device that converts a physical variable to an electrical signal is a ______________.
A: Let us see the answer below,
Q: The audience should be informed about the objective of a Work Breakdown Structure (WBS). Is it…
A: The above question is solved in step 2 :-
Q: Methodologies and SDLC are obviously distinct. You may explain the software development life cycle…
A: Introduction: SDL (Software Development Lifecycle) manages projects effectively.
Q: What exactly is meant by the term "device driver," and how does one work
A: A device driver is an extraordinary sort of programming program that controls a particular equipment…
Q: Because of the many problems associated with mobile technology, adoption is challenging. How much…
A: An overview: When employing mobile technology, there are several challenges to overcome. Mobile…
Q: In the context of computers, what is the difference between architecture and computer structure?
A: Computer architecture describes what a computer accomplishes, while Computer organization describes…
Q: Q6:Rewrite the following Matlab code using a while loop to avoid using the beak command clc; clear;…
A: Find the required code in matlab given as below and output :
Q: How are disc blocks available in Linux because it does not have a FAT file system?
A: Intro The following is the question that was asked: Because the Linux operating system lacks a FAT…
Q: Defects in wireless networks may cause a range of issues. Give examples of three of these problems…
A: Given: To keep their operations operating effectively, today's organizations rely on robust, secure…
Q: In what instances, in your experience, would you propose using assembly language code in the…
A: An assembly language is refers to a low-level programming language designed to interface directly…
Q: There are various essential features and behaviors for descriptive models that we will go through in…
A: DESCRIPTIVE MODEL Descriptive research is a form of research technique that describes all of the…
Q: Q\ Write a program to find the area of rectangle and compare it with 4 results using switch…
A: ALGORITHM:- 1. Take input for the dimensions of the rectangle. 2. Calculate the area of the triangle…
Q: Identify two significant issues to do with student consent or data privacy that has emerged in the…
A: Answer:
Q: Please provide an overview of the various access technologies.
A: Introduction :- An overview of the various access technologies.
Q: Consider the following HTML with associated CSS: #container { width: 400px; } #inner { padding:…
A: Please refer below for your reference: The container is of 400px and 50% of it is 400/2=200px;
Q: Is it better to have an on-premise CRM system, an on-demand CRM system, or open source CRM for a…
A: Introduction: Vtiger is ideal for fast expanding small businesses. The term "CRM" is an abbreviation…
Q: Do you have any suggestions for specific ways that may be utilized to capture the flow of data?
A: Data Flow Diagram: A data flow diagram (DFD) depicts data movement within a system or process. It…
Q: In terms of speed, size, and cost, explain the differences between DRAM and SDRAM.
A: This question describes the differences in speed, size, and cost between DRAM and SDRAM.
Q: ween SDLC and methods. Explain the Software Development Lifecycle (SDLC) and how it relates to…
A: A software life cycle model (likewise named process model) is a pictorial and diagrammatic portrayal…
Q: Exists a difference between traditional on-premises data centers and cloud settings with regard to…
A: Introduction Yes, there is a distinction between traditional on-premises and cloud-based data…
Q: Describe the steps involved in the program's analysis phase.
A: Introduction: The Analysis Phase is when the project's lifespan begins. The Analysis Phase is when…
Q: Students name lastname age ID rim ismail 19 123 sara kamel 18 134 milad ghantous 21 1345 1345 tarek…
A: Solution: option4: SELECT Roster.ID , Students.ID absence From Roster.Students Where…
Q: Using the S-R (set-reset) flip-flop, design a memory cell with the following inputs: Data-in,…
A:
Q: 2. Searching (6 pts): Consider the following array of int values. [2, 3, 10, 18, 23, 27, 45, 56, 57,…
A:
Q: According to your experience, in what instances would you recommend using assembly language code in…
A: Please refer below for your reference: Instances one would you use assembly language code in the…
Q: If you have the following primitive flow table, afte the merging step th- merging flow tabl…
A: Lets see the solution.
Q: { int x, y = 1; For(x=0; x<50; x+ =5) { cout << x << “ “<<y; y ++; }}
A: C++ programming
Q: , what do you mea
A: Introduction: Storage space allocation in the capacity gadget is alluded to as partitioning in the…
Q: A. 0 B. 1 C. 2 D. 3 E. 4 5. For which one of the following statements, x[0] Aut 1 does NOT cause an…
A: In question only 5th part is present,6th part not there. So, solving only 5th part in given…
Q: The OSI security architecture contains a wide array of advanced precautions to ensure the…
A: Intro The route used by all packets between their source and destination is the same. It is not…
Q: Do you think the rise of the cloud computing revolution has had an impact? Is there a correlation…
A: Using cloud computing helps teams work together. Real-time contact with your team Cloud technology…
Q: Assume that the above diagram is a partial EER model representing the seat booking system of Virgin…
A: Find the required SQL queries given as below :
Q: Determine the most crucial components of an information technology system. To have a…
A: Introduction: The fundamental elements of an information system
Q: anagement
A: In registering, a database is a coordinated assortment of data put away and got to electronically.…
Q: Enterprise University (EU) is an online university and has a student population over 80,000 and…
A: Big Data refers to a collection of large volumes of data, giving us greater insight of our data…
Q: try to make a simple java currency converter use any of the following: java awt java swing…
A: //Writing program using java swingimport javax.swing.*;class Main { public static void…
Q: Provide an explanation of the handshake protocol used by the embedded system.
A: Handshaking establishes a communication channel between two separate computer components. Data is…
Q: Q2: create a script file to generate NXN matrix in form like: 1 2 1 2 1 21 2 1 2 1 2 1 2 2 1 2 1 2 1…
A: Here we have given a script file to generate NxN matrix. You can find the solution in step 2.
Q: How do human-computer interaction (HCI) and information technology (IT) interact?
A: HCI is also known as human computer interaction.
Q: Are regions and availability zones important when it comes to implementing high-availability,…
A: Availability Zones (AZs): The global architecture of Amazon Web Services is organized according to…
Q: create a script file to generate NXN matrix in form like:
A: Given :
Step by step
Solved in 3 steps

- Write a program that asks the user to enter a 1st color choice from a set of options: red, yellow or blue, and then asks them to enter a 2nd color choice from the remaining 2Write a program that prompts the user to enter the center x-, y-coordinates, width, and height of two rectangles and determines whether the second rectangle is inside the first or overlaps with the first, as shown in Figure 4.15.Create a program that will accept integer values for month, day, and year and then output the“long version” of the specified date. Use up until switch statement only. Do not use other commands. For example, if month = 11, day = 5, and year = 2010, output the string, “November 5, 2010”.If there is any invalid input, display “Invalid date!” and end the program.
- Write a program that prompts the user to enter the center x-, y-coordinates, width, and height of two rectangles and determines whether the second rectangle is inside the first or overlaps with the first, as shown in Figure 4.10. Test your program to cover all cases.Write a program that draws a fixed circle centered at (100, 60) with radius 50. Whenever the mouse is moved while the left button is pressed, display the message indicating whether the mouse pointer is inside the circle, as shown in Figure 9.31.Write a program that prompts the user to enter the radius of the rings and draws an Olympic symbol of five rings of the same size with the colors blue, black, red, yellow, and green, as shown in Figure 3.5c.
- What is the output of the following code segment?intc=6,d=12;if(cd)if(c8)Write(blue);elseWrite(Red);elseWrite(Green); Blue Red Green nothingWhat is the output of the following code segment?intc=6,6=12;if(cd);Write(Green);WriteLine(Yellow); Green Yellow GreenYellow nothingWrite a program that prompts a user to enter a year between 1 and 2499 and prints its century in the format such as 1st, 2nd, 3rd, 4th, etc. please use a switch statement. for what we have done in class so far we have only used #include <iostream> <fstream> <cmath> <string> <iomanip>, so if possible if this can be done using that so I can understand for my next assignment that would be great thanks! Test Run 1:Enter a year between 1 and 2499 -- 19231923 is in the 20th century Test Run 2:Enter a year between 1 and 2499 -- 22022202 is in the 23rd century Test Run 3:Enter a year between 1 and 2499 -- 2630Wrong year!
- Here is the code i have written so far, please finish it #include <stdio.h>#include <cstack.c> int i=-1;int nextstate=0;cstack top; init_cstack(&top);while(1) switch{ case 0: i++; if (is_open(my_input[i])) nextstate= 1; else if (is_close(my_input[i])) nextstate= 2; else if (my_input[i] == '\0') nextstate= 3; else nextstate= 4; break; case 1: if(!is_cfull()){ cpush(&top, my_input[i]); nextstate= 0; } else{ printf("Error! Stack is full\n"); exit(0); } break; case 2: if (!is_cempty(top)){ if(is_brother(cpop(&top), my_input[i])){ nextstate= 0; } else{ printf("Error! Delimiter do not match\n"); return FALSE; } } else{ printf("No open delimiter to compare to\n"); return FALSE; } break; case 3: if…Write a program that prompts the user to enter the radius and draws four circles in the center of the screen, as shown in Figure 2.4a.Write a program that prompts the user to enter thecenter x-, y-coordinates, width, and height of two rectangles and determineswhether the second rectangle is inside the first or overlaps with the first, as shownin Figure . Test your program to cover all cases.

