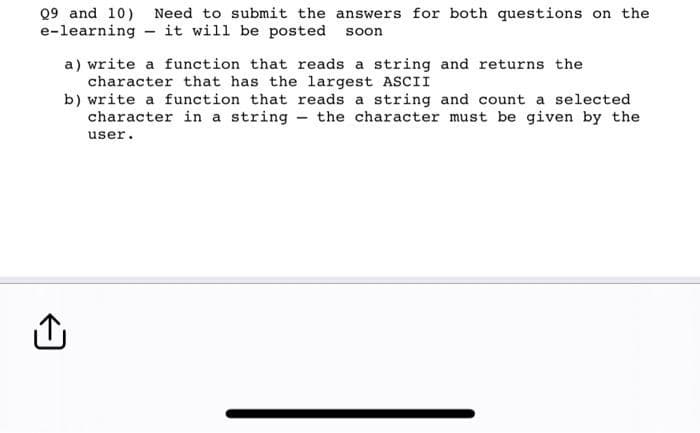
Q9 and 10) Need to submit the answers for both questions on the e-learning - it will be posted soon a) write a function that reads a string and returns the character that has the largest ASCII b) write a function that reads a string and count a selected character in a string the character must be given by the user. -
Q: What are the most important elements to keep in mind about data backup and recovery?
A: Importance of Elements: All living and non-living things are made up of elements, which are…
Q: Is there a danger associated with Internet usage?
A: Start: The loss of data is the cloud computing practise that poses the greatest potential threat to…
Q: It's crucial to describe the variations between Diagrams 0 and 1. Does the Context diagram include…
A: Introduction: Diagram 0 and the context diagram are dissimilar. The context diagram presents many…
Q: The system's method for detecting incursions
A: An internal network is protected against unauthorised servers and networks using a firewall based on…
Q: What is the most efficient method for acquiring application software? If you want to make a claim,…
A: Given: What is the most effective way to get application software? You should back up your claim…
Q: Help required! What advice would you give someone deciding between Linux and Windows?
A: Since 1985, Microsoft Windows has been the most popular home and workplace operating system. Windows…
Q: What is wrong with my code, why is my if statement not working Public Class Form1 Function…
A: The error is because the usage of the Mod operator is wrong. Mod operator required two operands for…
Q: Is the security of the cloud endangered by a data breach? What more can you tell me about…
A: Data breach: There is a data breach when data is stolen or destroyed from a system without the…
Q: How does one compress an encrypted file system on a computer?
A: Compressing a secure file system: Once the file has been encrypted, a stream of uncompressible…
Q: IT security Compare these encryption products' CIA (Confidentiality, Integrity, Availability)…
A: Information technology Security which referred to as info Sec, refers to the processes and which…
Q: Why is hashing passwords preferable to encrypting them when storing them in a file
A: A cryptographic technique called hashing can be used to check the legitimacy and consistency of…
Q: How can I get access to Application Software? The most effective technique to convey your point is…
A: Introduction: Application software is made to assist with a wide range of functions, including…
Q: A. test plan B. 【】 Set the correct order of the process of testing D. C. test requirement E. test…
A: The above question that is the correct order of testing is answered below step
Q: Each of the three units—the control, arithmetic, and logic—serves a particular function.
A: Arithmetic: The term arithmetic is used to describe the fundamentals of counting, measuring, and…
Q: In computer science, what do rollback and rollforward mean?
A: Moving Forward The roll forward capability is by default activated when a database, tablespace, or…
Q: What decisions must be taken in order to define database field requirements?
A: The database has its own "data dictionary," which is comprised of the field requirements. Within the…
Q: In terms of security, what is the difference between file encryption and disc encryption?
A: Disc encryption is a process of encoding all user data on a storage device such as a hard drive or…
Q: Should the IT director answer to the company's president?
A: An IT director, or chief information officer, is responsible for putting up a corporate strategy,…
Q: How probable do you believe it is that a data breach will have a future impact on cloud security? Is…
A: Given: Successive organisations are confident in their efforts to prevent data breaches and aware of…
Q: What recommended best practises are there for managing firewalls? Explain.
A: The network firewall is the essential security tool you own. Thus it must be as strong as possible.…
Q: The domain of discourse for this problem is a group of three people who are working on a project. To…
A: Statement A is True. Statement: ∀x∀y(x!=y) -> M(x,y) M(1,2) -> True M(1,3) -> True M(2,1)…
Q: A convenient method or instrument for providing computer-generated charts, diagrams, drawings, and…
A: Introduction: The field of computer science known as computer graphics is used to create pictures,…
Q: Why must user-defined function prototypes be specified when a programme has user-defined functions
A: Please find the answer below :
Q: Is the security of the cloud endangered by a data breach? The following are some potential solutions…
A: Introduction: Information theft, a ransomware, phishing, password guessing, viruses, malware,…
Q: A programme slice: what does that mean? discussion of programme segmentation, both static and…
A: Answer is Explanation: Program slicing can be defined in such a way that it is a technique used…
Q: All the requirements from Part 1 must still be met by the program, with the following changes and…
A: Here I have written a simple code in C# for a user to Step 1: Create a database and table with the…
Q: What decisions must be taken in order to define database field requirements?
A: Introduction: The database has its own "data dictionary," which is comprised of the field…
Q: Q5/ Write simple C++ program that create struct to read an informations of 20 Students (Name,
A: answer in step 2
Q: User-defined functions are preferred than those that are predefined.
A: Introduction Functions give better-measured quality to your application and a serious level of code…
Q: After a data breach, is it possible to increase cloud security? Among the possible countermeasures…
A: 1. Data Breaches : Usually done to obtain sensitive information such as financial details , health…
Q: What make up a typical operating system's kernel components and how are they used?
A: Typical OS kernel components:- I/O Manager Cache Manager Object Manager Power Manager Virtual…
Q: The encrypted file system of a computer may be stored in a compressed manner.
A: Version 3.0 of NTFS introduces the Encrypting File System (EFS), a technology that offers…
Q: 2. There are, by hypothesis, infinite number bases, but in computing we use hexadecimal, octal and…
A: The complete answer is below:
Q: what is more important – precision or accuracy? State a real-life scenario where it shows the more…
A: Introduction: Accuracy: How closely a measurement resembles the actual/recognized value…
Q: What does a Repository and Data Dictionary mean in terms of computers?
A: A repository is a location where data is stored. A data dictionary contains information about the…
Q: Examine the many kinds of access control systems and how they vary. Identify the various types of…
A: Answer : The different kinds of access control systems are : Role based access control mandatory…
Q: A user-defined functions programme must supply function prototypes.
A: User defined functions are those functions which are defined by the user according to it's need. A…
Q: (Flattening arrays with flatten vs. ravel) Create a 2-by-3 array containing the first six powers of…
A: According to the information given:- We have to follow the instruction in order to compare the…
Q: Refer to the given brief system descriptoin and answer the questions (a-c) below using your…
A: Below I have provided the solution to the given subpart question
Q: Do you have a sense of security? One of today's most serious challenges is physical security. There…
A: Physical security is the protection of people, property, and physical assets from actions and events…
Q: Python lists are commonly used to store data types. Lists are a collection of information typically…
A: Introduction: List: It is a kind of array used to hold values of various data kinds. A list's…
Q: How can I get access to Application Software? The most effective technique to convey your point is…
A: Introduction: Many jobs may be aided by application software, such as data management, data…
Q: What are the most essential aspects of data backup and recovery?
A: Introduction: In the event of a catastrophe, businesses must prepare for data loss, including the…
Q: What distinguishes several threads from multiple processes? Could you kindly provide a brief…
A: Given: In order to expand the amount of computing power available, multiprocessing makes use of two…
Q: Describe a real-world CSP, the issue it addressed, and the results it had on the local and global…
A: Constraint fulfillment issues are mathematical problems that are described as a set of objects whose…
Q: Define parallel processing, often sometimes referred to as multiprocessing. concurrent processing…
A: Parallel computing explained: Multiple computer cores are used in parallel computing to tackle…
Q: Through interface cards, the expansion bus may be utilised to link external devices to the CPU. Why?
A: An expansion bus is an input/output channel that carries data from internal hardware, such as RAM or…
Q: How and to what extent is physical security distinct from other forms of security? We must be aware…
A: Physical security is the protection of personnel, hardware, software, networks, and data from…
Q: When and how does a compiler create an Object() function by default in native code?
A: Given: If we don't specify our own Object() [native code] function, the C++ compiler will create a…
Q: Describe some strategies for session theft. Can anything be done to stop this from occurring?
A: Session Hijacking is an attack that enables unauthorized access to authorized session connections:…
Step by step
Solved in 3 steps with 4 images

- c++ A palindrome is a string that reads the same both forward and backward. For example, the string "madam" is a palindrome. Write a program that uses a recursive function to check whether a string is a palindrome. Your program must contain a value-returning recursive function that returns true if the string is a palindrome and false otherwise. Do not use any global variables; use the appropriate parameter.4. Complete the function show_upper. This function takes one parameter - a string (s). It should return a string made up of all the upper-case characters in s. For example, if s is “aBdDEfgHijK” then show_upper should return “BDEHK”. It should return the upper-case string - not print it. Do not change anything outside show_upper.capCount.py make a program called capCount.py that has a function that takes in a string and prints the number of capital letters in the first line, then prints the sum of their indices in the second line. The string "hEllo, World" would should look like this: 28
- Create a function that removes the first and last characters from a string. In c# Examples RemoveFirstLast("hello") - "ell" RemoveFirstLast ("maybe") - "ayb" RemoveFirstLast("benefit") - "enefi" RemoveFirstLast("a") - "a" Note If the string is 2 or fewer characters long, return the string itself (See example # 4).PYTHON without Def function Problem Statement Implement a function which takes two arguments: the first is a string and the second is a single character (as a string). This function should move every instance of the given character in the string to the end of the string, and then return (do NOT print) the final string. Sample Input "hello how are you?", "o" Sample Output "hell hw are yu?ooo"(4) Implement the GetNumOfWords() function. GetNumOfWords() has a constant string as a parameter and returns the number of words in the string. Hint: Words end when a space is reached except for the last word in a sentence. Call GetNumOfWords() in the PrintMenu() function.Ex: Number of words: 35
- 3.34 LAB: Mad Lib - loops in C++Mad Libs are activities that have a person provide various words, which are then used to complete a short story in unexpected (and hopefully funny) ways. Write a program that takes a string and integer as input, and outputs a sentence using those items as below. The program repeats until the input is quit 0. Ex: If the input is:apples 5shoes 2quit 0 the output is:Eating 5 apples a day keeps the doctor away.Eating 2 shoes a day keeps the doctor away. Make sure your answer is in C++.Vowel Words – a vowel word is a word that contains every vowel. Some examples of vowel words are sequoia, facetious, and dialogue. Write a program that uses a Boolean-valued function to determine whether a word input by the user is a vowel word. a) Request a word, word from the console.b) Define a function, isVowelWord(word) examines the word for vowels one at a time and terminates when a vowel is found to be missingor after all vowels have been considered. (Hint: Use in operator to check if a vowel appears in the word).c) Print out the search result (print statement should not be part of the function, isVowelWord(word)). Output Example 1:Enter a word: Education‘Education’ contains every vowel. Output Example 2:Enter a word: Python ‘Python’ does not contain every vowel. need help with pythonVowel Words – a vowel word is a word that contains every vowel. Some examples of vowel words are sequoia, facetious, and dialogue. Write a program uses a Boolean-valued function to determine whether a word input by the user is a vowel word.a) Request a word, word from the console. b) Define a function, isVowelWord(word) examines the word for vowels one at a time and terminates when a vowel is found to be missing or after all vowels have been considered.(Hint: Use in operator to check if a vowel appears in the word)c) Print out the search result (print statement should not be part of the function, isVowelWord(word)).
- Python question please include all steps and screenshot of code. Also please provide a docstring, and comments through the code, and test the given examples below. Thanks. Write a function crypto() that takes as an input a string s and returns an encryptedstring where encryption proceeds as follows: split the text up into blocks of two letterseach and swap each pair of letters (where spaces/punctuation, etc. is treated like letters).If the input string>>> crypto('Secret Message')'eSrcteM seaseg'>>> crypto('Secret Messages')'eSrcteM seasegs'5.19 LAB: Mad Lib - loops Mad Libs are activities that have a person provide various words, which are then used to complete a short story in unexpected (and hopefully funny) ways. Write a program that takes a string and an integer as input, and outputs a sentence using the input values as shown in the example below. The program repeats until the input string is quit and disregards the integer input that follows. Ex: If the input is: apples 5 shoes 2 quit 0 the output is: Eating 5 apples a day keeps you happy and healthy. Eating 2 shoes a day keeps you happy and healthy.#include <iostream>#include <string>#include <climits> using namespace std;class BalancedTernary { protected: // Store the value as a reversed string of +, 0 and - characters string value; // Helper function to change a balanced ternary character to an integer int charToInt(char c) const { if (c == '0') return 0; return 44 - c; } // Helper function to negate a string of ternary characters string negate(string s) const { for (int i = 0; i < s.length(); ++i) { if (s[i] == '+') s[i] = '-'; else if (s[i] == '-') s[i] = '+'; } return s; } public: // Default constructor BalancedTernary() { value = "0"; } // Construct from a string BalancedTernary(string s) { value = string(s.rbegin(), s.rend()); } // Construct from an integer BalancedTernary(long long n) { if (n == 0) { value = "0"; return; } bool neg = n < 0; if (neg) n = -n; value = ""; while (n !=…

