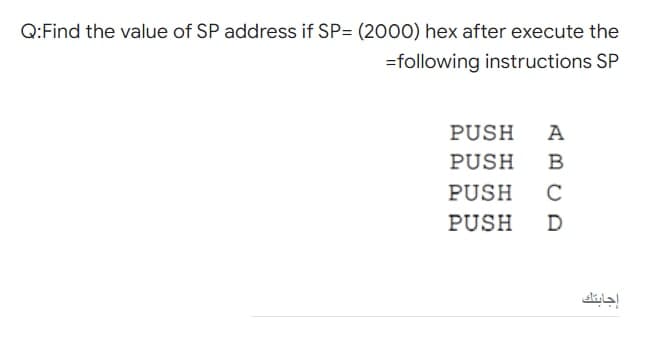
Q:Find the value of SP address if SP= (2000) hex after execute the =following instructions SP PUSH A PUSH PUSH C PUSH
Q: the Octal system can be represented in . bits in binary 3 O 5 O 7 O 8
A: Introduction: the Octal system can be represented in ...... bits in binary3 578
Q: 2. Explain the function and purpose of different types of Tristate, construct 4:1 Mux using…
A:
Q: What exactly is ethical system theory?
A: Answer: Rae says that ethics is a process that is both an art and a science, as previously stated.…
Q: Q:find the actual address for the ..il following instruction assume X=38 and R index=DCE8 hex LOAD…
A: Given: X = 38 R index = DCE8 hex LOAD X(Ri) , A Find the actual address.
Q: Q1)Read the passage carefully and then answer the items that follow. My brother and his friend don'…
A: The complete solution is given below:
Q: What are the challenges that businesses experience while attempting to shift to a cloud-based…
A: Introduction: Platform for cloud computing: Provides the architecture for a software service or…
Q: Comment briefly on multimedia and its numerous forms, including the most common medium for storage,…
A: A single interactive presentation may include many types of material, such as text, audio, pictures,…
Q: Consult with the websites of at least two other organisations, including Microsoft, Oracle, and…
A: Main technology corporations: An company obtains a market. It refuses to invest in new industries…
Q: ex implement the following peration: complement bits 6
A: data stored in register A * =(9E) hex implement the following micro operation: by complementing bits…
Q: write a java program to print the mirror image of right angled in x-direction after taking number of…
A: Required:- Write a Java program to print the mirror image of right-angled in x-direction after…
Q: how communication occurs a cross local ethernet network
A: Introduction: A local Area Network (LAN) is a data communication network that connects multiple…
Q: What is the relationship between a database and an information system, and how does this…
A: INTRODUCTION: Any collection of data or information that is particularly arranged for quick search…
Q: membership='Bronze' total_retail_price=1000 sales_tax=7.25 if membership=="Platinum" :…
A: The flow chart of this program is given below-
Q: What distinguishes "interdependence" from other ideas in systems theory?
A: Intro Given the varying definitions of a system: dependency is an important problem in systems…
Q: 3. Twin Primes A prime number is any integer greater than 1 that is divisible (without remainder) by…
A: Program: def twinPrimes(a,b):t=[]while a<=b:if a==1 or a==2:a+=1continueif isPrime(a):if…
Q: Identify and briefly outline the six basic transaction processing operations performed by all…
A: Required: Identify and briefly outline the six basic transaction processing operations performed by…
Q: Duality Principle can be : * O X(XY) = XY + XX O X(XY) = X + XY O x(XY) = YX + Y ALL ARE WRONG O O O
A: The duality Principle can be : Answer: All are wrong
Q: What are the consequences of the cloud computing revolution? Have you got Collaboration on your…
A: The goal of the research is to provide an overview of the advantages and dangers of cloud computing…
Q: Distinguish the advantages and disadvantages of virtualization and network storage options.
A: The network-based storage virtualization is a system that allows the physical organization of the…
Q: e) Find the moment of inertia of a hollow cylinder about the axis of the cylinder using a JAVA…
A: The solution to the given problem is below.
Q: Q:A CISC has large variety of addressing modes typically O from 5 to 20 different modes O from 15 to…
A: Dear learner , hope you are doing well , I will try my best to answer this question. Thank You !!
Q: Create a program that will sort the following words: Example: Will, Mike, Dustin, Lucas, Max, Eleven
A: here in the given question ask for sorting for a string array.
Q: Which VLAN is intended to provide administrative access to network devices?
A:
Q: Example-3: Write a program to calculate the Area and volume for a sphere. Sol. -The area of sphere 4…
A: According to the Question below the solution: Output:
Q: The term "system testing" has numerous meanings. Give an overview of the many sorts of testing that…
A: Intro System testing is a technique to testing that may be thought of as a kind of black-box…
Q: A program's controls are explained here.
A: Intro A program is a collection of logical instructions that is generated in order to acquire a…
Q: Is the BIOS operating system volatile?
A: Introduction: BIOS is a computer programme that runs when the computer is turned on.
Q: Example-3: Write a program to calculate the Area and volume for a sphere. Sol. -The area of sphere =…
A: According to the Question below the Solution:programming language is not mention so i am using…
Q: Why would you use prototyping in your system design?
A: Prototyping is the process of creating a representation of a system. This aids analysts in…
Q: What is the difference between TCP and UPD session hijacking?
A: TCP stands for transmission control protocol. UDP stands for user datagram protocol. Both are…
Q: What are the key advantages and disadvantages of cloud-based data storage?
A: The advantages are as follows: 1) Access your data anywhere: As data is stored remotely in cloud so…
Q: membership='Bronze' total_retail_price=1000 sales_tax=7.25 if membership=="Platinum" :…
A: Flow chart of the given program is :
Q: What are your thoughts on eavesdropping and network sniffing? What is it about them that makes them…
A: Wiretapping is a method for passively monitoring and analyzing the data flow inside a network. The…
Q: Explain Agile System Development briefly. Extend by referencing the Agile Manifesto.
A: The solution to the given question is: AGILE SOFTWARE DEVELOPMENT PROCESS Agile software development…
Q: Given an array, that can contain zeros, positive and negative elements. 1. Write an algorithm that…
A: Algorithm: Algo count_Numbers(arr , n) { decalre variables countZero , countPositive ,…
Q: Write a DHCP report (Dynamic Host Configuration Protocol). A research review, benefits, and…
A: Fill out a DHCP report (Dynamic Host Configuration Protocol). A review of the literature and…
Q: Provide some concrete examples to illustrate the key distinctions between a two-tier and a…
A: distinctions between a two-tier and three-tier application architecture. Two-Tier Database…
Q: Write a DHCP report (Dynamic Host Configuration Protocol). A research review, benefits, and…
A: Fill out a DHCP report (Dynamic Host Configuration Protocol). A review of the literature and…
Q: Which VLAN is intended to provide administrative access to network devices?
A: Which VLAN is intended to provide administrative access to network devices? In below step.
Q: Define and distinguish the SHA, RSA, and AES algorithms. Is hashing useful in the sphere of…
A: Answer : SHA, digest algorithm. it can be imagined that a relatively large data block can be…
Q: Let's say that an employee's regular pay is rate times hours. If they work more than 40 hours, they…
A: olution: Given, If they work more than 40 hours, they get time and a half. In that case, we…
Q: 1. Which of the following is not part of a standard SQL statement? a. Importable programming…
A: Given Which of the following is not part of a standard SQL statement? with options a Importable…
Q: Dnetwork running at 1Mbps ignal speed in the cable is 2 would be
A:
Q: It is easy to convert the hexadecimal to . bits equivalent binary representation O 3 O 2
A: To find solution for "it is easy to convert the hexadecimal to ______ bits equivalent binary…
Q: ke i-nodes to keep track o blocks are 1 KB in size, has space for 8 direct blc ct block and 1 triply…
A:
Q: 29. The fundamental storage unit is a bit which can be in an OFF or ON state. How many different…
A: Option C is correct: 25
Q: Write a program that helps Poslaju customers in calculating postage fee. Poslaju National Courier…
A: Note :- You have not mention the language of the program so. i'm answering your question in C…
Q: Create a parent class Person with one attribute age and one method greet() that prints out "Hello,…
A: I give the code in Java (Because you have not mentioned any specific language )along with output and…
Q: A small town is attempting to attract tourists who visit larger nearby cities. A network engineer is…
A: Given: A small town is attempting to attract tourists who visit larger nearby cities. A network…
Q: JS Register has Individu e status of ALU operatic
A: Flag Name Z Zero flag C Carry flag S / N Sign flag Negative flag V / O / W Overflow flag…
Step by step
Solved in 3 steps

- A(n) __________ is a storage location implemented in the CPU.Most Intel CPUs use the __________, in which each memory address is represented by two integers.The 32-bit number 52AB43FC (in hexadecimal) is stored in abyte-addressable memory starting at physical address FE08 (in hex) using Little-Endian notation. The byte(value ni hexadecimal) stored at theaddress FE0B will be
- A computer has a 16 bit address space A[15:0]. If all addresses having bits A[15:14]=11 are reserved for I/O device registers, then the maximum number of actual word addressable memory locations is 216 - 214 Group of answer choices True Falsemcq question The Physical address of the String Destination Memory Reference is: DS:DI, DS:SI, and DS:BX SS:SP, and SS:BP ES:DI only ES:DI and ES:SIAssembly language programming in MIPS. Use QTSpim to run code. Write a simple Assembly Language program that has a data section declared as follows:.data.byte 12.byte 97.byte 133.byte 82.byte 236 Add the values up, compute the average, and store the result in a memory location.
- Micro processor 8086 Assume that there are two bit 32-bit numbers:4444DDDDH and CCCC0003H .write an assembly program program to sum them , if it’s possible to do it with intel 8086 microprocessor then cross check (4444DDDH and CCCC0003HIn sim8085. c) Execute the given 8085 instructions and attach the memory view before and after execution. Take value of your choice at the required memory locations. Code: LXI H, 2000H MOV A,M ADI 02H INX H MOV M,A HLTthe available space list of a computer memory is specified as follows: 9 start address block address in words 100 50 200 150 450 600 1200 400 determine the available space list after allocating the space for the stream of requests consisting of the following block sizes: 25,100,250,200,100,150 use i) first fit ii) best fit and iii) worst fit algorithms
- In a 1 MB memory divided into 64 KB segments, if a segment starts at the address 1234A find the last address in the segment.A memory that is capable of determining whether a given datum is contained in one of its addresses is CAM why?0001 = Load AC from memory 0010 = Store AC to memory 0101 = Add to AC from memory 0011 = Load AC (the accumulator register) from an I/O device 0111 = Store AC to an I/O device With these instructions, a particular I/O device is identified by replacing the 12-bit address portion with a 12-bit device number. Remember that a number ending with a small ‘h’ means the number is a hexadecimal number. What is the hexadecimal string that expresses the following instructions? Load AC from memory location 62h. Add the contents of memory location 451h to AC. Store AC to memory location 8h. Store AC to I/O device number 8h.

