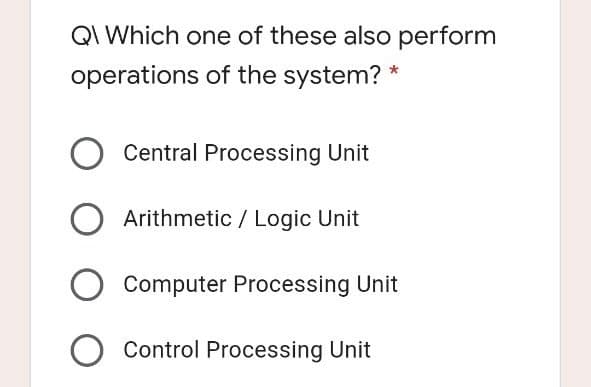
QI Which one of these also perform operations of the system? * O Central Processing Unit Arithmetic / Logic Unit Computer Processing Unit
Q: s the message box that was triggered instantly appear before or after the applicati
A: CreateWindow functionThis function creates a pop-up or child window that is overlapped. It provides ...
Q: 4.a. Which piece of equipment in a dim fiber lease can limit the lessee's access to multiple channel...
A: 4.a. Which piece of equipment in a dim fiber lease can limit the lessee's access to multiple channel...
Q: What is the difference between pattern and anti-pattern?
A: Let's understand pattern and anti pattern separately: Patterns: We all know what patterns generally ...
Q: The result is negative when the dividend and divisor have not same sign. * O False True
A: Binary Coded Decimal, or BCD, is a telephone system or code that uses binary numbers or digits to re...
Q: Counting Operations to Produce Polynomials In the following section, I will present you with multipl...
A: given by The amount of abstract operations achieved in the above code are: 1. 1(since the func...
Q: Given the machine code, identify the instruction line or command line. Use CAPITAL LETTERS . No spac...
A: SUMMARY: - Hence, we discussed all the points
Q: number repeats), both terminated by a -1. The size of each sequence can vary (maybe sequence-1 has f...
A: The given problem is related to merging a list of numeric sequences in a new list having an ordered ...
Q: Which of the following are true (mark all that apply)? O His a leaf and a child of D. O Eis the chil...
A: It is true because H has no children so it is a leaf node and H is the subnode of D.
Q: Explain how the Internet of Things works.
A: Introduction: Devices and items with built-in sensors are connected to an Internet of Things platfor...
Q: Write a query that returns the mean cost per install for each adgroup as well as the percentage of t...
A: the answer is given below:-
Q: Assign a name to the graphics processing unit.
A: Introduction: A graphics processing unit -GPU is a computer processor specifically designed to handl...
Q: Which among the following languages do not support concurrent programming? Answer Choices: e. Java f...
A: Concurrent programming is a computer programming in which during specific period of time multiple pr...
Q: Who or what is the Virtual Key Symbol for the Left Menu on the computer?
A: Virtual key: Virtual keys are keys that are not physically present on the keyboard but are mapping t...
Q: Computer Science Write a simple LISP function to count all leaves in a tree. You need to use a doubl...
A: Question 1. Write a simple LISP function to count all leaves in a tree. You need to use a double rec...
Q: an I please have the flow chart for this Python Code. current_year = 2021 class Employee:...
A: Here below i make simple flow chart of given python code: ==========================================...
Q: What is the output of the following Python code? myList = {} myDictionary = [] myList[0] = "chegg" m...
A: Insert function inserts element at particular index in list.
Q: Describe in fully the advantages of distributed systems.
A: Introduction: A distributed system is a computing environment in which various components are spread...
Q: Using C#, create an application that will ask the user to enter password set in the program for only...
A: Password print('Enter username and password to continue with exam')count=0while count < 3: us...
Q: 2. As you're troubleshooting a dead zone in your office, which measurement will help you determine t...
A: Received signal strength Indicator(RSSI) indicate the signal in decibels. There are certain network ...
Q: What is tha main function of router?
A: Introduction: Routers are computer networking devices used to transport data packets from one networ...
Q: Writepseudocodethatperformsthefollowing:Askausertoenteranumber.Ifthe number is between 0 and 10, wri...
A: Pseudocode is an informal way of describing a program that does not require any strict programming l...
Q: Compare between the Two Tier Client-Server DBMS Architecture and Three Tier Client-Server DBMS Archi...
A: Your answer is here. Introduction :- Two Tier Client-Server DBMS Architecture :- Two-tier client-ser...
Q: List the components of an HTTP requests
A: HTTP request has three components: Request line header body
Q: e IP part o
A: given - What is the purpose of the IP part of TCP? What is the relationship between IP and ICMP? in ...
Q: What are the potential benefits of the C calling convention over the STDCALL calling convention?
A: Answer: The STDCALL calling convention is very important because it tells you how to continue the fu...
Q: ASDFA
A: The solution to the given problem is below.
Q: Counting Operations to Produce Polynomials In the following section, I will present you with multipl...
A: In the following section, I will present you with multiple different bodies of code, and it is your ...
Q: Scenario: You are tasked with the development of an E-Scooter ride-share system. It allows registere...
A: As per bartleby we are allowed to answer only first question.For more question please post them sepa...
Q: Relationship between supertypes and subtypes. Where does the rule of disjunction apply?
A: A supertype is a generic entity type it has a relationship with one or more than one subtypes. A su...
Q: Computer Science Assume that you have a 3-class problem, and you have computed the cross-validated a...
A: The answer is given below.
Q: Need Network diagram for Student attendance fingerprint system
A: Biometric systems use a student's fingerprints to authenticate his or her identity and keep track of...
Q: Write a recursive function to get count of unique characters in given string or array of characters....
A: Use a set to insert each of the character and thus we don't have duplicates and simply return it's s...
Q: ftware archite
A: Software Architecture: Simply said, software architecture is the way a system is organized. This org...
Q: Your employer has charged you with implementing a risk management program. The CEO has requested you...
A: Security is prevention of unauthorised access into system. Exposure of holes in source code is respo...
Q: True or false 10. To express decimal to percent we simply move the decimal point two places to the r...
A: Decimal numbers are floated value which contains values in decimals.
Q: You will enter a series of integers and I will then tell you the largest and the smallest numbers yo...
A: C++ code to find maximum and min number from entered list #include <iostream> using namespace ...
Q: y are some connections never purely pinned or purely fixed, site examples of these instances. Note...
A: Lets see the solution.
Q: In Python write out the Python Code for the following in Jupiter Lab. Show code and outputs. Use a d...
A: arrow_forward Step 1 In questions with many asks, we must answer first. arrow_forward
Q: 60 seconds B. 1600 seconds C.
A:
Q: 2. As you're troubleshooting a dead zone in your office, which measurement will help you determine t...
A: measurement will help to determine the edge of dead zone
Q: What is printed by the call test_b(4)? А.024 В.0 2
A:
Q: How many comparsions would be needed for merge sort algorithm for these 3 types of arrays and all of...
A: The number of comparisons is 6*log26 - 5
Q: Non-Fungible Token (NFT) 1. What? 2. When? 3. Why?
A: Note: A per our guidelines, we are supposed to answer only the first three subparts. Kindly repost o...
Q: describe 2 advantages of using higher level socket compared to lower level of the network stack
A: advantages of using higher level socket compared to lower level of the network stack
Q: Q5: For the Binary search tree given below. 30 15 60 7 22 45 75 17 27 In-order Travetrsal Pre-Order ...
A: In Inorder traversal, the root is traversed in between the left and right subtrees and the same rule...
Q: Convert the following ER diagram into relational schema. Write the relational schema in SQL.
A: An entity relationship model (or ER model) describes interrelated things of interest in a specific d...
Q: You are provided with an array that contains different characters. Ask the user for an integer input...
A: INTRODUCTION: In the given problem statement we are asked to complete the code so that if user input...
Q: Write a program that contains two classes a Main class and a Student class: • • The Student class ha...
A: I give the code in Java along with output and code screenshot
Q: Basic concepts and benefits behind computer networks (Discuss the basic concepts behind compute...
A: Basic concepts and benefits behind computer networks are
Q: What is the process through which a virtual network interface card (VNIC) obtains a MAC address?
A: Defined the process through which a virtual network interface card(vNIC) obtains a MAC address
Step by step
Solved in 2 steps

- In Lesson 3 of this module you learned about cloud and fog computing. There is more—something called mist computing. Do some research on the net and explain what it is in relationship to cloud and fog computing. Note: This question relates to Module 3 - Lesson 3.Exist on the market any desktop operating systems? Determine the differences between macOS, Windows, and Unix-Linux.?How do the following terms apply to Windows 10? (If the term/s don't apply, put N/A) DMA I/O subsystem Device status table Block/Character device Network device CPU- control I/O
- What kinds of operating systems are there for desktop computers? Explain the differences between macOS, Windows, and Unix-Linux.3.Name two application-level communication services 4.What is the relation between a physical clock and a logical clock?A central computer surrounded by one or more satellite computers is called a star network why?

