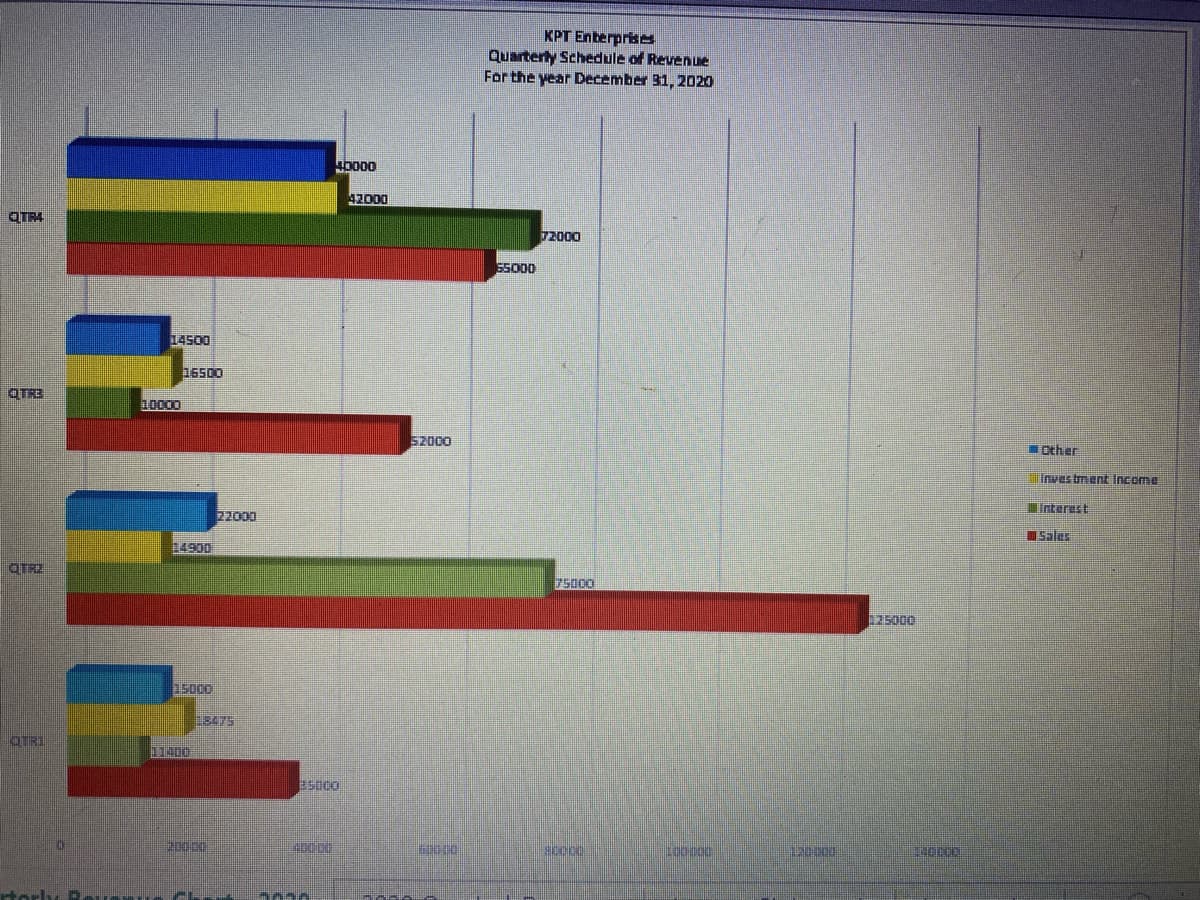
QTR4 TR3 TRZ TR1 14500 10000 16500 22000 14900 15000 18475 11400 40000 85000 42000 52000 60000 KPT Enterprises Quarterly Schedule of Revenue For the year December 31, 2020 72000 55000 75000 80000 120 000 125000 140000 Other Investment Income interest Sales
Q: What impact will AI have on the world? Now, which artificial intelligence-based software programmes…
A: INTRODUCTION: Artificial intelligence is a part of science where robots, especially PC frameworks,…
Q: Are there any steps you can take to guarantee that the source-control system is properly entered…
A: Source control system:- Source Control System is an important scheme that makes it possible,…
Q: For what reason do you still believe that encryption is the most effective means of safeguarding…
A: The answer is given in the below step
Q: Describe the firewall's function in network security. Remember to explain the phrase and offer…
A: let us see the answer:- Introduction:- An organization's previously set security policies are used…
Q: "\n" (called slash n) is used to print "enter". Try the following set of statement adding your name…
A: Since name and id are not mentioned, I am taking them as: name: Rene id: 111…
Q: Q.65 WAP to plot sine and cosine value by subplot() function.
A: As per the question statement, We need to write MATLAB code.
Q: use java to ; a. request for only name and rank to be entered into the system b. display results…
A: As per the question statement, We need to write JAVA program.
Q: Oracle 12c: SQL The JustLee DB contains a table called PROMOTION. It does not have any of the…
A: CREATE TABLE [Persons] ([Id] [INT] PRIMARY KEY, [Name] [VARCHAR](50) NOT NULL, [SurName]…
Q: Can you tell the different kinds of firewall designs apart?
A: Firewall Architectures: True demilitarise zone. Authentic DMZ designs are often considered the most…
Q: Could malware be considered a threat actor?
A: Considered a threat actor A threat actor, also known as a malicious actor, is a person or a group of…
Q: In a catch block, there is no limit to the amount of arguments that may be used.
A: Introduction: A typical sort of blunder that a modified could experience is a consistent mistake,…
Q: Identify and describe in a sentence or two a control for each of the following cells of the McCumber…
A:
Q: Is there a way to prevent tampering with class fields?
A: Protecting fields against corruption by mistake: There are two approaches to protecting class…
Q: 5) Given the input bits are 000110101001, sketch the output of a BPSK, QPSK. SPSK and 16PSK…
A: BPSK: library IEEE;use IEEE.STD_LOGIC_1164.ALL;use IEEE.STD_LOGIC_ARITH.ALL;use…
Q: Based on "Why computers are so powerful," incorporate the four attributes of a computer into today's…
A: Why computers are so powerful? A computer is a powerful tool because it is able to perform the…
Q: A description of how Moore's Law influences an organization's ability to manage IS and what an…
A: According to Moore's Law, a single microchip's computer capacity should double every two years as…
Q: Explain the difference between the following with simple example 1. plot and plot3. 2. H1 line and…
A: 1) plot :- Creates a 2-D line plot of the data in Y versus the corresponding values in X. plot3…
Q: Are there several kinds of malware? What is the difference between worms and viruses? Viruses and…
A: The Answer is in given below steps
Q: In general, there are two basic kinds of software products. Using one example, describe them (s).
A: Introduction: The primary classifications of software productsGeneric software and software that has…
Q: Do data breaches have any impact on the cloud's security? Do you have any notion what kind of…
A: Given: Theft of data, ransomware, phishing, guessing of passwords, viruses, malware,…
Q: Organizers of the Army Land programs, people have already started preparing for the upcoming sports…
A: Coded using Python 3.
Q: B) Use "solve" function to solve the following equations and "double" function to put the results in…
A: As per the question statement, We need to write MATLAB code.
Q: In what circumstances would it be appropriate to make the assumption that two select statements…
A: The question is about under conditions we could able to perform union operation for the two select…
Q: Q. what are the tyoes of code cloning in software cloning?
A: Code cloning:- Code cloning in software cloning is making use of pre- written code. Code cloning is…
Q: Give examples to show at least two different ways to select subset of columns from a dataframe data…
A: As per the question statement, We need to provide two different ways to select subset of columns…
Q: Create a simple payroll program that applies object-oriented concepts. create a console application…
A: As no programming language is mentioned, it is solved using Java
Q: Local declarations are those that are stored in the computer's memory, but how are they stored?…
A: Answer: Local Variables: A variable defined within a block or method or constructor is called a…
Q: 4. Consider the following graph. Apply Kruskal’s algorithm to find the minimum spanning tree and…
A: Kruskal algorithm is used to find the minimum spanning tree for a graph. To apply kruskal algorithm,…
Q: the time variation database system will be discussed.
A: The solution to the given question is: Time Variant of Database System A system is said to be time…
Q: Q2\ By using Adjoint method, find the inverse of the following matrix. [1 0 -31 Matlab A=4 2 -1 LO 3…
A: Code: A=[1 0 -3;4 2 -1;0 3 2]% Inverse of matrix using adjoint method is A^-1=(1/|A|)*adjoint(A) %…
Q: Q5/ Select the correct answer of the following: 1. Which of the following statements is correct? a)…
A: Find the required answer with explanation given as below : As per company guidelines we are supposed…
Q: A particle start from the point (4,4) and it's coordinates change by the increment AY=5 and AX= -8…
A:
Q: he von N
A: Von Neumann and Harvard architecture are known to be the two basic models on which computer systems…
Q: A symmetric block cipher's hardware components may be summarised as follows: Explain each of the two…
A: A symmetric block cipher's hardware components may be summarised as follows: Explain each of the two…
Q: se are the frequent item S sample transactions,
A: The source code is shown as,
Q: Is there a limit to the number of ways functions may interact with one another? Using relevant…
A: Lets see the solution in the next steps
Q: CUSTOMER Customer ID Customer Name Customer Contact No ORDER Order No Order Date Order Total Mode Of…
A: Following is the EER diagram of the given diagram
Q: algorithm
A: Given :- In the above question, a weighted graph is mention in the above given question Need to…
Q: atabase ma
A: Database Management System (DBMS): Database Management System (DBMS) is a software that allows…
Q: Write a C program that compares two given dates. To store a date use a structure that contains three…
A: #include<stdio.h> #include<stdbool.h> // defining a structure to…
Q: In a system, the analog sange ism tow (where MCN) and there is I byte in the digited Sistery. If the…
A: the solution is an given below :
Q: Assume your company's mail server sends you an email warning you that your password has been…
A: Phishing Attack: Phishing is sending fraudulent messages that appear to originate from a reputable…
Q: Database designs may be divided into two or three levels based on their specific needs, as is widely…
A: Given: According to their needs, database architectures might have two or three layers.…
Q: Write a python program to find the number of occurrences of each word in a text file. The first part…
A: Read line by line and then word by word then we convert to any of uppercase or lowercase to compare
Q: A symmetric block cipher's hardware components may be summarised as follows: Explain each of the two…
A: Utilizing a single key, symmetric encryption scrambles (encodes) and unscrambles (interprets)…
Q: Develop a program that calculates the total score and the average score for Quiz and classwork…
A:
Q: Are there any issues with using adjacency lists to depict a weighted graph?
A: Adjacency List: Adjacency is nothing but a collection or set of the unordered list that is generally…
Q: Oracle 12c: SQL Chapter Two Textbook Assignment Q1 Create a report showing ALL data from the…
A: SQL is the structured Query Languages is used as the standard programming languages that are used to…
Q: Software and hardware firewalls differ? Who wins? Which is appropriate?
A: A hardware firewall protects you from the outside world, whereas a software firewall safeguards a…
Q: Draw the package diagram for E voting system subject: SDA
A: Lets see the solution in the next steps
Step by step
Solved in 2 steps

- The following table shows a list of pets and their owners that is used by a veterinarian service. P_Name Type Breed DOB Owner O_Phone O_E-mail Kino Dog Std. Poodle 3/27/97 M. Downs 5551236 md@abc.com Teddy Cat Chartraux 4/2/98 M. Downs 1232343 md@abc.com Filo Dog Std. Poodle 2/24/02 R. James 2343454 rj@abc.com AJ Dog Collie Mix 11/12/95 Liz Frier 3456567 liz@abc.com Cedro Cat Unknown 12/10/96 R.James 7865432 rj@abc.com Woolley Cat Unknown 10/2/00 M. Trent 9870678 mt@abc.com Buster Dog Collie 4/4/01 Ronny 4565433 ron@abc.com a. Describe 4 problems that are likely to occur when using this table. b. Break the table into two tables in a way that fixes the four problems.INSTRUCTIONS Using spreadsheet software enter the following table below that shows thenumber of tourists visiting the following countries over a five-year period. UseTimes New Roman and Font size 12. Name the worksheet Table. COUNTRIEsS 2014 2015 2016 2017 2018‘000 ‘000 ‘000 ‘000 ‘000Grenada 350 465 375 250 485Antigua andBarbuda 153 160 155 149 256Barbados 573 625 725 680 740St. Kitts 347 515 538 178 384St. Lucia 600 436 368 535 858Trinidad andTobago 379 563 475 415 563Jamaica 416 200 500 300 475Bahamas 300 450 550 460 470Aruba 208 367 415 500 684Dominica 135 317 279 350 465 Insert a column to the right of the table with the heading “Total Visitors”. Inthat same column compute the total number of tourists that visited eachcountry over the years. Insert a row heading Maximum to show the maximum number of visitors foreach given year. Sort the data in ascending order based on the Countries. Insert a row heading Minimum to show the minimum number of visitors foreach given year. …CUSTOMERColumns = 7, Rows = 10 CustomerID LastName FirstName Address ZIP Phone Email 1 Shire Robert 6225 Evanston Ave N 98103 206-524-2433 Robert.Shire@somewhere.com 2 Goodyear Katherine 7335 11th Ave NE 98105 206-524-3544 Katherine.Goodyear@somewhere.com 3 Bancroft Chris 12605 NE 6th Street 98005 425-635-9788 Chris.Bancroft@somewhere.com 4 Griffith John 335 Aloha Street 98109 206-524-4655 John.Griffith@somewhere.com 5 Tierney Doris 14510 NE 4th Street 98005 425-635-8677 Doris.Tierney@somewhere.com 6 Anderson Donna 1410 Hillcrest Parkway 98273 360-538-7566 Donna.Anderson@elsewhere.com 7 Svane Jack 3211 42nd Street 98115 206-524-5766 Jack.Svane@somewhere.com 8 Walsh Denesha 6712 24th Avenue NE 98053 425-635-7566 Denesha.Walsh@somewhere.com 9 Enquist Craig 534 15th Street 98225 360-538-6455 Craig.Enquist@elsewhere.com 10 Anderson Rose 6823 17th Ave NE 98105 206-524-6877 Rose.Anderson@elsewhere.com EMPLOYEEColumns = 5, Rows = 5 EmployeeID LastName FirstName…
- CUSTOMERColumns = 7, Rows = 10 CustomerID LastName FirstName Address ZIP Phone Email 1 Shire Robert 6225 Evanston Ave N 98103 206-524-2433 Robert.Shire@somewhere.com 2 Goodyear Katherine 7335 11th Ave NE 98105 206-524-3544 Katherine.Goodyear@somewhere.com 3 Bancroft Chris 12605 NE 6th Street 98005 425-635-9788 Chris.Bancroft@somewhere.com 4 Griffith John 335 Aloha Street 98109 206-524-4655 John.Griffith@somewhere.com 5 Tierney Doris 14510 NE 4th Street 98005 425-635-8677 Doris.Tierney@somewhere.com 6 Anderson Donna 1410 Hillcrest Parkway 98273 360-538-7566 Donna.Anderson@elsewhere.com 7 Svane Jack 3211 42nd Street 98115 206-524-5766 Jack.Svane@somewhere.com 8 Walsh Denesha 6712 24th Avenue NE 98053 425-635-7566 Denesha.Walsh@somewhere.com 9 Enquist Craig 534 15th Street 98225 360-538-6455 Craig.Enquist@elsewhere.com 10 Anderson Rose 6823 17th Ave NE 98105 206-524-6877 Rose.Anderson@elsewhere.com EMPLOYEEColumns = 5, Rows = 5 EmployeeID LastName FirstName…GIFT MINRETAIL MAXRETAIL--------------- ---------- ----------BOOKMARKER 0 12BOOK LABELS 12.01 25BOOK COVER 25.01 56FREE SHIPPING 56.01 999.99 CREATE SEQUENCE data above for ocale sqlstudent Relation Student_ID Student_Name Dept_Name 0000 AAAAA Computer Science 1111 BBBBB Computer Science 2222 CCCCC Business Administration 3333 DDDDD Education 4444 EEEEE Physics 5555 FFFFF History Student_Courses Relation Student_ID Course_ID Section Year Grade 0000 CS 2203 2 2020 A 0000 CS 1101 1 2019 A 1111 CS 1101 5 2019 B 1111 CS 1102 1 2019 B 1111 CS 2204 1 2020 A 1111 CS 2401 1 2020 A 2222 BUS 1101 3 2019 C 2222 BUS 2201 1 2020 B 2222 BUS 3302 1 2020 B 3333 EDUC 5010 1 2019 A 3333 EDUC 5210 1 2020 B 4444 PHY 1101 4 2019 A 4444 PHY 2202 1 2020 C 4444 PHY 3304 1 2020 A Considering Student and Student_Courses relations shown above, discuss when Union, Inner Join, Left Outer Join, Right Outer Join, and Full Outer Join should be used and provide examples using the above relations. I AM GETTING USED TO MYSQL WORKBENCH. (Kindly take me through the path)
- 2.Compute the item endorsement index for BRS Item 3. __________ ID # Item 1 Item 2 Item 3 Item 4 Item 5 Item 6 BRS Total Score 25 5 5 5 5 5 5 55 24 5 5 2 4 5 5 50 21 5 4 5 3 5 5 48 22 5 5 4 3 3 4 46 23 5 3 3 5 5 2 46 18 4 5 5 4 4 4 44 20 5 5 4 3 3 4 44 16 5 4 5 5 4 3 42 19 4 5 4 1 4 4 41 9 5 5 4 5 5 5 38 10 5 5 4 4 4 4 36 13 2 4 3 5 4 5 36 7 3 5 5 5 5 5 35 11 5 3 3 5 3 4 34 15 4 3 3 1 3 5 34 4 5 5 4 5 5 5 33 17 1 2 2 4 5 2 33 2 5 5 5 5 5 5 32 5 4 5 4 4 5 5 32 12 4 4 1 4 4 2 31 8 3 4 3 3 3 3 27 6 4 3 3 2 4 4 26 14 2 1 2 2 2 3 26 3 5 4 4 4 2 3 25 1 1 3 2 3 3 3 16Given the following XML file student.xml <?xml version="1.0" encoding="UTF-8"?> <Myclass transacted= ”123”> <studlist> <student Rating= “average” > <firstName>John</firstName> <lastName>Smith</lastName> <email>jsmith@gmail.com</email> <mobile>0211223344</mobile> </student> <student Rating= “top 10” > <firstName>Ali</firstName> <lastName>Faizal</lastName> <email>ali@gmail.com</email> <mobile>0211223345</mobile> </student> </studlist> <Details> <location>Block15</location> <floor>First</floor> <roomno>909</roomno> </Details> </Myclass> Write an DTD document for the above xml file. What is the document root?uint16_t data = wiringPiI2CReadReg16(adc, 0x00); low = (data & 0xFF00) >> 8; high = (data & 0x00FF) << 8; value = (high | low)>>4; return value; I know this stables the value some how but how and why
- Show transcribed data MSU Corporation Database Department Mgr Start Date 2005-06-19 2013-01-01 1998-05-22 t No Name Headquarters Admin and Records 999555555 Production Mgr SSN 999666666 999444444 Employee EMP SSN FName Nme Address City State Zip DOB Salary Park Gender Dep |Super SSN t No ing Space 99Bock Dougl 1955 09-01 30000 542M St. Louis MO 63121 7 999444444 Dr 1969- 03-29 999222222Amin HyderSeaside Marina CA93941 Collinsville IL 66234 Waiman Lindber St. Louis MO 63121 3999555555 7 999444444 7 999666666 25000 422 M Apt. B #10 Oak St. 303 999333333 Joshi Dinesh 38000 332 M 09-15 1975 12-08 43000 32 999444444 Zhu 202 999555555 Joyner 1971 06-20 430003 CA 93941 Suzanne Burns Marina arm Chapter 8 Homework Answer the questions below. In doing this homework, you don’t have to use a DBMS. If you didn’t create MSU Corporation datanase to do Chapter 7 homework, you can use the table information in “MSU Corporation Database” document attached. If you want to create the database now, use…Following script is given to you at Google Classroom. Run script to generate tables inOracle APEX. EMP (EMPNO, ENAME, JOB, MGR, HIREDATE, SAL, COMM, DEPTNO)DEPT (DEPTNO, DNAME, LOC)SALGRADE (GRADE, LOSAL, HISAL)dont dont dont copys trict verystcrcity report

