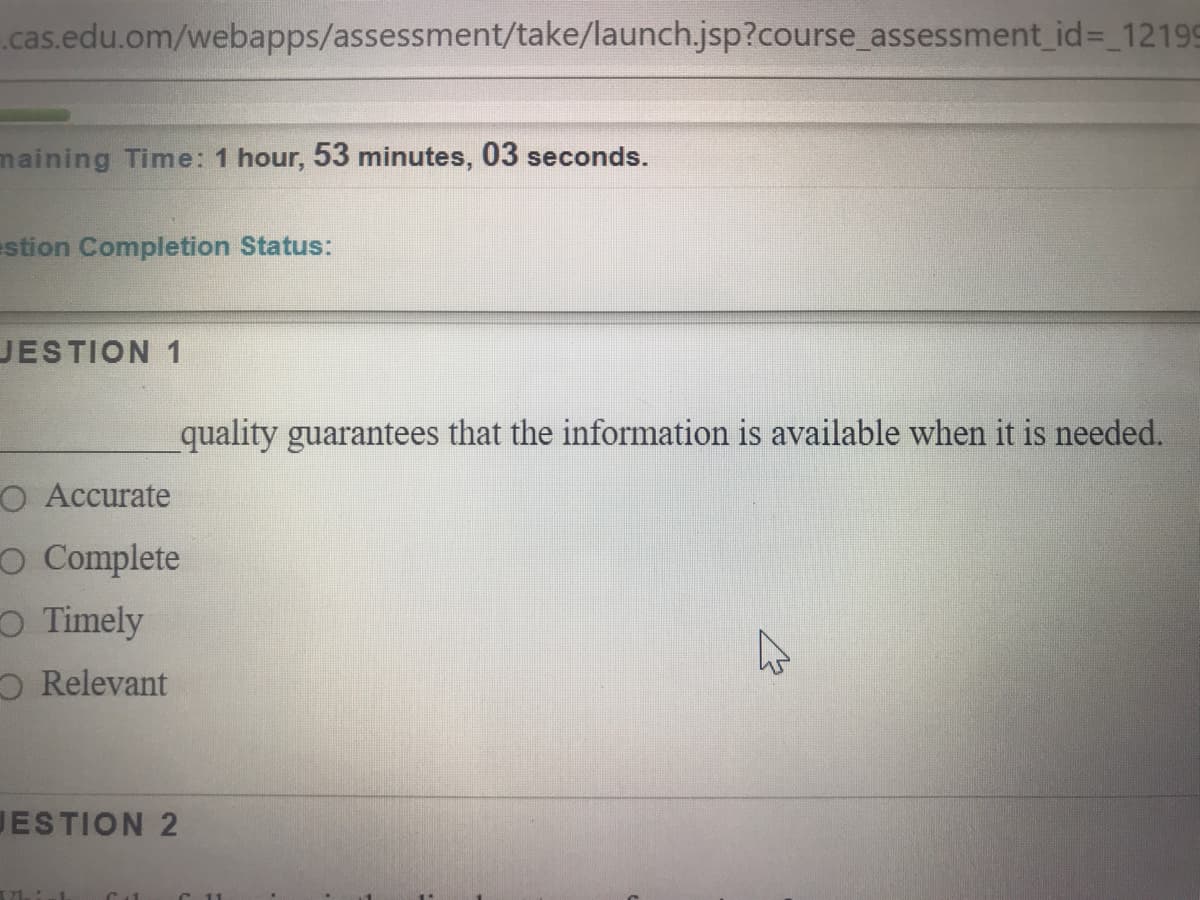
quality guarantees that the information is available when it is needed. Accurate Complete Timely Relevant
Q: CASE: WebSpective Software, Inc. Objectives of the case: - Understand the company’s…
A:
Q: Review and contrast the following IT strategic roles: IT Strategic Role Automated, Top-Down…
A: The answer is given in the below step
Q: TASK DESCRIPTION: Entrepreneurship represents an important career option, it offers opportunities to…
A: Solution:-- 1)The given question is related with the passage question as some of the task…
Q: Along with company information, professional experience, skills set, and qualifications, the salary…
A: Here we have given options to the multiple questions asked with explanation. You can find the…
Q: The role of the user in the Information Systems audit department
A: I have provided a solution in step2.
Q: Information Technology audits are used to examine and evaluate organization systems internal control…
A: The Answer is in step-2.
Q: Describe the functions and responsibilities of a system auditor.
A: Introduction: Conducts information control evaluations on system development standards, operating…
Q: List the steps in a typical recruiting process. Highlight the steps that involve interaction with…
A: Recruitment is a process of finding and attracting the potential resources for the finding and…
Q: Scenario: Your company has been tasked with the development of a university information system for…
A: Elicitation Techniques: Observation: Benefit: You can sort out exactly where users are at the start…
Q: Describe specific skills and knowledge and techniques student will learn or apply in an IT HELP DESK…
A: The following solutions are
Q: Software Functionality: Download a Great Plains software demo programme and analyse its accounts…
A: Intro The intense completion and fluctuating sales forced the vendors of enterprise resource…
Q: Information requirements of an organization can be determined by Select one: O a. sending a…
A: GIVEN: Information requirements of an organization can be determined by a. sending a questionnaire…
Q: explain how you will go about creating and preparing for a presentation as a business analyst
A: This is very simple. When communicating requirements to stakeholders, this is how we need to prepare…
Q: Utilize technology and information resources to conduct investigations into information system…
A: Introduction: The Agency for Healthcare Research and Quality financed its first medical informatics…
Q: TASK DESCRIPTION: Entrepreneurship represents an important career option, it offers opportunities…
A: ANSWER:-
Q: Scenario: Your company has been tasked with the development of a university information system for…
A: I have answered this question in step 2.
Q: cenario: Your company has been tasked with the development of a university information system for…
A: Answer :
Q: Case Study: University Malaysia Pekan is plan to develop Learning Management Systems (LMS e.g:…
A: We are not allowed to provide direct link to websites according to bartleby policy. so i will…
Q: Scenario: Your company has been tasked with the development of a university information system for…
A: ANSWER:-
Q: Explain what critical tasks you would recommend being included in an information security program…
A: Information security program: The InfoSec programme is used to create, implement, and maintain an…
Q: Discuss some of the trends and emerging issues that are present in professional issues
A: Patterns and arising issues in business morals Corporate social duty It has gotten a manner by…
Q: Explain how technological improvements have benefited in improving organizational communication.
A: Today's firms place a high value on the relationship that exists between communication and…
Q: rmation resources to research the difficu
A: Introduction: Below describe the Utilize technology and information resources to research the…
Q: Keeping policy current is critical. Discuss how policy needs to be updated to accommodate current…
A: Policies form the building block of any industry or organistaion. Without a policy organistaion…
Q: Quality assurance is a set of practices that are used to ensure that our results are accurate and…
A: Quality Assurance is a process of analyzing the product before its delivery
Q: career guidance offices job portals marital status verification convincing skills interpersonal…
A: Fill in the blanks:- ----placement agencies--------------- usually provide a paid service to two…
Q: infusion is a measure of how widely technology is spread throughout an organization
A: Please find the answer below :
Q: Scenario: Your company has been tasked with the development of a university information system for…
A: We need to identify and list the relevant project stakeholders.
Q: Describe the certification and training process and provide particular examples from your…
A: Training is an activity that teaches workers fundamental job skills. Continuous endeavour to…
Q: In elicitation technique, Questionnaire must be prepared. Interview users Examine source documents…
A: Lets see the solution.
Q: What would you call an individual who documents all the issues, problems, and open points that were…
A: INTRODUCTION: THIS IS OBJECTIVE QUESTION TYPE - CHOOSE OPTION ONE AND EXPLAIN THIS BELOW IN STEP 2
Q: Management information systemsa. collect data, hire personnel, and evaluateworkers.b. store data,…
A: Management information systems Management information system is a computer system that consists of…
Q: Creating an environment in which individuals, working together in groups, can accomplish well-…
A: The process of finding the right worker with relevant qualifications/experience and recruiting them…
Q: Define the components of information literacy. List steps in effective research and composition
A: To be determine: Define the components of information literacy. List steps in effective research and…
Q: 7. Implementing Software Metrics in an organization should be relatively easy to do. True False…
A: The solution to the given problem is below.
Q: Customer Support, Inc. (CSUP) is a large corporation with international clients that provides…
A: This object must have a uniqueId instance variable. Need all getters and setters and toString…
Q: Computerized information systems. On a typical client project, staff from Jobel Consultancy Company…
A: Management Information systems is referred as the informations systems that are used in the decision…
Q: What are the advantages and disadvantages of the interview elicitation approach?
A: The approaches that are used for producing or generating a reaction from the other person are termed…
Q: If something is not clear in the description and you need to make assumptions to make a decision,…
A: Answer :
Q: A portfolio highlighting your college experience is a useful tool during the job search process (and…
A: The answer is given below:-
Q: Research your desired field of study and explore what additional skills you will need will boost…
A: The following skills are required to boost employability and salary in the field of Computer…
Q: CASE: Change Management for ERP System Project You are a member of the human resources organization…
A: Actually, project is a series of tasks that need to be reach a task.
Step by step
Solved in 2 steps

- Using the DBMS 130 Course Project ERD and Table Details spreadsheet, develop an APEX script to CREATE the 6 tables and all the constraints (PK, FK, NOT NULL, etc.).Add these two constraints to the FLIX_MOVIES table1. Movie Rating can only have these values: a. Gb. PGc. PG13 or PG-13d. R2. Movie Category can only have these valuesa. DRAMAb. COMEDYc. ACTIONd. SCIFIe. DOCUMENTARYWhich of the following is the most sensitive IS that impacts the accuracy/quality of reports? ESSDSSMISTPS 2)Data warehouses are redundant and not normalized. *0/2TrueFalsedont dont dont copys trict verystcrcity report
- Design the layout of users, domains, trusted domains, anonymoususers, etc for a start-up open source software company ABC. Theyshould have an internal CVS server, which only internal developerscan access, an anonymous CVS server for outsiders to downloadsource code, WWW servers (one for internal and one for external),and a mail server. Outsiders should not be able to access eitherinternal CVS or internal WWW servers..You should finish the following parts:a) The topology diagram for the different servers and locations andtrust domains. For example, where are the firewalls, and whereare the users located in the topology.b) The assumptions that you make for your design and the securitypolicy to achieve this assumption Your final document should include the following parts:1. Network topology diagram and the domains of trust.2. Security related assumptions in your design, and security policy tomake this assumption valid.3. Trust assumptions about users (e.g., who could be root, what…Which data retention policy addresses how long data must be retained to meet regulatoryrequirements?A. RetrievalB. ClassificationC. FormatsD. PeriodsHello, can you please assist with the following problem? Q1.Using the DBMS 130 Course Project ERD and Table Details spreadsheet, develop andrun an APEX script to CREATE the 6 tables and all the constraints (PK, FK, NOT NULL,etc.).Q2.Add these two constraints to the FLIX_MOVIES table1. Movie Rating can only have these values:a. Gb. PGc. PG13d. PG-13e. R2. Movie Category can only have these valuesa. DRAMAb. COMEDYc. ACTIONd. SCIFIe. CHILDf. DOCUMENTARYQ3.Add a UNIQUE constraint to the Email column of FLIX_CUSTOMERS.Place comments in your script including course number, date, your name, and otherrelevant comments.In APEX, name your script:Course_Project_Part_1_yourInitials.sqlNOTE: Each script name must be unique in APEX. That is why you mustuse your initials in the name of your script. Otherwise, you will receive anAPEX error.
- dont dont dont post existing one posting multiple times report for sure else skipThe Great Bear Lodge is a hotel with an adjoining indoor waterpark and indoor minature golf center. The hotel sells packages which include overnight hotel stays with waterpark passes and minature golf passes. The hotel also has a plicy of selling daily passes to the indoor waterpakr and daily passes to the indoor minature golf center (in other words people do not need to stay at the hotel to use the indoor waterpark or indoor minature golf center.) Hotel guests may also choose to reserve just a hotel room without purchasing the waterpark or minature golf center passes. Great Bear Lodge is offering an incentive for the month of April. They are offering a package in which guests who reserve an overnight stay with the waterpark pass package will receive a free pass to the minature golf center. The total price for this package is $225 per night. The typical pricing for each of these sold independently are: One night hotel stay: $180, Daily Waterpark pass: $90, Minature Golf…Choose the correct answer from the following : UTAS Nizwa ETC department is planning to publish the final exam term results using UTASwebsite It is decided to keep two text boxes, one submit button and one reset button, Withrespect to the 3-tier client server architecture which type of service itis. 1- Data validation 2- Request / Response architecture 3- Domain range validation 4- Data Security 5- graphical user interface
- If you were analysing the architecture of a shopping cart on an eCommerce website that has interfaces to a banking app for credit card processing and a Shopify inventory management service, you would expect to find: Rest API's for transfering credit card and inventory data on URI's in plain text API's implementing platform web services for the Bank and Shopify connections using WSDL Synchronised, sharded databases implementing named pipe connections Cached local SQL mirrors of the Bank and the Shopify data sets for the eCommerce sitecreate a project web angular with bootstrap Bootstrap part: The project must contains - Grid System - Table - Forms - Jumbotron - Cards - Navbar Angular part: at least 4 components (required), routing (required), data services (required), data binding (required), event binding and pipes (required). please give me the project in drive or write code here but drive is bestI need some help with a little mysql coding. Here is the short description... A Database Story: Backup then Recovery [NG] Author: Daniel KillamFramework Category: Operate and MaintainSpecialty Area: Network ServicesWork Role: Network Operations SpecialistTask Description: Develop and implement network backup and recovery procedures. (T0065)Scenario It seems that our new intern has deleted some important database files needed for an upcoming project. This incident has caused us to realize that we are severely lacking in our standard recovery and backup procedures. As such , we need you to design and implement a plan for backing up and restoring data critical to our business. After designing these procedures, they need to be tested in order to ensure their functionality. Additional Information More details and objectives about this challenge will be introduced during the challenge meeting, which will start once you begin deploying the challenge.You will be able to check your progress…





