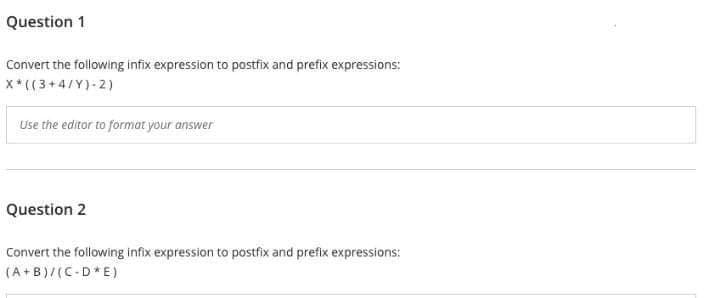
Question 1 Convert the following infix expression to postfix and prefix expressions: X*((3+4/Y)-2) Use the editor to format your answer Question 2 Convert the following infix expression to postfix and prefix expressions: (A+B)/(C-D*E)
Q: Many of the cornerstones of software engineering are missing. Explain?
A: First, a high-level summary of software development: Software engineering combines software with…
Q: Compress the following IPv6 addresses into their shortest expression…
A: Compress the following IPv6 addresses into their shortest expression…
Q: I'm not sure what you mean by "network security." Define how the data encryption standard works.
A: Definition: Network security, in general, refers to the measures taken by any company or…
Q: Question 27 For FY21Q2, which mobile device branding generated the most Revenue? A Samsung (B)…
A: According to the information given:- We have to choose the correct option to satisfy the statement.
Q: How do you want legacy systems to evolve in the long run? When will it be more economical to replace…
A: Legacy systems will continue to be updated and maintained, but may eventually be replaced if it is…
Q: Analyze the significance of wireless networks in today's emerging nations: Over the last several…
A: WLANs link two or more devices wirelessly. communication to create a local area network (LAN) in a…
Q: If you're going to explain how the internet works, why not go ahead and list all the components that…
A: The internet is a global network of interconnected computers, servers, and other devices that…
Q: If you're going to explain how the internet works, why not go ahead and list all the components that…
A: HOW THE INTERNET WORKS: The computer network known as the internet is described as transmitting…
Q: In this post, we will discuss the bool data type and logical (Boolean) expressions
A: Boolean Data Type: Boolean data types are used to hold either True or False as a value. One…
Q: In a computer network with a star topology, each node is connected to the hub through cables.
A: In computer network architecture, each node is linked to a central device hub.
Q: The Issue: How do you properly document the API of a library you've written? Oualline's Law of…
A: Oualline's Law of Documentation: Oualline's Law of Documentation states that "If a feature has a…
Q: Wireless networks are becoming more important in today's developing countries, especially in Africa.…
A: 1. A computer network refers to interconnected computing devices that can exchange data and share…
Q: Write HTML code to create following table. Also set its border color to “red”
A: For creating the required table with merged cells, we will be employing the concept of rowspan and…
Q: Give a brief explanation of source data automation (SDA), highlighting its at least two (2)…
A: Introduction: SDA: Source Data Automation The process of acquiring digital values at the source and…
Q: The Instruction Set includes a number of different kinds of instructions of their own. Walk me over…
A: Let's examine the answer : A computer with fewer instructions (RISC) : Reduced Instruction Set…
Q: Where do other fields of study have similarities to computer science? Where do they stand in terms…
A: Start: The study of computers and algorithmic processes, including their underlying concepts,…
Q: To what extent do computers aid scientific investigation? Convince the reader by using specific…
A: Computers have revolutionized scientific investigation by providing researchers with powerful tools…
Q: Decrypt the message MAXLJGTEAX which was encrypted using the affine cipher: Alphabet: A = 0, B = 1,…
A: Given : We have to Decrypt the give message MAXLJGTEAX Which was encrypted Using affine cipher :…
Q: To what extent should several points of view be included when modeling software systems?
A: Software systems modeling refers to the process of creating abstract representations of a software…
Q: What are the three things you need to do when working with classes that include pointer variables as…
A: Introduction of object-oriented programming: Object-oriented programming is a programming…
Q: Recite the four steps involved in the Linux boot and starting process.
A: An operating system is a programme that runs application programmes and acts as a communication…
Q: Do students have access to a network while in school? How does this one measure up when compared to…
A: Examine Ubuntu's performance versus other popular Linux distributions: Linux kernel-based Ubuntu.…
Q: Can you explain the pre-requisites for Deadlock Prevention to operate?
A: What prerequisites must be satisfied for deadlock prevention to work? Critical Circumstances To…
Q: Where does Linux stand when it comes to protecting its data? (Referring to the show itself)
A: File protection: how does Linux implement it? CS Linux was created on MINIX. Linux was based on…
Q: Because the FAT file system is not present in Linux, all of the data stored on a disk may be…
A: The query was: How are disc blocks accessible if the Linux operating system does not support the FAT…
Q: But under what circumstances does preventing deadlock save more money than allowing deadlocks grow…
A: An operating system is a programme that runs application programmes and acts as a communication…
Q: Evaluate Ubuntu's speed in comparison to that of other Linux distros. My strong convictions have…
A: Users may modify Linux, a powerful and efficient operating system. You know that Linux apps are…
Q: xplain and write down the advantages and disadvantages of Embedded SQL in SQL queries!
A: Advantages of Embedded SQL: Increased functionality: Embedded SQL allows you to execute SQL…
Q: The following C code containts a significant error in its use of pointers. Describe this error and…
A: According to the information given:- We have to follow the code mention in order to fix it.
Q: How to answers above questions?
A: Refer the answer below for above asked questions:
Q: How does one go about creating such computer programs? How many different methods are there?
A: Introduction: The elements of the programming design are as follows: Recognize the coder and do the…
Q: MAXLJGTEAX which was encrypted using the affine cipher:
A: The answer is
Q: Why is it crucial to have a systems analyst on board throughout the building of a system?
A: A systems analyst plays a crucial role in the building of a system as they are responsible for…
Q: Is there a limit on the size of a user ID?
A: Introduction: Variable, function, structure, and other things have identifiers. Because it uniquely…
Q: When it comes to the loT, what kinds of attacks have we seen recently?
A: IoT- the Internet of Things, refers to the overall network of interconnected devices and the…
Q: Problems include bad pointers, writing to the end of allotted memory, and memory leaks. When it…
A: 1. Encryption is the study of secure communication techniques that allow only the sender and…
Q: Instruct us on the ways of the arithmetic operators, please.
A: Arithmetic operators accept literals or variables as operands and return a single numerical value.…
Q: One essential component of cloud computing is the capacity to combine and share resources.
A: Cloud computing capitalises on the pooling and sharing of resources to achieve outcomes. The inquiry…
Q: Ubuntu has the edge over other well-known Linux variants. What do you think sets your idea apart…
A: The key differences between Linux and Ubuntu are outlined in the following list of points: Ubuntu is…
Q: Question 9 What cannot be collected by the default Analytics tracking code? A Browser language…
A: The answer is given below step.
Q: but there is no option of 23 msec there is only 7 , 16 and 2 msec
A: Given The total seek time = 13 milliseconds (msec) The total transfer time = 36 msec. Data size = 2…
Q: Many of software engineering's first ideas have been forgotten. Explain?
A: First, a general overview of software development: Software engineering mixes engineering and…
Q: When it comes to the IoT, what kinds of attacks have we seen recently?
A: Kinds of attacks have we seen recently are given in the below step
Q: How can data visualizations employ these five graphical data elements to highlight and contrast data…
A: Visualizing data It visually represents structured or unstructured data in order to convey…
Q: x86 Assembly Language Programming What will be the final value in EDX after this code executes? mov…
A: Answers:- The family of assembly languages known as "x86 assembly language. offers some degree of…
Q: In a few words, please describe source data automation (SDA) and describe at least two (2)…
A: Introduction: SDA: Source Data Automation : Source Data Automation (SDA) is the method of acquiring…
Q: Sharing and pooling resources is key to cloud computing's strategy for getting the job done.
A: Yes, that is correct. Here is a summary of the key points about the role of sharing and pooling…
Q: What options do we have for semantic representations in NLP systems?
A: Introduction of NLP: NLP is a field of AI that focuses on the analysis, comprehension, and…
Q: What sorts of measurements are necessary for software upkeep?
A: There are five types of metrics in software maintenance. Preventive maintenance compliance (PMC) is…
Q: Should the large software be divided into smaller modules, with each module responsible for a…
A: We will comprehend how functions work in C++ and how and why they are employed. This is accurate, so…
Step by step
Solved in 2 steps

- Question 8 Question text The arithmetic expression in postfix form can directly be calculated from left to right. -True -False Question 10 Question text The infix expression cannot be calculated directly because they consider the operator precedence. -False -True Question 15 Question text Which of the following is a postfix expression? a) * + A B - C D b) -10 c) A + B * C d) C A B + -PROGRAMMING LANGUAGE: C++ The following codes are required to run the program [3 CODES IN TOTAL]: dateType.cpp, dateType.h, main.cppEvaluate the following expressions. 4 + 7 / 2 <= 9 - 15 % 6
- data structure please solve it fast in 10 minutesFor each of the following expressions, add a pair of parenthesis (or number) foreach operator to indicate order of precedence. Then evaluate the expression in a seriesof steps, one line for each operation.0 == 1 > 11 % 4 / 2 13 ^ 11 | 14 >> 2 || 5 In C Please! Thank you!C++ data structure Answer both q fast…. Correct answer this time else will give u downvote
- Complete the makeDate functionUsing the following production rules parse the following strings in top-down and buttonupapproach. assignment => ID = expression ; expression => expression + term | expression - term| termterm => term * factor| term / factor| factorfactor => ( expression )| ID| NUMBERi. y = (2*x + 5)*x - 7comment what each line of code does
- Operators used to compare values. It either returns True or False according to the condition. Relational operators Logical operators Bitwise operators Assignment operatorsCreate a First Come First Served algorithm flowchart.Review the following code, find the error in the code: contents = '' infile = 'thefile.txt', 'r') contents = infile.read() infile.close() print(contents)

