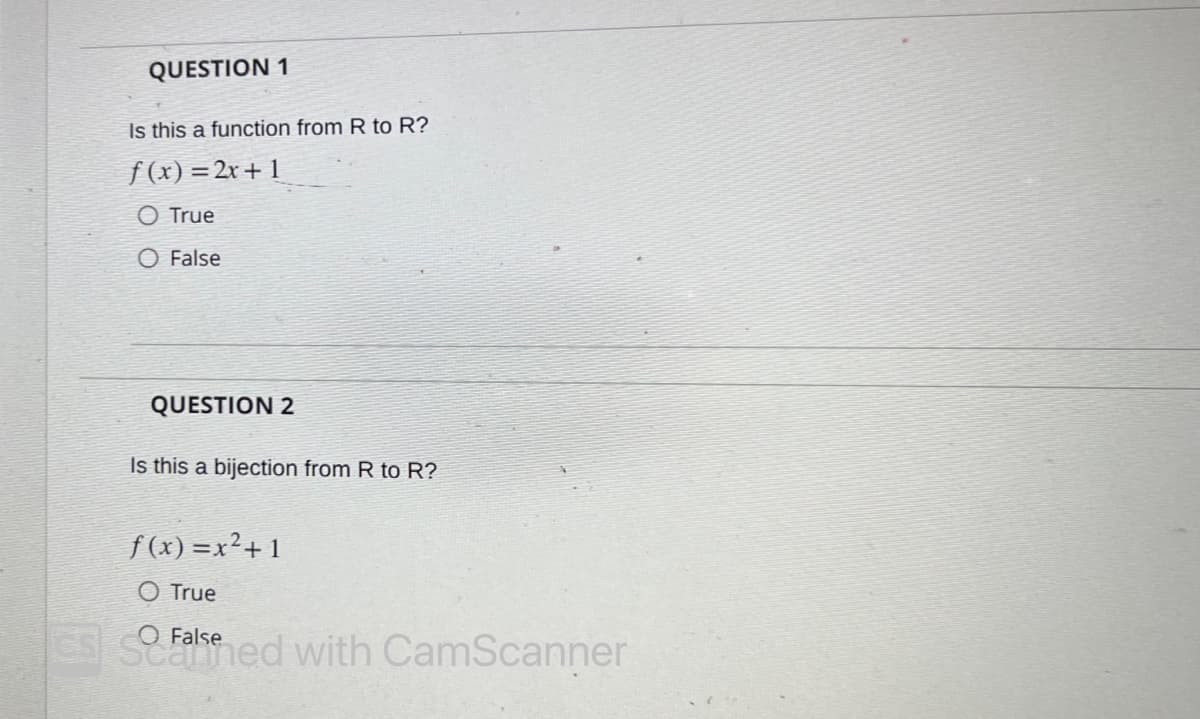
QUESTION 1 Is this a function from R to R? f(x)=2x+1 O True O False QUESTION 2 Is this a bijection from R to R? f(x)=x²+1 O True O CSS Falsened with CamScanner
Q: List 10-15 application that you have encountered or know.
A: Software programs are designed to perform specific tasks or functions on electronic devices such as…
Q: With "Why computers are so powerful?" in mind. Please take into account these four aspects as you…
A: Today's computers are incredibly powerful tools that can be used in the classroom to help students…
Q: A denial of service attack may cause problems for conventional email in many ways. You should…
A: Denial of Service (DoS) attacks can cause significant disruptions to email services, leading to lost…
Q: Create a collection. Along with GETMAX, MAXSTACK offers the ADT commands PUSH, POP, and EMPTYSTACK…
A: Create a collection. Along with GETMAX, MAXSTACK offers the ADT commands PUSH, POP, and EMPTYSTACK…
Q: give 1 example real life or anything example for this common run time complexity: O(1)…
A: O(1) time complexity O(1) represents constant time complexity. It means that the algorithm or…
Q: Explain why you think file extensions are so important. If you like, you may choose three file types…
A: A list of key contrasts between the system development cycle and the system maintenance cycle is…
Q: The attribute of a control, like the attribute of other controls, determines at runtime whether or…
A: A Form Control is a user interface control that serves as a point of interaction. Example, a button…
Q: Find out two future OS consequences that virtualization is anticipated to have and analyze them.
A: Virtualization is the technology that enables multiple operating systems to run on a single physical…
Q: When we say that Direct Memory Access (DMA) has the potential to increase concurrency, what…
A: GIVEN: What part does DMA play in boosting system concurrency? How does it increase the complexity…
Q: When deciding whether or not the waterfall method is right for your project, think about the pros…
A: Consider the waterfall technique's pros and cons in respect to the project in the original article…
Q: Which version of the Waterfall model, the Conventional Waterfall Model or the Iterative Waterfall…
A: The solution is in the steps below:- The numerous hardware resources that may be shared in a…
Q: what is servlet in java
A: As a middle layer between a request coming from a Web browser or other HTTP clients and databases or…
Q: How ransomware work? Provide plagiarism free answer
A: Introduction: Ransomware is a type of malicious software that encrypts a victim's data and demands…
Q: Split the UI/UX divide. Create a catalog of the top methods.
A: Solution: Given, Split the UI/UX divide. Create a catalog of the top methods.
Q: Three major technological companies' websites (Cisco, Oracle, and Microsoft) plus two more of your…
A: Introduction: With the advent of software, security has grown to be a major cause of worry for…
Q: nswer the following questions about the rooted tree shown. For questions in which you need to list…
A: 1) root node - A 2) What is the height of the graph - 6 3) What is the level of H - 2 4) List the…
Q: main.cc file #include #include #include #include "cup.h" int main() { std::string…
A: C++ is an extension of the C programming language, with additional features such as classes,…
Q: Please provide not one but two explanations for why you believe thi
A: Introduction: I understand the significance of a scientist who is trained as a programmer and…
Q: What is procedures in SQL? Provide me plagiarism free answer.
A: What is the procedures in sql: SQL: SQL (Structured Query Language) is a programming language used…
Q: Which version of the Waterfall model, the Conventional Waterfall Model or the Iterative Waterfall…
A: Distributed system hardware resources include the following:(i)Screen\s(ii)CPU Network capacity,…
Q: Provide concrete illustrations of the generalized functions of calls and returns.
A: Function in programming: A function in programming is a block of code that performs a specific task…
Q: Hello can you help me fix this code? these are the errors Exercise10_11.java:34: error: ';'…
A: Define a Circle2D class with three instance variables x, y, and radius. Implement two constructors…
Q: Clarify the potential applications of quantum entanglement in quantum cryptography and remote…
A: Introduction Remote cloning: Remote cloning is a process that enables users to copy files or entire…
Q: Several different forms of virtualization are examined at length (Language, Operating System and…
A: Introduction: Virtualization is a technology that enables the creation of virtual versions of…
Q: Design a stack MAXSTACK, which functions like an ordinary linked stack supporting the ADT operations…
A: We can implement MAXSTACK using a linked list to store the stack elements, and we can also maintain…
Q: In the context of creating software, what are the stages of the waterfall model? Further research on…
A: Definition: A common paradigm used in the system development life cycle to build a system in a…
Q: How many popular operating systems are in use today?
A: Your answer is given below
Q: Changes in technology are unavoidable. Find and analyze five (5) communication or computer-related…
A: Introduction: Computer trends are modifications or advancements in computer use that propagate…
Q: Could you please define and clarify cloud scalability for me? We need to know what factors affect…
A: Given: Please provide a brief description and explanation of cloud scalability. What factors affect…
Q: How Linux may be utilized in rocket technology.
A: Linux, being an open-source operating system, has a wide range of applications in various fields,…
Q: ease help m
A: The function first checks if the stack is empty or has only one element, which is considered sorted.…
Q: This is the present problem due to the tremendous capability found in today's computers. What are…
A: Given: This is a concern since modern computers are so powerful. What factors contributed to the…
Q: Explain in your own words what makes EPROMs and flash memory different from one another.
A: Three words for the digital system's memory are provided. Terms provided: Flash Memory, EEPROM, and…
Q: How l create files in folder in vb net
A: Introduction: In VB.NET, creating files in a folder is a straightforward process that involves using…
Q: How similar (or dissimilar) are the waterfall and incremental methods? I'm trying to understand the…
A: The waterfall and incremental methods are two different approaches to software development, each…
Q: What kinds of network architectures can be put into practice, if any at all?
A: A mesh network's devices are all directly connected to one another on a point-to-point basis. As…
Q: Because of the inherently different nature of wireless networks, they may provide their users with a…
A: Introduction: Wireless networks have become an integral part of modern life, offering users the…
Q: Describe EPROM, EEPROM, and Flash Memory's differences using just your own words.
A: Flash uses NAND-type memory, whereas EEPROM uses NOR. EEPROM erases bytes, whereas Flash erases…
Q: I'd want you to explain the development of computers by naming two contributing elements.
A: The development of computers has been a long and complex process that has involved a multitude of…
Q: If you're arguing for or against the use of a particular machine learning model, be sure to include…
A: wireless cellular radio network: The two separate networks are joined together by means of a radio…
Q: The user interface and the user experience are two separate but equally important factors.…
A: Answer: A user interface designer is in charge of a website's appearance. "User experience" refers…
Q: Please let us know if you have any suggestions for making global company websites more accessible to…
A: Global Audience Design You may think developing a global website is simpler than a local one.…
Q: When evaluating whether or not a waterfall method is suitable for your project, think about the…
A: When evaluating whether or not a waterfall method is suitable for a project, it is important to…
Q: See what effect wireless networks have on developing countries. The lack of LANs or other sorts of…
A: Wireless networks are playing an increasingly important role in developing countries, particularly…
Q: Considering the GSM So, what exactly does it mean to have a finite state machine? An analysis of its…
A: A. A mathematical computer model known as a Finite State Machine (FSM) is used to create…
Q: Identify the sectors that make use of web engineering, and the difficulties in developing, testing,…
A: Web engineering is used in a variety of sectors including e-commerce, healthcare, banking,…
Q: 4.25 (Generate vehicle plate numbers) Assume that a vehicle plate number consists of three uppercase…
A: Here's a Python program that generates random vehicle plate numbers: Code: import randomimport…
Q: What is the single most important thing to think about while implementing challenging real-time…
A: To be determined: What component of running demanding real-time systems is the most crucial? In…
Q: Think about the many difficulties and setbacks you'll face as you build the structure, as well as…
A: Cloud computing is a modern technology with a reliable infrastructure that is user-friendly and…
Q: Can someone demo a SHA-1 and MD5 encryption and decryption algorithm and how do I find a signature…
A: ANSWER in next step:
Step by step
Solved in 2 steps

- Create a function sumofAllOdd(s,e) that will return the sum of all odd numbers in a range of inputted numbers s (starting number), e(ending number). For example: Test Result sumofAllOdd(22,55) sumofAllOdd(5,10) Answer:(penalty regime: 10, 20, ... %)def rectangle_overlap(rect1_bl_x,rect1_bl_y, rect1_tr_x,rect1_tr_y, rect2_bl_x,rect2_bl_y, rect2_tr_x,rect2_tr_y): """ (int,int,int,int,int,int,int,int) -> str Function determines whether two rectangles overlap. When rectangles overlap, the function checks for the following scenarios 1. The two rectangles share the same coordinates 2. The first rectangle is contained within the second 3. The second rectangle is contained within the first 4. The rectangles have overlapping area, but neither is completely contained within the other Function inputs represent x and y coordinates of bottom left and top right corners of rectangles (see lab document) The function return one of the following strings corresponding to the scenario "no overlap" "identical coordinates" "rectangle 1 is contained within rectangle 2" "rectangle…(Fibonacci) The Fibonacci series0, 1, 1, 2, 3, 5, 8, 13, 21, …begins with the terms 0 and 1 and has the property that each succeeding term is the sum of the twopreceding terms. a) Write a nonrecursive function fibonacci(n) that calculates the nth Fibonaccinumber. Use unsigned int for the function’s parameter and unsigned long long int for its returntype. b) Determine the largest Fibonacci number that can be printed on your system.
- Please help with my homework for the get() function in Python. Start with the following Python code. alphabet = "abcdefghijklmnopqrstuvwxyz" test_dups = ["zzz","dog","bookkeeper","subdermatoglyphic","subdermatoglyphics"] test_miss = ["zzz","subdermatoglyphic","the quick brown fox jumps over the lazy dog"] # From Section 11.2 of: # Downey, A. (2015). Think Python: How to think like a computer scientist. Needham, Massachusetts: Green Tree Press. def histogram(s): d = dict() for c in s: if c not in d: d[c] = 1 else: d[c] += 1 return dfunction myCompose(f,g){// TODO: return (f o g);// that is, a function that returns f(g(x)) when invoked on x.}4. Using c++ Write a function isPrime that accepts a positive long num and returns true IFF num is prime (e.g. only divisible by 1 and itself).
- Let 1 represent true and 0 represent false. The function Conjunction(), whose incomplete code is given below, computes p∧q: def Conjunction(p,q):#FIX ME#return 1else:return 0 What should the line of code which contains the expression #FIX ME# be replaced with in order to complete the code? Question 3 options: if p != q: if p == 0 and q == 0: if p == q: if p == 1 and q == 1:Define a function called gaussian() that takes in the arguments x, mu, and sig. Convert the above normal equation into code and return the output of the equation. Recall that mu represents ? and sig represents ?. # TODO 1.1 y_values = display(y_values) todo_check([ (y_values.shape == (120,),'y_values does not have the correct shape of (120,)'), (np.all(np.isclose(y_values,…Use Clojure: a. Write a function is-it-four? that returns true when given the number 4, and returns false otherwise. b. Define a function func and an expression expr such that the following evaluates to true.(= 3 (apply func expr))
- What is the best statement about the following function, f1? void f1 (int i) { int j; for (j = 0; j < i; ++j); cout << ‘*’; cout << endl; } Group of answer choices The f1 function prints a star. The f1 function prints a start on the ith line. The f1 function prints a line of i-1 stars. The f1 function prints a start on each of the i lines. The f1 function prints a start on each of the i-1 lines.7. Write a function password_check() that takes as input two stringsnewpassword and oldpassword, and that accepts the new password (i.e., returnsTrue) if newpassword is different from oldpassword and newpassword is atleast 6 letters long. If the new password fails the check, your functions should returnFalse.>>> password_check('E10-s2ff', 'E10.s2ff')True>>> password_check('E10sf', 'E10.s2ff')False>>> password_check('E10-s2ff', 'E10-s2ff')False(Extra Credit) For extra credit, extend your password function so that it also checks thatthe new password contains a digit.>>> password_check('E10-s2ff', 'E10.s2ff') True>>> password_check('Eej-sdff', 'E10.s2ff')False3. Find Relatively PrimeWrite a function to return a number that is relatively prime with the given number. /* return an integer that is relatively prime with n, and greater than 1i.e., the gcd of the returned int and n is 1 Note: Although gcd(n,n-1)=1, we don't want to return n-1*/int RelativelyPrime (int n)



